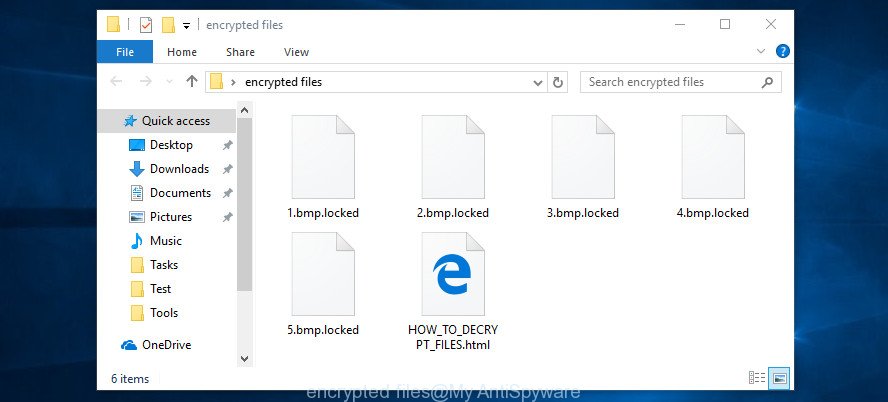
Gorentos@firemail.cc ransomware is a new crypto virus. Like other ransomware, it is basically a harmful program which gets on your PC and runs. It locks up your photos, documents and music and changes their extensions. This article will provide you a brief summary of information related to this crypto malware and how to restore (decrypt) encrypted files for free.
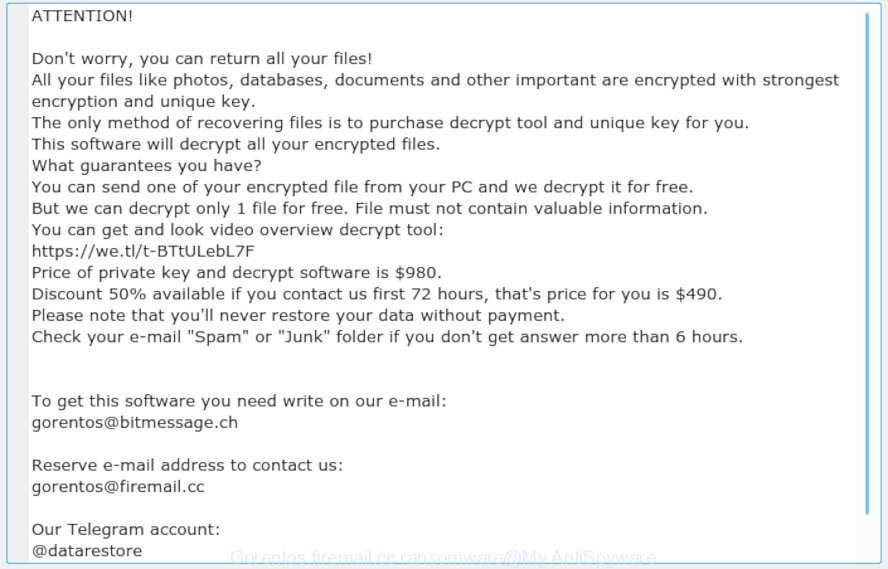
“Gorentos@firemail.cc ransomware” – ransom note
Gorentos@firemail.cc ransomware virus encrypts files using an unbreakable ‘key’ that only the software authors knows. It forces you to pay a ransom to decrypt them. It is known to encrypt almost all file types, including files with extensions:
.map, .pptm, .cer, .srf, .icxs, .fos, .1st, .srw, .wsh, .raf, .vtf, .gho, .wps, .layout, .dwg, .m3u, .dng, .jpeg, .xmmap, .3ds, .webp, .litemod, .3fr, .crt, .p12, .doc, .wire, .wmv, .xpm, .wpe, .ai, .db0, .ptx, .dazip, .sis, .z3d, .wbc, .pdd, .esm, .cas, .xlk, .lbf, .zdb, .odt, .wps, .rwl, .upk, .ws, .mlx, .wpw, .mrwref, .r3d, .wp5, .qdf, .fsh, .docx, .xlgc, .xlsb, .erf, .zip, .p7c, .zw, .ods, .kdb, .mdbackup, .yal, .m4a, .cfr, .xyw, .sie, .pef, .mddata, .dcr, .3dm, .wm, .zdc, .pak, .1, .mcmeta, .syncdb, .indd, .der, .wp6, .nrw, .blob, .mpqge, .wcf, .ybk, .docm, .xls, .sav, .p7b, .wpt, .x3f, .forge, .pkpass, .w3x, .m2, .xml, .das, .odb, .xdl, .raw, .webdoc, .asset, .t12, .wpd, .0, .re4, .ysp, wallet, .crw, .rar, .gdb, .png, .slm, .xx, .wp4, .zip, .ncf, .xf, .xxx, .wgz, .bar, .kdc, .xar, .pptx, .wsd, .wma, .rb, .wpb, .wp7, .hkx, .yml, .xls, .mdf, .dba, .vpk, .xmind, .psk, .kf, .wbmp, .wmv, .bik, .iwi, .iwd, .lrf, .xbdoc, .wpg, .wot, .sidd, .js, .wbm, .epk, .txt, .pst, .wb2, .wn, .x, .accdb, .bc7, .big, .ppt, .zabw, .csv, .qic, .jpg, .wri, .ff, .y, .cr2, .wpa, .pem, .menu, .xlsx, .xlsm, .wpl, .jpe, .wotreplay, .ntl, .wpd, .odc, .vdf, .flv, .pfx, .xll, .pdf, .fpk, .zi, .bc6, .sr2, .mdb, .rtf, .sb, .wmo, .t13, .x3d, .wdp, .orf
Once the encryption process is finished, it will drop a ransom demanding message named ‘_readme.txt’ offering decrypt all users photos, documents and music if a payment is made. An example of the ransomnote is:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-BTtULebL7F Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: gorentos@bitmessage.ch Reserve e-mail address to contact us: gorentos@firemail.cc Our Telegram account: @datarestore Your personal ID:
Threat Summary
| Name | Gorentos@firemail.cc |
| Type | Ransomware, Filecoder, Crypto virus, File locker, Crypto malware |
| Encrypted files extension | encrypted files |
| Ransom note | _readme.txt |
| Contact | gorentos@firemail.cc, gorentos@bitmessage.ch, @datarestore (telegram) |
| Ransom amount | $980, $490 in Bitcoins |
| Symptoms | Documents, photos and music won’t open. Files are encrypted with a encrypted files file extension. Files named like ‘_readme.txt’, ‘#_README_#’, ‘_DECRYPT_’ or ‘recover’ in each folder with at least one encrypted file. Your desktop is locked with a message about How to pay to unlock your system. |
| Distribution methods | Spam mails that contain malicious links. Exploit kits (cybercriminals use crypto malware packaged in an ‘exploit kit’ that can find a vulnerability in Adobe Flash Player, Web-browser, Windows operating system, PDF reader). Social media posts (they can be used to force users to download malicious software with a built-in ransomware downloader or click a malicious link). Remote desktop protocol (RDP) hacking. |
| Removal | To remove Gorentos@firemail.cc ransomware use the removal guide |
| Decryption | To decrypt Gorentos@firemail.cc ransomware use the steps |
Therefore it’s very important to follow the guide below immediately. The step-by-step instructions will allow you to delete Gorentos@firemail.cc ransomware. What is more, the step-by-step guidance below will help you recover encrypted photos, documents and music for free.
Quick links
- How to remove Gorentos@firemail.cc ransomware virus
- How to decrypt encrypted files
- Use STOPDecrypter to decrypt Gorentos@firemail.cc ransomware
- How to restore encrypted files
- How to protect your system from Gorentos@firemail.cc crypto malware?
- Finish words
How to remove Gorentos@firemail.cc ransomware virus
The following instructions will help you to remove Gorentos@firemail.cc ransomware and other malware. Before doing it, you need to know that starting to remove ransomware virus, you may block the ability to decrypt photos, documents and music by paying developers of the ransomware requested ransom. Zemana Anti-malware, Kaspersky virus removal tool and Malwarebytes Anti-malware can detect different types of active ransomware viruses and easily delete it from your system, but they can not recover encrypted photos, documents and music.
Run Zemana Anti-malware to remove Gorentos@firemail.cc ransomware
We suggest using the Zemana Anti-malware. You can download and install Zemana Anti-malware to search for and delete Gorentos@firemail.cc from your computer. When installed and updated, this malware remover will automatically scan and detect all threats present on the personal computer.
Visit the page linked below to download the latest version of Zemana AntiMalware (ZAM) for Microsoft Windows. Save it to your Desktop so that you can access the file easily.
165086 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
Once downloading is finished, start it and follow the prompts. Once installed, the Zemana AntiMalware will try to update itself and when this task is done, click the “Scan” button to search for Gorentos@firemail.cc crypto malware, other malware, worms and trojans.

A scan may take anywhere from 10 to 30 minutes, depending on the number of files on your PC and the speed of your PC. During the scan Zemana Anti Malware will find threats exist on your machine. You may remove threats (move to Quarantine) by simply press “Next” button.
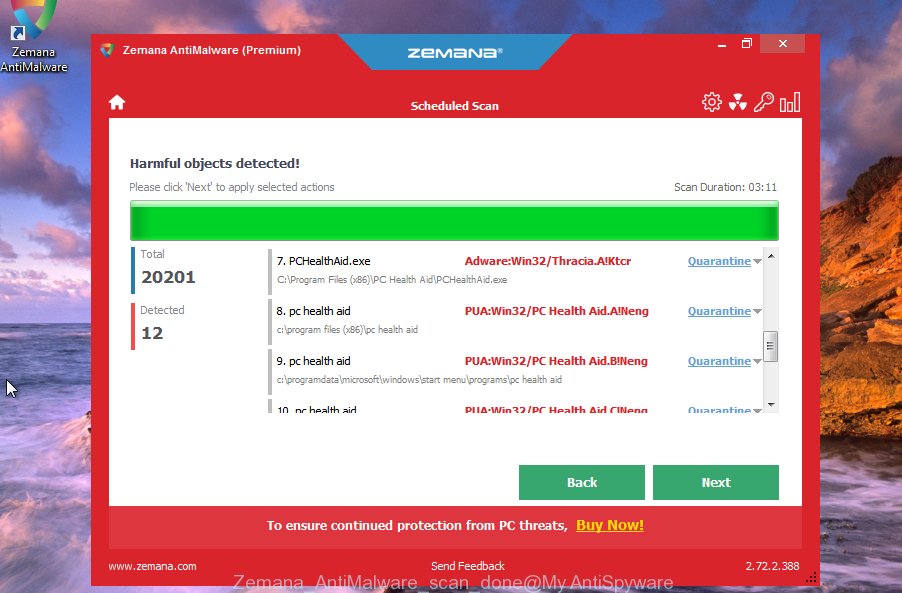
The Zemana AntiMalware will remove Gorentos@firemail.cc ransomware virus and other security threats and move items to the program’s quarantine.
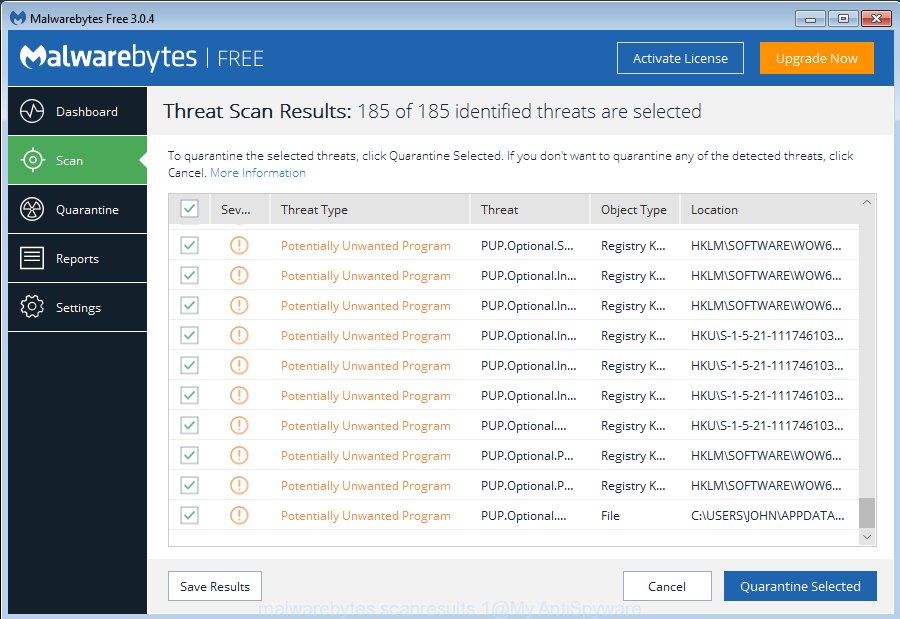
Remove Gorentos@firemail.cc virus with MalwareBytes
We suggest using the MalwareBytes Anti-Malware. You may download and install MalwareBytes Anti Malware to scan for and remove Gorentos@firemail.cc virus from your personal computer. When installed and updated, this free malware remover automatically finds and deletes all threats exist on the computer.
- Installing the MalwareBytes Free is simple. First you will need to download MalwareBytes AntiMalware from the following link. Save it on your MS Windows desktop.
Malwarebytes Anti-malware
327304 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
- At the download page, click on the Download button. Your browser will open the “Save as” prompt. Please save it onto your Windows desktop.
- After the downloading process is finished, please close all apps and open windows on your computer. Double-click on the icon that’s named mb3-setup.
- This will start the “Setup wizard” of MalwareBytes onto your personal computer. Follow the prompts and do not make any changes to default settings.
- When the Setup wizard has finished installing, the MalwareBytes Anti Malware will start and display the main window.
- Further, click the “Scan Now” button to search for Gorentos@firemail.cc crypto malware and other security threats. Depending on your PC system, the scan can take anywhere from a few minutes to close to an hour. While the MalwareBytes Anti Malware (MBAM) tool is scanning, you can see number of objects it has identified as being affected by malicious software.
- After that process is done, MalwareBytes AntiMalware (MBAM) will prepare a list of undesired programs adware.
- In order to delete all threats, simply press the “Quarantine Selected” button. After the clean up is finished, you may be prompted to restart the personal computer.
- Close the Anti-Malware and continue with the next step.
Video instruction, which reveals in detail the steps above.
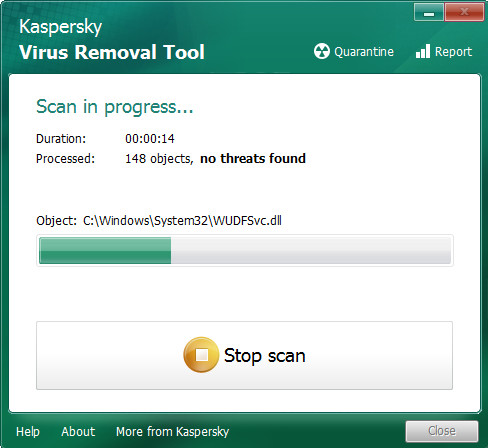
Scan and free your machine of crypto malware with KVRT
KVRT is a free removal tool which can scan your PC for a wide range of security threats like the Gorentos@firemail.cc crypto malware, trojans, worms as well as other malicious software. It will perform a deep scan of your computer including hard drives and MS Windows registry. After a malware is detected, it will help you to remove all detected threats from your personal computer with a simple click.
Download Kaspersky virus removal tool (KVRT) from the link below. Save it to your Desktop so that you can access the file easily.
129308 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
After downloading is finished, double-click on the Kaspersky virus removal tool icon. Once initialization process is finished, you’ll see the Kaspersky virus removal tool screen as on the image below.
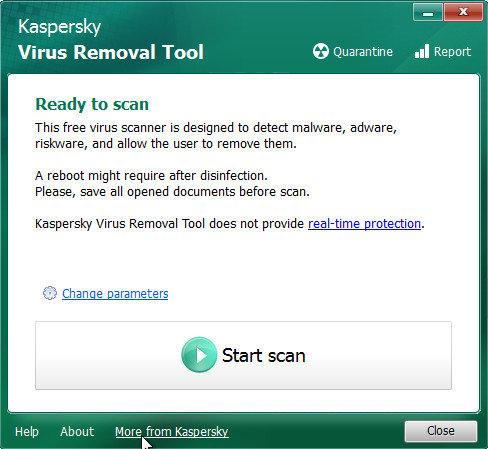
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next click Start scan button for checking your machine for the Gorentos@firemail.cc ransomware and other known infections. Depending on your PC, the scan can take anywhere from a few minutes to close to an hour. While the KVRT program is checking, you can see count of objects it has identified as threat.
Once Kaspersky virus removal tool has completed scanning your PC system, KVRT will display a list of found items as displayed on the screen below.
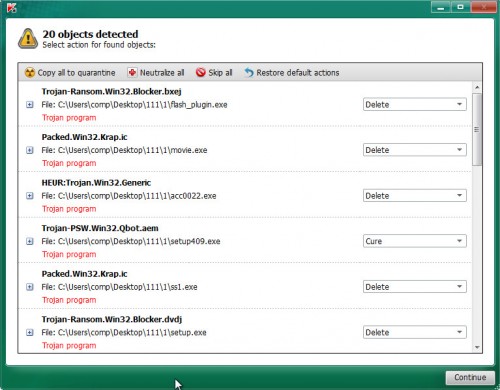
Next, you need to press on Continue to begin a cleaning task.
How to decrypt encrypted files
The encryption mode is so strong that it’s practically impossible to decrypt encrypted files without the actual encryption key. The bad news is that the only way to get your files back is to pay ($490, $980 in Bitcoins) authors of the Gorentos@firemail.cc ransomware virus for a copy of the private (encryption) key.

Should you pay the ransom? A majority of computer security professionals will reply immediately that you should never pay a ransom if infected by ransomware! If you choose to pay the ransom, there is no 100% guarantee that you can decrypt all files!
With some variants of Gorentos@firemail.cc ransomware, it is possible to decrypt or restore encrypted files using free tools such as STOPDecrypter, ShadowExplorer and PhotoRec.
Use STOPDecrypter to decrypt Gorentos@firemail.cc ransomware
Michael Gillespie (@) released a free decryption tool named STOPDecrypter (download from download.bleepingcomputer.com/demonslay335/STOPDecrypter.zip).
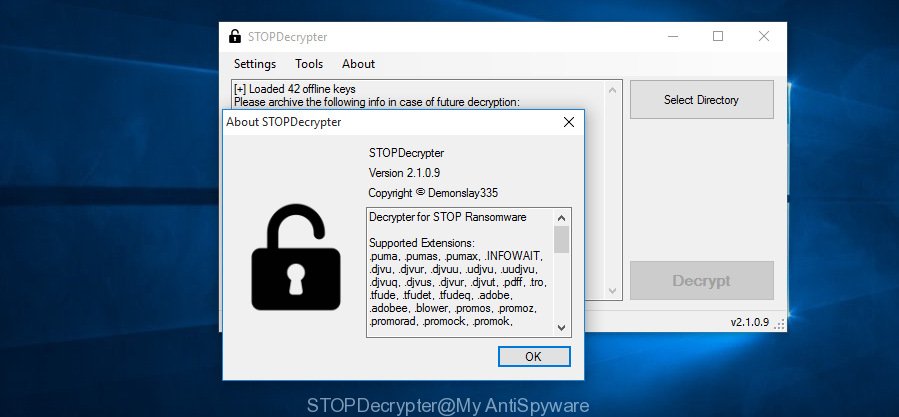
STOPDecrypter
STOPDecrypter has been updated to include decryption support for the following .djvu* variants (.djvu, .djvuu, .udjvu, .djvuq, .djvur, .djvut, .pdff, .tro, .tfude, .tfudeq, .tfudet, .rumba, .adobe, .adobee, .blower, .promos, .dotmap. STOPDecrypter will work for any extension of the Djvu* variants including new extensions.
Please check the twitter post for more info.
How to restore encrypted files
In some cases, you can recover files encrypted by Gorentos@firemail.cc ransomware virus. Try both methods. Important to understand that we cannot guarantee that you will be able to restore all encrypted documents, photos and music.
Run ShadowExplorer to recover encrypted files
If automated backup (System Restore) is enabled, then you can use it to recover all encrypted files to previous versions.
Visit the following page to download ShadowExplorer. Save it on your MS Windows desktop.
439697 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
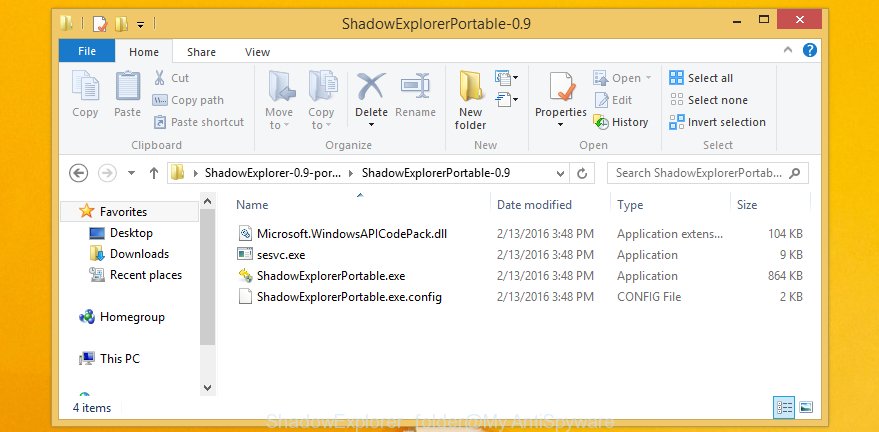
After the downloading process is finished, open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and select Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder as displayed in the following example.
Double click ShadowExplorerPortable to start it. You will see the a window as displayed in the figure below.
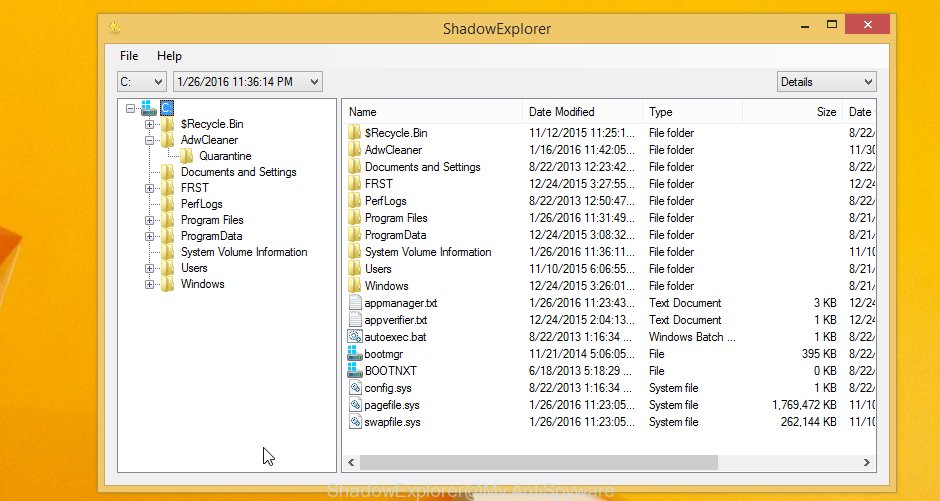
In top left corner, choose a Drive where encrypted files are stored and a latest restore point as shown below (1 – drive, 2 – restore point).
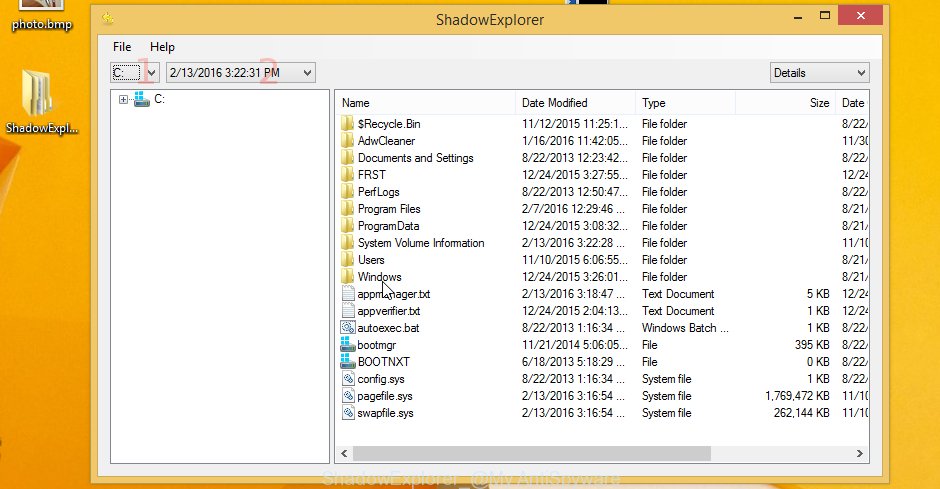
On right panel look for a file that you wish to recover, right click to it and select Export like below.

Use PhotoRec to recover encrypted files
Before a file is encrypted, the Gorentos@firemail.cc ransomware makes a copy of this file, encrypts it, and then deletes the original file. This can allow you to restore your files using file restore apps such as PhotoRec.
Download PhotoRec from the link below. Save it directly to your Microsoft Windows Desktop.
After the download is complete, open a directory in which you saved it. Right click to testdisk-7.0.win and select Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as displayed below.

Double click on qphotorec_win to run PhotoRec for Windows. It will display a screen as displayed in the figure below.
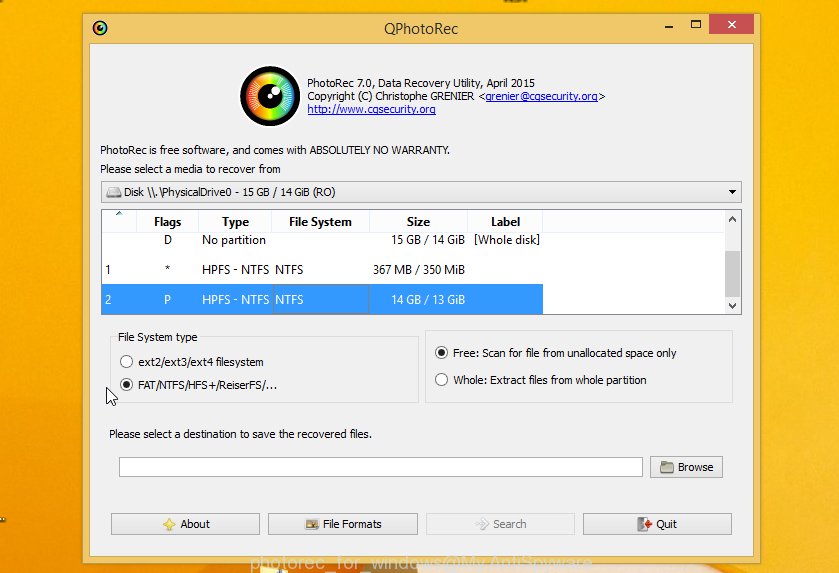
Select a drive to recover as displayed below.
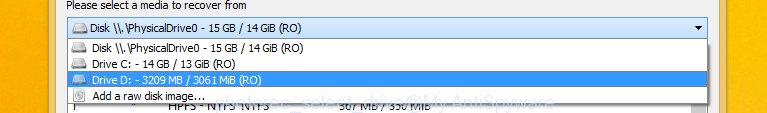
You will see a list of available partitions. Choose a partition that holds encrypted files like below.
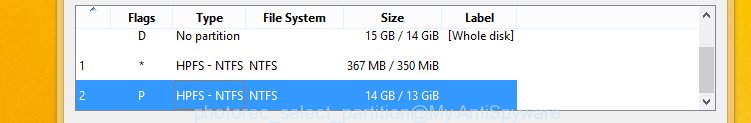
Click File Formats button and specify file types to restore. You can to enable or disable the restore of certain file types. When this is done, click OK button.
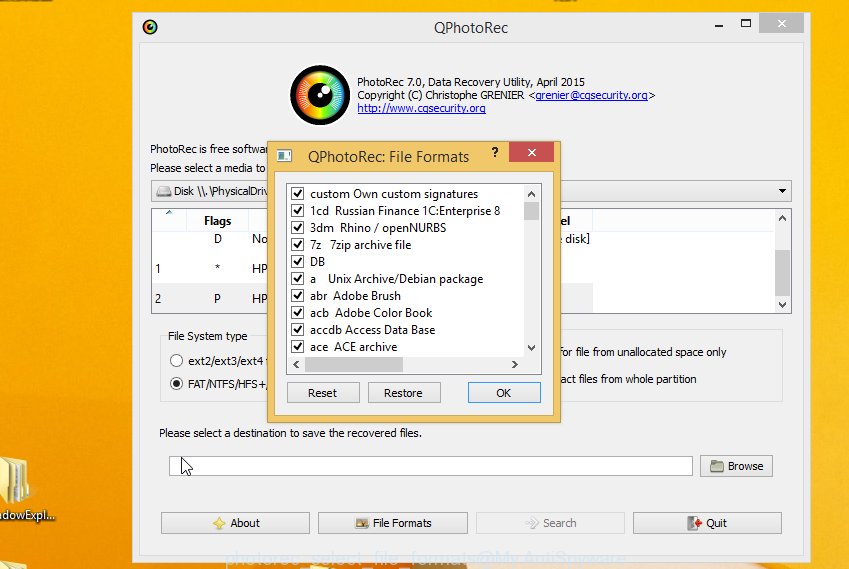
Next, click Browse button to choose where recovered files should be written, then click Search.
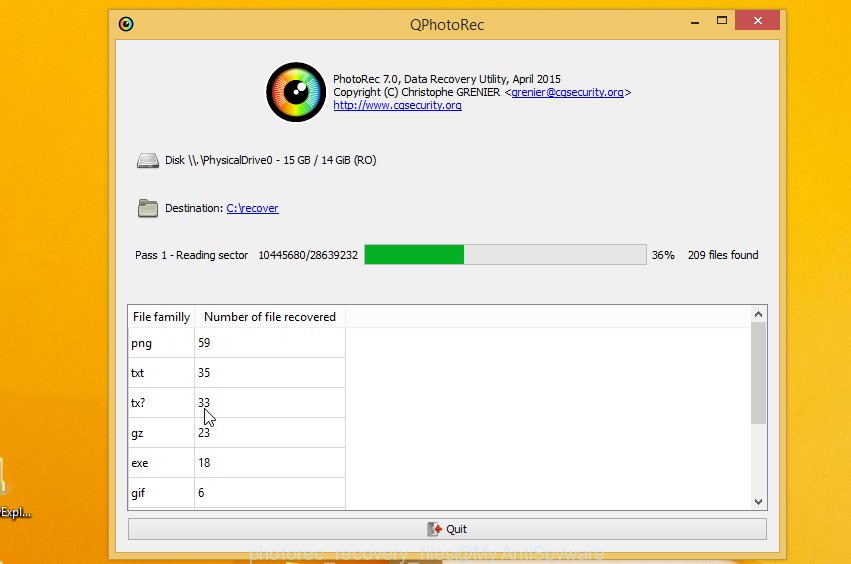
Count of recovered files is updated in real time. All restored personal files are written in a folder that you have selected on the previous step. You can to access the files even if the restore process is not finished.
When the restore is complete, press on Quit button. Next, open the directory where recovered personal files are stored. You will see a contents like below.
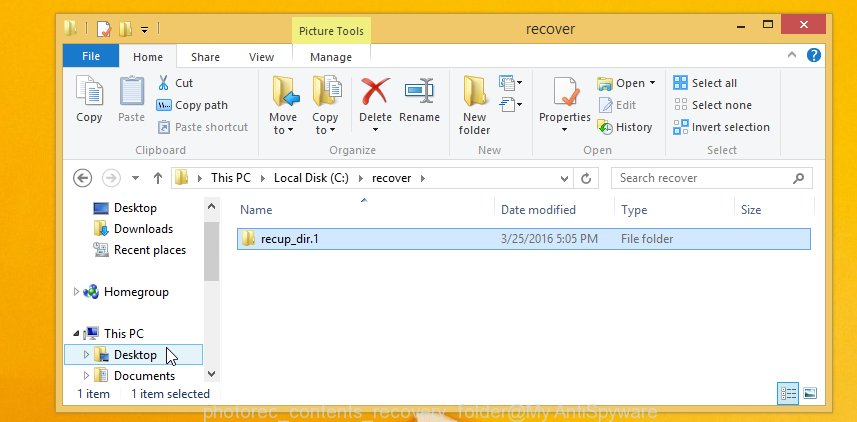
All restored documents, photos and music are written in recup_dir.1, recup_dir.2 … sub-directories. If you are searching for a specific file, then you can to sort your restored files by extension and/or date/time.
How to protect your system from Gorentos@firemail.cc crypto malware?
Most antivirus apps already have built-in protection system against the crypto malware. Therefore, if your machine does not have an antivirus program, make sure you install it. As an extra protection, use the HitmanPro.Alert.
Run HitmanPro.Alert to protect your PC system from Gorentos@firemail.cc crypto malware
HitmanPro.Alert is a small security tool. It can check the system integrity and alerts you when critical system functions are affected by malware. HitmanPro.Alert can detect, remove, and reverse ransomware effects.
HitmanPro Alert can be downloaded from the following link. Save it to your Desktop.
After the download is complete, open the directory in which you saved it. You will see an icon like below.

Double click the HitmanPro.Alert desktop icon. Once the tool is started, you’ll be shown a window where you can select a level of protection, as displayed on the image below.

Now press the Install button to activate the protection.
Finish words
Now your system should be free of the Gorentos@firemail.cc ransomware virus. Delete Kaspersky virus removal tool and MalwareBytes AntiMalware. We suggest that you keep Zemana (to periodically scan your machine for new malicious software). Probably you are running an older version of Java or Adobe Flash Player. This can be a security risk, so download and install the latest version right now.
If you are still having problems while trying to get rid of Gorentos@firemail.cc ransomware from your machine, then ask for help here.




















