What is Search.tablicious.com?
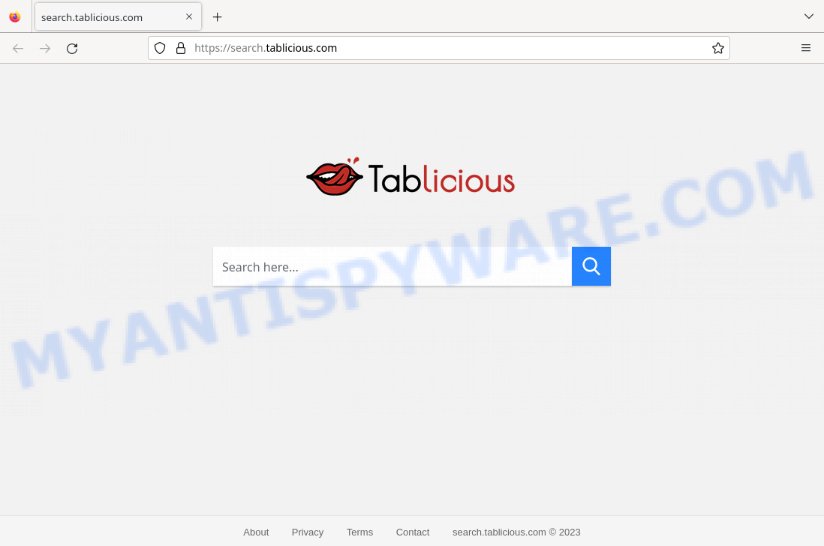
Search.tablicious.com is yet another fake search engine. A fake search engine is a website that appears to be a legitimate search engine, but in reality it is designed to manipulate users and deceive them into clicking on advertisements or visiting other websites. The most commonly used method for promoting fake search engines is browser hijacking, where malicious software changes a user’s default search engine to a fake search engine without their knowledge or consent. This method can be particularly dangerous, as it can make it difficult for users to return to their preferred search engine and can expose them to potential security risks.
QUICK LINKS
Search.tablicious.com in detail
Browser hijackers usually trick users into using fake search engines by changing their default search engine without permission. These fake search engines may resemble legitimate ones, but they display false or misleading results that lead users to phishing or dangerous websites. The search results page may also have added ads or pop-ups, making it harder for the user to find what they need. The fake search engine might also gather information about the user’s search queries for malicious use, such as targeted advertising or identity theft.
Search.tablicious.com search results:
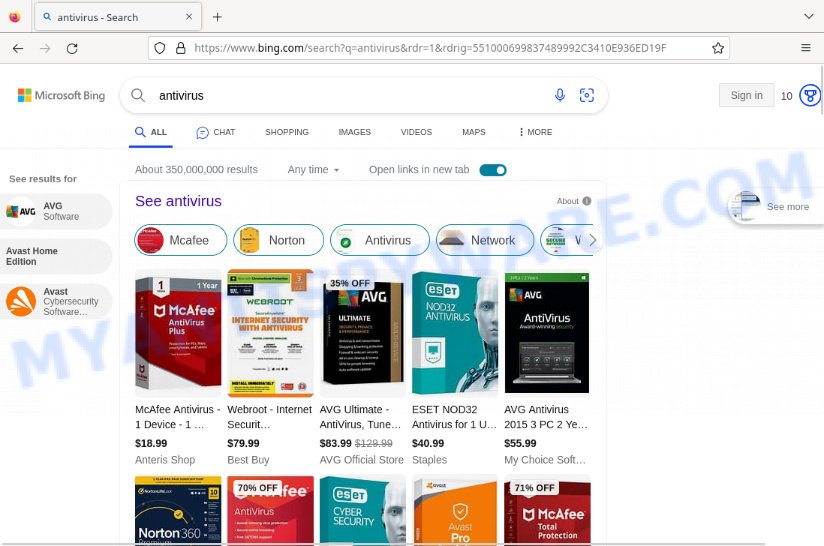
Browser hijackers may also direct users to legitimate search engines like Google, Bing, or Yahoo. By redirecting users to a trusted search engine, the browser hijacker can display ads or collect information about their search and web browsing activities.
In addition, browser hijackers can redirect users to fraudulent websites as part of their harmful actions. This redirection can occur without the user’s knowledge and is usually done to deceive them into visiting sites that steal their personal information, such as login credentials or credit card numbers.
These scam websites may seem like legitimate ones, like online stores, banks, or payment processors, but they are actually fake and created to steal sensitive information. When users visit these scam sites, they may be asked to provide personal information, such as their name, address, and credit card number, which can then be used for malicious purposes like identity theft.
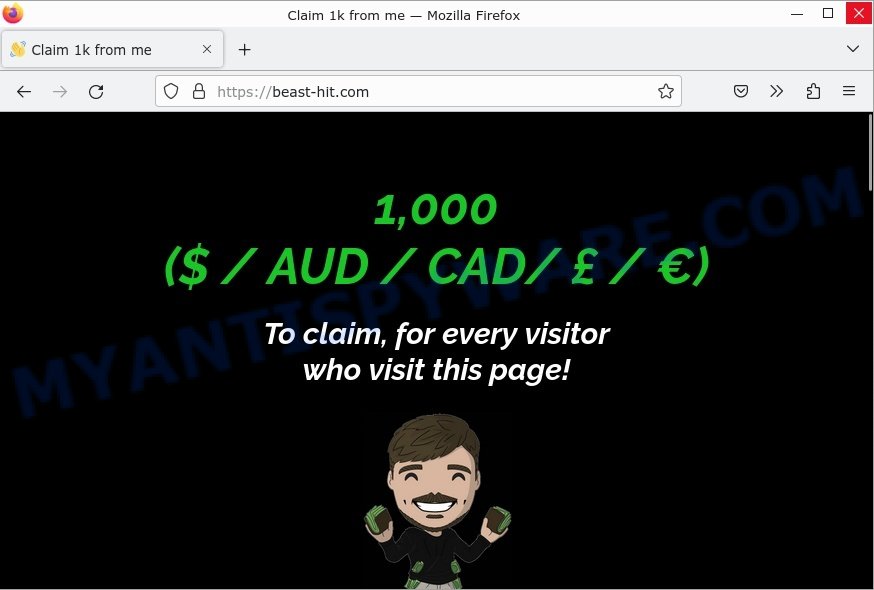
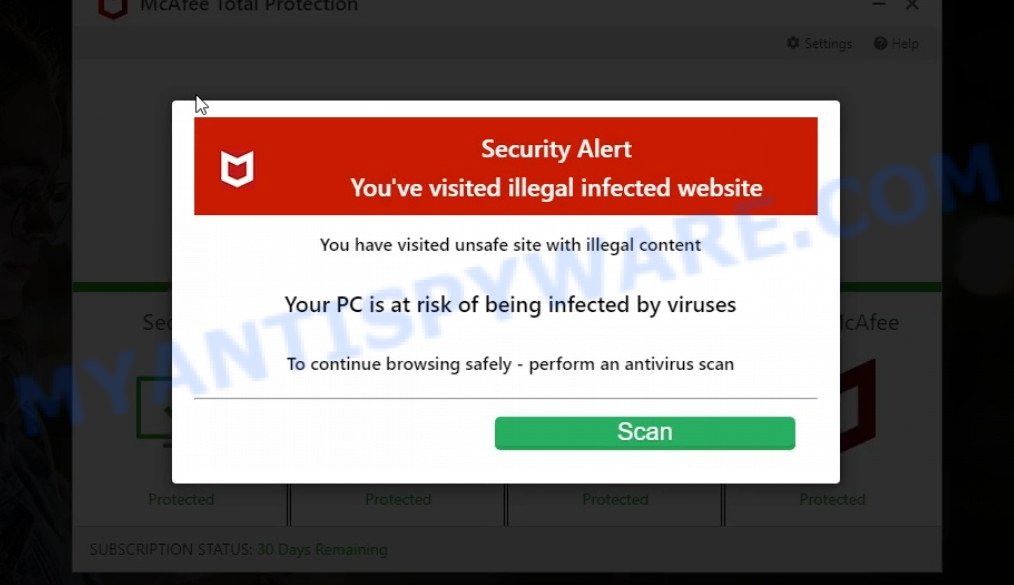
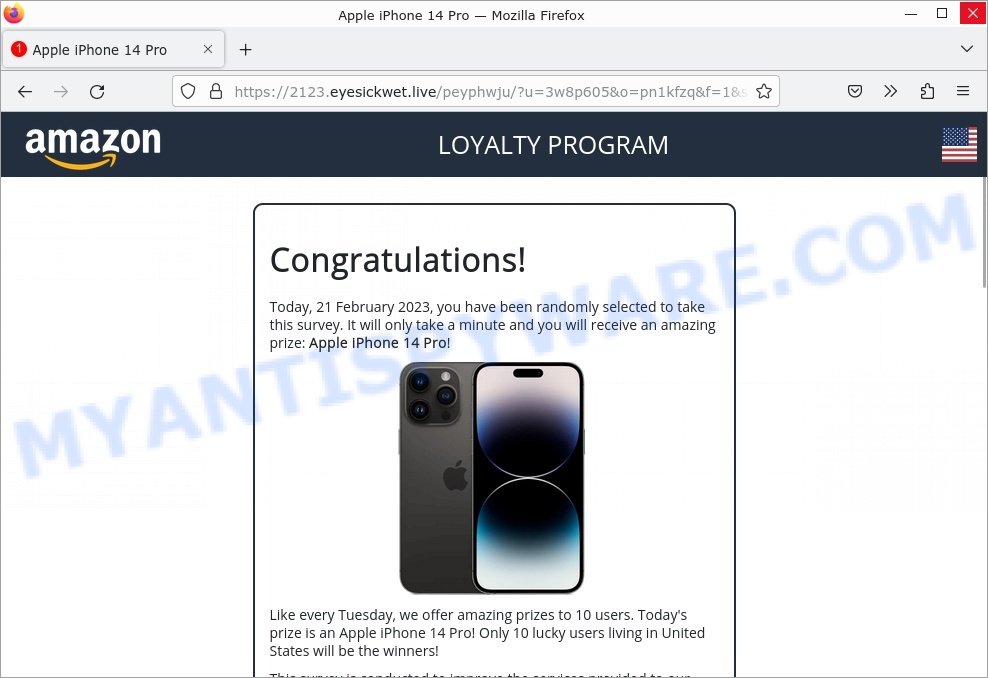
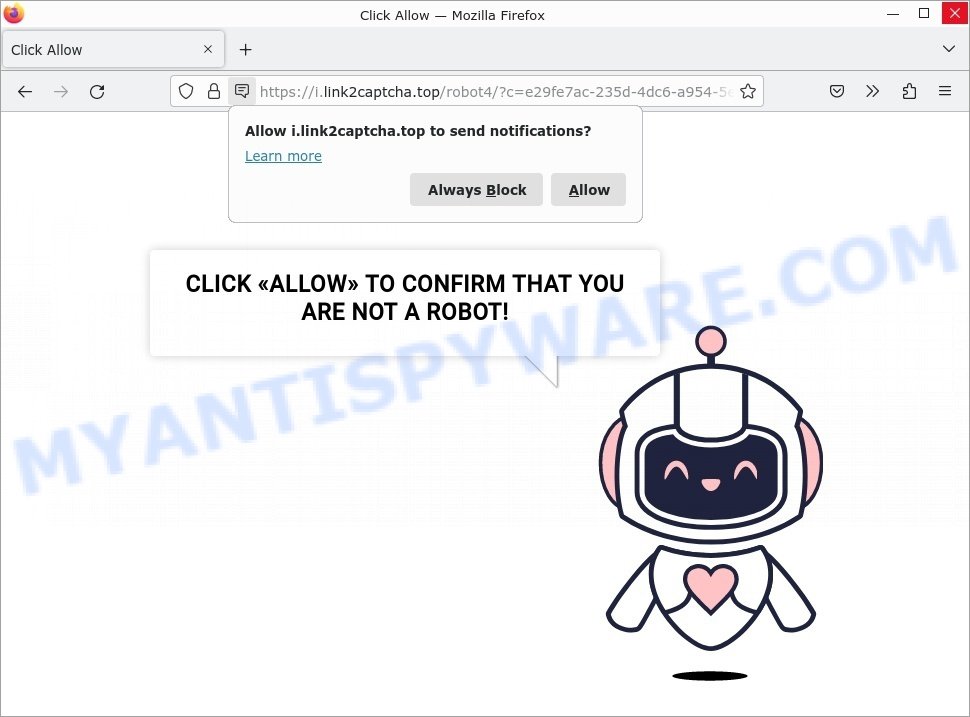
Below are some examples of scam websites:
- Beast-hit.com Claim 1k from me Scam
- Foylosd.xyz McAfee Scam
- Top Captcha Today Virus Amazon LOYALTY PROGRAM Scam
- Link 2captcha Virus Click Allow Scam
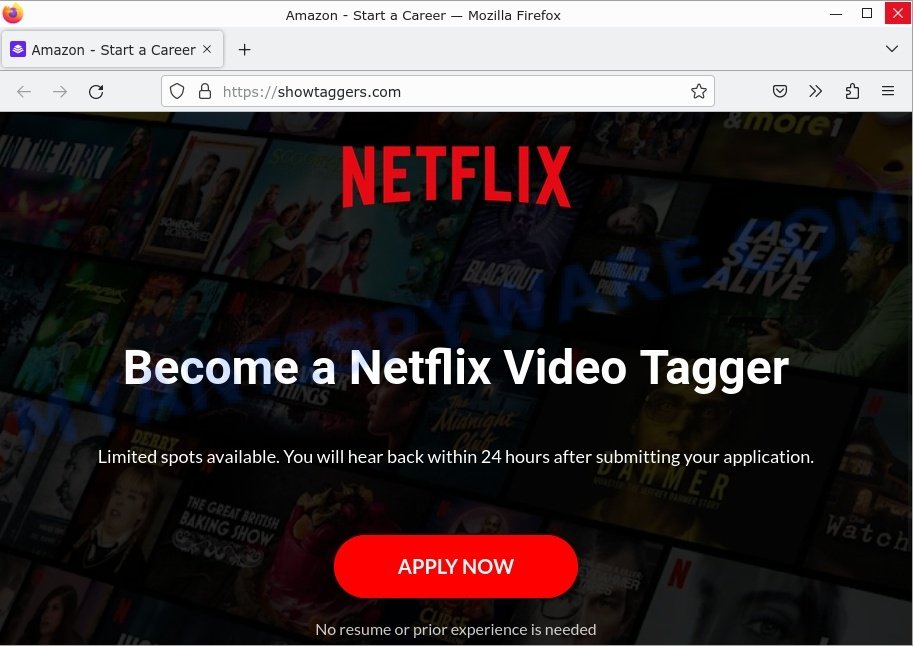
- Showtaggers.com Netflix Tag Career Scam
Browser hijackers can target all popular web browsers, including Google Chrome, Mozilla Firefox, Microsoft Edge (formerly Internet Explorer), Apple Safari, and others. No web browser is immune to browser hijacking, and all users are at risk of being affected by this type of malware.
In summary, Search.tablicious.com can have a significant impact on the user’s browsing experience and can make it difficult to navigate the web.
How did Search.tablicious.com get installed?
Fake search engines can be installed in a browser through several methods: software bundling, drive-by downloads, phishing scams, downloading from untrusted sources;
- When downloading and installing new software, the fake search engine may be included as a part of the package. If the user does not uncheck the installation of the fake search engine, it can be installed onto their browser.
- Drive-by downloads is a type of malware attack where the fake search engine is downloaded onto the user’s computer without their knowledge. This can happen when a user visits a compromised website or clicks on a malicious link.
- Phishing scams are attempts to steal sensitive information, such as login credentials, by posing as a trustworthy entity. A fake search engine may be installed on a user’s browser as part of a phishing scam.
- Downloading and installing software or browser extensions from untrusted sources, such as third-party websites, can also result in a fake search engine being installed.
It is important to be cautious when downloading and installing software and to only download from trusted sources to reduce the risk of a fake search engine being installed on a browser.
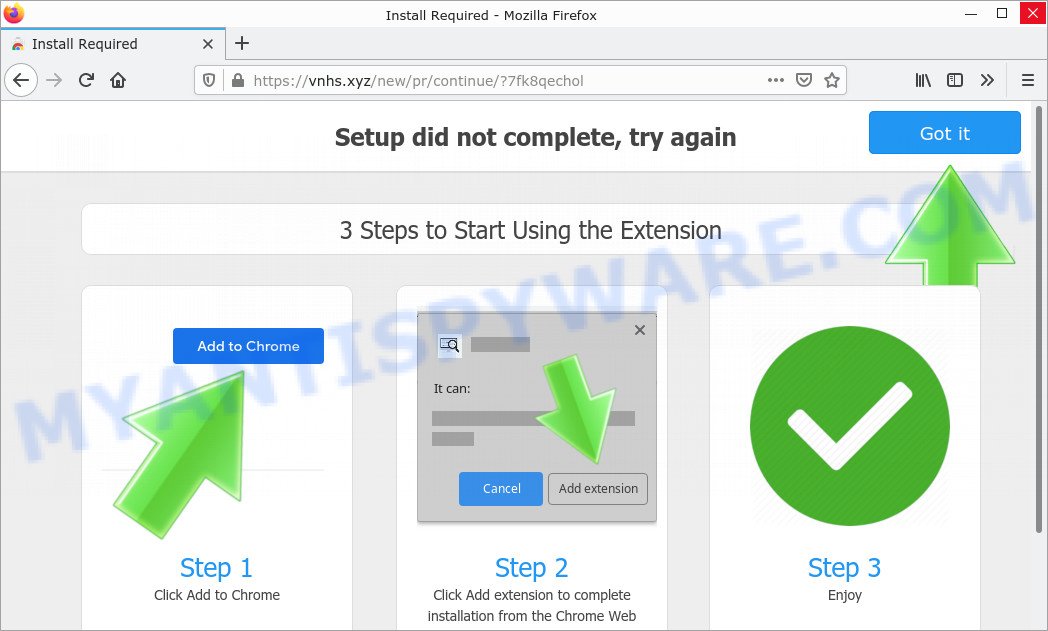
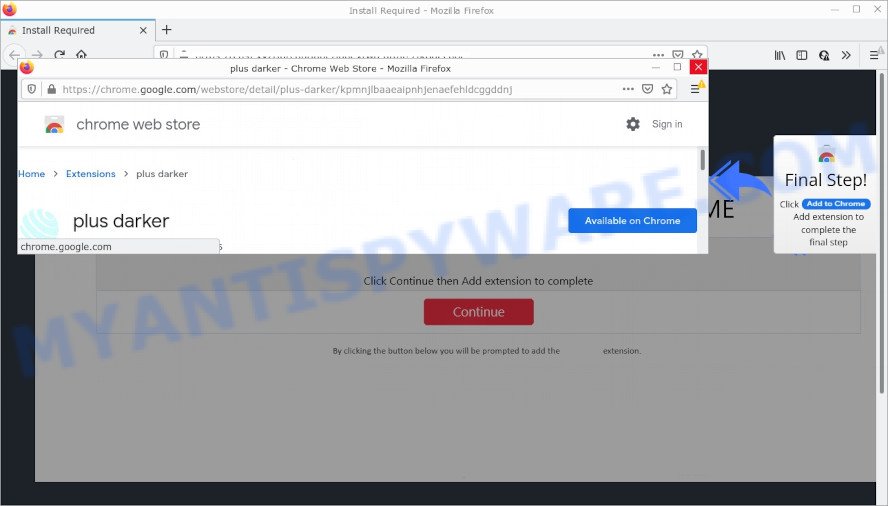
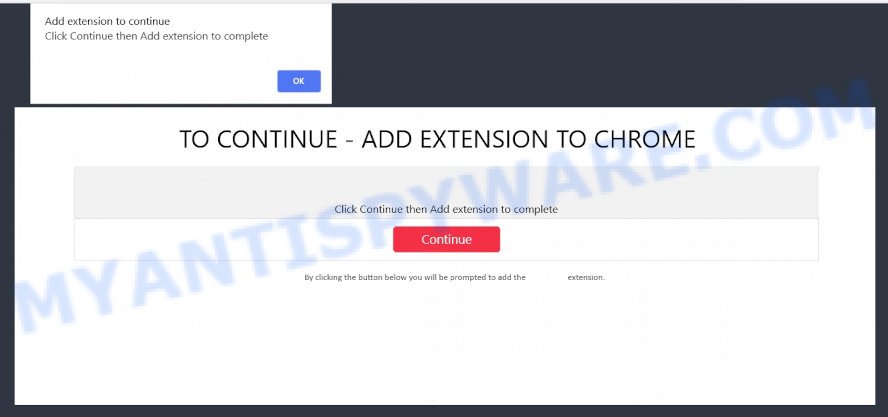
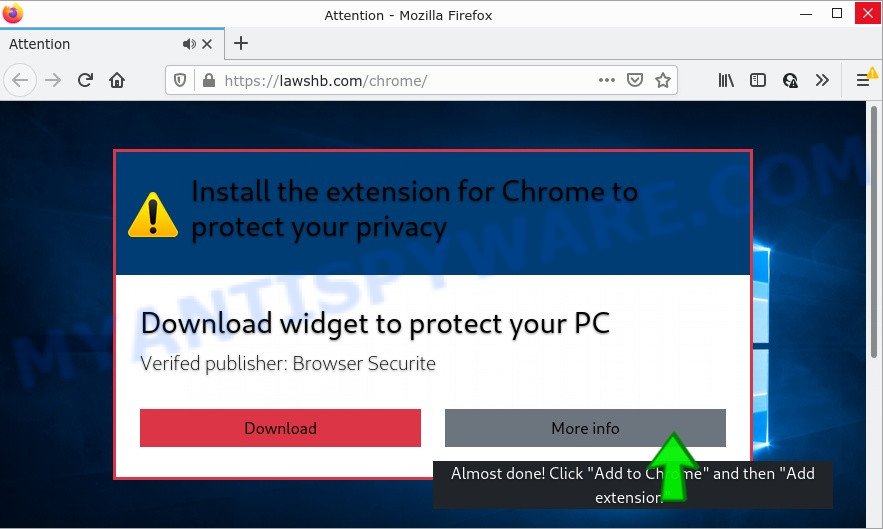
Examples of scam pages that are designed to trick users into installing browser hijackers and adware:
- TO CONTINUE – ADD EXTENSION TO CHROME pop-ups promote a browser hijacker
- “TO CONTINUE – ADD EXTENSION TO CHROME” POP-UP is a SCAM
- Install the extension for Chrome to protect your privacy POP-UPS are a SCAM
It’s important to be cautious when downloading software, especially free software from unknown sources, and to only install software from trusted sources.
Threat Summary
| Name | Search.tablicious.com, “Search.tablicious.com redirect”, “Search.tablicious.com PUP” |
| Type | browser hijacker, home page hijacker, PUP, search provider hijacker, redirect virus |
| Affected Browser Settings | home page, newtab page URL, search provider |
| Distribution | dubious popup ads, freeware installers, fake update tools |
| Damage | Privacy invasion: browser hijackers can collect and transmit personal information, such as search queries, browsing history, and login credentials; security risks: browser hijackers can expose the computer to other forms of malware; ad revenue generation: browser hijackers can display unwanted pop-up ads; performance degradation: browser hijackers can cause the affected web browser to become slow; altered search results: browser hijackers can alter search results to display sponsored or unwanted websites. |
| Symptoms | Changes to the homepage: browser hijackers may change the homepage of the affected web browser; changes to the default search engine: browser hijackers may change the default search engine of the affected web browser; new toolbars or extensions: browser hijacker may install new toolbars or extensions; pop-up ads: browser hijackers may cause the display of unwanted pop-up ads while the user is browsing the web; redirection to unfamiliar and scam websites; slow or unresponsive web browser. |
| Removal | If you experience any of these symptoms above, it is a sign that your web browser has been hijacked. To remove the hijacker, Search.tablicious.com removal guide |
Examples of Browser hijackers
Browser hijackers can be used to distribute other malware. They install trojans, adware, keyloggers, ransomware, spyware and more. Some of the malware designed to collect user data, others install ransomware and trojans on computers, and still others add infected computers to botnets, and so on. In any case, each malicious program is a huge threat to both user privacy and computer security. Therefore, malicious programs must be removed immediately after detection; using an infected computer is very dangerous.
More examples of browser hijackers are below:
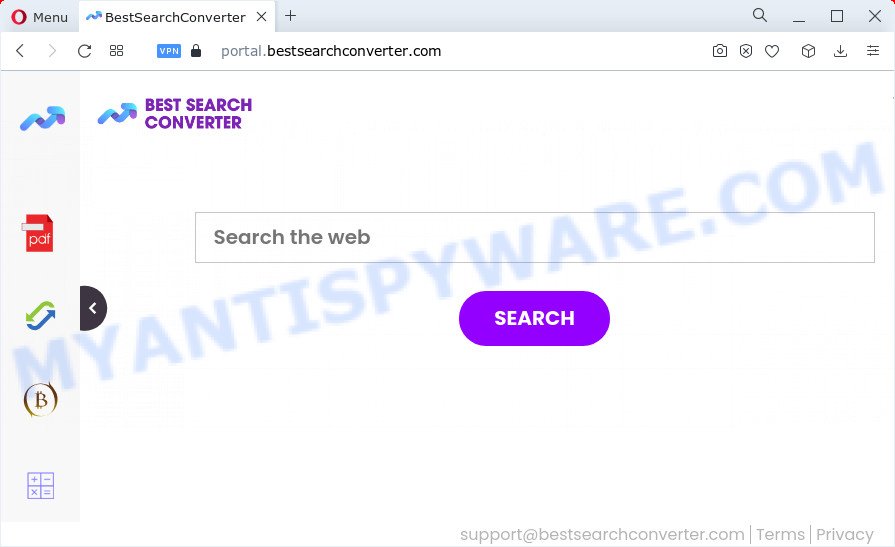
- BestSearchConverter is a hijacker
- Media Tab browser hijacker
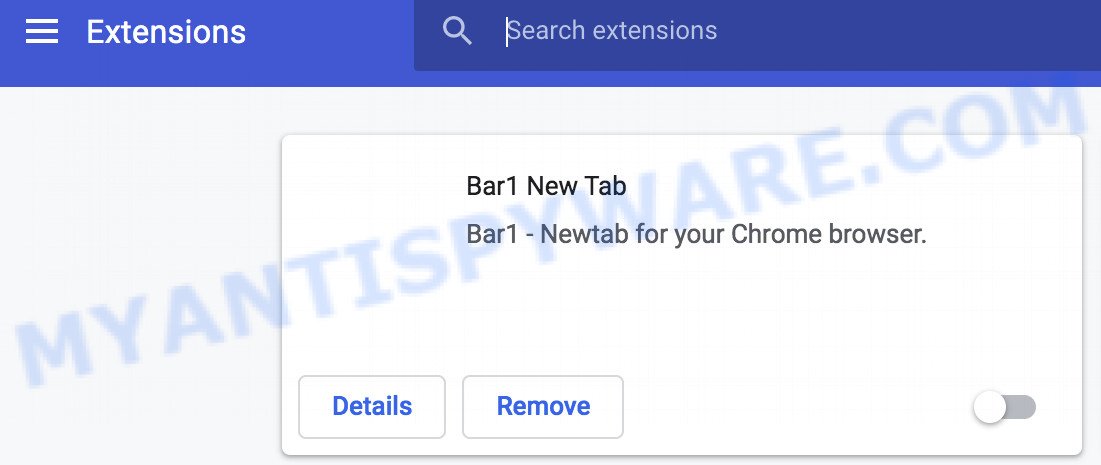
- Bar1 New Tab is a browser hijacker
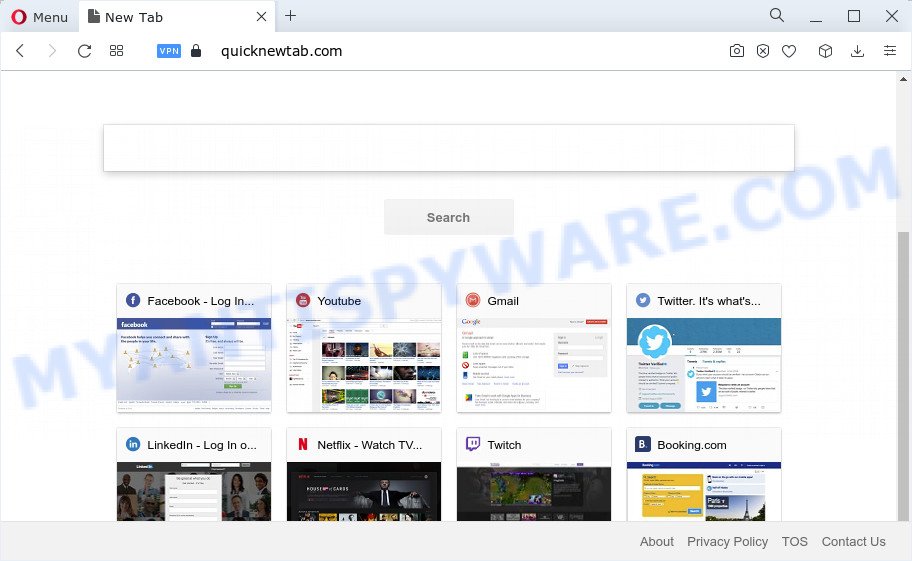
- Quick App is a browser hijacker
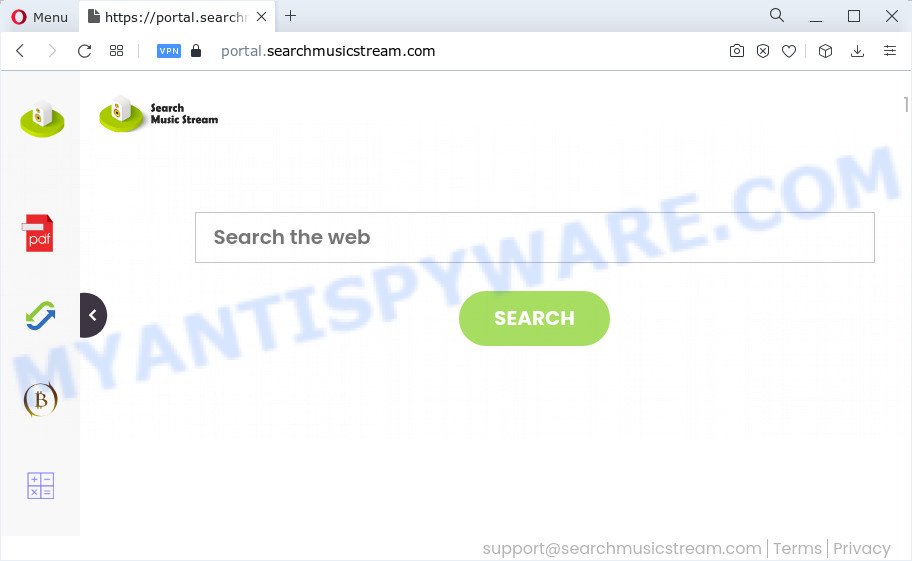
- SearchMusicStream is a browser hijacker
How to remove Search.tablicious.com from Windows 11 (10, 8, 7, XP)
To remove Search.tablicious.com from your browser, go to the browser’s extensions or add-ons settings and uninstall any suspicious extensions. Then, change the default search engine in the browser’s settings to a trusted source such as Google or Bing. If the fake search engine is still present, reset the browser to its default settings. Additionally, it’s important to scan your computer for malware using an antivirus program.
If you have any questions or need help, write a comment below. Some steps will require you to restart your device or exit this web page. So, read this guide carefully and then bookmark this page or open it on your smartphone for future reference.
To remove Search.tablicious.com, perform the steps below:
- Uninstall Search.tablicious.com associated software
- Remove Search.tablicious.com hijacker from web-browsers
- Automatic Removal of Search.tablicious.com
- How to stop Search.tablicious.com redirect
Read this section to know how to manually remove the Search.tablicious.com hijacker. Even if the step-by-step guide does not work for you, there are several free removers below which can easily handle such hijackers.
Uninstall Search.tablicious.com associated software
Check the list of installed programs on your computer and delete any that you did not intentionally install. Some browser hijackers can be installed as part of a software bundle.
|
|
|
|
Remove Search.tablicious.com hijacker from web-browsers
If you are still seeing Search.tablicious.com that won’t go away, you might have malicious addons installed on your web browser. Check your web browser for unwanted add-ons using the steps below.
You can also try to remove Search.tablicious.com hijacker by reset Chrome settings. |
If you are still experiencing issues with Search.tablicious.com removal, you need to reset Mozilla Firefox browser. |
Another method to get rid of Search.tablicious.com hijacker from Internet Explorer is reset Internet Explorer settings. |
|
Automatic Removal of Search.tablicious.com
Antivirus software is a great method to remove browser hijackers because it’s designed to detect and remove malicious software, including browser hijackers. The software uses a database of known threats and virus definitions to identify and remove any malicious software that is present on your computer.
Additionally, antivirus software has the ability to scan your entire computer, including all files and system areas, to detect and remove any hidden or persistent threats. This is important because browser hijackers can often hide themselves and change system settings to make them difficult to remove.
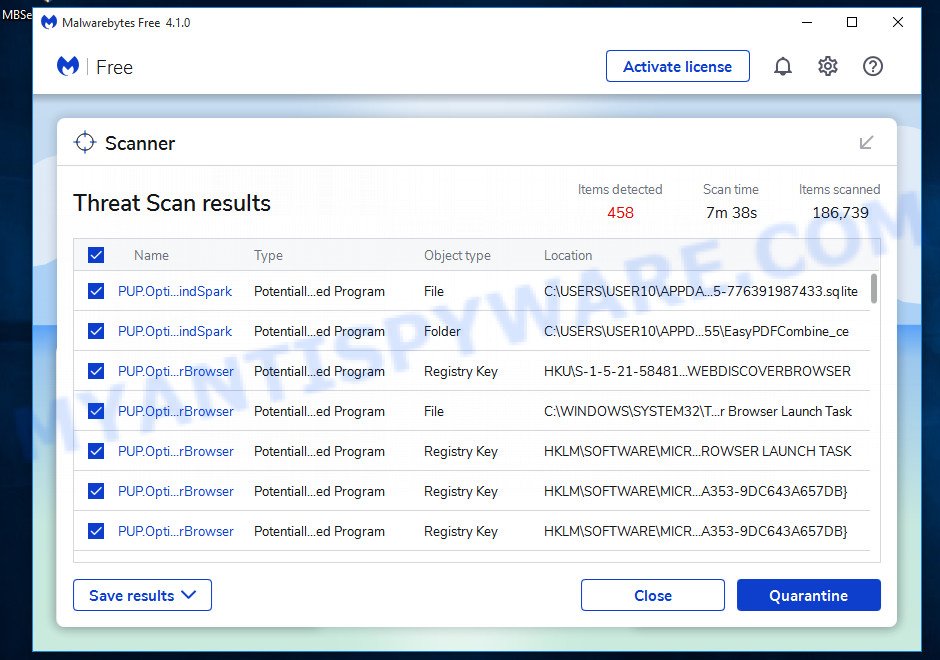
How to remove Search.tablicious.com with MalwareBytes Anti-Malware
You can automatically get rid of the browser hijacker with MalwareBytes Anti-Malware. We recommend this free malware removal tool because it can easily remove hijackers, adware, potentially unwanted programs and toolbars with all their components such as files, folders and registry entries.
- Install and update antivirus and anti-malware software: Choose a reliable and up-to-date antivirus and anti-malware software, such as Malwarebytes. Download it by clicking on the link below. Save it on your Windows desktop.
Malwarebytes Anti-malware
327299 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
- Once the download is done, close all applications and windows on your personal computer. Open a folder in which you saved it. Double-click on the icon that’s named MBsetup.
- Choose “Personal computer” option and press Install button. Follow the prompts.
- Once installation is finished, scan your computer. Run a full scan of your computer to detect and remove any browser hijackers and other forms of malware. The scan may take several minutes to complete, depending on the size of your hard drive and the speed of your computer.
- Remove detected threats. If the scan finds any threats, click Quarantine to remove them. The software will automatically remove the browser hijacker and any associated malware. After the removal process is complete, restart your computer to ensure that any changes made by the hijacker are fully removed.
The following video demonstrates how to remove hijackers, adware and other malware with MalwareBytes.
How to remove Search.tablicious.com with Zemana
Zemana Anti-Malware is highly recommended because it can detect security threats such as hijackers and adware that most “classic” anti-malware applications cannot detect. Moreover, if you have any problems with Search.tablicious.com hijacker removal that cannot be fixed by this utility automatically, Zemana provides 24/7 online help from highly trained support staff.
Now you can install and use Zemana AntiMalware to get rid of Search.tablicious.com hijacker from your internet browser by following the steps below:
Visit the following page to download Zemana setup file called Zemana.AntiMalware.Setup on your computer. Save it on your Windows desktop or in any other place.
165079 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
Start the installation package after it has been downloaded successfully and then follow the prompts to set up this tool on your computer.
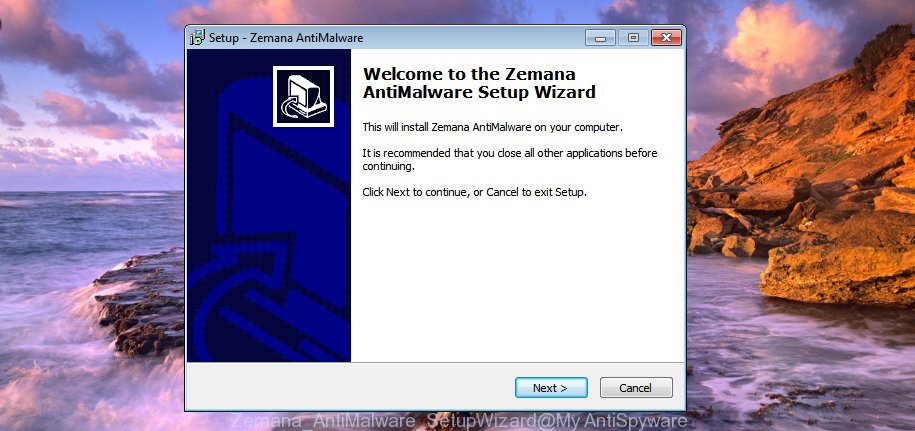
During installation you can change some settings, but we suggest you do not make any changes to default settings.
When setup is complete, this malicious software removal tool will automatically start and update itself. You will see its main window as displayed in the following example.

Now click the “Scan” button for scanning your computer for the Search.tablicious.com hijacker. While Zemana AntiMalware is scanning, you can see number of objects it has identified either as being malware.

Once Zemana AntiMalware has completed scanning your PC, it will open the Scan Results. Next, you need to click “Next” button.
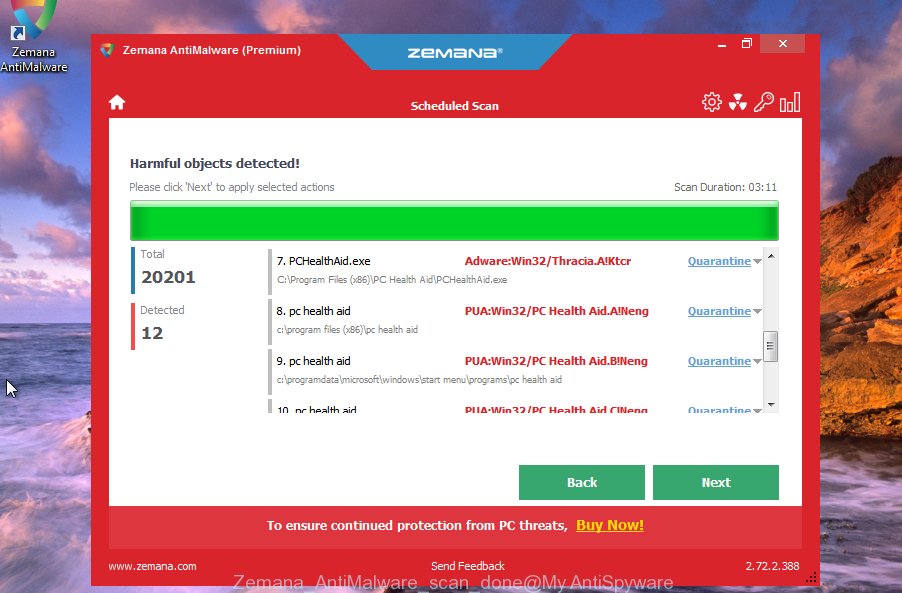
The Zemana AntiMalware will start to remove Search.tablicious.com hijacker. After that process is complete, you can be prompted to restart your computer to make the change take effect.
Remove Search.tablicious.com hijacker and malicious extensions with Hitman Pro
Hitman Pro is one of the most useful tools for deleting hijackers, adware software, potentially unwanted programs and other malware. It can scan for hidden malware in your device and delete all malicious folders and files linked to hijacker. Hitman Pro will help you to get rid of Search.tablicious.com from your personal computer and Firefox, Chrome, IE and Edge. We strongly advise you to download this utility as the creators are working hard to make it better.
Installing the Hitman Pro is simple. First you’ll need to download Hitman Pro by clicking on the link below.
Download and use Hitman Pro on your computer. Once started, press “Next” button for scanning your personal computer for the Search.tablicious.com hijacker. Depending on your computer, the scan can take anywhere from a few minutes to close to an hour. While the Hitman Pro is scanning, you can see count of objects it has identified either as being malware..
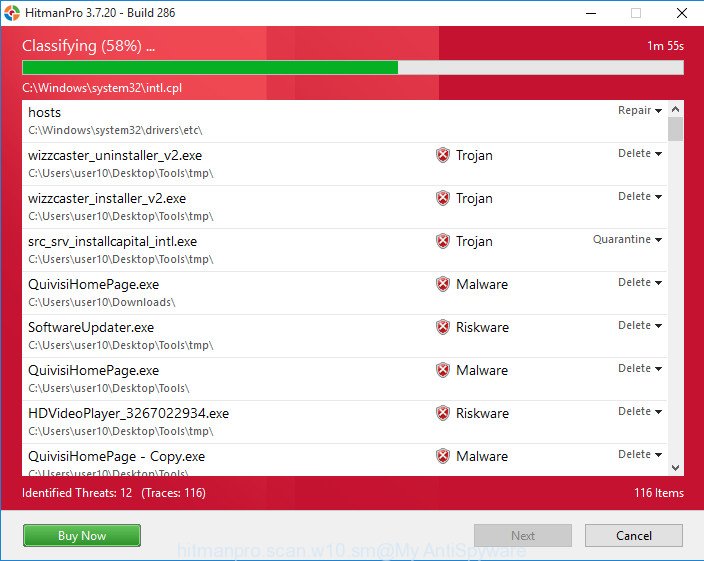
When HitmanPro has completed scanning your computer, HitmanPro will show a list of all threats found by the scan.
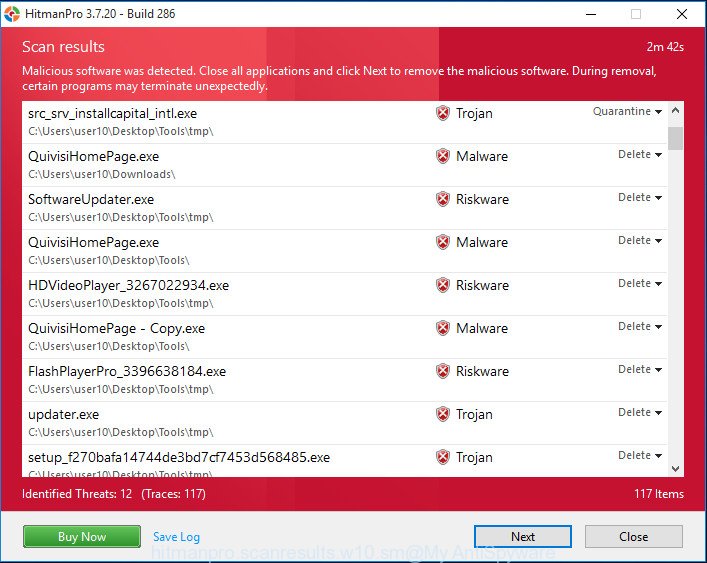
You may remove threats (move to Quarantine) by simply press Next button.
It will display a prompt, press the “Activate free license” button to start the free 30 days trial to remove all malware found.
How to stop Search.tablicious.com redirect
We suggest to install an adblocker program which can block scam pages and malicious browser redirects. The ad blocker utility such as AdGuard is a program which basically removes advertising from the Internet and stops access to malicious websites. Moreover, security experts says that using ad-blocking apps is necessary to stay safe when surfing the World Wide Web.
Visit the page linked below to download the latest version of AdGuard for MS Windows. Save it to your Desktop so that you can access the file easily.
26906 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, start the downloaded file. You will see the “Setup Wizard” screen as shown on the image below.
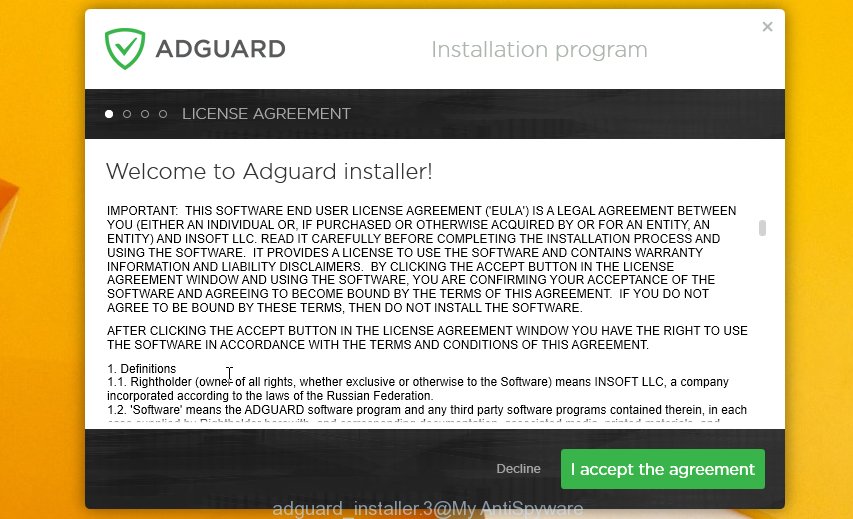
Follow the prompts. After the installation is finished, you will see a window as displayed in the following example.

You can click “Skip” to close the setup program and use the default settings, or click “Get Started” button to see an quick tutorial that will assist you get to know AdGuard better.
In most cases, the default settings are enough and you don’t need to change anything. Each time, when you start your computer, AdGuard will launch automatically and stop unwanted ads, block malicious and misleading websites. For an overview of all the features of the program, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
Once you have removed the hijacker using the few simple steps, MS Edge, Google Chrome, Mozilla Firefox and Internet Explorer will no longer redirect you to the Search.tablicious.com page. Unfortunately, if the few simple steps does not help you, then you have caught a new hijacker, and then the best way – ask for help.
Please create a new question by using the “Ask Question” button in the Questions and Answers. Try to give us some details about your problems, so we can try to help you more accurately. Wait for one of our trained “Security Team” or Site Administrator to provide you with knowledgeable assistance tailored to your problem with the Search.tablicious.com hijacker.