What is Trix file extension
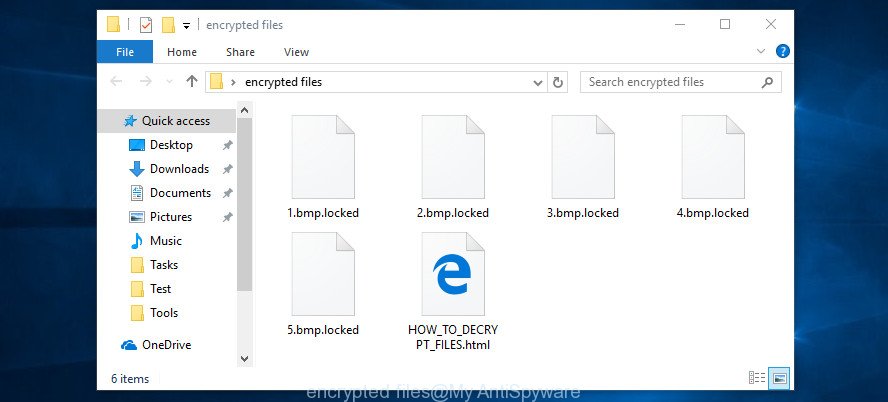
.Trix file extension is a file extension that is used by a malware belonging to the category of Ransomware to mark files that have been encrypted. Trix ransomware is a malicious program that encrypts user files and demands a ransom for a key-decryptor pair that is necessary to decrypt the affected files. Ransomware uses a strong encryption system and a long key, which virtually eliminates the possibility of decrypting files without a key. Files encrypted with .Trix extension become useless, their contents cannot be read without the key that the criminals have.
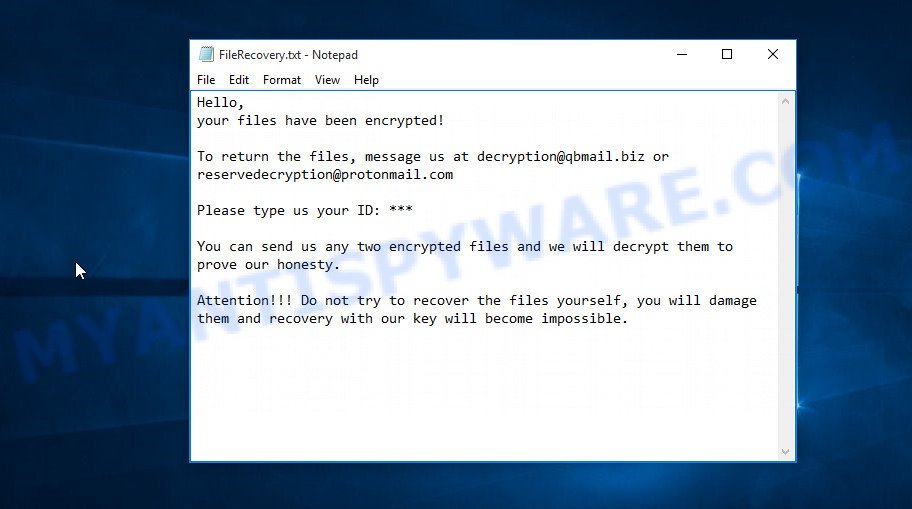
Trix ransomnote
What is Trix ransomware
Trix ransomware is a new malware that belongs to the category of ransomware. It appends the ‘.trix’ extension to each file that it encrypts using a complex encryption mechanism. As other ransomware, it can use the same distribution methods (spam emails, adware, cracks, key generators and so on). Upon execution, the Trix ransomware collects information about the computer and then proceeds to encrypt the files located on it. The following common file types can be encrypted:
.wsh, .1, .bc7, .fsh, .apk, .mdbackup, .xxx, .rgss3a, .css, .bik, .cdr, .wpl, .xls, .bay, .7z, .srf, .xld, .nrw, .wp5, .py, .t12, .vdf, .ws, .rofl, .slm, .wcf, .cer, .raw, .w3x, .zip, .wpd, .snx, .ppt, .xdl, .xf, .sid, .bsa, .wps, .zabw, .jpe, .wsc, .dbf, .rw2, .mov, .odb, .wma, .pdf, .wp4, .pak, .y, .xdb, .1st, .dba, .wm, .wgz, .xlgc, .wpd, .zdc, .x3f, .bkf, .csv, .jpeg, .xbplate, .hkdb, .dazip, .pptm, .mlx, .flv, .vcf, .ybk, .wpw, .js, .mpqge, .rim, .sav, .forge, .bkp, .wp7, .wpg, .asset, .xlsx, .wb2, .xar, .lrf, .xll, .rb, .ai, .wp, .xyw, .webp, .xy3, .zif, .ncf, .vfs0, .dxg, .iwd, .srw, .cas, .map, .docx, .itdb, .wav, .wmv, .blob, .wbz, .ods, .z, .kdb, .vpp_pc, .rwl, .0, .lbf, .dcr, .zw, .lvl, .mdf, .odc, .litemod, .3dm, .wdp, .upk, .xlk, .pkpass, .mef, .crt, .sb, .mp4, .ysp, .menu, .epk, .dwg, .wps, .mrwref, .m3u, .pst, .wpb, .mddata, .ztmp, .psk, .big, .rar, .ltx, .qic, .wot, .layout, .hkx, .docm, .wbm, .wpe, .wire, .webdoc, wallet, .sidd, .tor, .m4a, .sum, .xmmap, .wmd, .wbmp, .p7b, .wp6, .der, .vpk, .zi, .sidn, .pfx, .zip, .m2, .wotreplay, .p7c, .sql, .2bp, .tax, .wn, .dng, .raf, .xpm, .wpa, .doc, .sr2, .desc, .wma, .ptx, .xx, .jpg, .mdb, .x3d, .wbk, .pptx, .3ds, .wsd, .dmp, .pem, .gho, .wpt, .wmo, .iwi, .ibank, .xlsb, .xlsm, .hvpl, .wri, .orf, .hplg, .xwp, .yal, .esm, .bar, .itm, .gdb, .yml, .indd, .pdd, .svg, .cr2, .fos, .das, .itl, .avi, .xyp, .t13, .ff, .rtf, .pef, .vtf, .wbc, .xlsm, .x3f, .r3d, .accdb, .erf, .x, .z3d, .txt, .mcmeta, .bc6, .xml, .syncdb, .arw, .xls, .wbd, .ntl, .kdc, .re4, .xmind, .zdb, .crw, .psd, .kf, .wmv, .png, .odp, .fpk, .eps, .cfr, .sie, .arch00, .xbdoc, .qdf, .icxs, .wmf, .odm, .3fr, .sis, .d3dbsp, .odt, .wdb, .db0, .xlsx, .p12
All documents, photos, archives located on local disks, system disks and connected network drives will be encrypted. The Trix ransomware encrypts the contents of all disks file by file. Each file that has been encrypted is marked, the ransomware appends the ‘_ID_[USERID]_[[email protected]].trix’ extension to its name. For example, if a file had the name ‘document.doc’, then after this file is encrypted by this ransomware, it will have a name similar to the following ‘document.doc_ID_[567492175]_[[email protected]].trix’. Removing the extension or renaming the file will not help access the contents of the file. The associated program will not be able to read its contents.
The Trix ransomware creates a file with the name “FileRecovery.txt” on the infected computer. This file contains a message from the ransomware authors. The full text of this file is:
Hello,
your files have been encrypted!
To return the files, message us at [email protected] or [email protected]Please type us your ID: ***
You can send us any two encrypted files and we will decrypt them to prove our honesty.
Attention!!! Do not try to recover the files yourself, you will damage them and recovery with our key will become impossible.
Criminals use the “FileRecovery.txt” file to demand ransom from the Trix ransomware victims. The ransom demand message said that the victim’s files are encrypted. The ransomware authors demand a ransom in exchange for a key and a decryptor. Attackers offer to decrypt two files for free. Of course, decryption of two files cannot guarantee that, after paying the ransom, the victim will be able to recover files affected with the ransomware.
Threat Summary
| Name | Trix |
| Type | File locker, Ransomware, Crypto malware, Crypto virus, Filecoder |
| Encrypted files extension | _ID_[USERID]_[[email protected]].trix |
| Ransom note | FileRecovery.txt |
| Contact | [email protected], [email protected] |
| Ransom amount | $500-$1500 in Bitcoins |
| Detection Names | Trojan/Win32.Wacatac, TR/DelShad.nncre, Trojan.MulDrop12.13063, Trojan-Ransom.Gogoogle, BehavesLike.Win64.Autorun.vm, Win32/Trojan.f9e, Trojan:Win32/Bluteal!rfn, Trojan.Gen.MBT, Trojan.Win32.DelShad.dcn |
| Symptoms | Encrypted documents, photos and music. Your photos, documents and music have a wrong name, suffix or extension, or don’t look right when you open them. Files named like ‘FileRecovery.txt’, ‘READ-ME’, ‘_open me’, _DECRYPT YOUR FILES’ or ‘_Your files have been encrypted” in every folder with an encrypted file. Your desktop is locked with a message about How to pay to unlock your system. |
| Distribution methods | Phishing email scam that attempts to scare users into acting impulsively. Drive-by downloads from a compromised webpage. Social media, such as web-based instant messaging applications. Malvertising campaigns. |
| Removal | Trix ransomware removal guide |
| Recovery | Trix File Recovery |
On current date, antivirus companies have not created a method to decrypt files encrypted with .trix extension. Nevertheless, you do not need to despair. There are several ways to find and remove Trix ransomware, and there is also a chance to restore part or even all encrypted files to their original state. Below we will describe in detail how to do this.
How to remove Trix ransomware, Restore .Trix files
If you encounter the malicious actions of Trix ransomware, and your files have been encrypted with ‘.Trix’ extension, then you need to remove the virus or be 100% sure that there is no ransomware on your computer, and then proceed to restore the files. Both the ransomware removal process and the file recovery process will take a lot of time, so do not believe the magical instructions that say that this can be done very quickly. We definitely recommend, even if for some reason one of the methods proposed below did not suit you, try another one and try all of them. Perhaps one of them will help you. Feel free to ask questions in the special section on our website or in the comments below. In addition, we want to say that all the tools that we recommend using in our instructions are free and verified by security experts. And the last, before proceeding with the instructions, we advise you to read it thoroughly carefully, and then print or open it on a tablet or smartphone to have it always at hand.
- How to remove Trix ransomware
- How to decrypt .trix files
- How to restore .trix files
- How to protect your personal computer from Trix ransomware
How to remove Trix ransomware
There are not many good and free malware removal tools with high detection ratio. The effectiveness of malware removal utilities depends on various factors, mostly on how often their virus/malware signatures DB are updated in order to effectively detect modern worms, trojans, ransomware and other malware. We suggest to run several programs, not just one. These programs that listed below will allow you remove all components of the Trix crypto virus from your disk and Windows registry.
Use Zemana Anti-malware to remove Trix ransomware
Zemana is a free malware removal tool. Currently, there are two versions of the program, one of them is free and second is paid (premium). The principle difference between the free and paid version of the utility is real-time protection module. If you just need to scan your computer for malicious software and delete Trix ransomware, other kinds of potential threats such as malware and trojans, then the free version will be enough for you.
Visit the page linked below to download Zemana Anti Malware installation package called Zemana.AntiMalware.Setup on your computer. Save it on your Desktop.
165741 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
Run the installer after it has been downloaded successfully and then follow the prompts to install this utility on your machine.
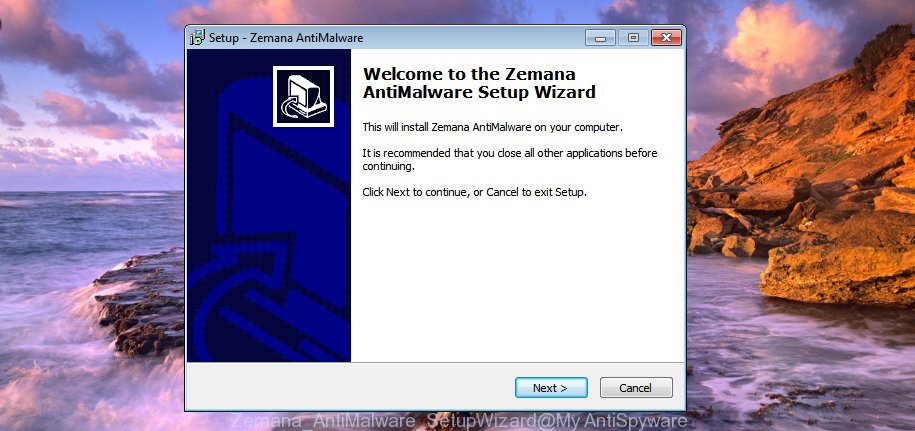
During install you can change some settings, but we suggest you do not make any changes to default settings.
When installation is finished, this malware removal utility will automatically start and update itself. You will see its main window as shown on the image below.

Now click the “Scan” button . Zemana Anti Malware (ZAM) program will scan through the whole PC system for the Trix ransomware, other kinds of potential threats like malicious software and trojans. A scan can take anywhere from 10 to 30 minutes, depending on the number of files on your machine and the speed of your computer. While the Zemana AntiMalware (ZAM) program is checking, you may see how many objects it has identified as threat.

Once the checking is complete, Zemana AntiMalware (ZAM) will show a scan report. Make sure to check mark the threats which are unsafe and then click “Next” button.
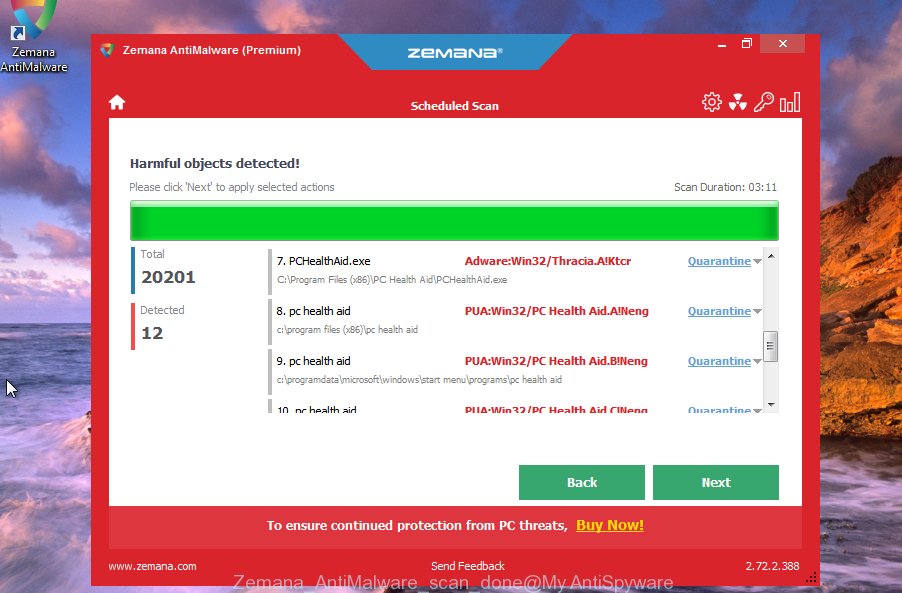
The Zemana Free will start to uninstall Trix crypto malware, other malicious software, worms and trojans. When that process is done, you can be prompted to restart your system to make the change take effect.
Remove Trix virus with MalwareBytes AntiMalware (MBAM)
We suggest using the MalwareBytes Anti Malware (MBAM) which are completely clean your system of ransomware. This free tool is an advanced malicious software removal program created by (c) Malwarebytes lab. This program uses the world’s most popular anti malware technology. It’s able to help you uninstall ransomware, potentially unwanted software, malicious software, adware software, toolbars, and other security threats from your personal computer for free.
MalwareBytes can be downloaded from the following link. Save it directly to your Microsoft Windows Desktop.
328051 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
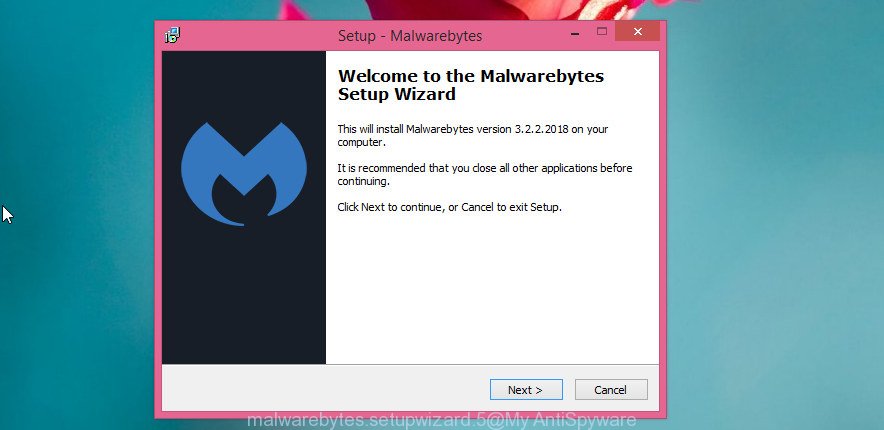
After the downloading process is complete, close all windows on your computer. Further, open the file called mb3-setup. If the “User Account Control” dialog box pops up as shown below, click the “Yes” button.
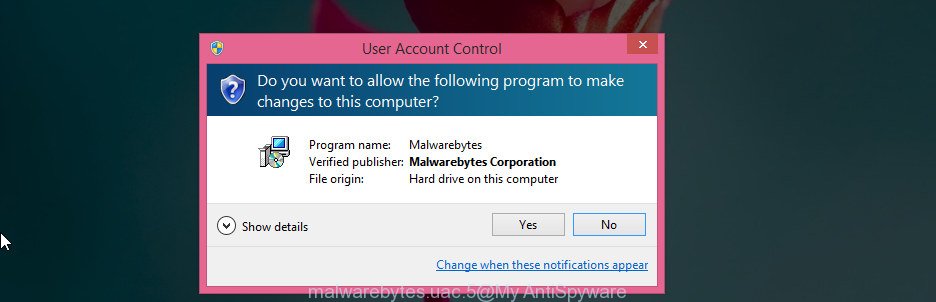
It will show the “Setup wizard” that will assist you set up MalwareBytes on the machine. Follow the prompts and do not make any changes to default settings.
Once installation is done successfully, press Finish button. Then MalwareBytes will automatically start and you may see its main window as shown below.
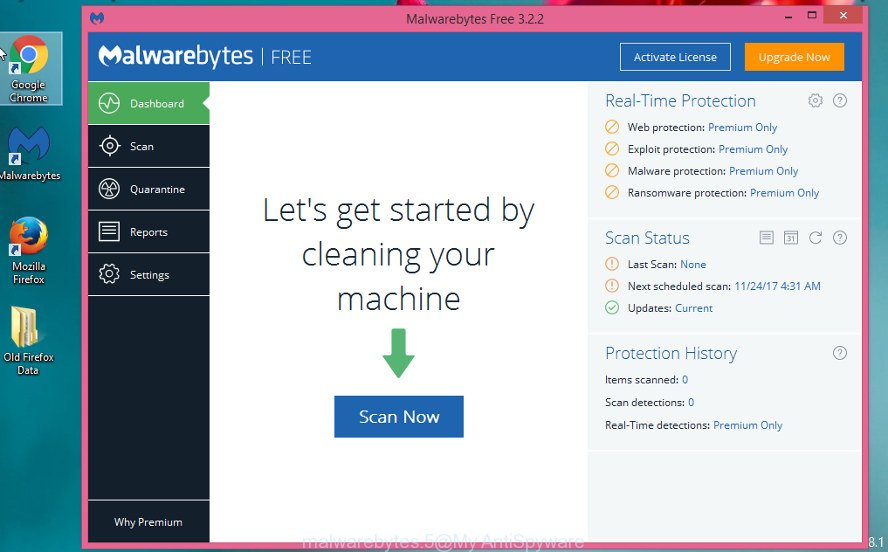
Next, click the “Scan Now” button to perform a system scan for the Trix crypto virus and other security threats. A system scan can take anywhere from 5 to 30 minutes, depending on your computer. While the MalwareBytes tool is checking, you can see number of objects it has identified as being affected by malicious software.
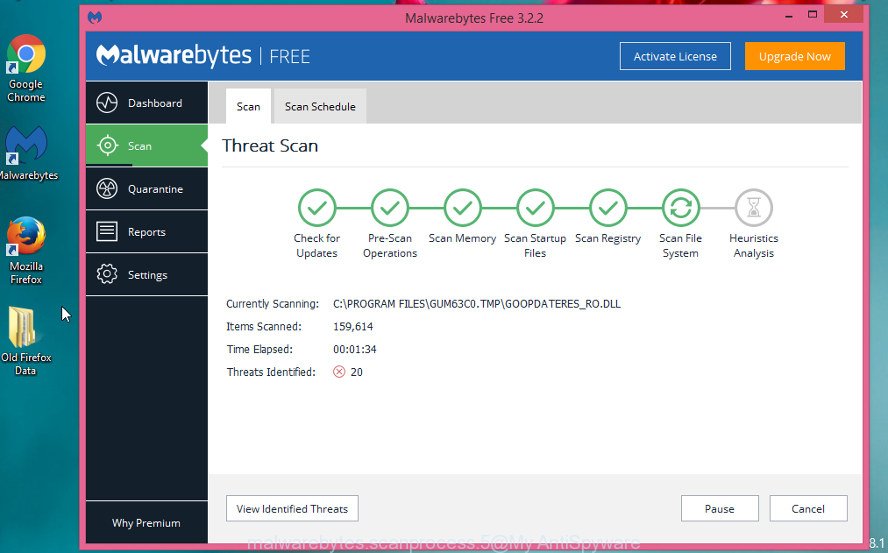
When finished, MalwareBytes Anti Malware will create a list of unwanted apps and ransomware. All found items will be marked. You can delete them all by simply click “Quarantine Selected” button.
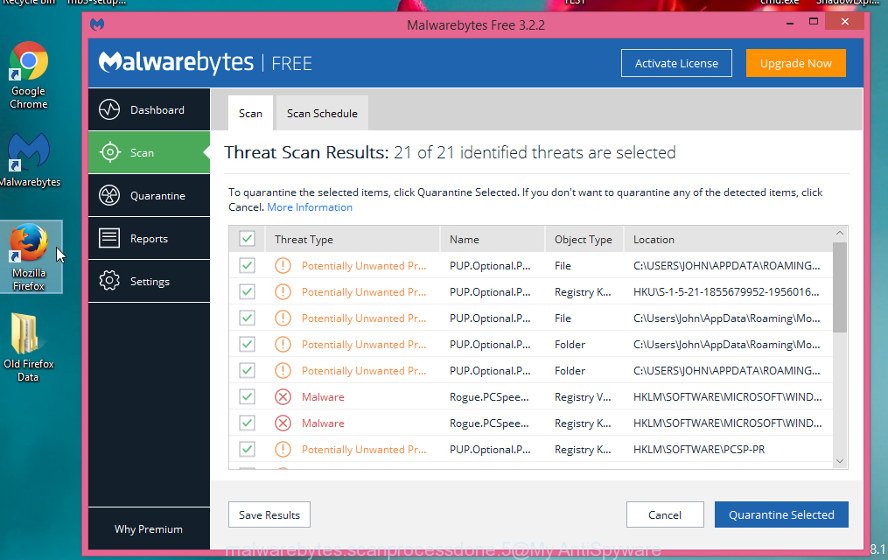
The MalwareBytes Anti Malware will remove Trix ransomware, other kinds of potential threats like malicious software and trojans and move the selected items to the Quarantine. Once that process is complete, you can be prompted to reboot your machine. We suggest you look at the following video, which completely explains the procedure of using the MalwareBytes Anti-Malware (MBAM) to delete browser hijacker infections, adware and other malware.
Use KVRT to remove Trix virus
If MalwareBytes anti malware or Zemana anti-malware cannot delete this ransomware, then we suggests to use Kaspersky virus removal tool (KVRT). KVRT is a free removal utility for ransomware, worms, spyware, trojans, adware, potentially unwanted software and other malware.
Download Kaspersky virus removal tool (KVRT) on your MS Windows Desktop from the following link.
129572 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
After the downloading process is done, double-click on the KVRT icon. Once initialization process is complete, you will see the KVRT screen as shown on the image below.
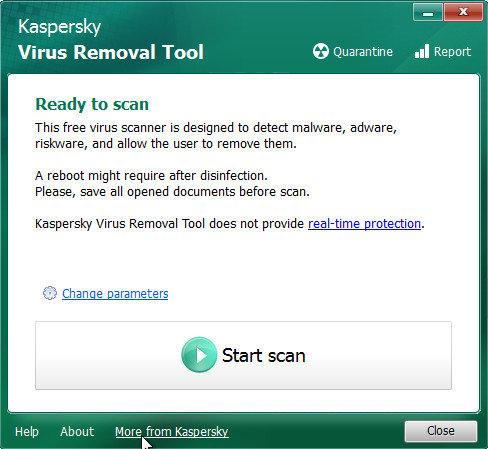
Click Change Parameters and set a check near all your drives. Press OK to close the Parameters window. Next press Start scan button to perform a system scan for the Trix ransomware and other known infections. Depending on your PC system, the scan may take anywhere from a few minutes to close to an hour. While the KVRT is checking, you may see number of objects it has identified either as being malicious software.
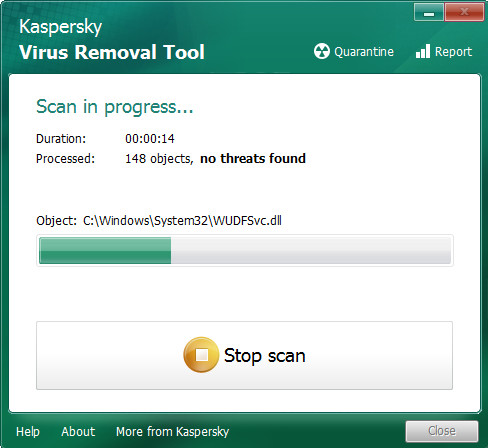
When KVRT has completed scanning, a list of all threats detected is produced as displayed in the following example.
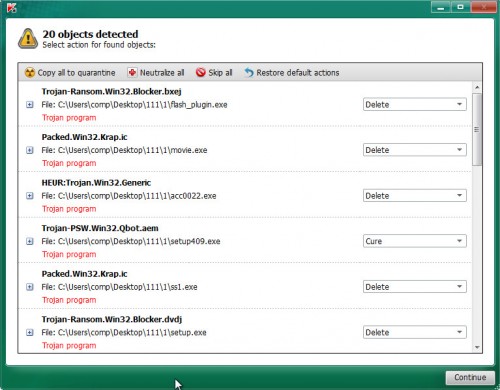
All found threats will be marked. You can delete them all by simply press on Continue to begin a cleaning task.
How to decrypt .trix files
Files with the extension ‘.trix’ are encrypted files. In other words, the contents of these files are locked. Their contents cannot be read even if you rename files or change their extension. Unfortunately, today there is no way to decrypt files encrypted by Trix ransomware virus, because to decrypt them you need a unique key, and this key is in the hands of criminals.

Never pay the ransom! Nevertheless, everyone has to remember that paying the developers of the Trix ransomware virus who are threatening you is a terrible idea. You can pay this money, but there is no guarantee that your files will be yours again. That is the reason why you should consider other options (that do not involve paying the makers of the Trix ransomware) in order to decrypt locked personal files. There still are some ways to defuse crypto malware without paying ransom, so you would not need to pay hackers and you would not let them reach their goal.
Fortunately, there are several alternative methods that do not require the use of a key and therefore allow you restore the contents of encrypted files. Try to recover the encrypted files using free tools listed below.
How to restore .trix files
If all your files are encrypted with .trix file extension, then you only have one thing left, use alternative methods to restore the contents of the encrypted files. There are several alternative methods that may allow you to restore the contents of encrypted files. These methods of file recovery do not use decryption, so there is no need for a key and decryptor. Before you begin, you must be 100% sure that the computer does not have active ransomware. Therefore, if you have not yet checked your computer for ransomware, do it right now, use free malware removal tools or return to step 1 above.
Recover .trix encrypted files using Shadow Explorer
A free tool named ShadowExplorer is a simple solution to use the ‘Previous Versions’ feature of MS Windows 10 (8, 7 , Vista). You can recover your documents, photos, and music encrypted by Trix ransomware from Shadow Copies for free. Unfortunately, this method does not always work due to the fact that the ransomware almost always deletes all Shadow copies.
ShadowExplorer can be downloaded from the following link. Save it to your Desktop.
440334 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
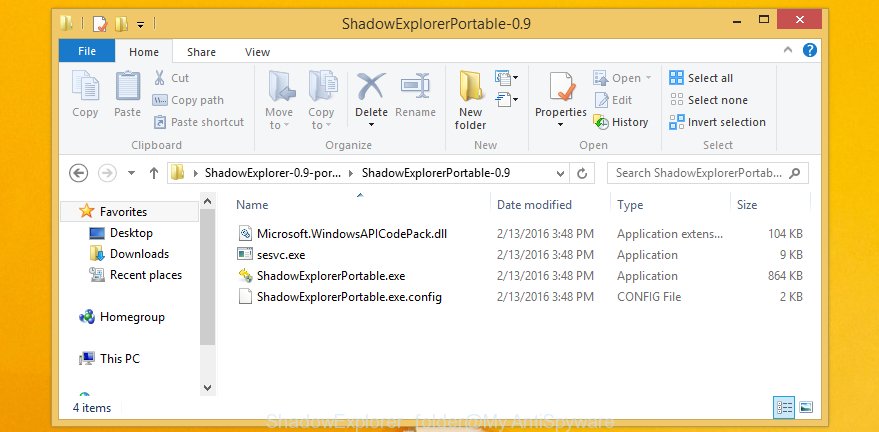
When the downloading process is complete, open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and select Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder as displayed on the screen below.
Start the ShadowExplorer utility and then select the disk (1) and the date (2) that you wish to recover the shadow copy of file(s) encrypted by the Trix ransomware as displayed on the screen below.
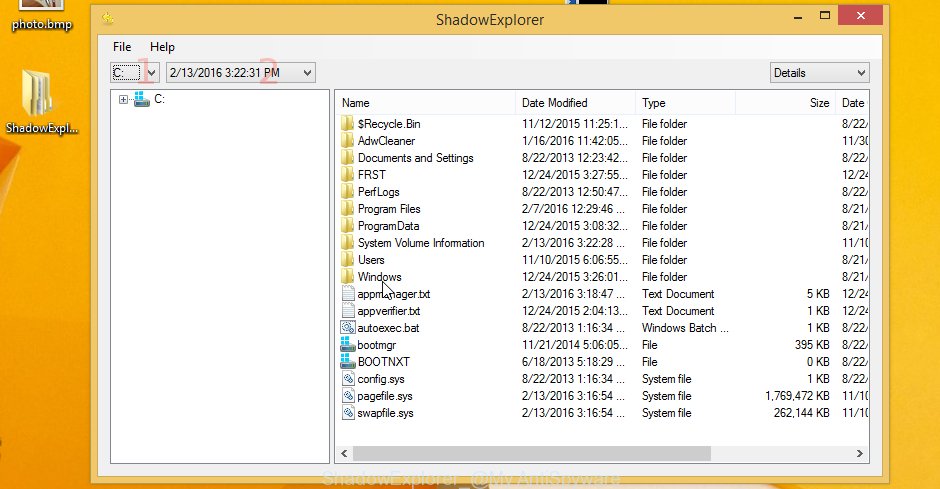
Now navigate to the file or folder that you wish to restore. When ready right-click on it and press ‘Export’ button as displayed in the following example.

Recover .trix files with PhotoRec
There is another way to recover the contents of the encrypted files. This method is based on using data recovery tools. We recommend using a tool called PhotoRec. It has all the necessary functions and is completely free.
Download PhotoRec by clicking on the following link. Save it directly to your Windows Desktop.
After the downloading process is done, open a directory in which you saved it. Right click to testdisk-7.0.win and select Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as displayed below.

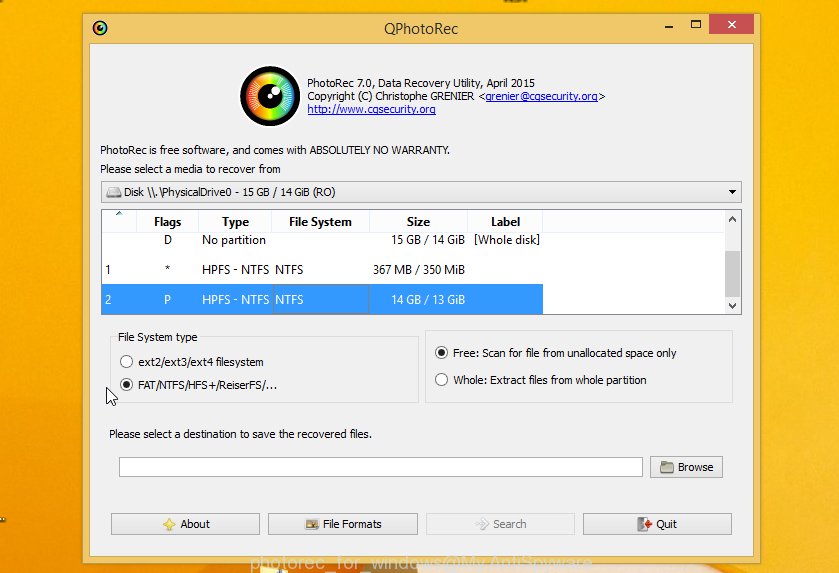
Double click on qphotorec_win to run PhotoRec for Microsoft Windows. It’ll display a screen as shown on the screen below.
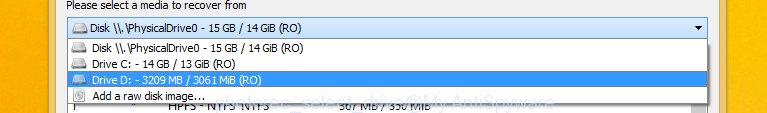
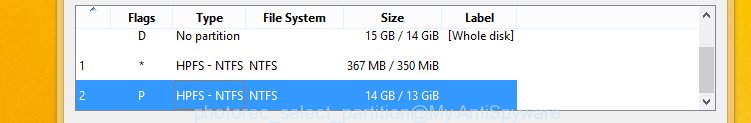
Choose a drive to recover as on the image below.
You will see a list of available partitions. Choose a partition that holds encrypted photos, documents and music as displayed on the screen below.
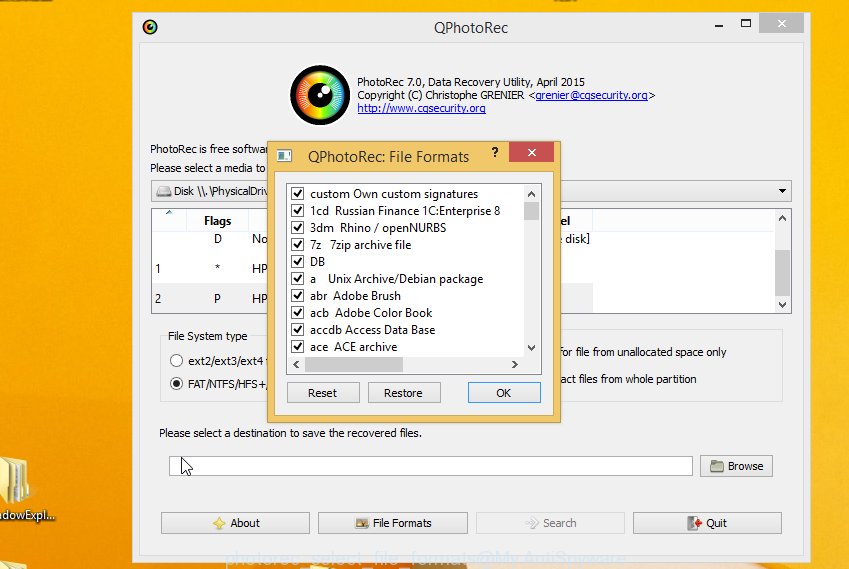
Click File Formats button and select file types to restore. You can to enable or disable the restore of certain file types. When this is complete, click OK button.
Next, press Browse button to choose where recovered photos, documents and music should be written, then click Search.
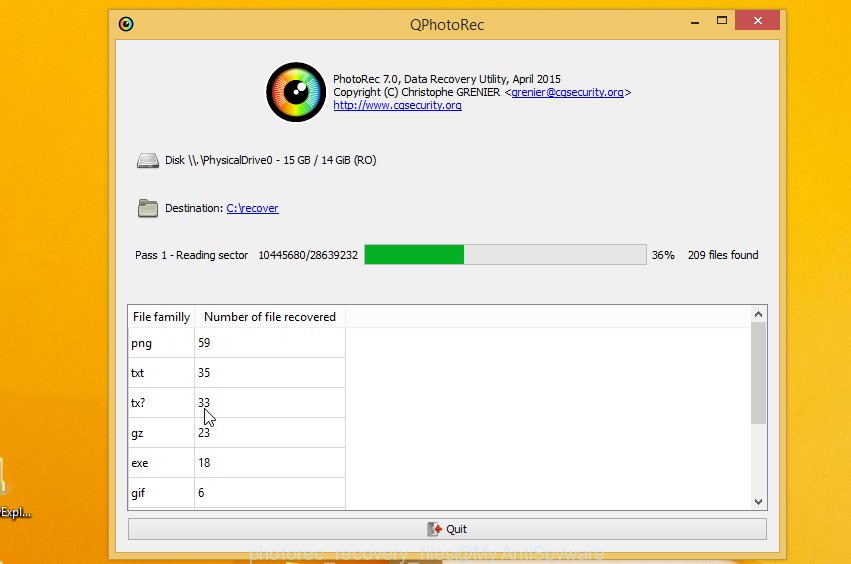
Count of recovered files is updated in real time. All restored personal files are written in a folder that you have chosen on the previous step. You can to access the files even if the recovery process is not finished.
When the recovery is finished, click on Quit button. Next, open the directory where restored files are stored. You will see a contents such as the one below.
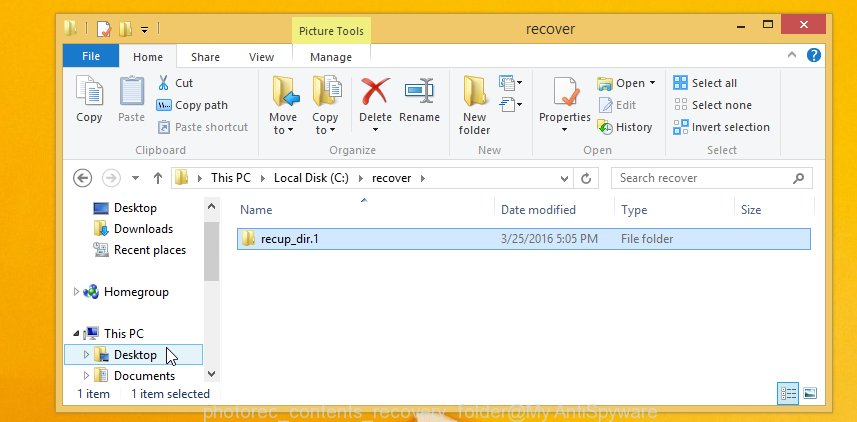
All recovered personal files are written in recup_dir.1, recup_dir.2 … sub-directories. If you’re looking for a specific file, then you can to sort your recovered files by extension and/or date/time.
How to protect your personal computer from Trix ransomware
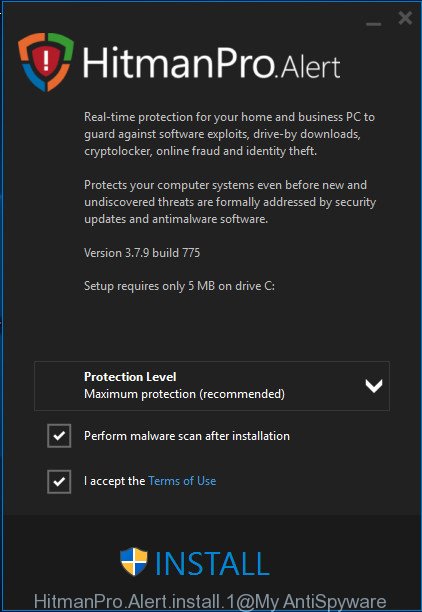
Most antivirus apps already have built-in protection system against the crypto malware. Therefore, if your computer does not have an antivirus application, make sure you install it. As an extra protection, use the HitmanPro.Alert. All-in-all, HitmanPro.Alert is a fantastic utility to protect your PC system from any ransomware. If ransomware is detected, then HitmanPro.Alert automatically neutralizes malware and restores the encrypted files. HitmanPro.Alert is compatible with all versions of MS Windows operating system from Microsoft Windows XP to Windows 10.
Please go to the link below to download the latest version of HitmanPro Alert for MS Windows. Save it on your MS Windows desktop or in any other place.
When the downloading process is complete, open the directory in which you saved it. You will see an icon like below.

Double click the HitmanPro Alert desktop icon. After the utility is started, you’ll be displayed a window where you can choose a level of protection, as shown on the image below.
Now press the Install button to activate the protection.
Finish words
This guide was created to help all victims of the Trix ransomware virus. We tried to give answers to the following questions: how to remove ransomware; how to decrypt .Trix files; how to recover the encrypted files. We hope that the information presented in this manual has helped you.
If you have questions, then write to us, leaving a comment below. If you need more help with Trix related issues, go to here.






















