Hello! You’ve been hacked! is a new Bitcoin Email Scam that has been spreading on the Internet recently. Many people from all over the world have received such emails and reported about it on the Internet.
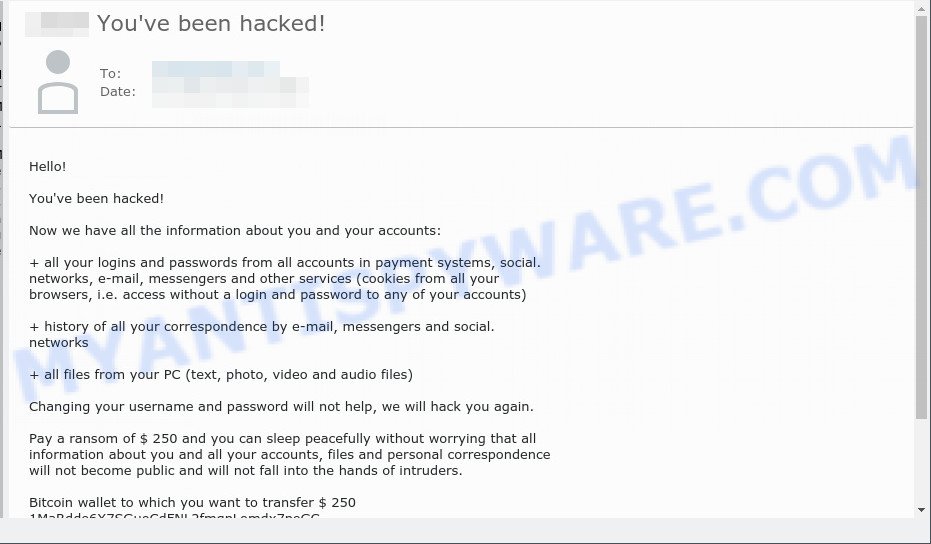
You’ve been hacked! email scam
Scammers use threats to get a ransom from the recipients of such emails. Despite the fact that these email messages are very suspicious, and most people simply delete them, scammers hope that at least a few recipients will be naive enough and pay a ransom.
There are variations in the wording of the email body, but all of these messages are basically the same. Below is one of the scam variants that are slightly different from each other.
Hello!
You’ve been hacked!
Now we have all the information about you and your accounts:
+ all your logins and passwords from all accounts in payment systems, social. networks, e-mail, messengers and other services (cookies from all your browsers, i.e. access without a login and password to any of your accounts)
+ history of all your correspondence by e-mail, messengers and social. networks
+ all files from your PC (text, photo, video and audio files)
Changing your username and password will not help, we will hack you again.
Pay a ransom of $ 250 and you can sleep peacefully without worrying that all information about you and all your accounts, files and personal correspondence will not become public and will not fall into the hands of intruders.
Bitcoin wallet to which you want to transfer $ 250
If you do not pay until tomorrow evening, then we will sell all this information on the darknet, there is a huge demand for such information
Pay $ 250 and sleep well!
What is Bitcoin email scam
Bitcoin email scam is old extortion scheme – which try to guilt people into paying off someone claiming to have secretly recorded video or compromising information. Scammers uses the database of emails to sent this email scam out to millions of people around the World. The messages are sent to email addresses exposed in previous known data breaches in which the user database (email address and/or password) was indexed online.
Should you pay?
The best advice is: Don’t pay the ransom! If you receive the blackmail scam, just ignore the scammers’ empty threats. The best way to deal with the scam email is simply to move it to trash!
Threat Summary
| Name | You’ve been hacked! SCAM |
| Type | Phishing, Bitcoin Email Scam, Fraud, Scam |
| Ransom amount | $250 |
| Distribution method | spam email campaigns |
| Removal | If you gets an email like You’ve been hacked!, our computer security experts recommend follow some easy steps below |
What to do when you receive the You’ve been hacked! SCAM
We advice to someone who gets this fraudulence message:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email spam to the FTC at https://www.ftc.gov/
- Scan your computer for malware.
- Install an anti-phishing software.
How to scan your PC for malware
Zemana AntiMalware highly recommended, because it can detect security threats such as adware, PUPs, trojans and malicious software which most ‘classic’ antivirus apps fail to pick up on. Moreover, if you have any malware removal problems which cannot be fixed by this utility automatically, then Zemana provides 24X7 online assistance from the highly experienced support staff.
Go to the following link to download Zemana installation package called Zemana.AntiMalware.Setup on your PC system. Save it to your Desktop.
165075 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
Run the installation package after it has been downloaded successfully and then follow the prompts to set up this utility on your PC.
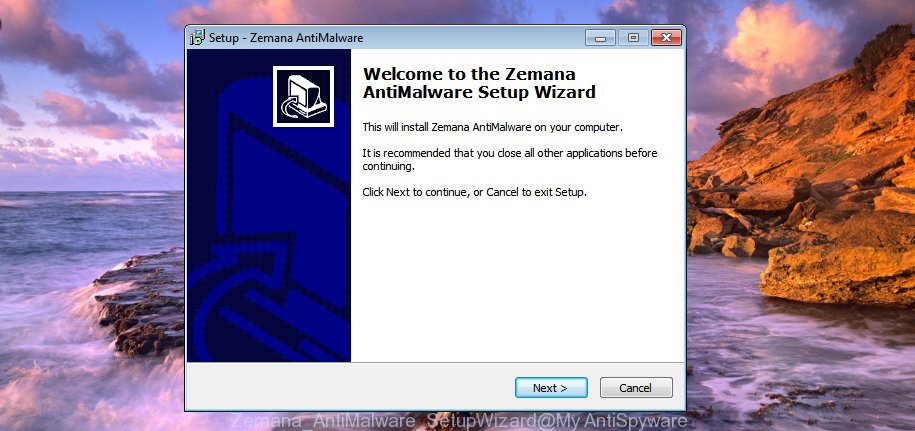
During install you can change some settings, but we suggest you don’t make any changes to default settings.
When installation is finished, this malicious software removal utility will automatically run and update itself. You will see its main window as shown in the figure below.

Now press the “Scan” button to start scanning your personal computer for malware. This process can take quite a while, so please be patient. While the utility is checking, you may see count of objects and files has already scanned.

When the scan is finished, Zemana Anti-Malware will display a list of all threats found by the scan. Make sure all items have ‘checkmark’ and press “Next” button.
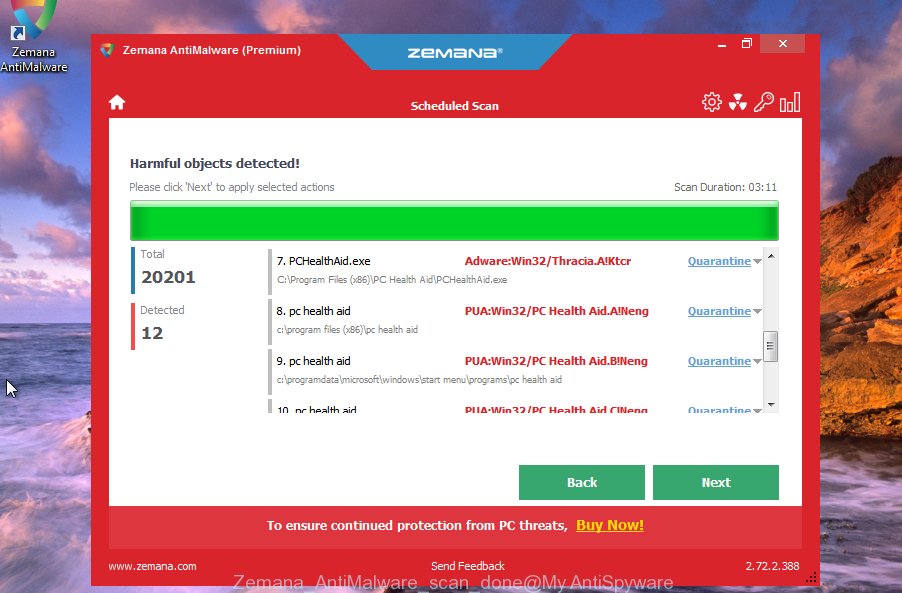
The Zemana will remove malicious software and move the selected items to the program’s quarantine. After disinfection is complete, you may be prompted to restart your computer to make the change take effect.
If you are having issues with malware removal, then check out MalwareBytes Anti Malware (MBAM). This is a utility that can help clean up your computer and improve your speeds for free. Find out more below.
Go to the link below to download MalwareBytes Free. Save it directly to your Microsoft Windows Desktop.
327297 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
Once the download is done, close all apps and windows on your PC system. Open a directory in which you saved it. Double-click on the icon that’s named MBSetup as displayed in the following example.
![]()
When the install begins, you’ll see the Setup wizard that will help you set up Malwarebytes on your computer.
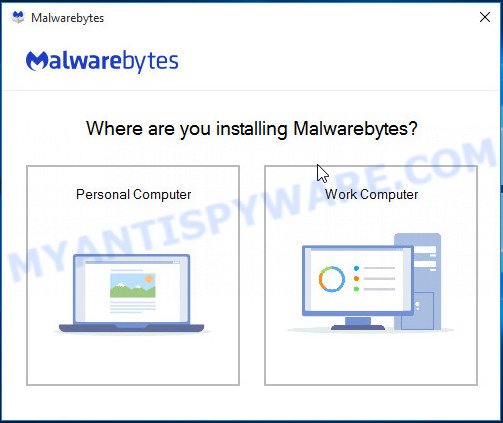
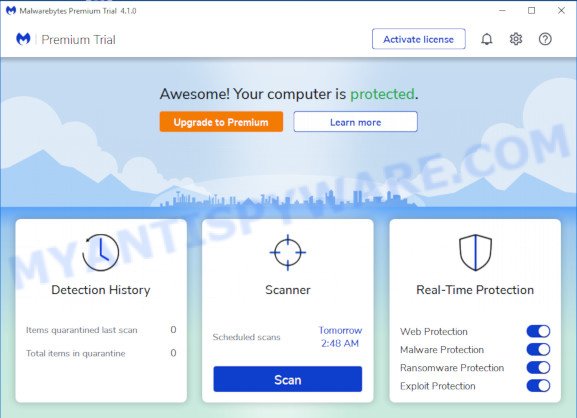
Once installation is complete, you’ll see window as on the image below.
Now click the “Scan” button to scan your computer for malicious software. A scan can take anywhere from 10 to 30 minutes, depending on the number of files on your personal computer and the speed of your personal computer. While the utility is scanning, you can see number of objects and files has already scanned.
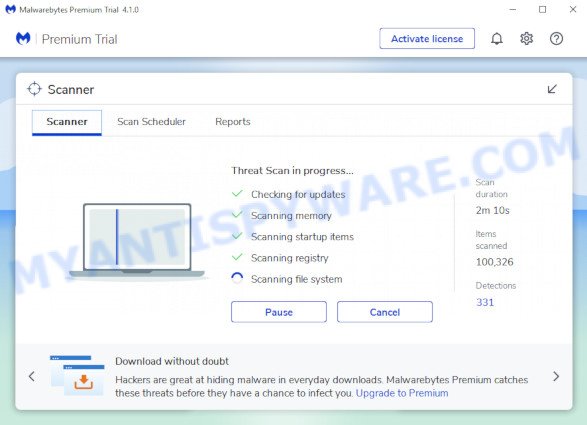
When MalwareBytes Free completes the scan, MalwareBytes AntiMalware will display a list of all items found by the scan. Review the scan results and then press “Quarantine” button.
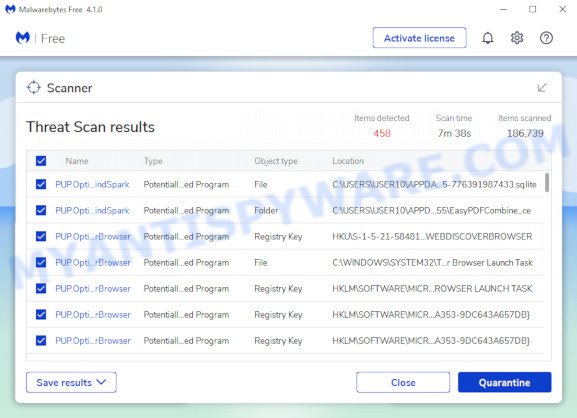
The Malwarebytes will now delete malicious software and move the selected items to the Quarantine. After that process is finished, you may be prompted to restart your device.

The following video explains guidance on how to get rid of browser hijackers, adware software and other malware with MalwareBytes AntiMalware (MBAM).
How to protect yourself from phishing, malicious and misleading websites
If you want to protect yourself from phishing websites, then install an ad blocker program such as AdGuard. It can block malicious and misleading web sites, stop unwanted advertisements and popups when using the Internet Explorer, Google Chrome, Firefox and Edge. So, if you like surf the Internet, and want to protect your computer from malicious web pages, then the AdGuard is your best choice.
Installing the AdGuard is simple. First you’ll need to download AdGuard by clicking on the link below.
26905 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as displayed below.
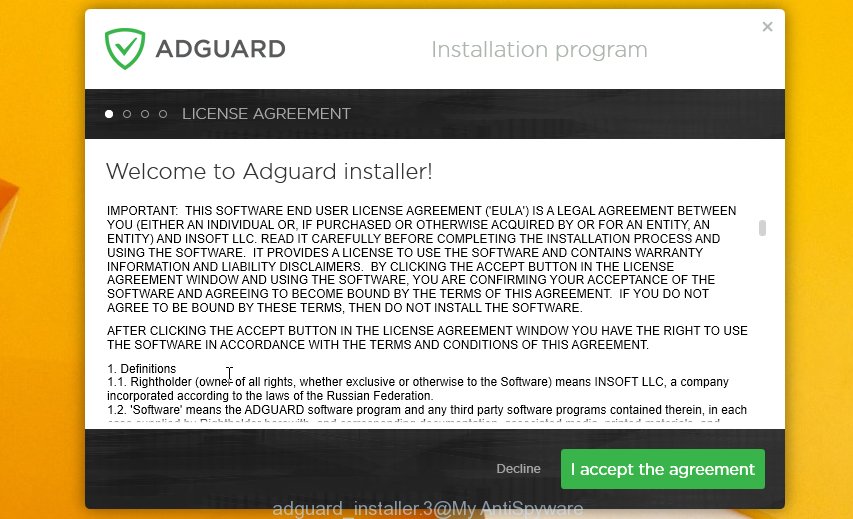
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guide as displayed on the screen below.

Click “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick guidance which will assist you get to know AdGuard better.
Each time, when you start your system, AdGuard will start automatically and stop unwanted advertisements, block phishing, as well as other harmful or misleading websites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
We hope that this article helped you understand what the You’ve been hacked! SCAM is and not succumb to the threats of scammers. If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. It will help our team monitor the latest scams.

















