Computer security researchers discovered a new variant of ransomware which named SynAck ransomware. It appends a ten random alpha characters as extension to encrypted file names. This article will provide you with all the things you need to know about this ransomware, how to remove SynAck ransomware from your computer and how to decrypt or restore all encrypted documents, photos and music for free.
The SynAck ransomware uses very strong hybrid encryption with a large key. When the virus encrypts a file, it will add ten random alpha characters as extension to every encrypted file. Once the ransomware finished enciphering of all personal files, it will drop a file named “RESTORE_INFO-[ID].txt” with a guide on how to decrypt all photos, documents and music.
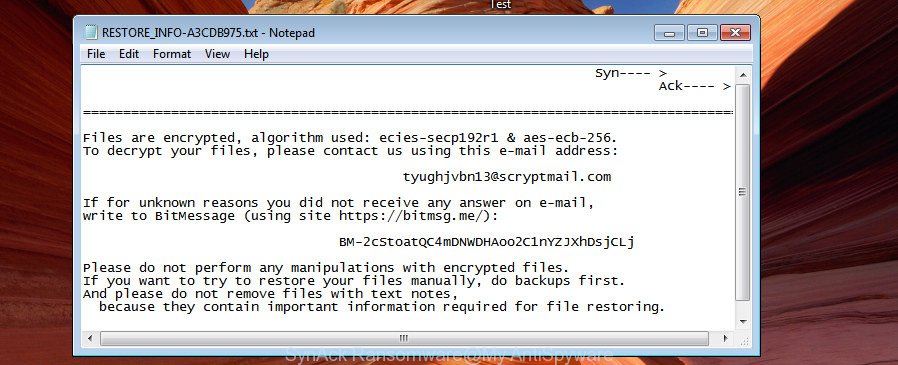
SynAck Ransomware – ransomnote
The RESTORE_INFO-[ID].txt ransom note offers victim to contact SynAck’s creators by using the following email addresses:
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
or by using BitMessage:
- BM-2cTp9eosgjWs8SV14kYCDzPN3HJkwYk1LQ
- BM-2cStoatQC4mDNWDHAoo2C1nYZJXhDsjCLj
- BM-2cWsgWxq1X5M6qjDEBPvCdEbbPLn2zi43k
These persons will require to pay a ransom (usually demand for $500 – $3000 in Bitcoins). Important to know, currently not possible to decrypt files encrypted by SynAck ransomware without a decrypt program. If you choose to pay the ransom, there is no 100% guarantee that you can decrypt all photos, documents and music! If you do not want to pay for a decrypt program, then you have a chance to restore encrypted files.
Therefore it is very important to follow the steps below as quickly as possible. The few simple steps will assist you to remove SynAck ransomware virus. What is more, the guidance below will help you recover encrypted documents, photos and music for free.
What is SynAck ransomware virus
SynAck is a variant of crypto viruses (malware which encrypt personal files and demand a ransom). It affects all current versions of Windows OS such as Windows XP, Windows Vista, Windows 7, Windows 8, Windows 10. This ransomware uses ECC (Elliptic Curve Cryptography) and AES algorithm to eliminate the possibility of brute force a key which will allow to decrypt encrypted documents, photos and music.
When the SynAck ransomware infects a machine, it uses system directories to store own files. To run automatically whenever you turn on your machine, SynAck ransomware creates a registry entry in Windows: sections HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ Run, HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ RunOnce, HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ Run, HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ RunOnce.
Immediately after the launch, the ransomware scans all available drives, including network and cloud storage, to determine which files will be encrypted. The ransomware uses the file name extension, as a way to define a group of files that will be subjected to encrypting. Encrypted almost all types of files, including common as:
.blob, .m3u, .wpa, .ws, .bay, .wbk, .wp, .crt, .desc, .gho, .mdbackup, .mov, .wmd, .mdb, .2bp, .xll, .m4a, .dxg, .sidd, .zip, .pef, .indd, .wdp, .arw, .layout, .pptx, .flv, .raf, .mrwref, .snx, .odp, .docm, .wpt, .lvl, .iwd, .srw, .ntl, .crw, .orf, .xpm, .wsd, .bik, .xdb, .ybk, .syncdb, .fos, .lrf, .bsa, .p7b, .wmo, .qdf, .wgz, .zip, .mcmeta, .vfs0, .wbc, .wma, .sid, .itdb, .raw, .xlsm, .wm, .rar, .itm, .ncf, .wps, .xlsx, .7z, .xls, .xld, .mp4, .odb, .m2, .arch00, .dcr, .xlgc, .upk, .avi, .wma, .wp6, .jpe, .png, .rb, .xwp, .x, .cdr, .xbplate, .rwl, .dbf, .ztmp, .doc, .eps, .xf, .wdb, .kdb, .tor, .rgss3a, .fpk, .r3d, .vdf, .vpp_pc, .sum, .pkpass, .x3d, .xlk, .zif, .wp4, .ptx, .rofl, .fsh, .sav, .zw, .sis, .asset, .epk, .wn, .dazip, .bc6, .pfx, .odc, .wpd, .wcf, .dmp, .3dm, .das, .xxx, .wpe, .ppt, .xlsm, .hplg, .sb, .jpg, .y, .csv, .webp, .vcf, .txt, .pptm, .sie, .nrw, .wav, .ysp, .xar, .xbdoc, .wbmp, .xmind, .svg, .vpk, .psk, .0, .tax, .docx, .xx, .ibank, .cas, .rtf, .odt, .mef, .db0, .iwi, .gdb, .cer, .dng, .zdb, .slm, .qic, .forge, .re4, .ltx, .pem, .icxs, .js, .1st, .sidn, .bar, .sr2, .wsc, .ai, .bc7, .x3f, .yml, .itl, .t12, .kf, .mddata, .bkf, .psd, .z3d, .der, .pak, .z, .wpw, .wmf, .xy3, .pst, .kdc, .hkx, .wri, .apk, .hkdb, .xlsb, .zdc, .wpl, wallet, .wpb, .3fr, .zabw, .big, .xdl, .erf, .wbd, .lbf, .wb2, .map, .hvpl, .py, .webdoc, .mdf, .wps, .rw2, .1, .wmv, .3ds, .vtf, .mpqge, .rim, .odm, .cr2, .wmv, .zi, .ff, .wbm, .dba, .litemod, .wbz, .xls, .yal, .x3f, .pdf, .wot, .xmmap, .wotreplay, .bkp, .wp5, .xyp, .d3dbsp, .mlx, .w3x, .esm, .xml, .wpd, .srf, .pdd, .jpeg, .t13, .ods, .dwg, .wsh, .xyw, .menu, .accdb, .wpg, .p7c, .sql
Once a file is encrypted, its extension modified to ten random alpha chars. For example, a file named sample.doc would be encrypted and renamed to sample.doc.THGRDFxbgr. Next, the SynAck ransomware virus creates a file named “RESTORE_INFO-[ID].txt”. This file contain guide on how to decrypt all encrypted personal files. Examples of the instructions are:
Files on your computer are encrypted. Algorithm: ecc-secp192r1 & aes-ecb-256 To decrypt your files, please contact us using one of these e-mail addresses: [email protected] [email protected] [email protected] Please include the following text in your message:
Syn---- > Ack---- > ================================================================================== Files are encrypted, algorithm used: ecies-secp192r1 & aes-ecb-256. To decrypt your files, please contact us using this e-mail address: [email protected] If for unknown reasons you did not receive any answer on e-mail, write to BitMessage (using site https://bitmsg.me/): BM-2cStoatQC4mDNWDHAoo2C1nYZJXhDsjCLj Please do not perform any manipulations with encrypted files. If you want to try to restore your files manually, do backups first. And please do not remove files with text notes, because they contain important information required for file restoring. Please include the following text in your message:
Files are encrypted, algorithm used: ecies-secp192r1 & aes-ecb-256. To decrypt your files, please contact us using this e-mail address: [email protected] If for unknown reasons you did not receive any answer on e-mail, write to BitMessage (using site https://bitmsg.me/): BM-2cWsgWxq1X5M6qjDEBPvCdEbbPLn2zi43k Please do not perform any manipulations with encrypted files. If you want to try to restore your files manually, do backups first. And please do not remove files with text notes, because they contain important information required for file restoring. Please include the following text in your message:
The SynAck ransomware actively uses scare tactics by giving the victim a brief description of the encryption algorithm and showing a ransom instructions on the desktop. It is trying to force the user of the infected PC, do not hesitate to pay a ransom, in an attempt to restore their documents, photos and music.
How to decrypt files encrypted by SynAck ransomware
Currently there is no available way to decrypt encrypted files, but you have a chance to recover encrypted photos, documents and music for free. The ransomware virus repeatedly tells the victim that uses a strong encryption algorithm with a large key. What does it mean to decrypt the files is impossible without the decrypt program. Use a “brute forcing” is also not a solution because of the big length of the key. Therefore, unfortunately, the only payment to the authors of the SynAck ransomware virus entire amount requested – the only way to try to get the decryption key and decrypt all your files.
There is absolutely no guarantee that after pay a ransom to the makers of the SynAck ransomware virus, they will provide the necessary key to decrypt your files. In addition, you must understand that paying money to the cyber criminals, you are encouraging them to create a new ransomware infection.
How to remove SynAck ransomware
There are not many good free antimalware programs with high detection ratio. The effectiveness of malicious software removal tools depends on various factors, mostly on how often their virus/malware signatures DB are updated in order to effectively detect modern malicious software, ‘ad supported’ software, ransomware viruses and other malware. We suggest to use several applications, not just one. These applications which listed below will help you remove all components of the SynAck ransomware virus from your disk and Windows registry.
To Remove SynAck ransomware, use the following steps:
- Remove SynAck ransomware with Zemana Anti-malware
- Remove SynAck virus with Malwarebytes
- Remove SynAck from computer with KVRT
Remove SynAck ransomware with Zemana Anti-malware
We recommend using the Zemana Anti-malware that are completely clean your machine of the ransomware. The utility is an advanced malicious software removal program made by (c) Zemana lab. It’s able to help you remove potentially unwanted software, ransomware, ad-supported software, malware and other security threats from your personal computer for free.
Download Zemana anti malware on your computer from the following link.
165741 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
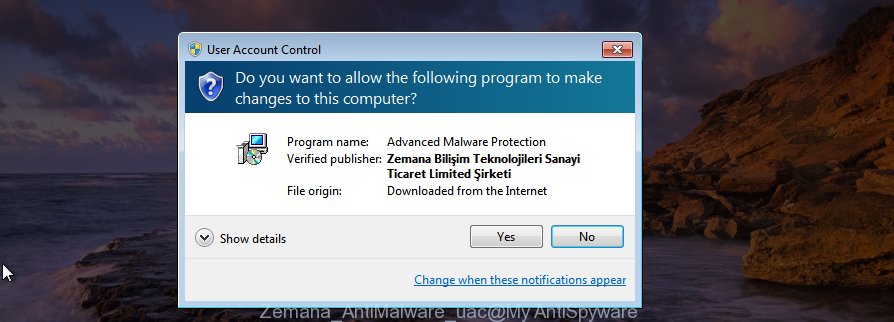
Once the downloading process is done, close all programs and windows on your PC system. Double-click the set up file named Zemana.AntiMalware.Setup. If the “User Account Control” prompt pops up as shown in the following example, click the “Yes” button.
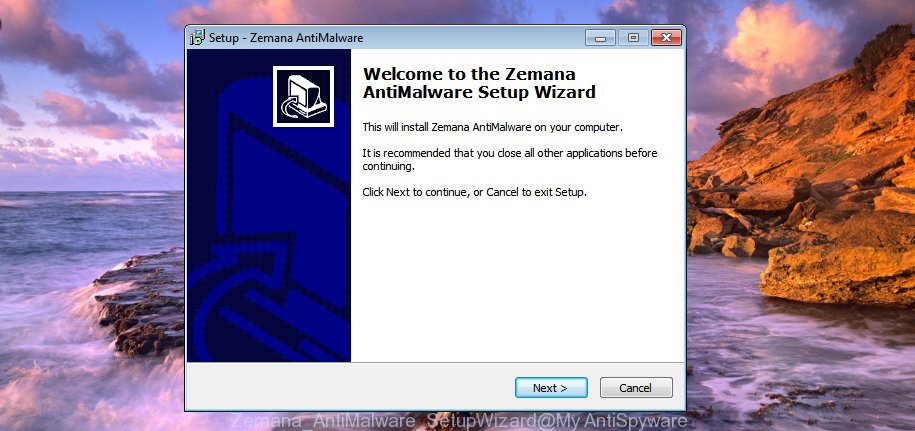
It will open the “Setup wizard” that will help you install Zemana anti-malware on your computer. Follow the prompts and do not make any changes to default settings.
Once install is finished successfully, Zemana anti-malware will automatically start and you can see its main screen as shown below.

Now click the “Scan” button to perform a system scan with this tool for the SynAck ransomware virus . This procedure can take quite a while, so please be patient. While the utility is scanning, you can see number of objects it has identified as being infected by malware.

As the scanning ends, a list of all items detected is produced. In order to get rid of all items, simply click “Next” button. The Zemana anti-malware will start removing SynAck virus and other security threats. Once disinfection is complete, you may be prompted to reboot the machine.
Remove SynAck virus with Malwarebytes
Get rid of SynAck ransomware infection manually is difficult and often the virus is not completely removed. Therefore, we recommend you to use the Malwarebytes Free that are completely clean your system. Moreover, the free program will help you to remove malicious software, PUPs, toolbars and ad-supported software that your machine can be infected too.
Download Malwarebytes from the link below. Save it on your MS Windows desktop or in any other place.
328051 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
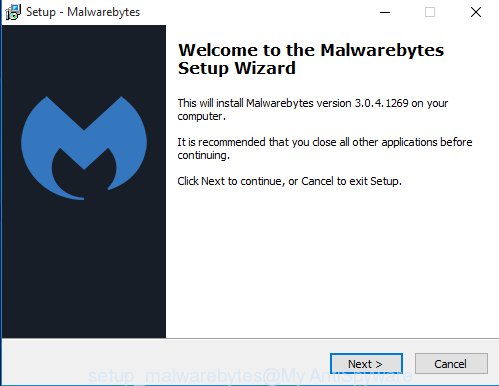
Once the downloading process is finished, close all software and windows on your PC system. Open a directory in which you saved it. Double-click on the icon that’s named mb3-setup as shown in the following example.
![]()
When the installation begins, you will see the “Setup wizard” which will help you install Malwarebytes on your computer.
Once setup is complete, you will see window as on the image below.
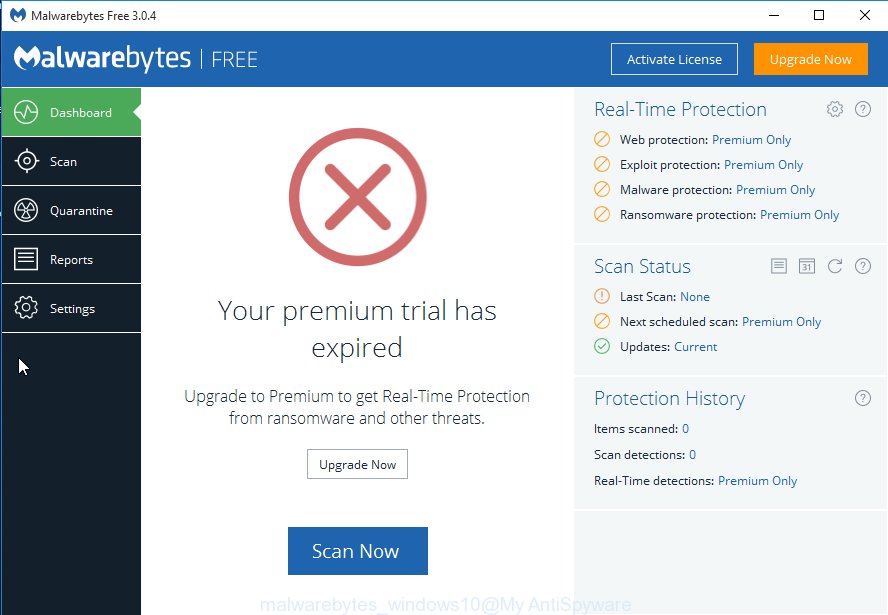
Now click the “Scan Now” button for checking your machine for the SynAck ransomware infection and other known infections. Depending on your computer, the scan can take anywhere from a few minutes to close to an hour. When a malicious software, ad supported software or PUPs are detected, the number of the security threats will change accordingly. Wait until the the checking is finished.
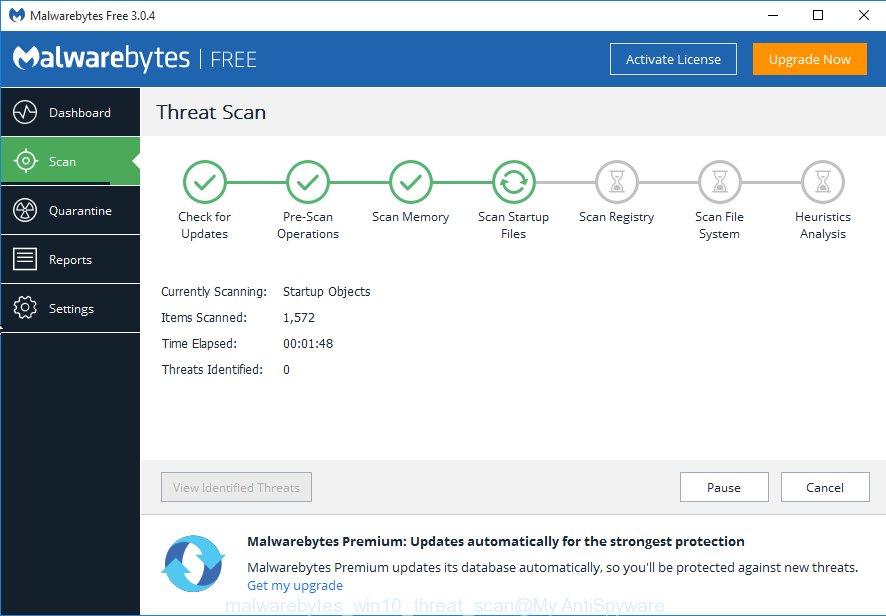
Once the system scan is finished, you can check all threats found on your PC. In order to remove all threats, simply press “Quarantine Selected” button.
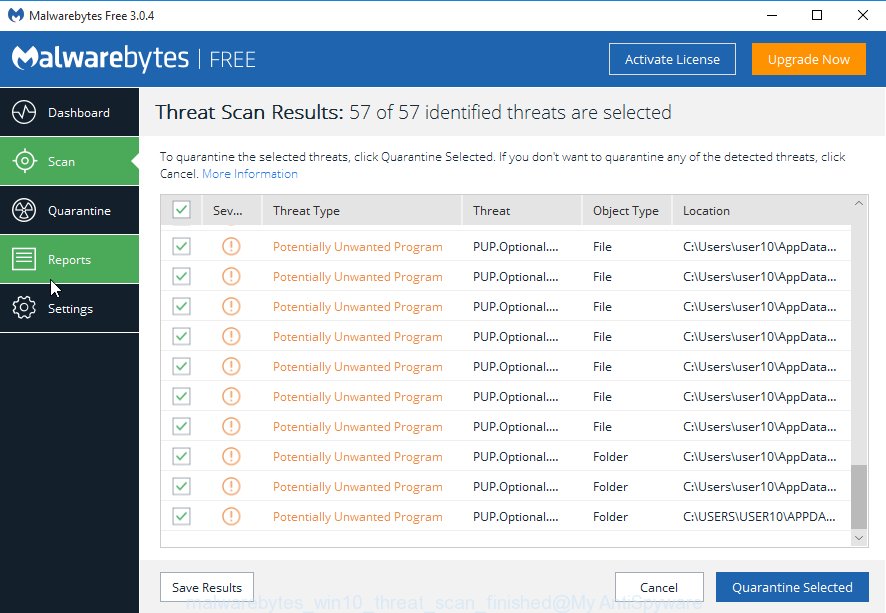
The Malwarebytes will start removing SynAck ransomware virus related files, folders, registry keys. Once disinfection is done, you may be prompted to reboot your computer.
The following video explains step-by-step tutorial on how to delete virus and other malware with Malwarebytes Anti-malware.
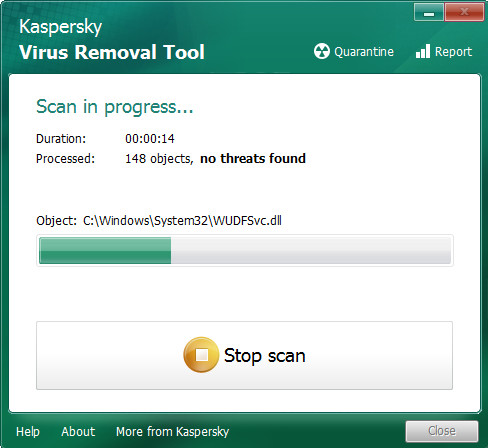
Remove SynAck from computer with KVRT
KVRT is a free portable program that scans your computer for adware, PUPs and viruss such as SynAck and allows remove them easily. Moreover, it’ll also help you get rid of any harmful browser extensions and add-ons.
Download Kaspersky virus removal tool (KVRT) by clicking on the link below and save it to your Desktop.
129572 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
Once the downloading process is finished, double-click on the KVRT icon. Once initialization process is finished, you will see the KVRT screen as shown below.
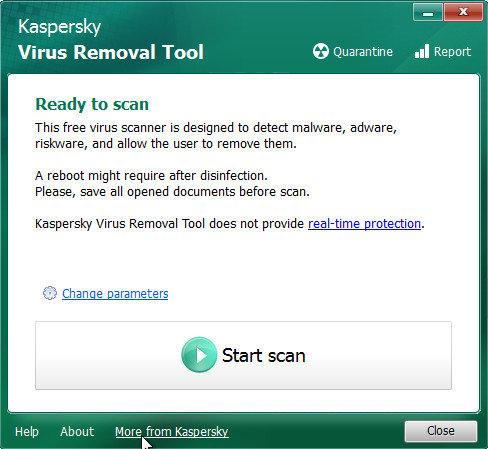
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next press Start scan button for checking your computer for the SynAck ransomware virus and other malicious software. A system scan can take anywhere from 5 to 30 minutes, depending on your machine. During the scan it will detect all threats exist on your personal computer.
After it has completed scanning, a list of all threats detected is produced as shown in the figure below.
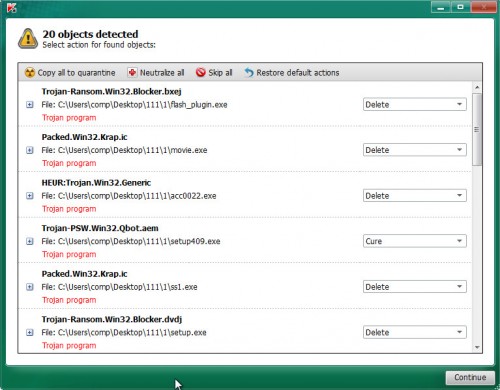
When you’re ready, press on Continue to begin a cleaning procedure.
How to restore files encrypted by SynAck ransomware
In some cases, you can restore files encrypted by SynAck ransomware virus. Try both methods. Important to understand that we cannot guarantee that you will be able to recover all encrypted personal files.
To restore files encrypted by SynAck ransomware, use the following steps:
- Restore files encrypted by SynAck ransomware with ShadowExplorer
- Recover files encrypted by SynAck virus with PhotoRec
Restore files encrypted by SynAck ransomware with ShadowExplorer
If automated backup (System Restore) is enabled, then you can use it to recover all encrypted files to previous versions.
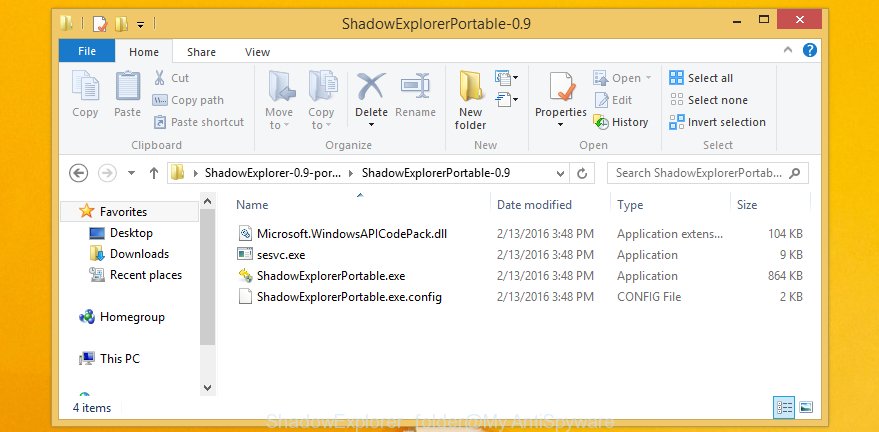
Download ShadowExplorer from the following link. This utility is available for Windows Vista, Windows 7, Windows 8 and Windows 10.
440334 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
Once the downloading process is finished, open a directory in which you saved it. Right click to ShadowExplorer-0.9-portable and choose Extract all. Follow the prompts. Next please open the ShadowExplorerPortable folder as displayed below.
Run ShadowExplorerPortable. You will see the a window as displayed in the figure below.
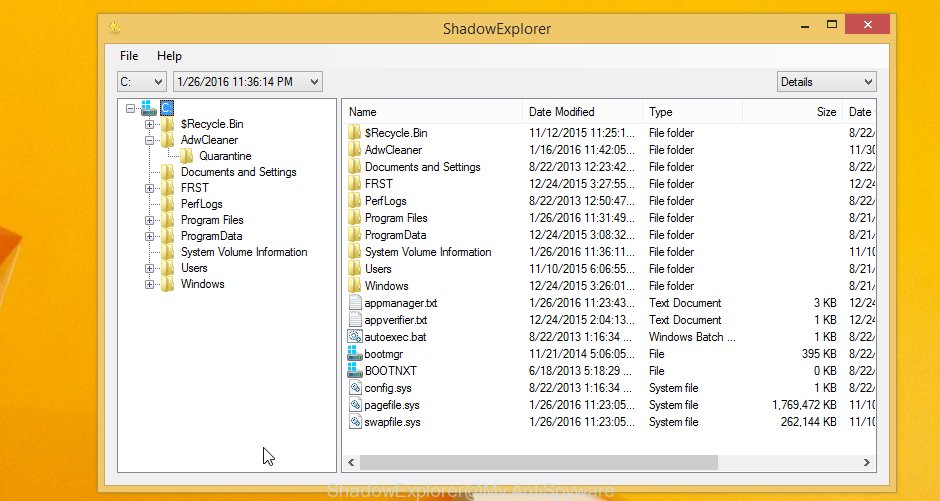
From the first drop down list you can select a drive that contains encrypted photos, documents and music, from the second drop down list you can select the date that you wish to restore from. 1 – drive, 2 – restore point, as displayed on the image below.
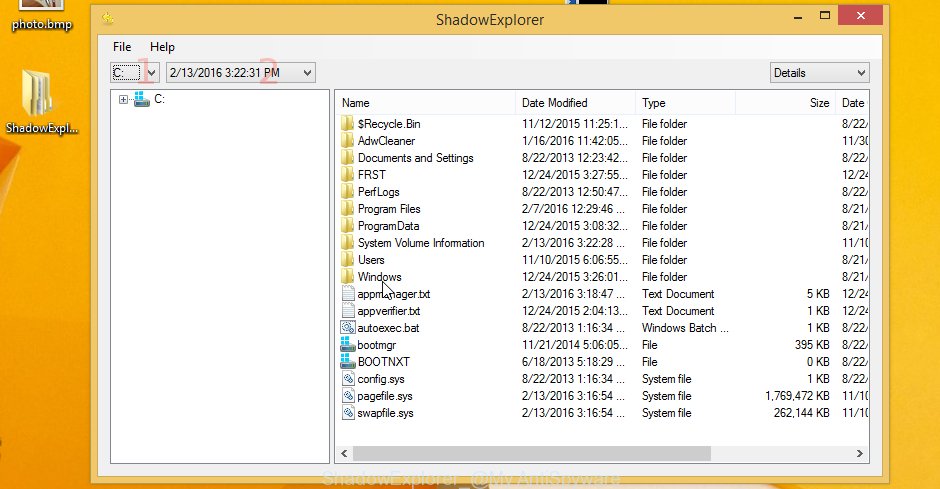
Righ-click entire folder or any one encrypted file and choose Export, as shown below.

It will open a prompt that asking whether you’d like to restore a file or the contents of the folder to.
Recover files encrypted by SynAck ransomware with PhotoRec
Before a file is encrypted, the SynAck ransomware virus makes a copy of this file, encrypts it, and then deletes the original file. This can allow you to restore your documents, photos and music using file restore programs such as PhotoRec.
Download PhotoRec from the following link. Save it on your Desktop.
Once the download is finished, open a directory in which you saved it. Right click to testdisk-7.0.win and choose Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as displayed on the image below.

Double click on qphotorec_win to run PhotoRec for MS Windows. It will show a screen as on the image below.
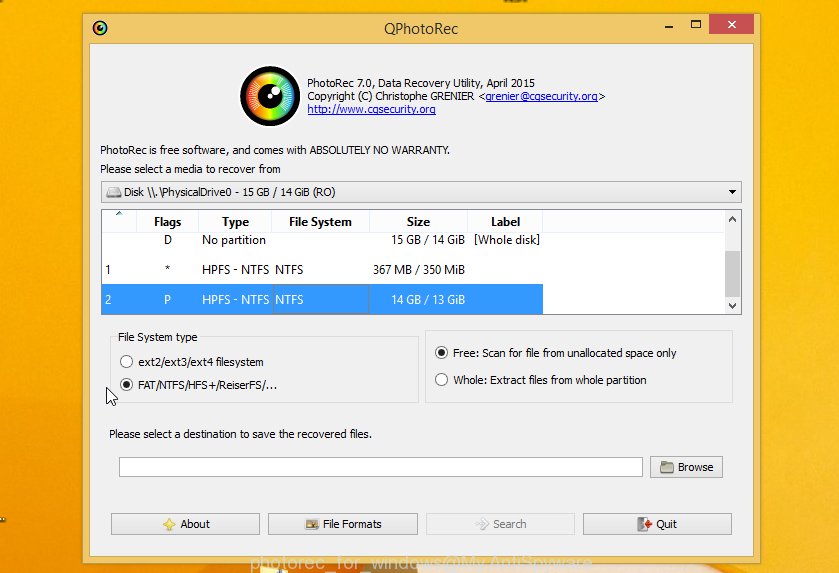
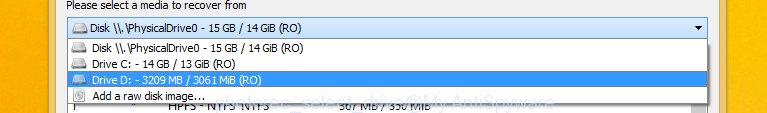
Select a drive to recover as displayed in the following example.
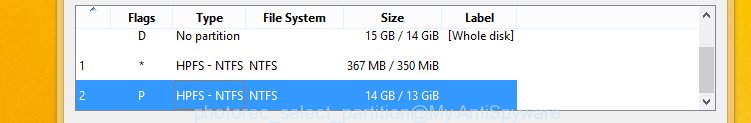
You will see a list of available partitions. Select a partition that holds encrypted files as displayed below.
Press File Formats button and specify file types to recover. You can to enable or disable the restore of certain file types. When this is finished, click OK button.
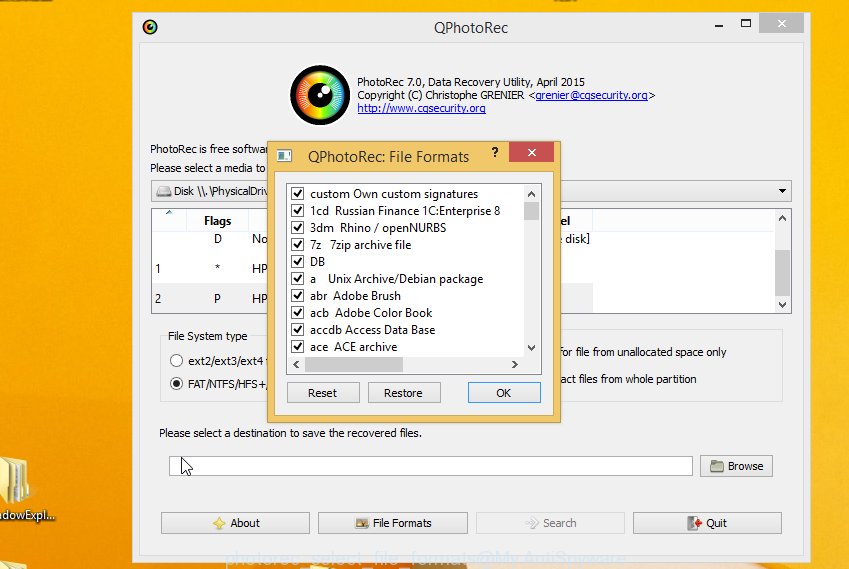
Next, click Browse button to choose where restored personal files should be written, then click Search.
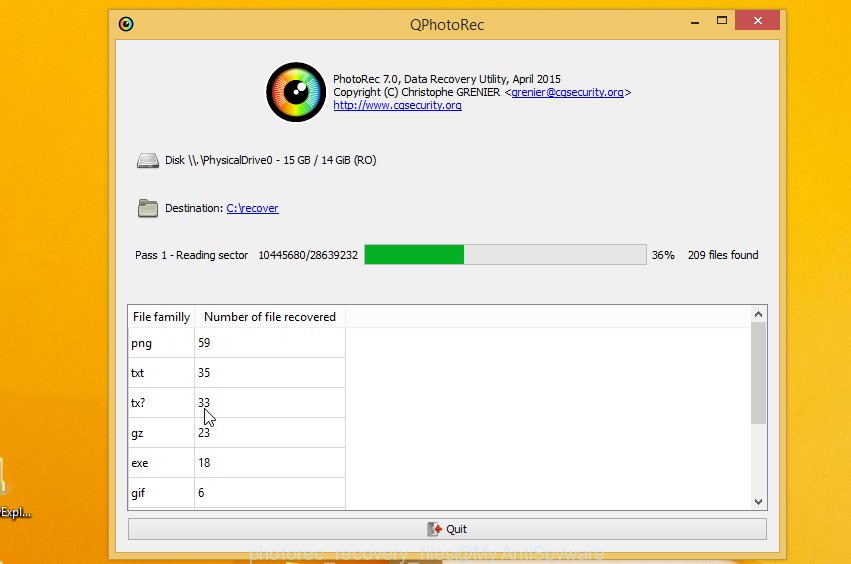
Count of recovered files is updated in real time. All restored documents, photos and music are written in a folder that you have selected on the previous step. You can to access the files even if the restore process is not finished.
When the restore is finished, click on Quit button. Next, open the directory where restored files are stored. You will see a contents as on the image below.
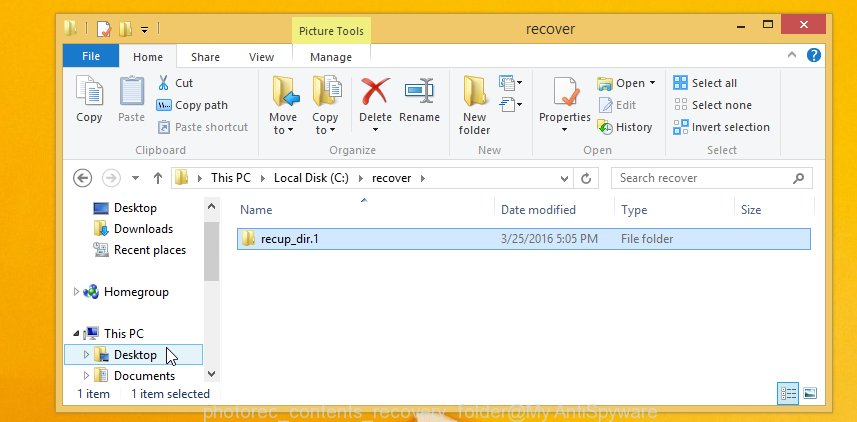
All restored documents, photos and music are written in recup_dir.1, recup_dir.2 … sub-directories. If you’re searching for a specific file, then you can to sort your recovered files by extension and/or date/time.
How to prevent your personal computer from becoming infected by SynAck ransomware?
Most antivirus applications already have built-in protection system against any ransomware. Therefore, if your computer does not have an antivirus program, make sure you install it. As an extra protection, run the CryptoPrevent.
Run CryptoPrevent to protect your PC system from SynAck virus
Download CryptoPrevent from the following link. Save it on your Windows desktop.
www.foolishit.com/download/cryptoprevent/
Run it and follow the setup wizard. Once the installation is finished, you’ll be shown a window where you can select a level of protection, as shown in the figure below.
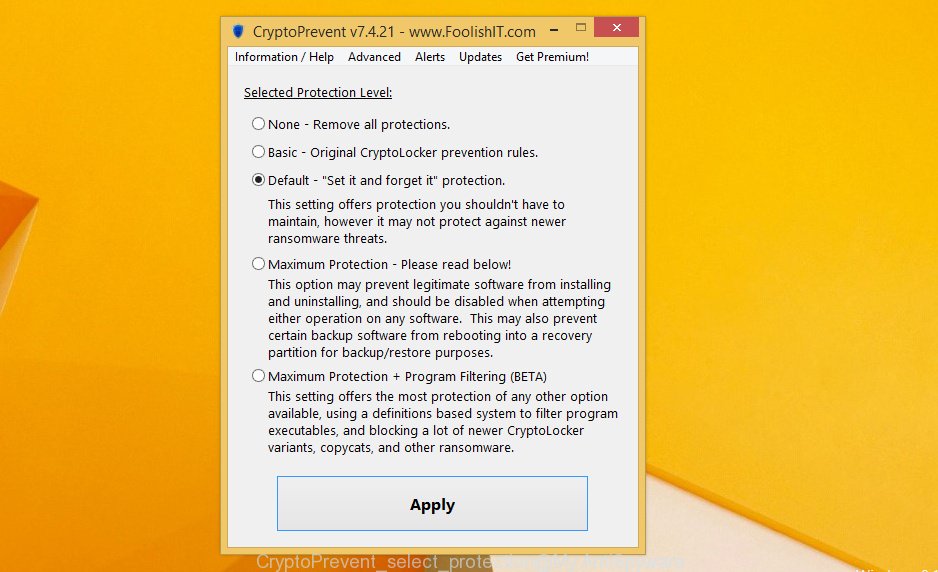
Now press the Apply button to activate the protection.
Finish words
Once you have complete the instructions shown above, your personal computer should be clean from SynAck ransomware and other malware. Your personal computer will no longer encrypt your personal files. Unfortunately, if the instructions does not help you, then you have caught a new variant of virus, and then the best way – ask for help.
- Download HijackThis by clicking on the link below and save it to your Desktop.
HijackThis download
5452 downloads
Version: 2.0.5
Author: OpenSource
Category: Security tools
Update: November 7, 2015
- Double-click on the HijackThis icon. Next click “Do a system scan only” button.
- When it has finished scanning, the scan button will read “Save log”, click it. Save this log to your desktop.
- Create a Myantispyware account here. Once you’ve registered, check your e-mail for a confirmation link, and confirm your account. After that, login.
- Copy and paste the contents of the HijackThis log into your post. If you are posting for the first time, please start a new thread by using the “New Topic” button in the Spyware Removal forum. When posting your HJT log, try to give us some details about your problems, so we can try to help you more accurately.
- Wait for one of our trained “Security Team” or Site Administrator to provide you with knowledgeable assistance tailored to your problem with the SynAck ransomware virus.






















