What is I have got two not really pleasant news for you EMAIL?
I have got two not really pleasant news for you is a new ‘sextortion’ scam that spreads through spam email campaigns. This scam email attempts to immediately grab the user’s attention with the following header: Bill for Payment #. But this is just a new version of the ‘sextortion’ email scam, which, like most sextortion scams, relies on “social engineering”, a process through which the scammers induce shame, panic or guilt. The scammers (the authors of the email) claim that they obtained material compromising the user (as a result of a computer hack, email account hack, router hack, etc) and threaten to publish it if the ransom is not paid. All these claims are not based on anything, they are just deception. Therefore, you can safely ignore this email, just delete it or move it to spam.
The “I have got two not really pleasant news for you” email is a SCAM
QUICK LINKS
- What is I have got two not really pleasant news for you EMAIL?
- Should you pay?
- What to do when you receive the email scam?
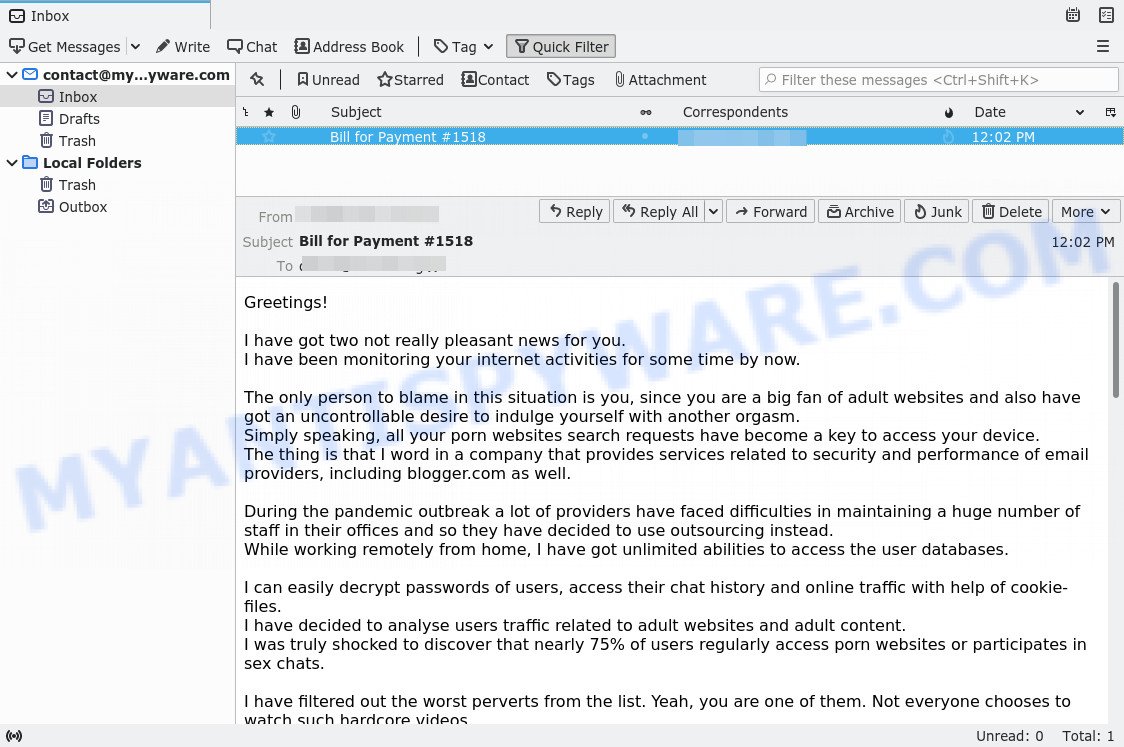
The “I have got two not really pleasant news for you” email states that the hacker (the sender of the letter) for some time had full access to the recipient’s device, as well as to the microphone and camera connected to it. This attacker claims that he was able to install a Trojan on the victim’s device, which allowed him to take full control of the device and record a video in which the victim masturbates while watching a porn video. The hacker threatens to send the video to everyone on the victim’s contact list and upload it to public websites unless the victim pays a ransom of $ 1,450. If the victim pays the required amount in Bitcoin, the hacker promises to delete all the data. Next, the scam email contains the bitcoin address to which the ransom should be transferred. The “I have got two not really pleasant news for you” email is just a sextortion scam, all statements are fake. Therefore, this email and other emails containing such content should be ignored.
Text presented in the “I have got two not really pleasant news for you” message:
Greetings!
I have got two not really pleasant news for you.
I have been monitoring your internet activities for some time by now.The only person to blame in this situation is you, since you are a big fan of adult websites and also have got an uncontrollable desire to indulge yourself with another orgasm.
Simply speaking, all your porn websites search requests have become a key to access your device.
The thing is that I word in a company that provides services related to security and performance of email providers, including blogger.com as well.During the pandemic outbreak a lot of providers have faced difficulties in maintaining a huge number of staff in their offices and so they have decided to use outsourcing instead.
While working remotely from home, I have got unlimited abilities to access the user databases.I can easily decrypt passwords of users, access their chat history and online traffic with help of cookie-files.
I have decided to analyse users traffic related to adult websites and adult content.
I was truly shocked to discover that nearly 75% of users regularly access porn websites or participates in sex chats.I have filtered out the worst perverts from the list. Yeah, you are one of them. Not everyone chooses to watch such hardcore videos…
Basically, I have infected your device with one of the best Trojan viruses in the market. It was relatively easy, since I have access to your email address (xxx@xxxxx).
It was sufficient to prepare one of your routine emails asking you to click the harmful link…My spyware functions as a driver. Hence, I can fully control your device and have access to your microphone, camera, cursor and set of symbols.
Generally speaking, your device is some sort of my remote PC.
Since this spyware is driver-based, then I can constantly update its signatures, so that no antivirus can detect it.
While digging through your hard drive, I have saved your entire contact list, social media access, chat history and media files.One week ago, I have montaged a videoclip, which shows you masturbating on one side of the screen and on the other side a porn video
that you were watching at that moment of time – recently this type of exotic stuff is really popular on the internet!
Don’t worry, I will need just a few mouse clicks in order to share this video with your entire contact list and upload it to some porn website, like Bigle.
I believe that you would not like this to happen, since a long holiday season is just about to start soon –
just imagine the number of silly jokes and loud laughter that would get provoked by your video all over the neighbourhood bars and pubs…I am offering a simple and reasonable solution:
All you need to do is transfer an amount equivalent to $1450 (USA Dollars) to my bitcoin wallet and we both forget about this silly story forever.
All your data and this video will be deleted by me once and for all. You have my honest word!
You’ve got to agree, this amount is really insignificant. Just imagine how much time and resources I have spent to get this done…
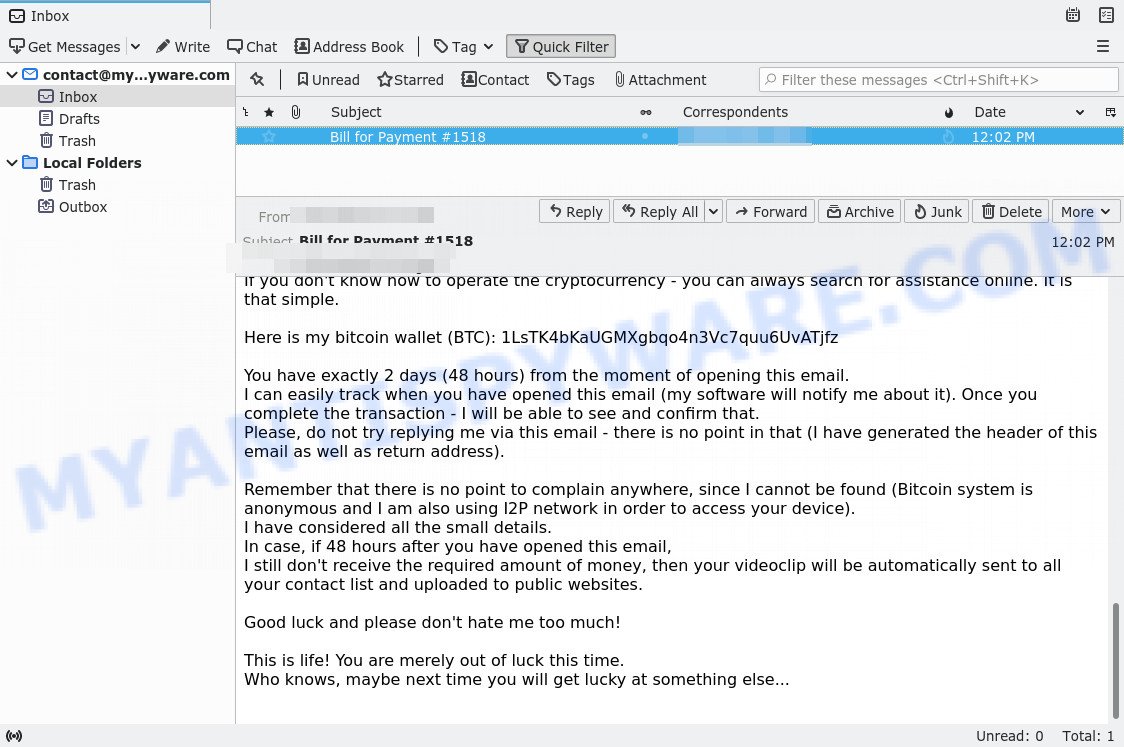
If you don’t know how to operate the cryptocurrency – you can always search for assistance online. It is that simple.Here is my bitcoin wallet (BTC): 1LsTK4bKaUGMXgbqo4n3Vc7quu6UvATjfz
You have exactly 2 days (48 hours) from the moment of opening this email.
I can easily track when you have opened this email (my software will notify me about it). Once you complete the transaction – I will be able to see and confirm that.
Please, do not try replying me via this email – there is no point in that (I have generated the header of this email as well as return address).Remember that there is no point to complain anywhere, since I cannot be found (Bitcoin system is anonymous and I am also using I2P network in order to access your device).
I have considered all the small details.
In case, if 48 hours after you have opened this email,
I still don’t receive the required amount of money, then your videoclip will be automatically sent to all your contact list and uploaded to public websites.Good luck and please don’t hate me too much!
This is life! You are merely out of luck this time.
Who knows, maybe next time you will get lucky at something else…
What is Sextortion email scam
Sextortion is the practice of extorting money from victims by blackmailing them; threatening to reveal evidence of their sexual activity. It is an old scam scheme – which try to guilt people into paying off someone claiming to have secretly recorded video or compromising information. Scammers use a database of stolen email to send out scam emails to to millions of people around the World. The messages are sent to email addresses exposed in previous known data breaches in which the user database (email address and/or password) was indexed online.
Bottom of the scam email
Should you pay?
The best advice is: Don’t pay the ransom! If you receive the sextortion email scam, just ignore the scammers’ empty threats. The best way to deal with the scam email is simply to move it to trash!
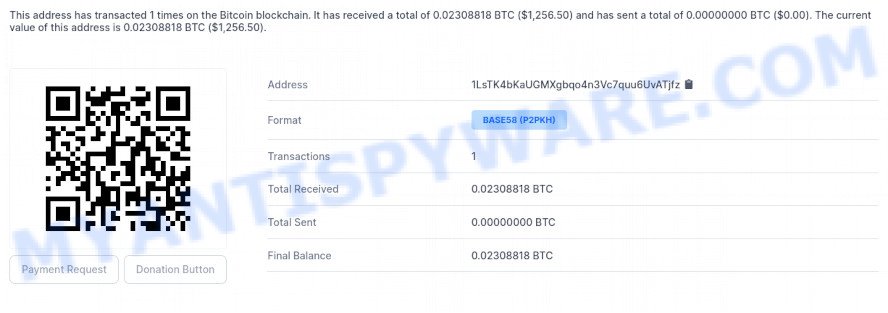
It looks like the scammers have already received a ransom from one of the victims.
Threat Summary
| Name | I have got two not really pleasant news for you SCAM |
| Type | Phishing, Bitcoin Email Scam, Fraud, Scam |
| Email subject line | Bill for Payment # |
| Ransom amount | $1450 |
| Bitcoin Address | 1CsJeU1fHeRMaUh3FpeCzX41MrqVrkKYfN, 16fbeN6D5JkTU7Ywh8zdAPoQWD6TzN1ZSf, 176hSePwUyHECsoE7TUEhvGUyBxhwY6VDf, 1LsTK4bKaUGMXgbqo4n3Vc7quu6UvATjfz |
| Distribution method | spam email campaigns, WhatsApp |
| Removal | If you gets an email like I have got two not really pleasant news for you, our computer security experts recommend follow some easy steps below |
What to do when you receive the I have got two not really pleasant news for you SCAM
We advise anyone who has received this scam email:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the scam email to the FTC at https://www.ftc.gov/
- Scan your computer for malware.
- Install an anti-phishing software.
How to scan your PC for malware
If you suspect that your computer is infected with malicious software, we recommend scanning it for viruses. In addition to anti-virus software, we recommend using Zemana Anti Malware. It is a lightweight utility which designed to use alongside your antivirus software, detecting and removing malicious software, adware and PUPs that other security tools miss. Zemana Anti Malware is easy to use, fast, does not use many resources and have great detection and removal rates.
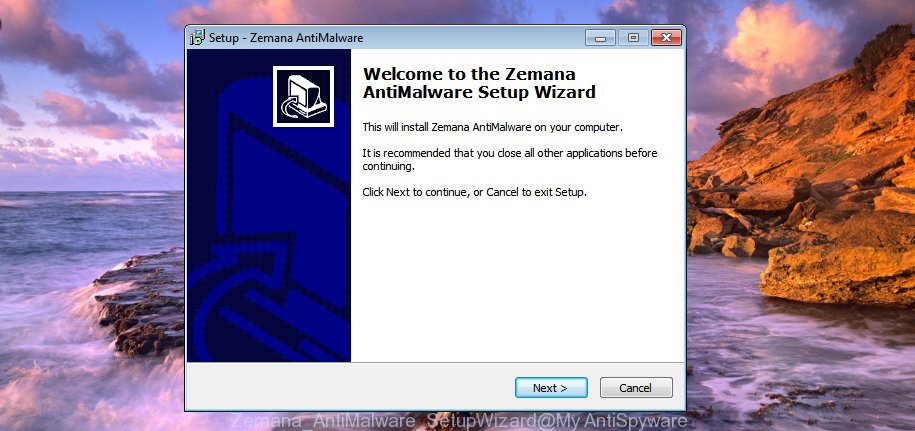
- Installing the Zemana is simple. First you’ll need to download Zemana on your device by clicking on the link below.
Zemana AntiMalware
165094 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
- Once you have downloaded the setup file, make sure to double click on the Zemana.AntiMalware.Setup. This would start the Zemana installation on your device.
- Select installation language and click ‘OK’ button.
- On the next screen ‘Setup Wizard’ simply click the ‘Next’ button and follow the prompts.

- Finally, once the installation is finished, Zemana will run automatically. Else, if doesn’t then double-click on the Zemana icon on your desktop.
- Now that you have successfully install Zemana AntiMalware, let’s see How to use this tool to detect and remove malware from your computer.
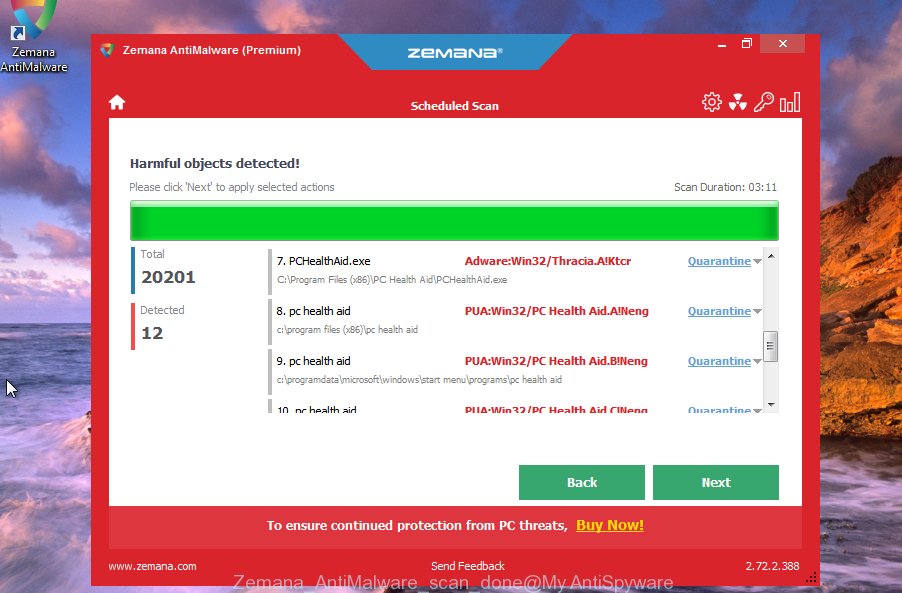
- After you have started the Zemana AntiMalware, you’ll see a window as shown on the image below, just click ‘Scan’ button to perform a system scan with this tool for malicious software.

- Now pay attention to the screen while Zemana scans your device.

- Once Zemana Anti Malware has finished scanning, it will display a list of all items found by the scan. Once you’ve selected what you wish to remove from your computer click ‘Next’ button.

- Zemana Anti Malware may require a reboot computer in order to complete the malware removal procedure.
- If you want to permanently remove malicious software from your PC, then click ‘Quarantine’ icon, select all malware, adware, PUPs and other items and click Delete.
- Reboot your personal computer to complete the malware removal process.
If you are having issues with malware removal, then check out MalwareBytes. We recommend this free malware removal utility because it may easily delete trojans, spyware, browser hijackers, adware, potentially unwanted software and toolbars with all their components such as files, folders and registry entries. Visit the page linked below to download the latest version of MalwareBytes Anti-Malware for Windows.
327319 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
We suggest you look at the following video, which completely explains the process of using the MalwareBytes Anti Malware to remove malicious software.
How to protect yourself from phishing, malicious and misleading websites
If you want to protect yourself from phishing websites, then install an ad blocker program such as AdGuard. It can block malicious and misleading web sites, stop unwanted advertisements and popups when using the Internet Explorer, Google Chrome, Firefox and Edge. So, if you like surf the Internet, and want to protect your computer from malicious web pages, then the AdGuard is your best choice.
Installing the AdGuard is simple. First you’ll need to download AdGuard by clicking on the link below.
26913 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as displayed below.
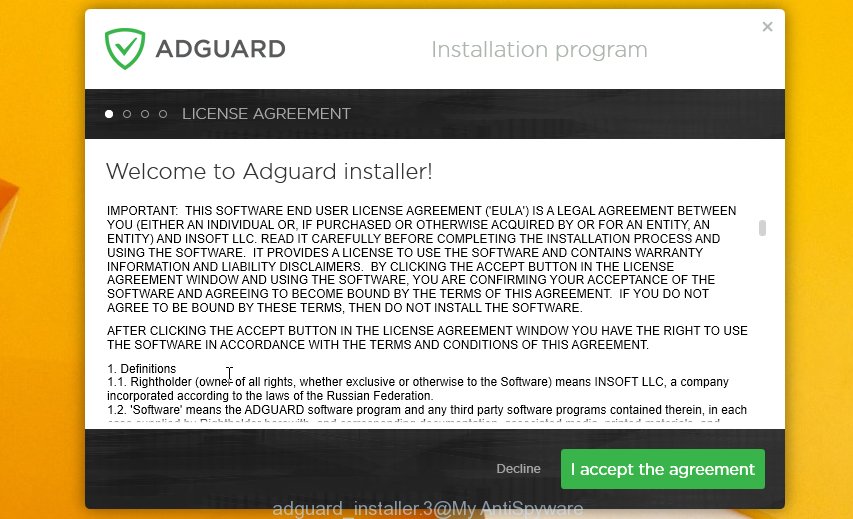
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guide as displayed on the screen below.

Click “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick guidance which will assist you get to know AdGuard better.
Each time, when you start your system, AdGuard will start automatically and stop unwanted advertisements, block phishing, as well as other harmful or misleading websites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
We hope that this article helped you understand what the “I have got two not really pleasant news for you” SCAM is and not succumb to the threats of scammers. If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. It will help our team monitor the latest scams.