Have you received an email that claims your email account has been hacked and that the sender (“spyware software developer”) has compromising information about you? If so, you’re not alone. This type of scam is becoming increasingly common, and it’s important to know how to spot it and protect yourself.
The email typically includes a message claiming that the sender has hacked into your device and has access to personal information and even videos or photos of your private activities. They then demand payment in exchange for not sharing this information with your contacts. But don’t be fooled – this is a classic sextortion scam designed to scare you into giving away your money.
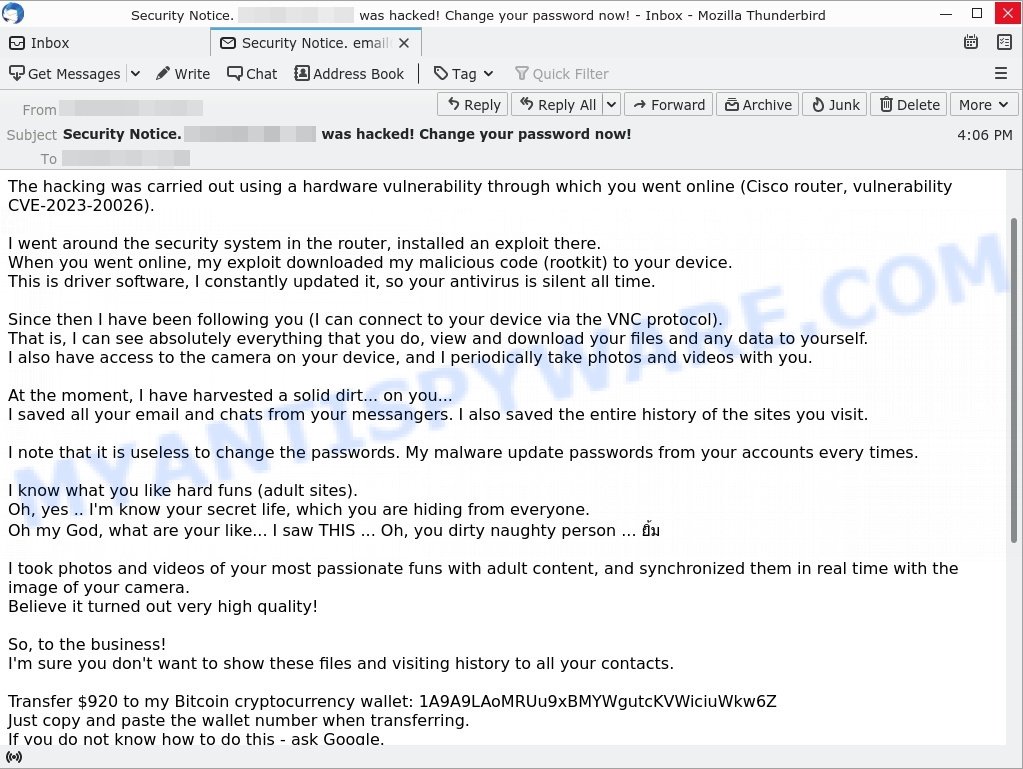
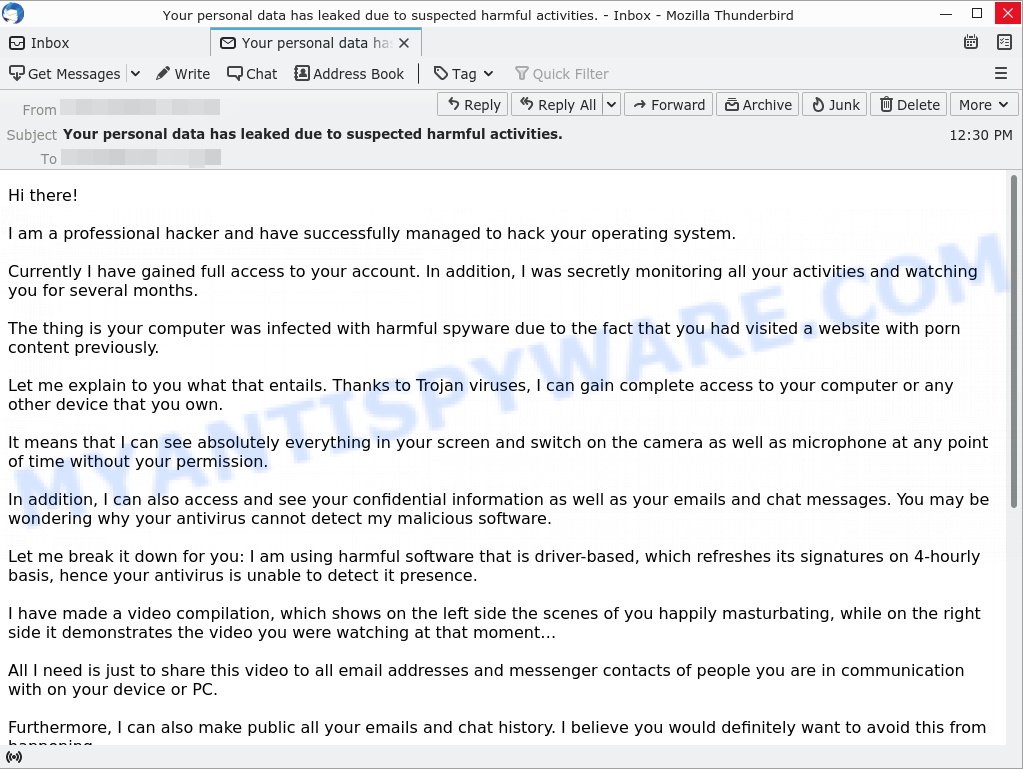
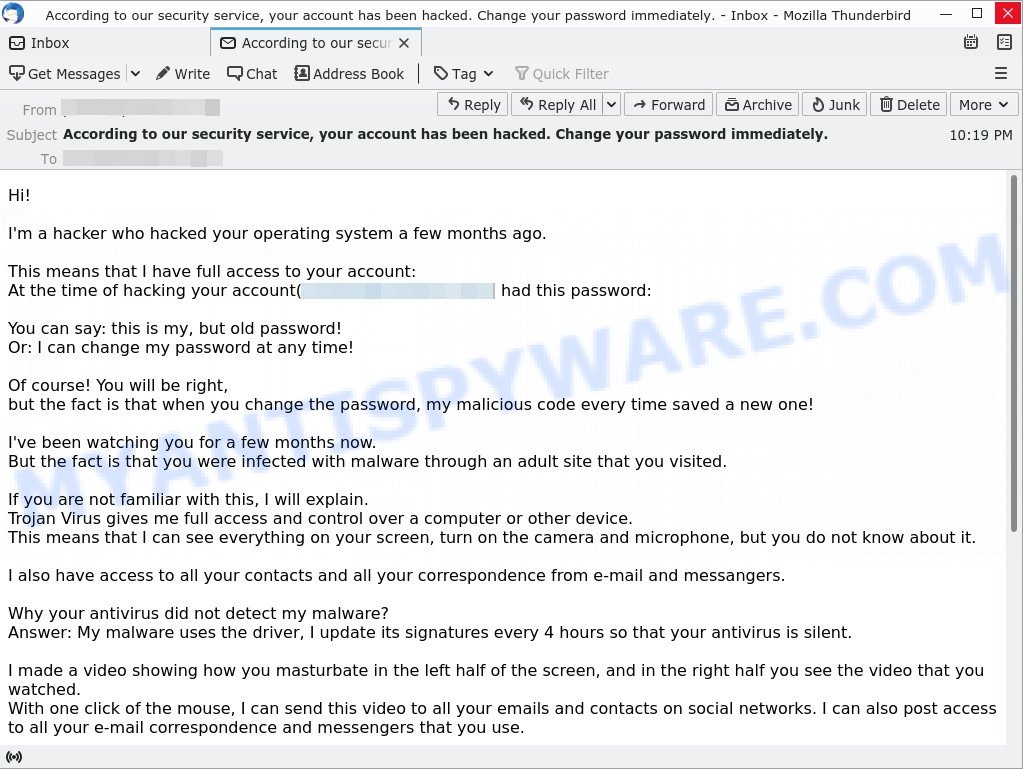
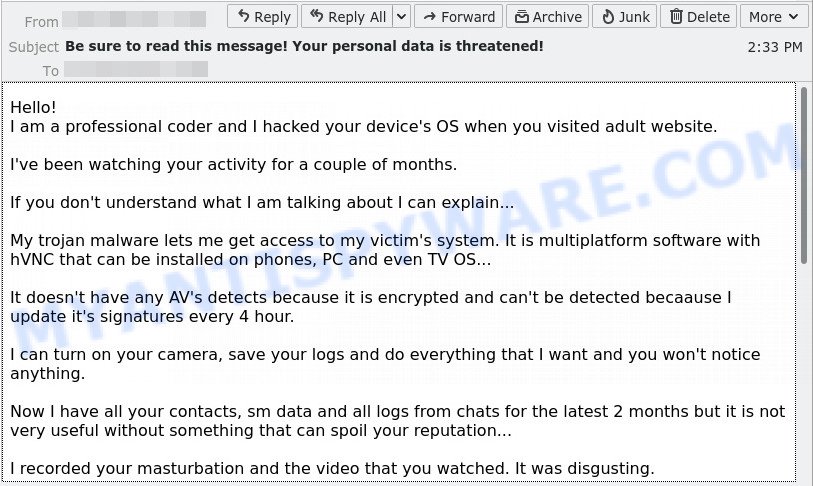
Here’s an example of the “I am a spyware software developer. Your account has been hacked.” Scam Email:
QUICK LINKS
- I am a spyware software developer Email Scam Explained
- Should you pay?
- What to do when you receive a sextortion email?
- Report a Scam
I am a spyware software developer Email Scam Explained
The scam involves an email from someone claiming to have hacked into your device and stolen personal information, such as emails, chats, and videos of your private activities. The sender then demands payment, usually in the form of Bitcoin or another cryptocurrency, in exchange for not releasing the information to your contacts.
Here are some examples of the language used in these scam emails:
- “I am a spyware software developer. Your account has been hacked by me couple months ago.”
- “Since then I have been following you (I can connect to your device via the VNC protocol). That is, I can see absolutely everything that you do, view and download your files and any data to yourself.”
- “I took photos and videos of your most passionate funs with adult content, and synchronized them in real time with the image of your camera.”
These types of emails are scams because they are designed to scare people into giving away money. The sender does not actually have the information they claim to possess and are simply trying to trick people into giving them money.
There are several reasons why these emails are scams:
- The sender does not actually have access to your device or personal information. They may have obtained your email address and some basic information about you from a data breach or other source, but they do not have the level of access they claim.
- The sender’s threats are empty. They may threaten to release embarrassing information or take legal action, but they are unlikely to follow through on these threats.
- The demand for payment in Bitcoin or another cryptocurrency is a red flag. These forms of payment are often untraceable, making it easy for scammers to take the money and disappear without a trace.
In summary, if you receive an email claiming to have compromising information about you and demanding payment, it is likely a scam. Do not respond to the email or send any money. Instead, report it to your email provider or law enforcement and take steps to protect yourself from future scams.
A typical “I am a spyware software developer. Your account has been hacked.” scam email reads as follows:
I am a spyware software developer.
Your account has been hacked by me couple months ago.The hacking was carried out using a hardware vulnerability through which you went online (Cisco router, vulnerability CVE-2023-20026).
I went around the security system in the router, installed an exploit there.
When you went online, my exploit downloaded my malicious code (rootkit) to your device.
This is driver software, I constantly updated it, so your antivirus is silent all time.Since then I have been following you (I can connect to your device via the VNC protocol).
That is, I can see absolutely everything that you do, view and download your files and any data to yourself.
I also have access to the camera on your device, and I periodically take photos and videos with you.At the moment, I have harvested a solid dirt… on you…
I saved all your email and chats from your messangers. I also saved the entire history of the sites you visit.I note that it is useless to change the passwords. My malware update passwords from your accounts every times.
I know what you like hard funs (adult sites).
Oh, yes .. I’m know your secret life, which you are hiding from everyone.
Oh my God, what are your like… I saw THIS … Oh, you dirty naughty person … ยิ้มI took photos and videos of your most passionate funs with adult content, and synchronized them in real time with the image of your camera.
Believe it turned out very high quality!So, to the business!
I’m sure you don’t want to show these files and visiting history to all your contacts.Transfer $920 to my Bitcoin cryptocurrency wallet: 1A9A9LAoMRUu9xBMYWgutcKVWiciuWkw6Z
Just copy and paste the wallet number when transferring.
If you do not know how to do this – ask Google.My system automatically recognizes the translation.
As soon as the specified amount is received, all your data will be destroyed from my server, and the rootkit will be automatically removed from your system.
Do not worry, I really will delete everything, since I am “working” with many people who have fallen into your position.
You will only have to inform your provider about the vulnerabilities in the router so that other hackers will not use it.Since opening this letter you have 48 hours.
If funds not will be received, after the specified time has elapsed, the disk of your device will be formatted, and from my server will automatically send email and sms to all your contacts with compromising material.I advise you to remain prudent and not engage in nonsense (all files on my server).
Good luck!
Should you pay?
Don’t pay the ransom! Paying a ransom is not recommended for several reasons:
- It may encourage further scams: If the scammers see that you are willing to pay, they may continue to send similar emails or target other victims.
- It may result in financial losses: Paying a ransom will result in financial losses and put your personal and financial information at risk.
- It does not guarantee the scammers will stop: Even if you pay the ransom, there is no guarantee that the scammers will stop sending emails or will not release any fabricated sensitive information.
In summary, paying a ransom in response to a sextortion email, or any type of scam, is not recommended and may result in further harm to the victim. If you receive a sextortion email, it is best to seek help from law enforcement and take steps to secure your online accounts and personal information, instead of sending money to the attacker.
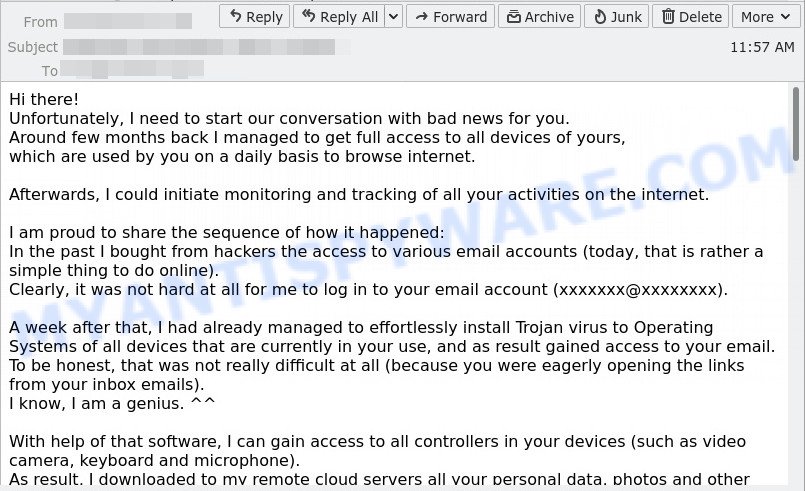
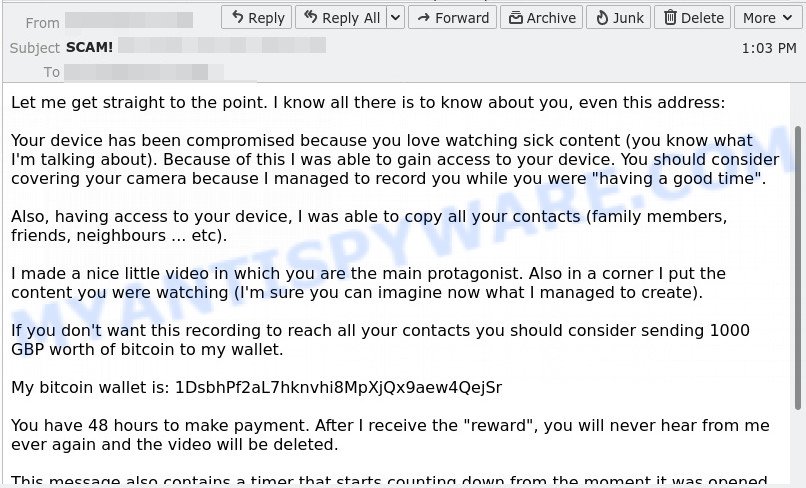
Examples of Sextortion Scams
I have to share bad news with you, I need to start our conversation with bad news for you, Have you recently noticed that I have e-mailed you from your account are other examples of Sextortion scam emails.
- I need to start our conversation with bad news for you Email Scam
- Let me get straight to the point Email Scam
- Your personal data has leaked due to suspected harmful activities. Email Scam
- I’m a hacker who hacked your operating system Email Scam
- I hacked your device EMAIL SCAM
What to do when you receive a sextortion email?
If you receive a sextortion email scam, it is important to take the following steps:
- Do not panic: While these emails are designed to instill fear and panic in the victim, it is important to stay calm and take a measured response to the situation. Remember that the email is fake, and that the attacker does not have access to the sensitive information they are threatening to release
- If the sextortion email scam contains a link, it is important to avoid clicking on it: Avoid clicking on links in sextortion emails as they may lead to malware or phishing sites that can compromise your computer or steal sensitive information.
- Do not respond to the email: Do not reply to the email, or send any money to the attacker.
- Report the scam: Report the scam to the FTC at https://www.ftc.gov/ and relevant authorities, such as your email provider or local law enforcement.
- Delete the email: Delete the email from your inbox and trash folder.
- Secure your accounts: Take steps to secure your online accounts and personal information, such as changing your passwords and enabling two-factor authentication.
- Stay informed: Stay informed about current scams and the tactics used by attackers, so that you can better recognize and avoid them in the future.
- If you suspect that your computer is infected with spyware or trojan, you accidentally clicked on a link in the scam email, or just want to scan your computer for malware, then use one of the best free malware removal tools.
Threat Summary
| Name | I am a spyware software developer. Your account has been hacked Email SCAM |
| Type | Phishing, Bitcoin Email Scam, Fraud, Scam |
| Email subject line | “Security Notice. Email was hacked! Change your password now!”, “Settle your debt in order to avoid additional fees.” |
| Ransom amount | $1350, $920, $1400, $780 |
| Bitcoin Address | 14YLQA98RNJX22W2Prmc7PRQNf6QQf1B1D, 1PNWAfqoNQhTR2jCpcSPL6P5XrCxCofqB3, 1A9A9LAoMRUu9xBMYWgutcKVWiciuWkw6Z |
| Distribution method | spam email campaigns |
| Damage | significant financial loss, emotional distress, reputational damage, compromised personal information, stolen identity |
| Removal | If you gets an email like I sent you an email from your email account, our computer security experts recommend follow some easy steps above |
Report a Scam
If you have received the “I am a spyware software developer” Scam email or an email message that is similar but not the same as the example above, then post it as comment on this article. Please include the email address the email came from. This helps us to warn users about current scams, monitor trends and disrupt scams where possible.
















Similar threat, I have received at least 50 of these over the last week.
I have received the same email but it also lists a very old password I used for that email account (changed at least 4 years ago). Just wondering how they would have got this information as it’s definitely not one you could easily guess (just random letters and numbers).
I had the same as Katie. An old password. However I only used this account for 5 things.
Paypal (use regularly)
Facebook acount (that I do not use)
IG (not used so closed account last month)
Plus500 ( not used)
ADSS Securities ( not used)
The anomoly was ADSS Securities. I had a flurry of emails 6 months ago to get me to deposit funds into the account before new rules were imposed. I did not and when legislation changed they gave up. I asked questions after and they couldn’t be bothered to answer. Then I had an email from them out the blue saying ‘Password Expiration Reminder. Day later I had this Spam email. Coincidence? I had another email recently from them and another spam message a few days apart.
I like this part though 😉
“Since opening this letter you have 48 hours.
If funds not will be received, after the specified time has elapsed, the disk of your device will be formatted,
and from my server will automatically send email and sms to all your contacts with compromising material.
I advise you to remain prudent and not engage in nonsense (all files on my server).
Good luck!”
It’s been since October and my drive is fine lol. 2 months!!
Good luck yourselves with the camera on my device btw. I don’t have one!
haveibeenpwned.com/
turns out it was lastfm. Can’t remember the last time I use that.
The site above is great. found another account that I did not know had been leaked. I will now change the password on it.
As with the others, they hacked an old password of mine from 6 years ago that i used on a few torrent sites.
But what’s strange is that they are now sending these messages from my very own email account, as to prove the point they’ve hacked me.
And even stranger, when i change the password, it still doesn’t prevent them from using my email address to auto send these spam.
How is that possible ?
Scammers use email spoofing—sending emails that appear legitimate but are anything but (en.wikipedia.org/wiki/Email_spoofing).