[email protected] is an email address that cyber criminals use to contact victims of Dharma ransomware. Ransomware is a type of malware that blocks access to files by encrypting them, until the victim pays a ransom.
[email protected] virus locks up the files using AES-RSA technology, that makes it impossible to unlock the encrypted data by the victim without obtaining a key and a decryptor, which is the only way to decrypt affected files. It can be obtained only in the case of payment of the required ransom through cryptocurrency wallet. The ransomware virus encrypts almost of database, videos, documents, music, web application-related files, archives and images, including common as:
.xld, .wps, .vfs0, .arw, .ybk, .wmf, .wotreplay, .itm, .apk, .gho, .p7c, .vpk, .wn, .srw, .xls, .wpw, .der, .hplg, .jpe, .icxs, .qic, .cfr, .pst, .xbplate, .pptx, .sr2, .bar, .wsd, .fsh, .sid, .desc, .sidn, .wp7, .blob, .sidd, .wmv, .xlsm, .indd, .mov, .rw2, .sis, .vcf, .crw, .sb, .wpa, .png, .db0, .1, .wdp, .xbdoc, .rar, .lvl, .wdb, .wpb, .ods, .psd, .iwd, .map, .wbc, .webp, .pfx, wallet, .zabw, .wmv, .pkpass, .hkx, .dcr, .wp4, .ncf, .cr2, .sie, .wav, .mdbackup, .gdb, .wsc, .xf, .litemod, .y, .wire, .wps, .snx, .esm, .dng, .3fr, .re4, .xpm, .kf, .wp, .hvpl, .yml, .py, .vtf, .js, .big, .xmind, .bc7, .bc6, .dwg, .rb, .pak, .zdb, .doc, .mpqge, .mcmeta, .upk, .rwl, .wmo, .mlx, .dba, .ztmp, .wcf, .rgss3a, .txt, .srf, .docm, .ff, .layout, .dmp, .xlsb, .wpd, .wma, .nrw, .odb, .wsh, .xlgc, .rim, .xdb, .d3dbsp, .wgz, .3dm, .zip, .pdf, .raw, .jpg, .wbk, .p7b, .xml, .1st, .ai, .erf, .wp5, .iwi, .wma, .raf, .tor, .r3d, .zif, .zi, .3ds, .csv, .ntl, .sql, .lrf, .mdb, .lbf, .wpt, .bay, .xls, .xwp, .xar, .z, .wbm, .vdf, .rofl, .ltx, .avi, .x3f, .dazip, .z3d, .xy3, .pdd, .xdl, .bik, .odt, .xxx, .bkp, .crt, .0, .wmd, .cdr, .cer, .mp4, .mef, .flv, .7z, .bsa, .t13, .fos, .wri, .eps, .kdb, .wbmp, .arch00, .cas, .wpg, .m4a, .xlsm, .wpd, .itdb, .menu, .epk, .m3u, .xlsx, .odp, .xmmap, .sav, .2bp, .xlk, .accdb, .dxg, .vpp_pc, .wm, .ibank, .hkdb, .bkf, .mdf, .tax, .svg, .forge, .rtf, .slm, .wb2, .webdoc, .sum, .x3f, .wpl, .orf, .xlsx, .wbz, .css, .wp6, .m2, .yal, .xyp, .kdc, .jpeg, .zdc, .xx, .ptx, .ws, .x3d, .mrwref, .qdf, .pem, .zip, .mddata, .psk, .zw, .itl, .das, .ysp, .t12, .x, .wpe, .odm, .asset, .pef, .dbf, .fpk, .ppt, .p12, .wot, .docx, .wbd, .odc
With the encryption process is finished, all encrypted files will now have a new extension appended to them. In every directory where there are encrypted files, [email protected] virus drops a file called ‘FILES ENCRYPTED.txt’. This file contains a ransom note that is written in the English. The ransom message directs victims to make payment in exchange for a key needed to unlock personal files.
Summary
| Email address | [email protected] |
| Related ransomware | Dharma family |
| Variants of Dharma that use this address | .[[email protected]].ROGER |
| Ransom note | FILES ENCRYPTED.txt |
| Ransom amount | $300 – $1000 |
| Removal | Free Malware Removal Tools |
| Recover Encrypted files | How to recover ransomware encrypted files |
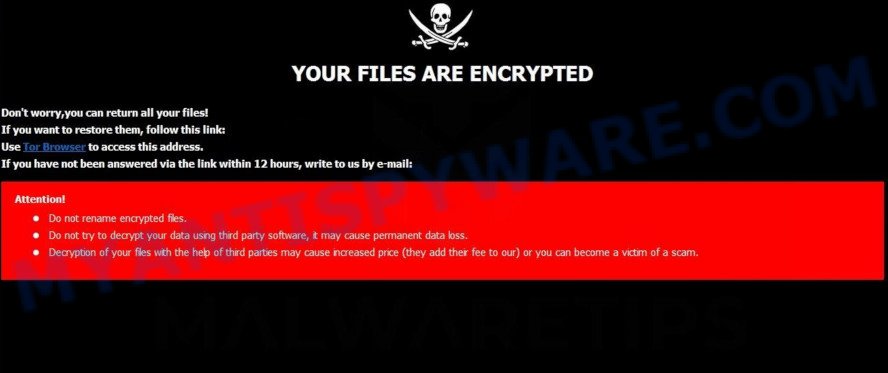
Text presented in “FILES ENCRYPTED.txt”:
YOUR FILES ARE ENCRYPTED
Don’t worry,you can return all your files!
If you want to restore them, follow this link:
Use Tor Browser to access this address.
If you have not been answered via the link within 12 hours, write to us by e-mail:[email protected]
Attention!
Do not rename encrypted files.Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
How to recover .[[email protected]] files
Unfortunately, at the moment it is impossible to decrypt .[[email protected]] files, but do not despair. Fortunately, there are several alternative methods that can allow everyone to recover the contents of encrypted files. Each of these methods does not involve the use of special knowledge and paid programs and can be performed by everyone. We have prepared an instruction with illustrations, which describes in detail the process of data recovery. Before you begin data recovery, check your computer for malware using free malware removal tools. You must be 100% sure that [email protected] virus is completely removed.

















