What is 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ?
89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware is a malicious program that targets cryptocurrency users and functions like a clipboard hijacker. Clipboard hijacker is a form of malicious software that allows an attacker to take control of the victim’s clipboard and replace its contents with their own data.
The 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware can be spread with the help of trojan horses and other forms of malware, but in most cases, it is bundled within the setup files from file sharing and torrents sites. So, install a “cracked” and “pirated” software is a a good chance that you will find a bundled malware.
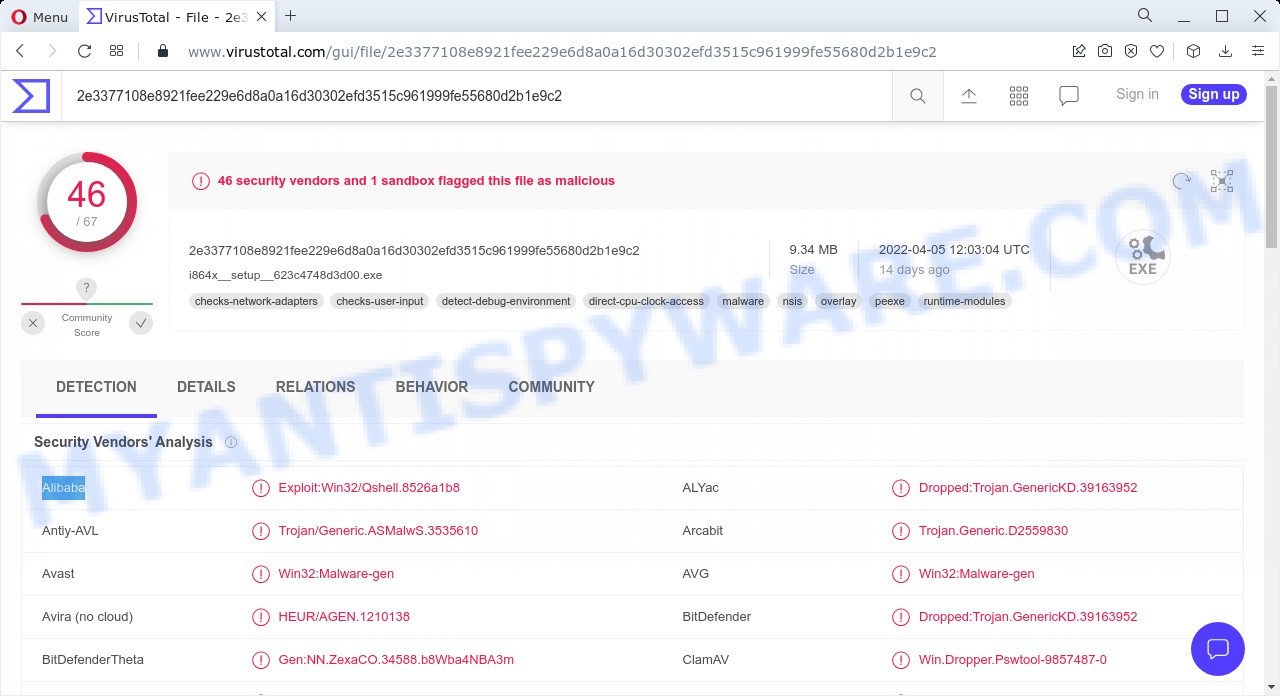
89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware – Detection names
If you still are not sure that your personal computer is affected with malware, then check your computer for the common symptoms of this infection:
- your browser displays advertisements where previously you have never seen;
- web browser settings such as homepage, new tab page and search engine are hijacked;
- webpage links redirect to web pages different from what you expected;
- new entries appear in your Programs folder;
- your antivirus software detects an infection;
- Internet connection is slow.
QUICK LINKS
Any malware is a serious threat. Trojans usually infect a computer with other types of malware. Trojans can download and run other very dangerous malware such as ransomware and cryptominers. Especially dangerous are ransomware that secretly encrypt the victim’s files and then demand a ransom to decrypt them. The recovery of encrypted files becomes impossible in most cases. Ransomware can lead to the loss of personal documents and important data.
Cryptominers are malware that uses computer resources to secretly mine cryptocurrency. This process uses up a lot of system resources, which means that it slows down the speed of the computer. Moreover, cryptominers can lead to overheating of the main components of the computer and their failure.
Trojans are also used to infect computers with browser hijackers and adware. This malicious software is less dangerous than ransomware or cryptominers, but it causes intrusive ads and unwanted browser redirects. In some cases, Trojans have capabilities that allow criminals to remotely control the infected computer.
To summarize, the presence of 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware on a computer can lead to serious problems, loss of personal data, large financial losses, damage to computer parts, and much more.
Threat Summary
| Name | 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware |
| Type | Trojan, malware, clipboard hijacker, spyware |
| Detection Names | Trojan.Win32.Agent.a!c, Trojan.Win32.Agent.cl, HEUR/AGEN.1210138, Trojan.Generic.D2559830, HEUR:Trojan-Spy.MSIL.Stealer.gen, Exploit:Win32/Qshell.8526a1b8, Trojan/Generic.ASMalwS.3535610, Gen:NN.ZexaCO.34588.b8Wba4NBA3m, Win.Dropper.Pswtool-9857487-0, W32/MSIL_Agent.CZV.gen!Eldorado, Dropped:Trojan.GenericKD.39163952 (B), Backdoor.BDS/Redcap.yyemp, Win32.Troj.Undef.(kcloud), Trojan-Downloader.Win32.Agent.xxzxqt, BehavesLike.Win32.Generic.tc |
| Malicious Process Name | AutoIt v3 Script (32 bit) |
| Distribution methods | Cracked (pirated) software. Spam mails that contain malicious links. Malicious downloads that happen without a user’s knowledge when they visit a compromised webpage. Social media, such as web-based instant messaging applications. |
| Removal | 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware removal guide |
On the Internet, users can come across many Trojans that perform various malicious actions. Among them there are such as AnarchyGrabber Stealer, Numando malware and DPD Delivery Email virus, although, of course, there are many more. Some of them collect user data, others install malware on computers, and still others add infected computers to botnets, and so on. In any case, each Trojan is a huge threat to both user privacy and computer security. Therefore, Trojans must be removed immediately after detection; using an infected computer is very dangerous.
How to remove 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware (Malware removal guide)
If you accidentally run a file attached to a spam email, or suspect that your computer is infected with the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware, then you need to follow the steps, which are given below. You may find some minor differences in your MS Windows install. No matter, you should be okay if you follow the steps outlined below: kill malicious processes, remove 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ associated files, scan computer for malware. Some of the steps will require you to reboot your personal computer or close this web-site. So, read this guidance carefully, then bookmark this page or open it on your smartphone for later reference.
To remove 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware, complete the steps below:
- Kill 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware
- Disable 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware start-up
- Scan computer for malware
Kill 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware
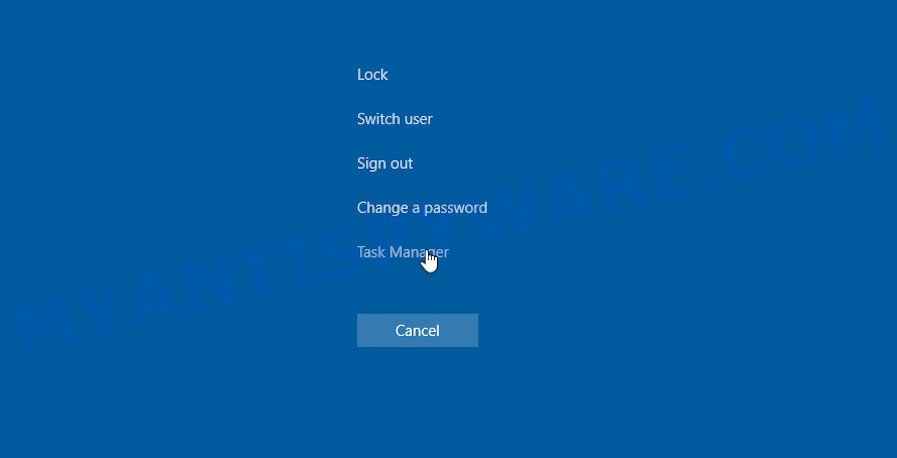
Press CTRL, ALT, DEL keys together.
Click Task Manager. Select the “Processes” tab, look for something suspicious that is the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware then right-click it and select “End Task” or “End Process” option. If your Task Manager does not open or the Windows reports “Task manager has been disabled by your administrator”, then follow the guide: How to Fix Task manager has been disabled by your administrator.
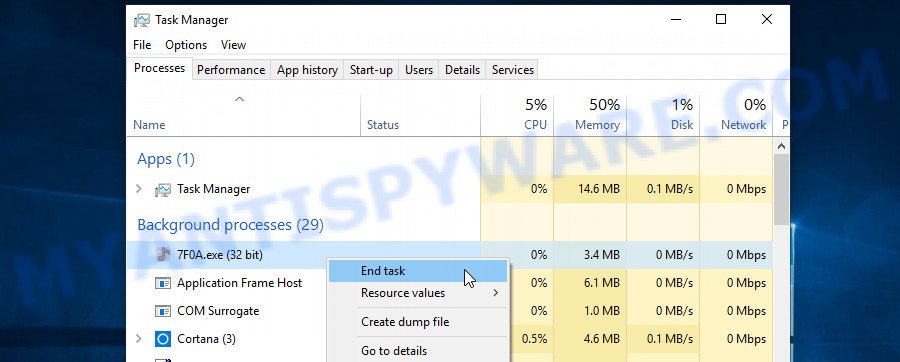
It is not difficult to detect a process related to the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware. When looking for a malicious process, pay attention to the process icon and its name. Most often, this malware has the following process name: AutoIt v3 Script. The process name can also contain “(32 bit)”. If you do not find a process with a similar name in the list of processes, then most likely the malware has finished working. But keep in mind, if you do not remove the malware autostart entries, as demonstrated below, and do not delete its file, then after a while it may start again.
Disable 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware start-up
Select the “Start-Up” tab, look for something suspicious that is a malicious program, right click to it and select Disable.
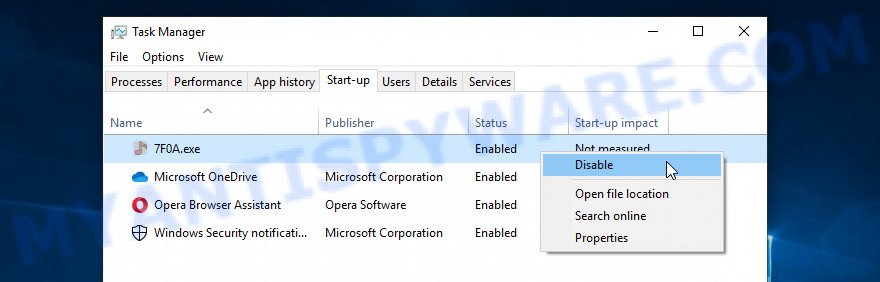
Close Task Manager.
Scan computer for malware
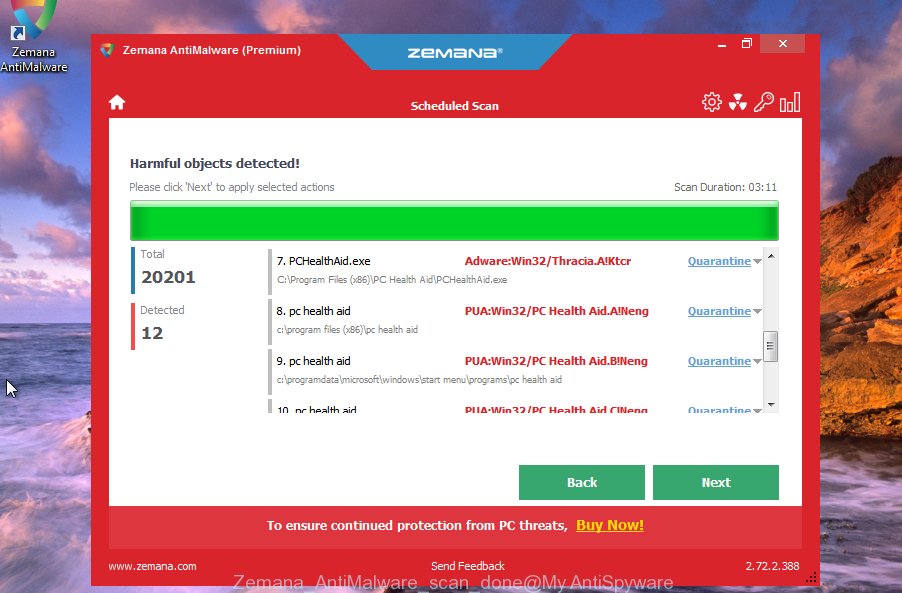
We suggest using the Zemana Anti-Malware that can detect and remove the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware. The utility is an advanced malicious software removal program developed by (c) Zemana lab. It’s able to help you remove PUPs, viruses, adware, malware, toolbars, ransomware and other security threats from your computer for free.
Installing Zemana is simple. First you will need to download Zemana Anti Malware from the following link. Save it on your Windows desktop or in any other place.
165094 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
Once downloading is finished, start it and follow the prompts. Once installed, Zemana will try to update itself and when this task is done, click the “Scan” button to begin scanning your PC for the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware, other malicious software and spyware.

A system scan can take anywhere from 5 to 30 minutes, depending on your PC. Review the report and then press “Next” button.
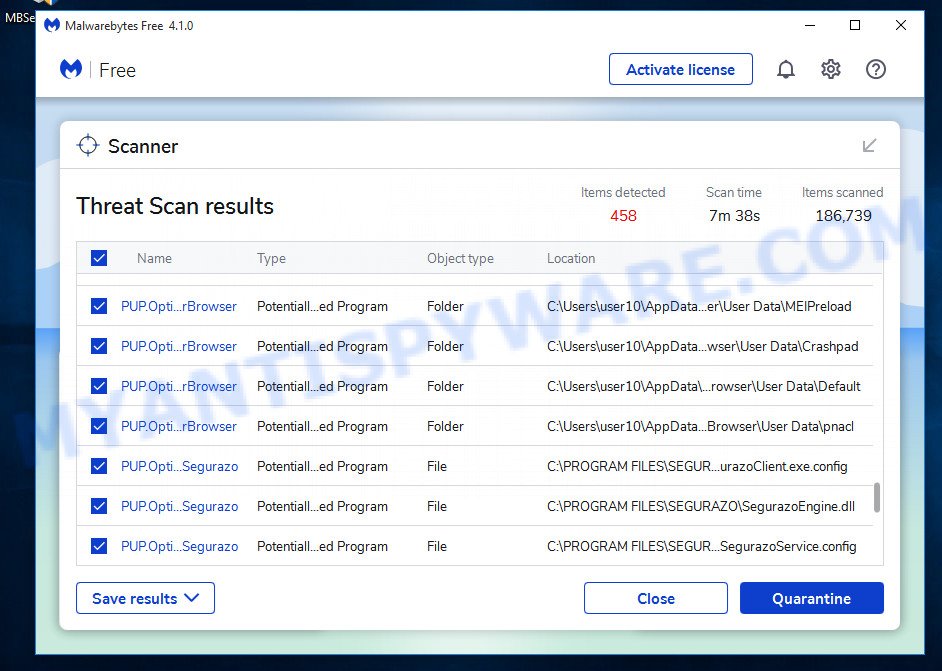
In order to be 100% sure that the computer no longer has the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware, we recommend using MalwareBytes. It can easily detect and remove adware software, trojans, browser hijackers, PUPs and malicious toolbars with all their components such as files, folders and registry entries.
MalwareBytes can be downloaded from the following link. Save it to your Desktop.
327319 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
After the downloading process is complete, run it and follow the prompts. Once installed, MalwareBytes will try to update itself and when this procedure is finished, click the “Scan” button to perform a system scan with this utility for the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware, spyware, worms and other malware. Make sure to check mark the threats which are unsafe and then press “Quarantine” button.
MalwareBytes is a free malware removal tool that you can use to remove all detected folders, files, services, registry entries and so on. To learn more about this malware removal utility, we advise you to read and follow the step-by-step guide or the video guide below.
How to stay safe online
Using an adblocker such as AdGuard will protect you from harmful websites, misleading ads and phishing content. Moreover, you can find that AdGuard have an option to protect your privacy and stop spam web pages. Additionally, ad blocking software will help you to avoid unwanted pop-ups and unverified links that also a good way to stay safe online.
Visit the following page to download AdGuard. Save it on your Desktop.
26913 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
When downloading is finished, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as shown on the screen below.
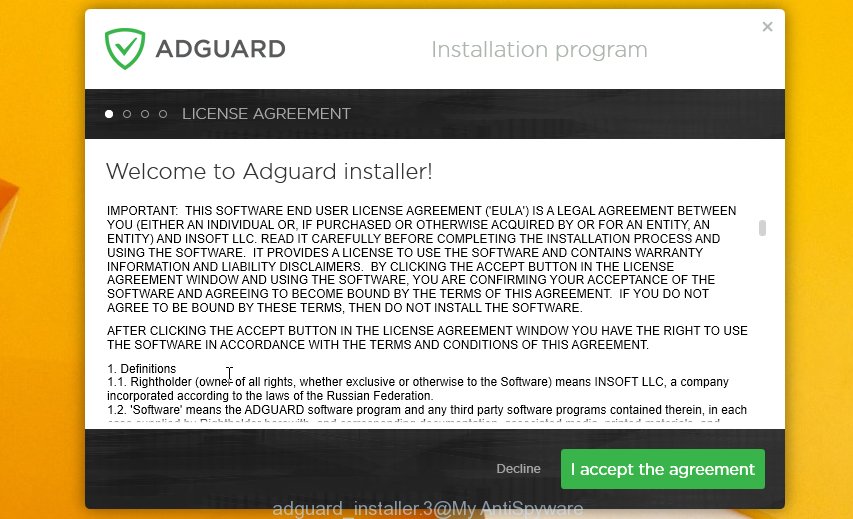
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guidance as shown on the screen below.

Click “Skip” button to close the window and use the default settings, or click “Get Started” to see an quick guide that will allow you get to know AdGuard better.
Each time, when you run your PC, AdGuard will start automatically and stop unwanted advertisements, block phishing websites, as well as other harmful or misleading web-pages. For an overview of all the features of the program, or to change its settings you can simply double-click on the AdGuard icon, that is located on your desktop.
Finish words
Now your computer should be clean of the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware. We suggest that you keep AdGuard (to help you block unwanted pop-up advertisements and unwanted malicious webpages) and Zemana (to periodically scan your device for malware, browser hijackers and adware). Make sure that you have all the Critical Updates recommended for Microsoft Windows OS. Without regular updates you WILL NOT be protected when new trojans, ransomware and malware are released.
If you are still having problems while trying to remove the 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ malware from your computer, then ask for help here.


















