The email message titled “Your account is being used by another person” or “Your account is being accessed by another person!” is the latest phishing scam affecting lots of people. Thankfully, this email is a fake! Your email account, your computer and other devices have not been hacked.
The “Your account is being used by another person” email is nothing more than a phishing scam.
“Your account is being accessed by another person!” email scam
There is one thing that it does to make itself appear real. It uses your own e-mail address as the “From” address, but do not be fooled. This phishing scam uses so-called “email spoofing”. Email spoofing is the creation of email messages with a forged sender address. Email spoofing has been around for a long time! Scammers use it in phishing attacks to force users into thinking they have received mail message from a friend or trusted person.
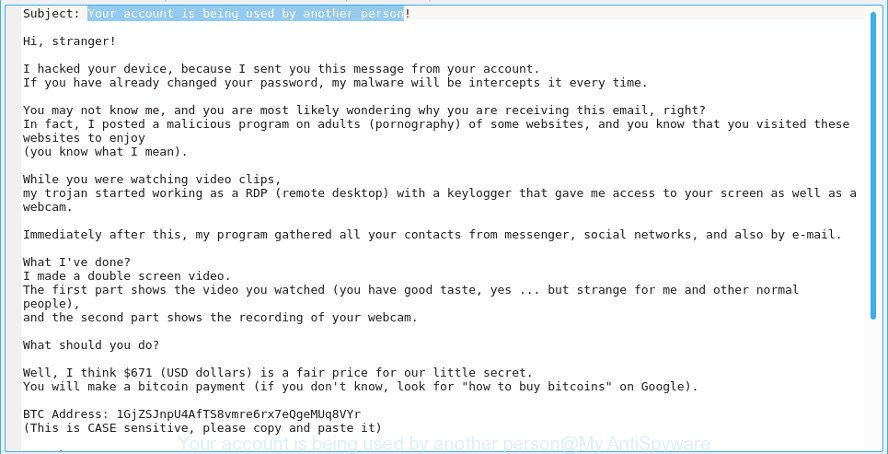
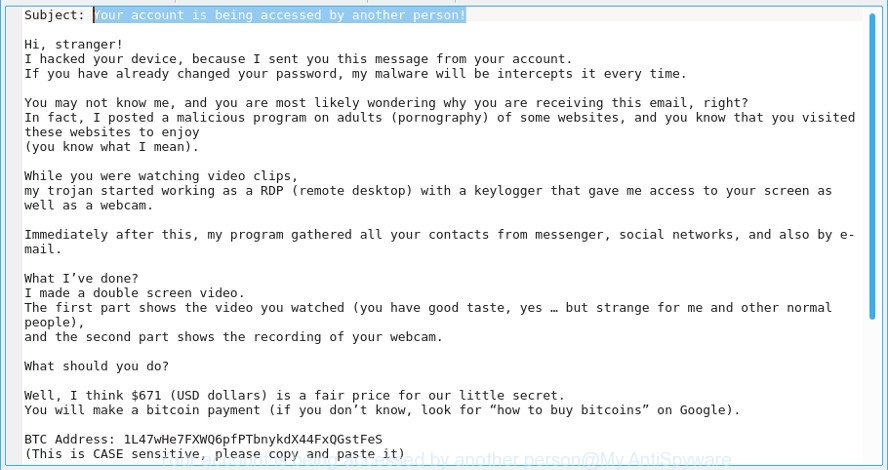
Cyber security specialists continue to receive reports of fraudulent e-mail messages. Here below is an example. Recent version demands $671 ransom payment (BTC Wallets are: 1GVDLggCfp4yQL8aAQQxB5qwqTFFQyd4fY, 1GjZSJnpU4AfTS8vmre6rx7eQgeMUq8VYr, 1L47wHe7FXWQ6pfPTbnykdX44FxQGstFeS).
Hi, stranger! I hacked your device, because I sent you this message from your account. If you have already changed your password, my malware will be intercepts it every time. You may not know me, and you are most likely wondering why you are receiving this email, right? In fact, I posted a malicious program on adults (pornography) of some websites, and you know that you visited these websites to enjoy (you know what I mean). While you were watching video clips, my trojan started working as a RDP (remote desktop) with a keylogger that gave me access to your screen as well as a webcam. Immediately after this, my program gathered all your contacts from messenger, social networks, and also by e-mail. What I've done? I made a double screen video. The first part shows the video you watched (you have good taste, yes ... but strange for me and other normal people), and the second part shows the recording of your webcam. What should you do? Well, I think $671 (USD dollars) is a fair price for our little secret. You will make a bitcoin payment (if you don't know, look for "how to buy bitcoins" on Google). BTC Address: 1GjZSJnpU4AfTS8vmre6rx7eQgeMUq8VYr, 1L47wHe7FXWQ6pfPTbnykdX44FxQGstFeS (This is CASE sensitive, please copy and paste it) Remarks: You have 2 days (48 hours) to pay. (I have a special code, and at the moment I know that you have read this email). If I don't get bitcoins, I will send your video to all your contacts, including family members, colleagues, etc. However, if I am paid, I will immediately destroy the video, and my trojan will be destruct someself. If you want to get proof, answer "Yes!" and resend this letter to youself. And I will definitely send your video to your any 19 contacts. This is a non-negotiable offer, so please do not waste my personal and other people's time by replying to this email. Bye!
What to do when you receive “Your account is being used by another person” email scam
Here are some easy steps which you need to follow after receiving the email message to keep yourself safe.
- First, do not pay the cyber criminals.
- Do not panic.
- Mark the email as SPAM (junk mail)
- Avoid clicking links in email.
- Turn off or cover any web cams when you are not using them to prevent sex-based extortion schemes.
- Report any scams like these to the FBI.
- Scan your computer for malware
- Install an anti-phishing software
- If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article.
How to scan your computer for malware and protect your PC from phishing scams
There are a few methods that can be used to scan your computer for malware and protect your system from phishing scams. Most cyber threat analysts states that Zemana Anti Malware, MalwareBytes Anti Malware (MBAM) or HitmanPro tools are a right choice. These free applications are able to scan for and remove malware from your computer and protect your computer from phishing attacks.
- How to uninstall suspicious software through the Windows Control Panel
- How to detect and remove malware
- How to stay safe online
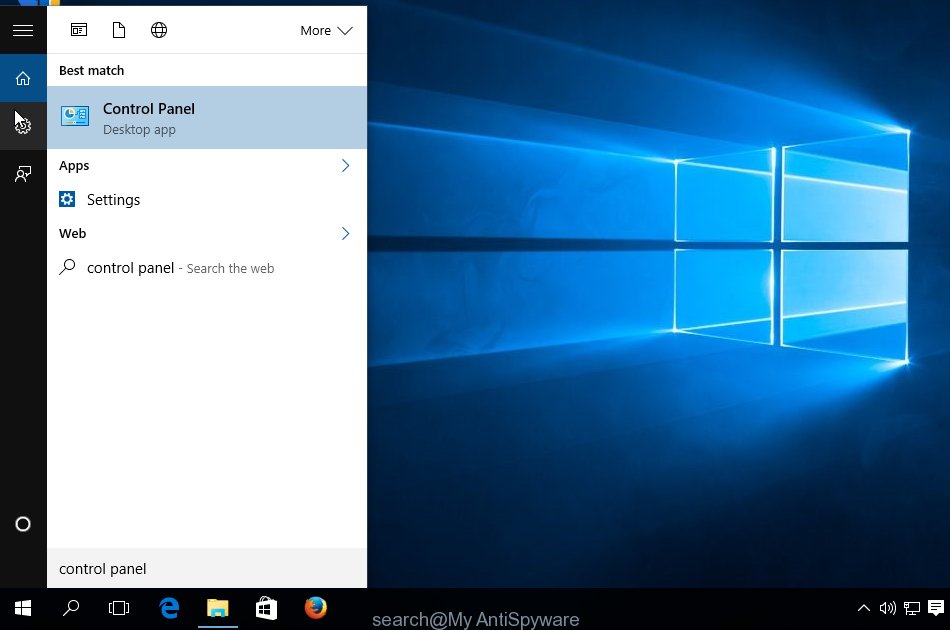
How to uninstall suspicious software through the Windows Control Panel
First method for manual malware is check out the Windows Control Panel (Programs and Features section) to see all installed programs. We suggest to click on the “Date Installed” in order to sort the list of programs by the date you installed them. If you see any unknown and suspicious programs, they are the ones you need to remove.
First, click Windows button ![]() , then click Search
, then click Search ![]() . Type ‘Control panel’and press Enter as on the image below.
. Type ‘Control panel’and press Enter as on the image below.
After the ‘Control Panel’ opens, click the ‘Uninstall a program’ link under Programs category as displayed in the following example.
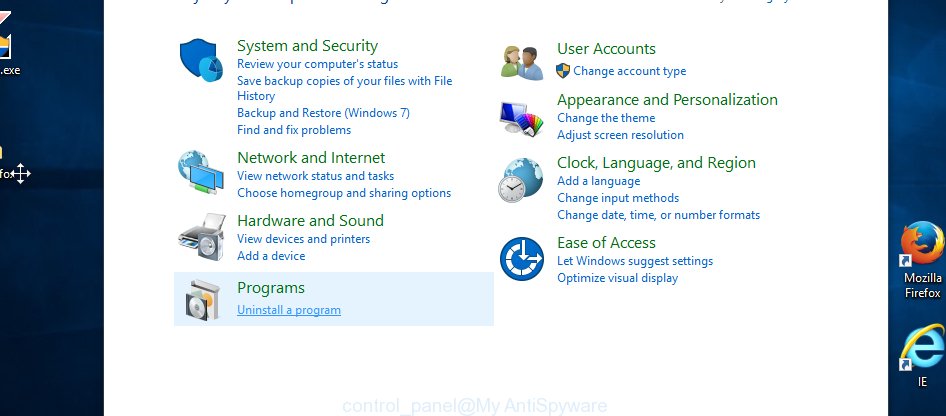
You will see the ‘Uninstall a program’ panel as shown on the image below.

Very carefully look around the entire list of apps installed on your computer. Once you have found a dubious, unwanted or unused application, right click to it, after that click ‘Uninstall’.
How to detect and remove malware
If you are not expert at computer technology, then we recommend to run malware removal tool named “Zemana Anti Malware” (ZAM). Zemana Free highly recommended, because it can look for security threats such as key-loggers, spyware, adware and browser hijackers which most ‘classic’ antivirus apps fail to pick up on. Moreover, it does not need any drivers and special dlls. It’s probably easier to use than any alternative malware removal tools you have ever tried.
Visit the page linked below to download the latest version of Zemana Anti Malware (ZAM) for MS Windows. Save it to your Desktop so that you can access the file easily.
165054 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
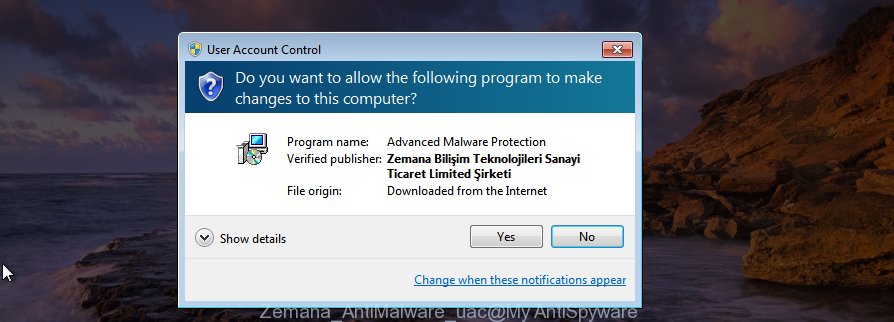
When the download is complete, close all windows on your PC system. Further, open the setup file named Zemana.AntiMalware.Setup. If the “User Account Control” dialog box pops up as on the image below, click the “Yes” button.
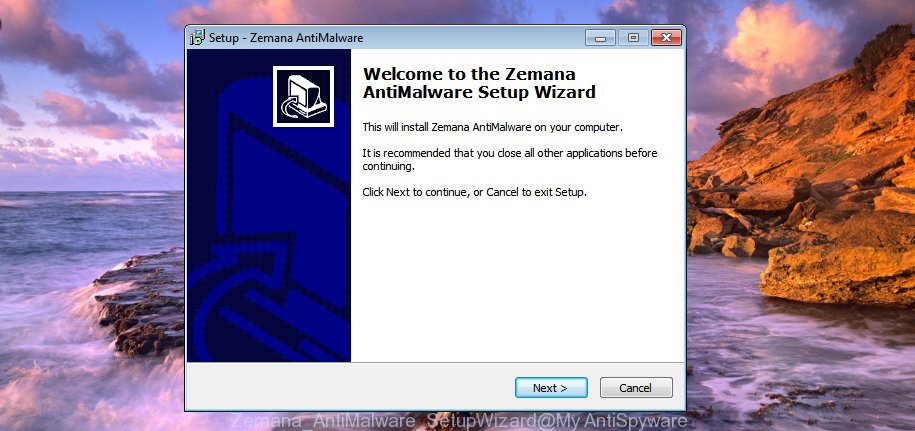
It will display the “Setup wizard” which will assist you install Zemana Anti-Malware on the computer. Follow the prompts and do not make any changes to default settings.
Once installation is done successfully, Zemana Free will automatically launch and you can see its main window as displayed on the screen below.

Next, click the “Scan” button to start scanning your personal computer for malware and other security threats. This task can take quite a while, so please be patient. While the Zemana AntiMalware utility is scanning, you can see how many objects it has identified as being infected by malicious software.

When the scan is finished, the results are displayed in the scan report. Make sure all items have ‘checkmark’ and click “Next” button.
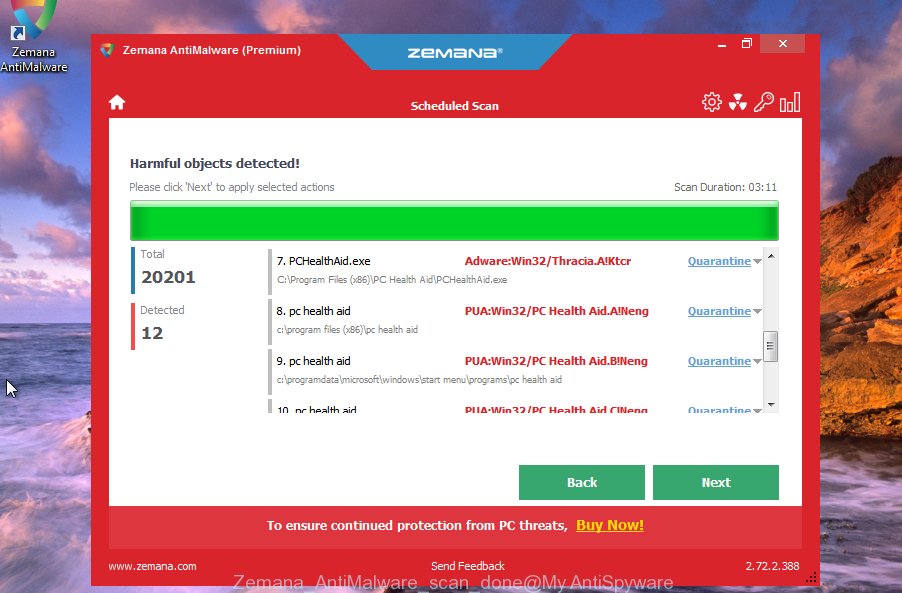
The Zemana AntiMalware (ZAM) will delete malware and other unwanted software. Once finished, you can be prompted to restart your machine.
How to stay safe online
In order to increase your security and protect your computer against phishing web-sites, malicious advertising and shady webpages, you need to run ad blocking program that blocks an access to harmful ads and malicious web pages. Moreover, the program can block the show of intrusive advertising, that also leads to faster loading of websites and reduce the consumption of web traffic.
Installing the AdGuard is simple. First you will need to download AdGuard on your Windows Desktop by clicking on the link below.
26903 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
When the downloading process is finished, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as shown on the image below.
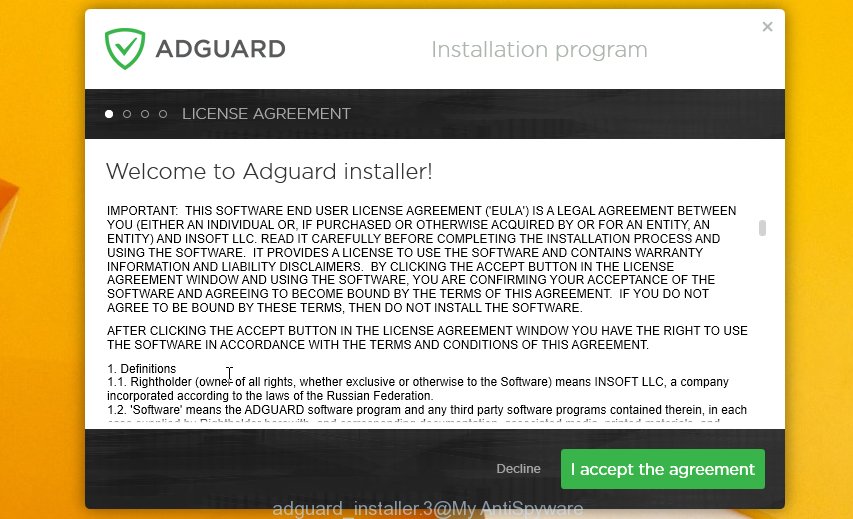
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick instructions as shown on the screen below.

Press “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick instructions which will help you get to know AdGuard better.
Each time, when you launch your system, AdGuard will run automatically and stop unwanted ads, as well as phishing web-sites, other malicious or misleading webpages. For an overview of all the features of the program, or to change its settings you can simply double-click on the AdGuard icon, that can be found on your desktop.




















Hi, stranger!
I hacked your device, because I sent you this message from your
account.
If you have already changed your password, my malware will be
intercepts it every time.
You may not know me, and you are most likely wondering why you
are receiving this email, right?
In fact, I posted a malicious program on adults (pornography) of
some websites, and you know that you visited these websites to
enjoy
(you know what I mean).
While you were watching video clips,
my trojan started working as a RDP (remote desktop) with a
keylogger that gave me access to your screen as well as a webcam.
Immediately after this, my program gathered all your contacts
from messenger, social networks, and also by e-mail.
What I’ve done?
I made a double screen video.
The first part shows the video you watched (you have good taste,
yes … but strange for me and other normal people),
and the second part shows the recording of your webcam.
What should you do?
Well, I think $315 (USD dollars) is a fair price for our little
secret.
You will make a bitcoin payment (if you don’t know, look for “how
to buy bitcoins” on Google).
BTC Address: 1BCGDtVZPqBMZWm5FdFe1RVgCGku17LZgb
(This is CASE sensitive, please copy and paste it)
Remarks:
You have 2 days (48 hours) to pay. (I have a special code, and at
the moment I know that you have read this email).
If I don’t get bitcoins, I will send your video to all your
contacts, including family members, colleagues, etc.
However, if I am paid, I will immediately destroy the video, and
my trojan will be destruct someself.
If you want to get proof, answer “Yes!” and resend this letter to
youself.
And I will definitely send your video to your any 19 contacts.
This is a non-negotiable offer, so please do not waste my
personal and other people’s time by replying to this email.
Update:
New subject: “Your account is being accessed by another person!”
New BTC Address: 1L47wHe7FXWQ6pfPTbnykdX44FxQGstFeS
Your account is being used by another person!
Hello!
I have very bad news for you.
12/10/2018 – on this day I hacked your OS and got full access to your account ***
So, you can change the password, yes… But my malware intercepts it every time.
How I made it:
In the software of the router, through which you went online, was a vulnerability.
I just hacked this router and placed my malicious code on it.
When you went online, my trojan was installed on the OS of your device.
After that, I made a full dump of your disk (I have all your address book, history of viewing sites, all files, phone numbers and addresses of all your contacts).
A month ago, I wanted to lock your device and ask for a not big amount of btc to unlock.
But I looked at the sites that you regularly visit, and I was shocked by what I saw!!!
I’m talk you about sites for adults.
I want to say – you are a BIG pervert. Your fantasy is shifted far away from the normal course!
And I got an idea….
I made a screenshot of the adult sites where you have fun (do you understand what it is about, huh?).
After that, I made a screenshot of your joys (using the camera of your device) and glued them together.
Turned out amazing! You are so spectacular!
I’m know that you would not like to show these screenshots to your friends, relatives or colleagues.
I think $618 is a very, very small amount for my silence.
Besides, I have been spying on you for so long, having spent a lot of time!
Pay ONLY in Bitcoins!
My BTC wallet: 145SmyE7DBEQExsnXZobojbQqr5UdgbCHh
You do not know how to use bitcoins?
Enter a query in any search engine: “how to replenish btc wallet”.
It’s extremely easy
For this payment I give you two days (48 hours).
As soon as this letter is opened, the timer will work.
After payment, my virus and dirty screenshots with your enjoys will be self-destruct automatically.
If I do not receive from you the specified amount, then your device will be locked, and all your contacts will receive a screenshots with your “enjoys”.
I hope you understand your situation.
– Do not try to find and destroy my virus! (All your data, files and screenshots is already uploaded to a remote server)
– Do not try to contact me (this is not feasible, I sent you an email from your account)
– Various security services will not help you; formatting a disk or destroying a device will not help, since your data is already on a remote server.
P.S. You are not my single victim. so, I guarantee you that I will not disturb you again after payment!
This is the word of honor hacker
I also ask you to regularly update your antiviruses in the future. This way you will no longer fall into a similar situation.
Do not hold evil! I just do my job.
Have a nice day!
Hello!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $612 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1DASN5fH1E1PCoxU9qMEF7QDjnXcA2b3Km
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $737 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1GoWy5yMzh3XXBiYxLU9tKCBMgibpznGio
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account: At the time of hacking your account(heathr3@***) had this password: *********** [[this was the correct password. How did they get it?? I have never used any “adult” sites…]]
You can say: this is my, but old password!
Or: I can change my password at any time!
Of course! You will be right,
but the fact is that when you change the password, my malicious code every time saved a new one!
I’ve been watching you for a few months now.
But the fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence from e-mail and messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this, transfer the amount of $761 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1GB22WpNfFPcAYnad1Sd3qWoVJeDbtN72M
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Bye!
Update:
New BTC Address: 16KfNQg7xzVGmyr51jKa92LCWtjYtw4w7D