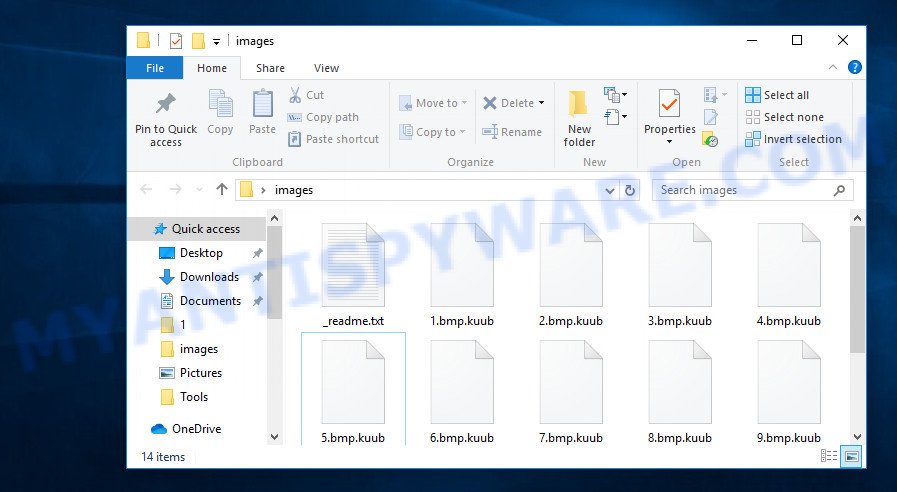
What is a .Kuub file extension? The ‘Kuub file extension’ at the end of your file names is an indication that these files have been encrypted. This confirms the message that the security expert posted on his Twitter account here.

Ransomware extension “.kuub” (v0169) spotted on ID Ransomware.
The ‘ID Ransomware’ is a site where victims can inform experts about a ransomware infection and get additional information about the ransomware. Thus, you are not the first to become a victim of this virus, many people around the world have faced the same problem and found these .Kuub files on their computer. There is bad and good news here. The bad news is that at the moment you cannot decrypt files, neither antivirus companies nor experts can help you with this. There is good news, the virus can be found and removed, and in addition, there is a chance to restore the encrypted .Kuub files to their normal state. Further in our article we will tell you how to remove a ransomware and restore encrypted files.
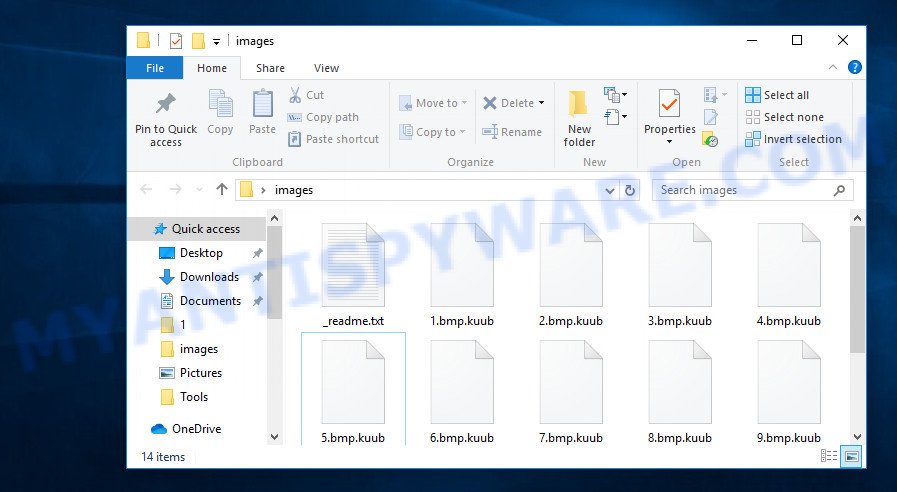
Files with the ‘.kuub’ extension are encrypted files
Even if you rename files, just delete ‘.Kuub’ from their name, then this will not help you. All the same, these files cannot be opened by the programs that you used to work with them. If you find files with this extension, then you should also find files with the name ‘_readme.txt’ or ‘_readme’. Such files were created by the virus automatically, in every directory where at least one encrypted file is present. Below you can find the contents of such a file.
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-JeLOm18e5g
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gerentoshelp@firemail.ccYour personal ID:
0169#####################################################
Despite the fact that the ‘Kuub’ virus is already the 169th version of one ransomware, the message that the attackers leave is almost unchanged. The main meaning of this message can be reduced to one: pay a ransom to decrypt the files. To obtain the wallet address where the ransom must be transferred, as well as confirm the possibility of decrypting the files, the victim must write an email letter to the authors of the virus. Of course, there is no guarantee that even if the victim pays the ransom, he will receive the necessary key and program that will decrypt the files. Obviously, attackers can simply ignore the victim’s requests, or dramatically increase the size of the ransom.
Threat Summary
| Name | Kuub ransomware |
| Type | File locker, Filecoder, Crypto virus, Crypto malware, Ransomware |
| Encrypted files extension | .kuub |
| Ransom note | _readme.txt |
| Contact | gorentos@bitmessage.ch, gerentoshelp@firemail.cc |
| Ransom amount | $980 in Bitcoins |
| Symptoms | Your documents, photos and music fail to open. Your photos, documents and music have new extension appended at the end of the file name. Files named like ‘_readme.txt’, ‘#_README_#’, ‘_DECRYPT_’ or ‘recover’ in each folder with at least one encrypted file. |
| Distribution ways | Phishing emails that contain malicious attachments. Malicious downloads that happen without a user’s knowledge when they visit a compromised website. Social media, such as web-based instant messaging programs. USB key and other removable media. |
| Removal | To remove Kuub ransomware use the removal guide |
| Decryption | To decrypt Kuub ransomware use the steps |
In addition to the fact that all versions of the ransomware have the same ransom message, they use the one way to infect the computer and encrypt the files on it. Most often, the Kuub ransomware is built into the installers of hacked or free programs that are located on various suspicious sites. When the computer user launches such a file, the ransomware copies itself to one of the system directories, after which it begins its harmful actions on the infected computer. The virus detects all available disks (including network drives), after which disk by disk, directory by directory, file by file encrypts all files available to it. When all the files are encrypted in the directory, the virus creates a file with the name ‘_readme.txt’, we talked about this file above. The Kuub ransomware can encrypt almost all files. Most often, ransomware leaves only important system files unencrypted, all the rest are encrypted. That is, the virus can encrypt almost all files, including files with the following extensions:
.rwl, .3dm, .mrwref, .pdd, .xf, .wbmp, .wma, .xdb, .wp7, .wmd, .sb, .wbd, .x, .doc, .xx, .crt, .itdb, .der, .tor, .bc7, .wn, .ptx, .layout, .dwg, .jpe, .wps, .pst, .xls, .xmmap, .r3d, .dba, .rim, .indd, .psk, .cas, .wot, .css, .ibank, .asset, .epk, .rar, .x3f, .w3x, .2bp, .bar, .yal, .zdc, .wire, .t13, .wmv, .jpeg, .sum, .qic, .wbc, .psd, .crw, .dxg, .xyw, .itm, .srf, .xls, .odt, .wri, .apk, .tax, .wbz, .sql, .re4, .bc6, .slm, .cr2, .bkp, .qdf, .rtf, .mddata, .xar, .dcr, .wdb, .iwi, .1st, .wm, .vpp_pc, .hkdb, .odm, .sid, .wpb, .hplg, .wpw, .sie, .odp, .syncdb, .3ds, .wsc, .ws, .docx, .cdr, .wsh, .mcmeta, .sav, .xpm, .mov, .xbdoc, .webp, .jpg, .vfs0, .wpg, .rofl, .bay, .wps, .snx, .raw, .menu, .mef, .p12, .xlsx, .erf, .ysp, .blob, .xlgc, .txt, .hkx, .xbplate, .gho, .flv, .ppt, .wp6, .7z, .zip, .m2, .x3d, .eps, .itl, .webdoc, .sis, .wp4, .mdb, .vpk, .bkf, .zw, .das, .arch00, .xlsm, .avi, .dazip, .zi, .cer, .1, .icxs, .0, .big, .xxx, .png, .wdp, .kdc, .srw, .dmp, .mp4, .mlx, .xll, .dng, .mdf, .zdb, .wpe, .d3dbsp, .zip, wallet, .esm, .wma, .sr2, .wsd, .py, .wpa, .t12, .arw, .svg, .xdl, .wav, .xlk, .vdf, .lbf, .rw2, .pef, .cfr, .ai, .wmo, .js, .xlsx, .upk, .3fr, .wbm, .wbk, .dbf, .wcf, .p7b, .xlsm, .docm, .accdb, .ntl, .x3f
Although the ransomware uses the same encryption method on all infected computers, the authors of the virus use an unique key on each computer to encrypt files, which eliminates the possibility for victims to use the same key to decrypt files. That is, if someone bought the key, having paid the ransom, this key will not work on other computers. Each computer needs an unique key. But do not despair, although the key cannot be obtained without paying the ransom, there is a small chance to return all the files. Below we will describe in detail how to do this.
How to remove Kuub ransomware and restore encrypted files
If, you or your friends became a victim of this ransomware, then, as we said above, there is the opportunity to find and remove the virus. Then you can try to restore the encrypted files and the state that they had before they were blocked by the virus.
Remove Kuub ransomware virus
If your computer has become a victim of this ransomware, then the first thing you need to do is find it and delete it. It is very difficult to do this manually, because the virus can place its files in different system directories; moreover, these files often do not have fixed names. Therefore, we recommend using programs that are specifically designed to search for and remove malware. We suggest you use the following malware removal tools: Zemana Anti-malware, Hitman Pro and Kaspersky Virus Removal Tool. Once again we want to repeat, be sure to check the computer for malware before proceeding with file recovery.
How to remove Kuub virus with Zemana AntiMalware
First of all, we suggest you use the program, which is called Zemana AntiMalware. This program has a small size, simple interface and a powerful scanner that will allow you to fully scan your computer. If malware is found during the scanning process, then you can easily remove it simply by pressing a single key (for free). You do not need to buy its full version. This program can work with an already installed antivirus without causing any conflicts.
Zemana can be downloaded from the following link. Save it to your Desktop so that you can access the file easily.
165094 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
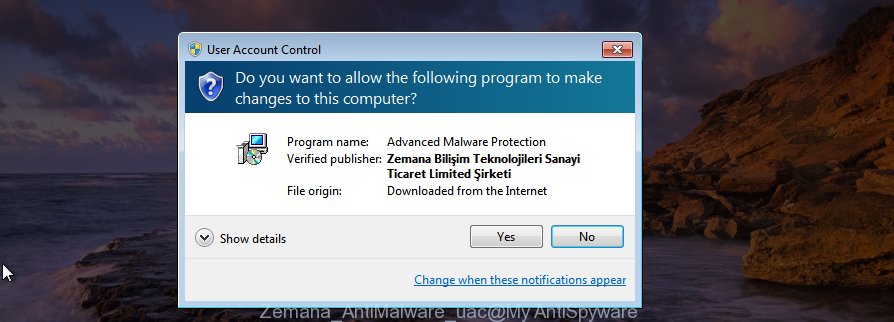
When downloading is complete, close all windows on your system. Further, open the setup file called Zemana.AntiMalware.Setup. If the “User Account Control” prompt pops up similar to the one below, click the “Yes” button.
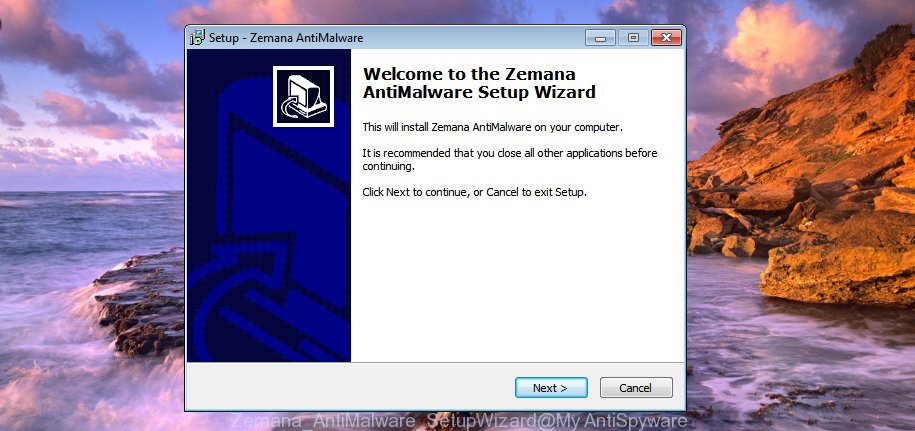
It will display the “Setup wizard” that will assist you install Zemana Anti-Malware (ZAM) on the computer. Follow the prompts and do not make any changes to default settings.
Once installation is finished successfully, Zemana AntiMalware (ZAM) will automatically launch and you may see its main window as on the image below.

Next, click the “Scan” button to begin checking your computer for the Kuub crypto virus, other malware, worms and trojans. Depending on your PC system, the scan can take anywhere from a few minutes to close to an hour.

When the scan get completed, Zemana Free will display you the results. Make sure all threats have ‘checkmark’ and press “Next” button.
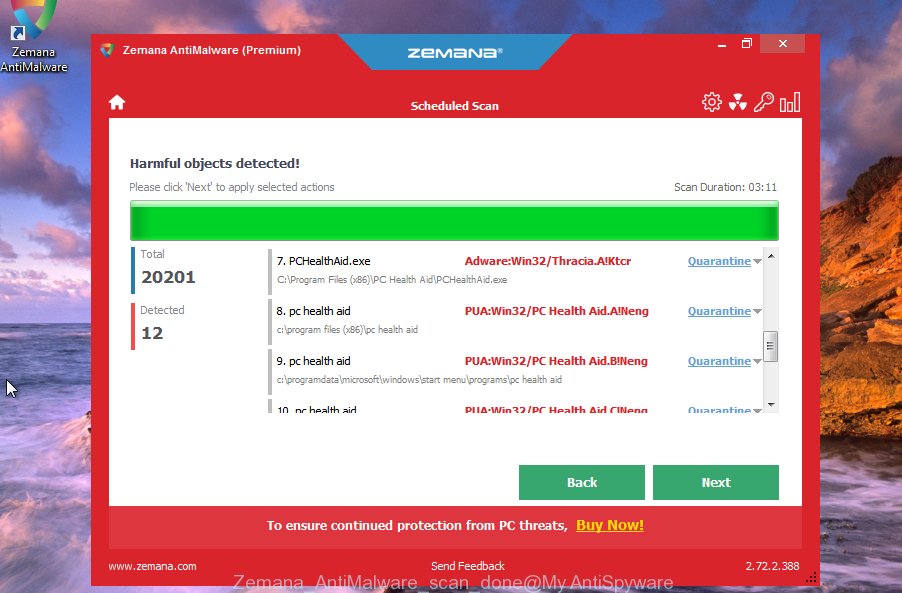
The Zemana Free will delete Kuub crypto malware, other kinds of potential threats like malicious software and trojans and move threats to the program’s quarantine. Once disinfection is done, you can be prompted to reboot your machine.
Run Hitman Pro to remove Kuub ransomware virus
Hitman Pro is a portable program which requires no hard setup to identify and delete Kuub ransomware. The application itself is small in size (only a few Mb). Hitman Pro does not need any drivers and special dlls. It’s probably easier to use than any alternative malicious software removal utilities you have ever tried. Hitman Pro works on 64 and 32-bit versions of Microsoft Windows 10, 8, 7 and XP. It proves that removal tool can be just as effective as the widely known antivirus programs.
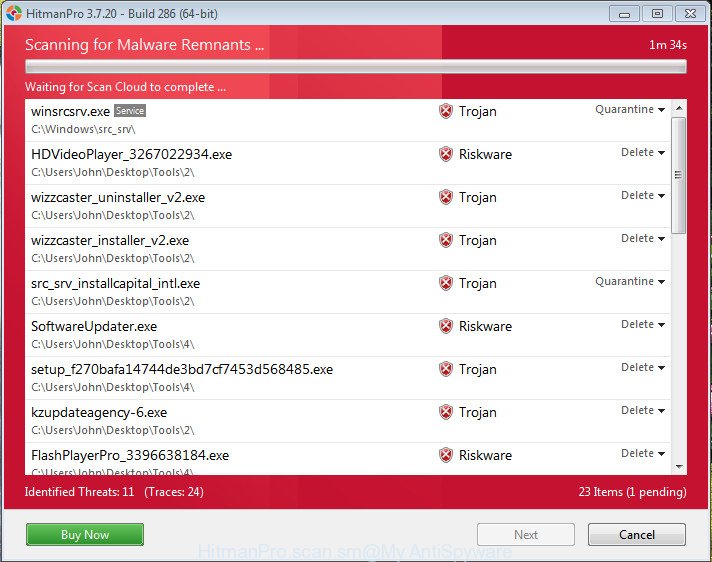
- HitmanPro can be downloaded from the following link. Save it to your Desktop so that you can access the file easily.
- When the download is finished, double click the Hitman Pro icon. Once this tool is launched, press “Next” button to perform a system scan for the Kuub virus. Depending on your machine, the scan can take anywhere from a few minutes to close to an hour. While the tool is scanning, you can see how many objects and files has already scanned.
- When the system scan is finished, Hitman Pro will prepare a list of ransomware. Next, you need to click “Next” button. Now click the “Activate free license” button to start the free 30 days trial to get rid of all malware found.
Double-check for ransomware with Kaspersky Virus Removal Tool
Kaspersky Virus Removal Tool (KVRT) is a free removal tool that can be downloaded and use to delete ransomware, trojans, worms, spyware and other malware from your PC. You can use this utility to scan for threats even if you have an antivirus or any other security program.
Download Kaspersky virus removal tool (KVRT) on your system by clicking on the following link.
129312 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
Once the download is finished, double-click on the Kaspersky virus removal tool icon. Once initialization procedure is finished, you will see the KVRT screen as on the image below.
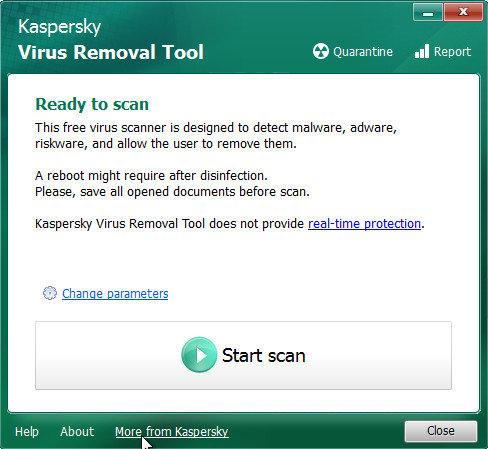
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next click Start scan button to scan for Kuub ransomware virus . This procedure can take quite a while, so please be patient. While the tool is checking, you can see how many objects and files has already scanned.
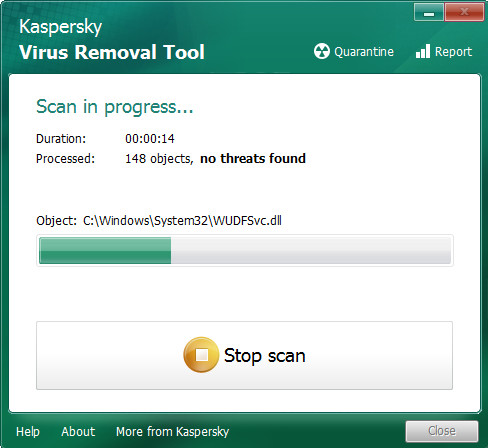
As the scanning ends, you’ll be displayed the list of all found items on your computer as displayed in the figure below.
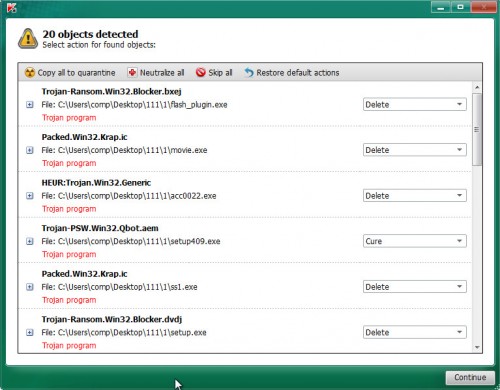
When you are ready, click on Continue to start a cleaning procedure.
Is it possible to decrypt .kuub files?
Although this virus is already the 169th version of one ransomware, at the moment there is no way to decrypt the locked data. Both anti-virus companies and experts will not help in this. The reason for this is that the virus uses a very strong encryption system. it’s almost impossible to find a decryption key or crack it. Therefore, the only way to get the key is to pay a ransom. Of course, you need to understand that when paying a ransom, the victim only pushes attackers to develop new viruses.

Never pay the ransom! Any expert will say this and repeat it again, again and again. Despite the fact that the files are encrypted and cannot be decrypted now, there is always a chance that sooner or later there will be a way to decrypt all the files. Antivirus companies are constantly on the lookout for a 100% way to help everyone who has been affected by this ransomware.
Files with the ‘.kuub’ extension are encrypted files
There is some good news. For some previous versions of this ransomware, experts have found a way to recover some of the encrypted files. This is possible due to the method that the virus uses to encrypt files. When a virus detects that a computer is disconnected from the network, it uses an offline key for encryption. This key is one for all users. Therefore, there is a hope that, in your case, the files are encrypted with an offline key and you just need to wait a bit to be able to decrypt .kuub files. Of course, as soon as an offline key is found we will report in this article.
Update: A few days ago a free decryptor was released. Below I provide a link where you will find detailed information on where to download it and how to use it to decrypt .kuub files.
STOP Djvu Ransomware Decryptor – Free way to decrypt encrypted files
How to restore .kuub files
Although you cannot decrypt files, there is a small chance that you will be able to restore the encrypted files to the state they were in before encryption. It doesn’t need any ‘magic’ tools or super computer specialists, we recommend that you use programs that are designed to find and recover deleted and lost files. Our experts recommend using programs called PhotoRec and ShadowExplorer. These are 100% proven utilities that have already repeatedly helped the victims of ransomware recover encrypted files. We want to add the following, the less you used your computer before restoring files, the higher the chance that you will be able to restore them. You can even remove the disk from the infected computer, connect it to another computer and start the file recovery process from it. Be sure to check the computer for ransomware before starting the file recovery procedure!
Use ShadowExplorer to recover .kuub files
In some cases, you have a chance to restore your documents, photos and music which were encrypted by the Kuub ransomware. This is possible due to the use of the tool called ShadowExplorer. It is a free program that created to obtain ‘shadow copies’ of files. Unfortunately, it very often happens that a virus deletes all ‘shadow copies’ of files. As a result, the program will not be able to find copies of your files created before the virus started the encryption process. Nevertheless, be sure to try this method, as the ransomware for some reason may not delete the shadow copies, and you can quickly restore your files.
Download ShadowExplorer by clicking on the link below.
439713 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
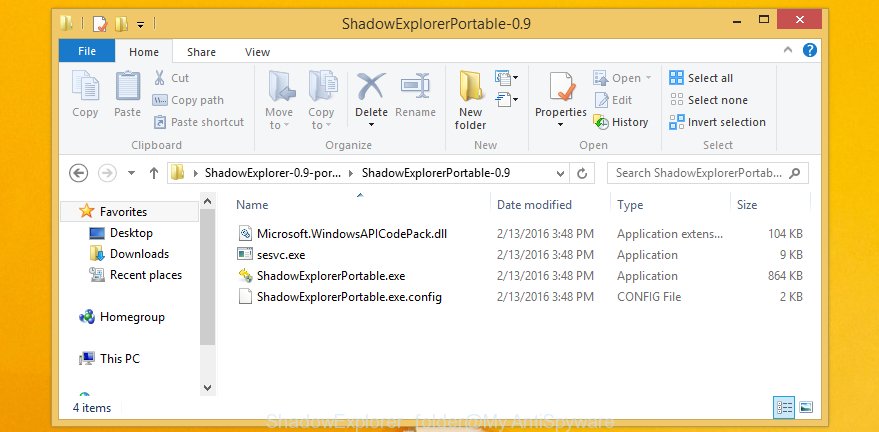
When the download is complete, open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and select Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder like below.
Double click ShadowExplorerPortable to run it. You will see the a window as on the image below.
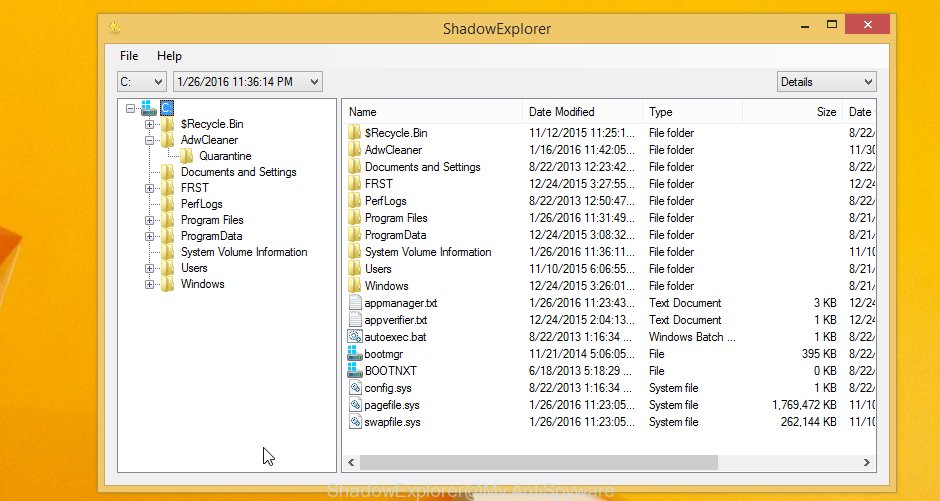
In top left corner, select a Drive where encrypted documents, photos and music are stored and a latest restore point like below (1 – drive, 2 – restore point).
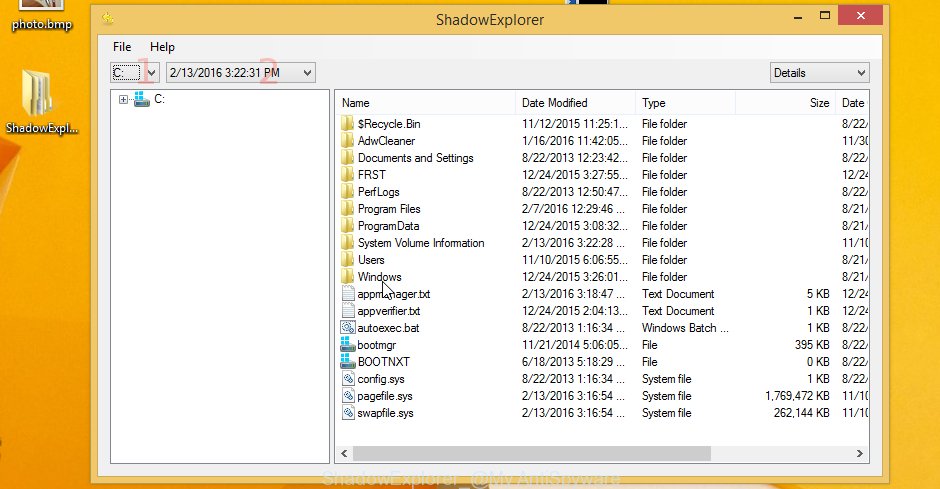
On right panel look for a file that you want to restore, right click to it and select Export as displayed in the following example.

Use PhotoRec to restore .kuub files
Another way to recover files is to use a tool that finds deleted files and restores them. This method is based on the fact that the OS does not physically delete files, but simply marks them as deleted. The PhotoRec finds such files and restores them.
Download PhotoRec from the link below.
When the download is complete, open a directory in which you saved it. Right click to testdisk-7.0.win and select Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as shown in the following example.

Double click on qphotorec_win to run PhotoRec for Windows. It will show a screen as displayed in the figure below.
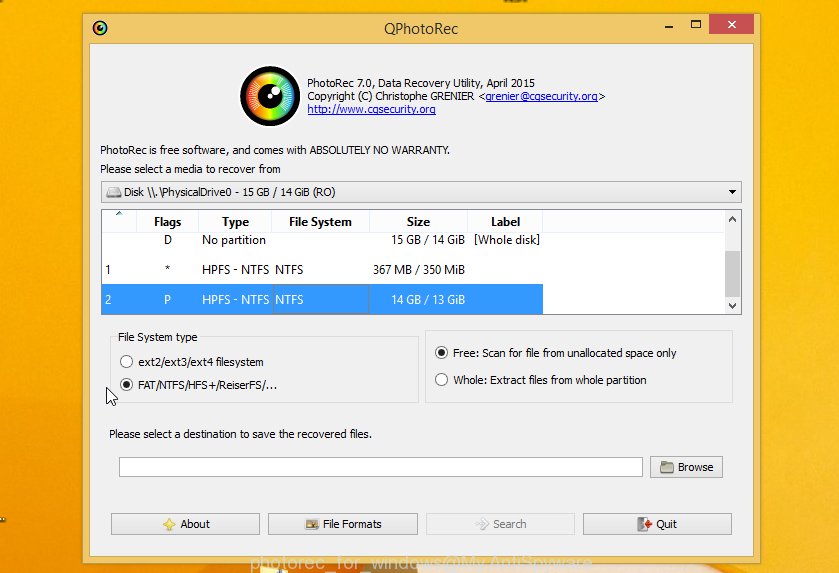
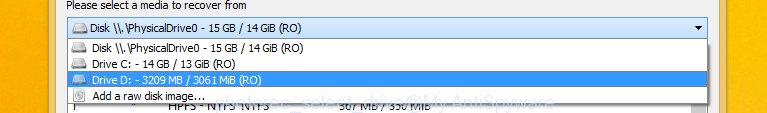
Choose a drive to recover as shown in the figure below.
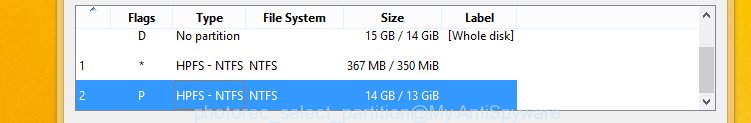
You will see a list of available partitions. Select a partition that holds encrypted documents, photos and music as shown in the following example.
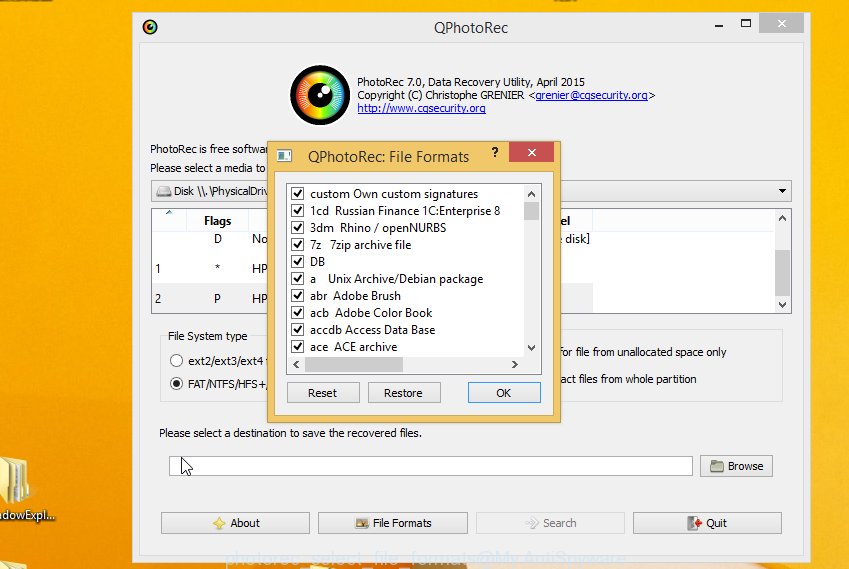
Click File Formats button and choose file types to recover. You can to enable or disable the restore of certain file types. When this is done, press OK button.
Next, click Browse button to select where recovered documents, photos and music should be written, then click Search.
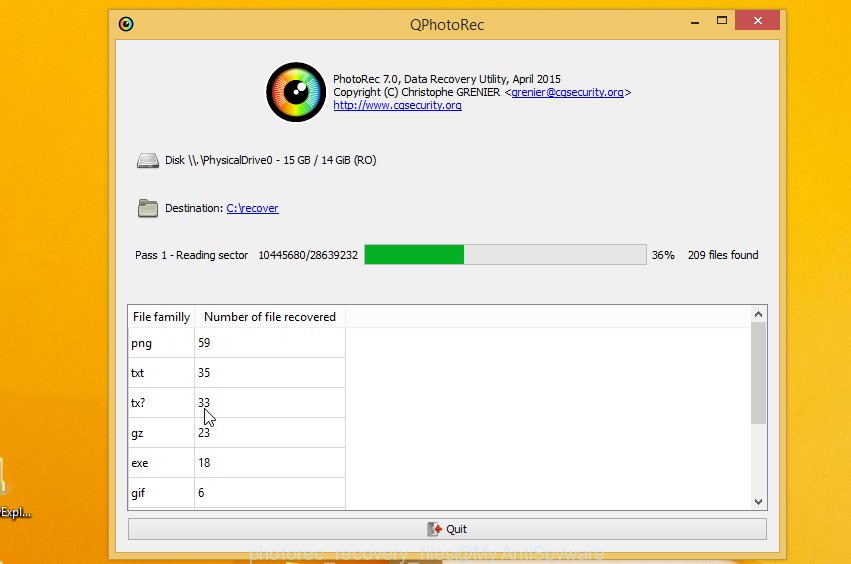
Count of restored files is updated in real time. All restored documents, photos and music are written in a folder that you have selected on the previous step. You can to access the files even if the recovery process is not finished.
When the restore is complete, press on Quit button. Next, open the directory where restored personal files are stored. You will see a contents as on the image below.
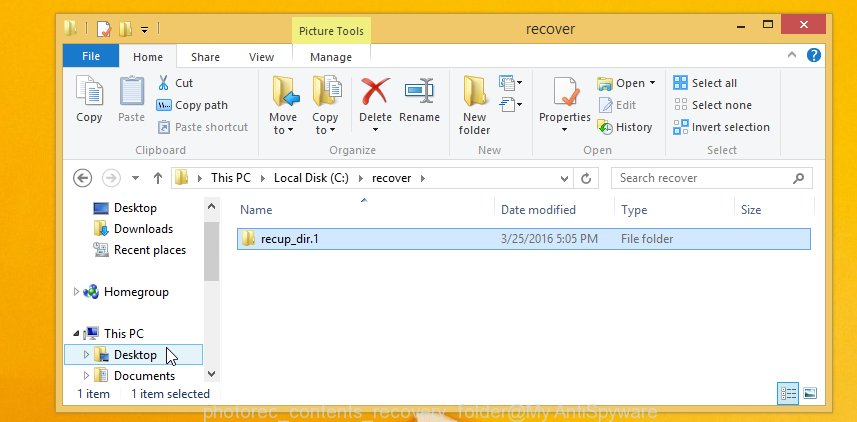
All recovered files are written in recup_dir.1, recup_dir.2 … sub-directories. If you’re looking for a specific file, then you can to sort your recovered files by extension and/or date/time.
To sum up
We hope that our article helped you understand the reason for the appearance of the ‘.kuub’ extension at the end of your file name. Understand what a ransomware is and how to remove it. But most importantly, we hope that you were able to recover all or part of the encrypted files. In any case, tell us about your case, how your computer was infected, whether you were able to recover your files.





















