What is “You have outstanding debt” EMAIL?
You have outstanding debt email is an online sextortion scam. Sextortion is another word for “sexual extortion”. Sexual extortion is a type of “phishing attack”, where scammers try to trick people into paying a ransom. Sextortion scam targets victims via Email/SMS/text messages. Scammers threaten to reveal intimate photos of their victims if the ransom is not paid.
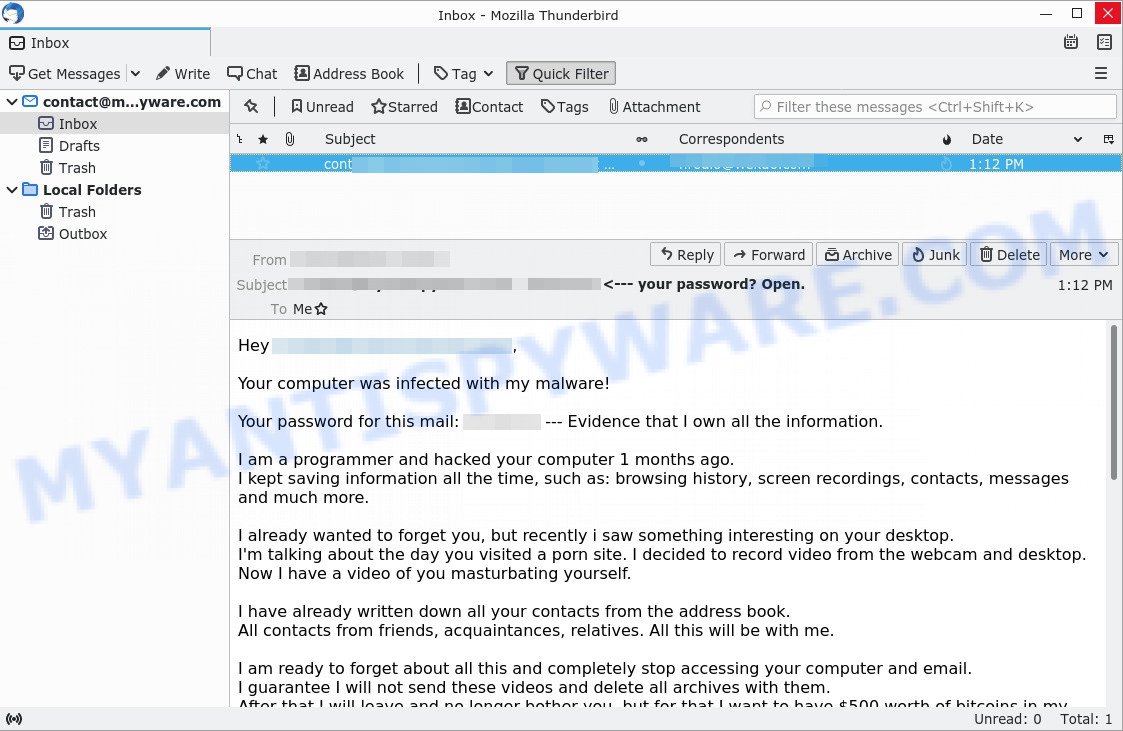
Sextortion scam emails may contain a genuine password from one of the victim’s accounts. Usually passwords are appended to these messages as proof, that is, if the password was actually used by the victim, then what is described in the email is true. Scammers get these real passwords by buying them on darknet.
“You have outstanding debt.” email is a sextortion scam
QUICK LINKS
- What is “You have outstanding debt” EMAIL?
- Should you pay?
- What to do when you receive the scam email?
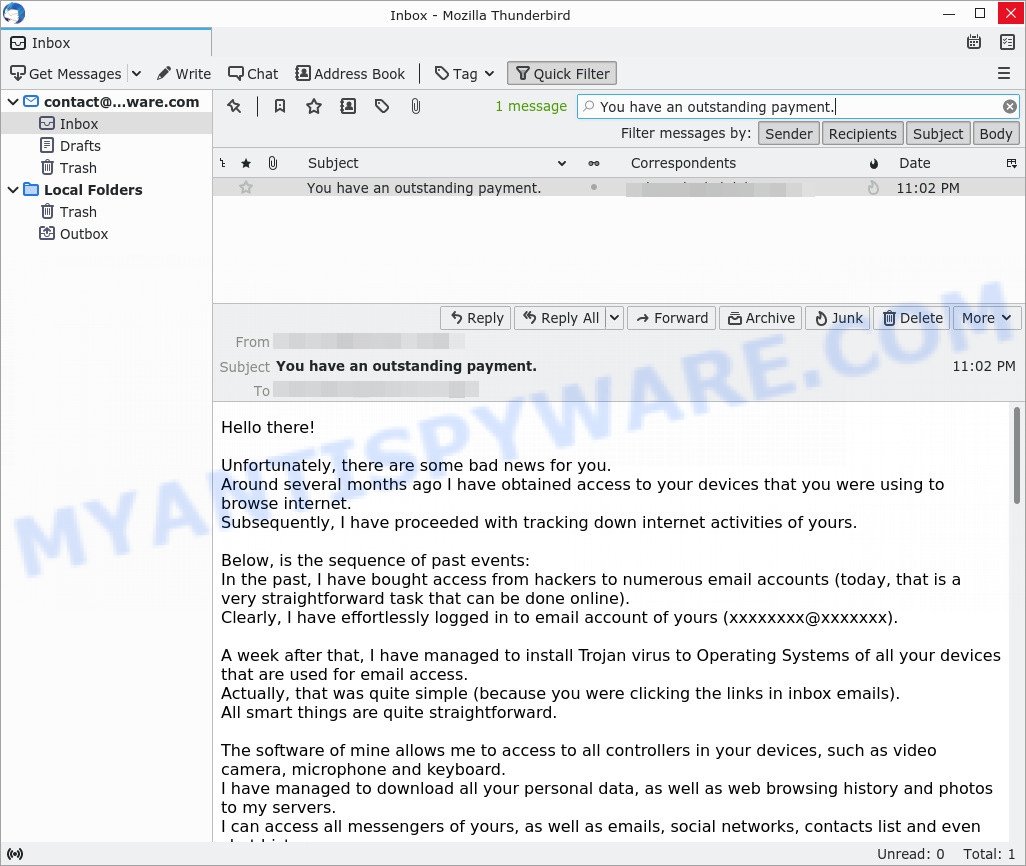
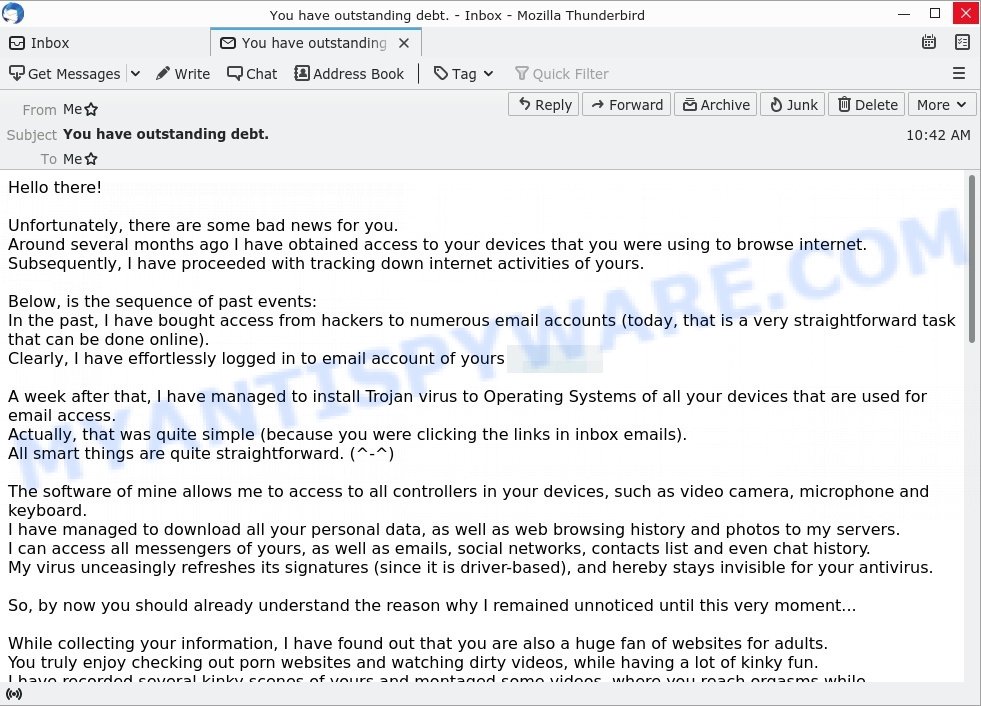
You have outstanding debt Email Scam in detail
Sextortion Scam emails say that someone has been watching the victim, because the victim’s computer has a virus, which is a Trojan that allows the attacker to completely control the computer and even record video from the computer’s camera. The scam emails claim that a video was recorded showing the victim masturbating while browsing porn sites. This video will be sent to the victim’s friends, family and even colleagues unless the victim pays the ransom to the bitcoin address provided in the message.
Text presented in the scam email:
Hello there!
Unfortunately, there are some bad news for you.
Around several months ago I have obtained access to your devices that you were using to browse internet.
Subsequently, I have proceeded with tracking down internet activities of yours.Below, is the sequence of past events:
In the past, I have bought access from hackers to numerous email accounts (today, that is a very straightforward task that can be done online).
Clearly, I have effortlessly logged in to email account of yours (xxxxxxxx).A week after that, I have managed to install Trojan virus to Operating Systems of all your devices that are used for email access.
Actually, that was quite simple (because you were clicking the links in inbox emails).
All smart things are quite straightforward. (^-^)The software of mine allows me to access to all controllers in your devices, such as video camera, microphone and keyboard.
I have managed to download all your personal data, as well as web browsing history and photos to my servers.
I can access all messengers of yours, as well as emails, social networks, contacts list and even chat history.
My virus unceasingly refreshes its signatures (since it is driver-based), and hereby stays invisible for your antivirus.So, by now you should already understand the reason why I remained unnoticed until this very moment…
While collecting your information, I have found out that you are also a huge fan of websites for adults.
You truly enjoy checking out porn websites and watching dirty videos, while having a lot of kinky fun.
I have recorded several kinky scenes of yours and montaged some videos, where you reach orgasms while passionately masturbating.If you still doubt my serious intentions, it only takes couple mouse clicks to share your videos with your friends, relatives and even colleagues.
It is also not a problem for me to allow those vids for access of public as well.
I truly believe, you would not want this to occur, understanding how special are the videos you love watching, (you are clearly aware of that) all that stuff can result in a real disaster for you.Let’s resolve it like this:
All you need is $1450 USD transfer to my account (bitcoin equivalent based on exchange rate during your transfer), and after the transaction is successful, I will proceed to delete all that kinky stuff without delay.
Afterwards, we can pretend that we have never met before. In addition, I assure you that all the harmful software will be deleted from all your devices. Be sure, I keep my promises.That is quite a fair deal with a low price, bearing in mind that I have spent a lot of effort to go through your profile and traffic for a long period.
If you are unaware how to buy and send bitcoins – it can be easily fixed by searching all related information online.Below is bitcoin wallet of mine: 17kmbhxxMsrFhmQNim1jbjD6AeBUQ2SbYp
You are given not more than 48 hours after you have opened this email (2 days to be precise).
Below is the list of actions that you should not attempt doing:
> Do not attempt to reply my email (the email in your inbox was created by me together with return address).
> Do not attempt to call police or any other security services. Moreover, don’t even think to share this with friends of yours. Once I find that out (make no doubt about it, I can do that effortlessly, bearing in mind that I have full control over all your systems) – the video of yours will become available to public immediately.
> Do not attempt to search for me – there is completely no point in that. All cryptocurrency transactions remain anonymous at all times.
> Do not attempt reinstalling the OS on devices of yours or get rid of them. It is meaningless too, because all your videos are already available at remote servers.Below is the list of things you don’t need to be concerned about:
> That I will not receive the money you transferred.
– Don’t you worry, I can still track it, after the transaction is successfully completed, because I still monitor all your activities (trojan virus of mine includes a remote-control option, just like TeamViewer).
> That I still will make your videos available to public after your money transfer is complete.
– Believe me, it is meaningless for me to keep on making your life complicated. If I indeed wanted to make it happen, it would happen long time ago!Everything will be carried out based on fairness!
Before I forget…moving forward try not to get involved in this kind of situations anymore!
An advice from me – regularly change all the passwords to your accounts.
Sextortion scam emails attempt to get victims to pay someone who claims to have secretly recorded a video or compromising information. It should be emphasized that any statements, claims and threats contained in the sextortion emails are false and should be ignored.
To summarize, the “You have outstanding debt” email is just a sextortion scam. If you receive a sextortion scam email that threatens you in any way, and asks you to make a Bitcoin payment, don’t take the bait.
Threat Summary
| Name | You have outstanding debt Email Scam |
| Type | Sextortion, Phishing, Bitcoin Blackmail Scam |
| Ransom amount | $1450 |
| Bitcoin Address | 1Q3bj3y63wqXPGcsXhiC9N1YbYhF5euBBY, 17kmbhxxMsrFhmQNim1jbjD6AeBUQ2SbYp |
| Distribution method | spam email campaigns |
| Removal | If you get a scam email that is similar the example above, our computer security experts recommend follow some easy steps below |
Should you pay?
The best advice is: Don’t pay the ransom! If you receive a sextortion scam email, just ignore the scammers’ empty threats. The best way to deal with the scam email is simply to move it to trash!
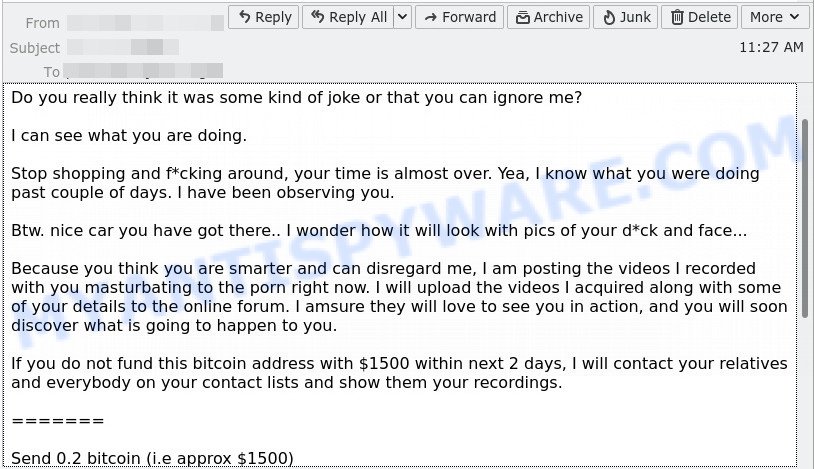
Examples of such scams
There are many sextortion scams circulating via email. Scammers often change the content of emails in order to deceive victims and bypass the security system. Payment from your account, , Waiting for the payment are other examples of sextortion scam emails. Such emails are also often used to distribute ransomware, trojans, worms and other malware.
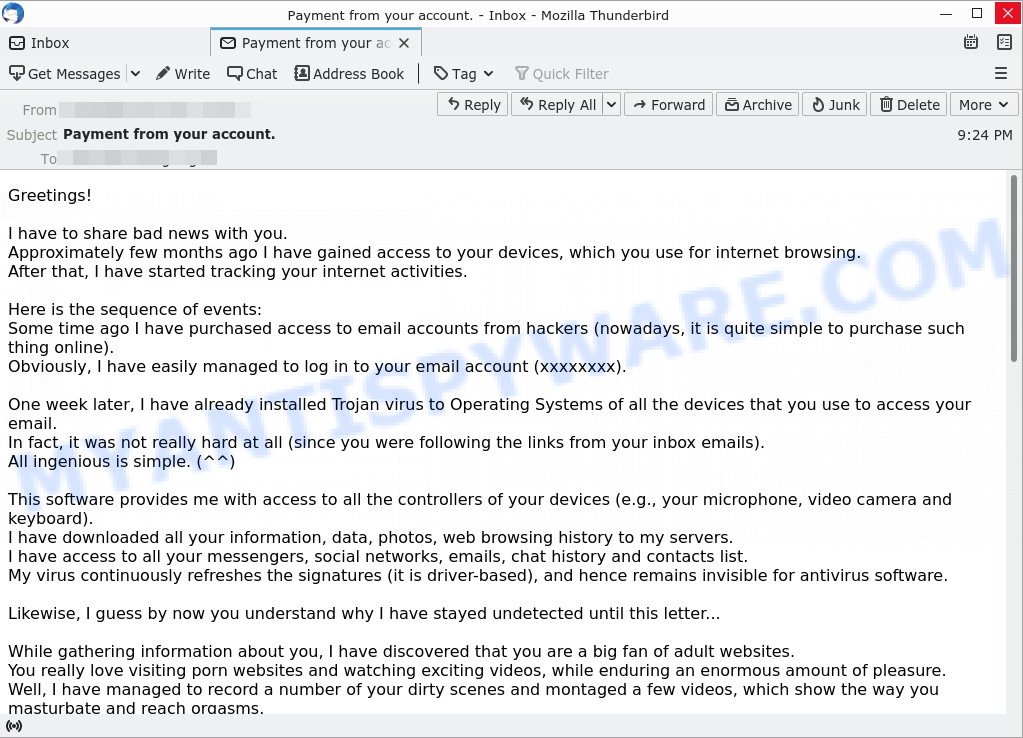
- “Payment from your account.” email is a ‘sextortion’ scam
- FINAL WARNING email is a sextortion scam
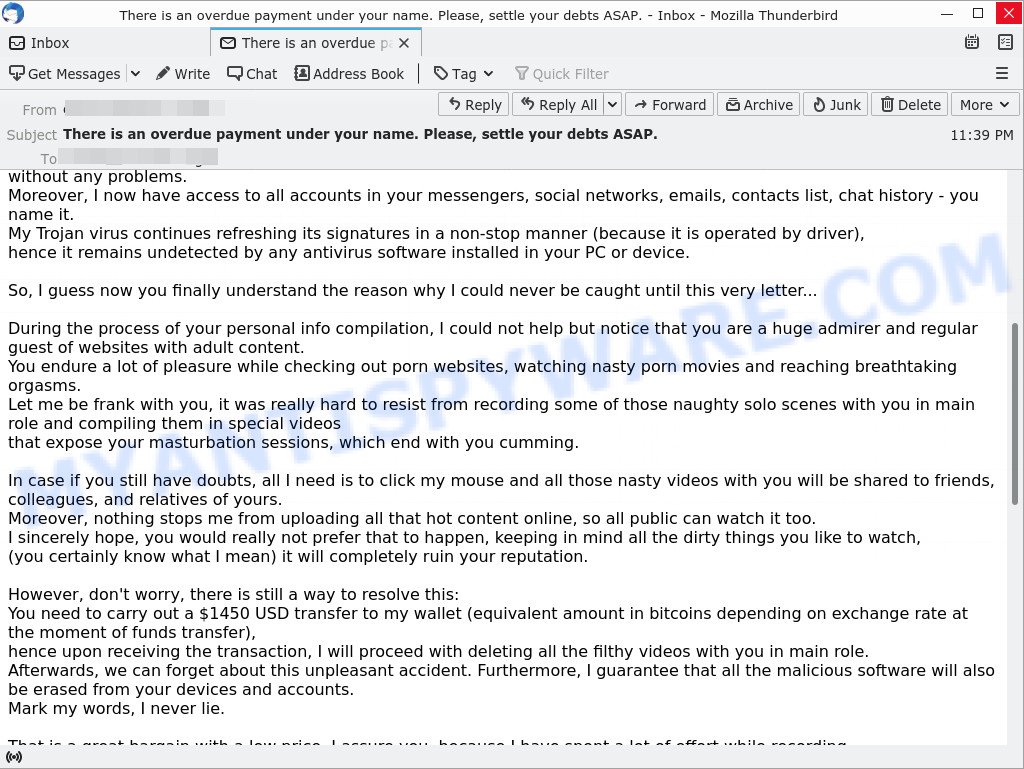
- “There is an overdue payment under your name. Please, settle your debts ASAP.” email is a SCAM
- The “You have an outstanding payment.” email is a SCAM
- Your computer was infected with my malware Email Message is a SCAM
What to do when you receive the sextortion scam email
We advice to someone who gets this fraudulence message:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email spam to the FTC at https://www.ftc.gov/.
- Mark the scam email as SPAM/JUNK and delete it.
- Scan your computer for malware.
- Install an anti-phishing software.
How to scan your computer for malware
If you suspect that your computer is infected with malware, you accidentally clicked on a link in the scam email, or just want to scan your computer, then use one of the best free malware removal tools. MalwareBytes is an antivirus that can be used to perform a virus scan, detect and remove almost all the forms of malicious programs including ransomware, trojans, worms, adware, browser hijackers, potentially unwanted software and spyware. MalwareBytes has real-time protection that can defeat most malicious software and ransomware. Despite so many features, it does not reduce the performance of your computer. You can use MalwareBytes with any other antivirus without any conflicts.
First, please go to the link below, then click the ‘Download’ button in order to download the latest version of MalwareBytes.
327278 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
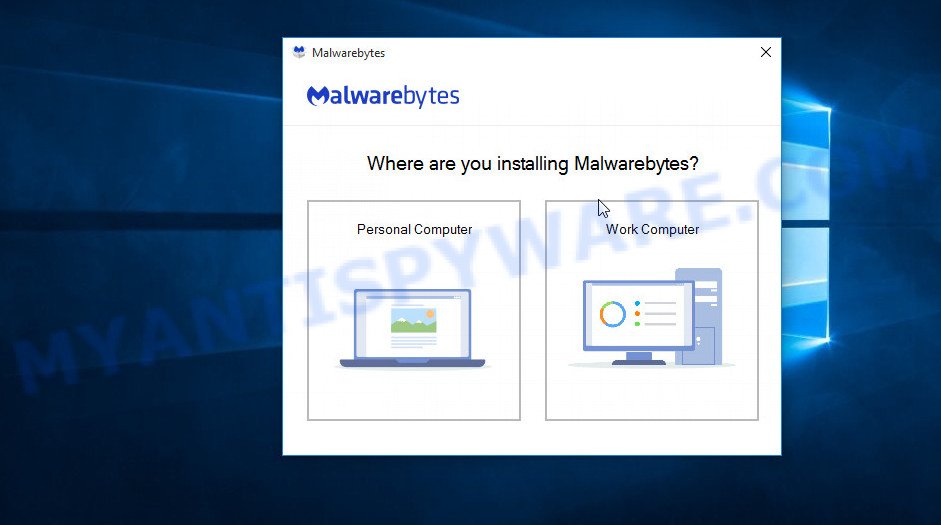
When the downloading process is done, close all windows on your computer. Further, launch the file named MBSetup. If the “User Account Control” dialog box pops up like below, click the “Yes” button.
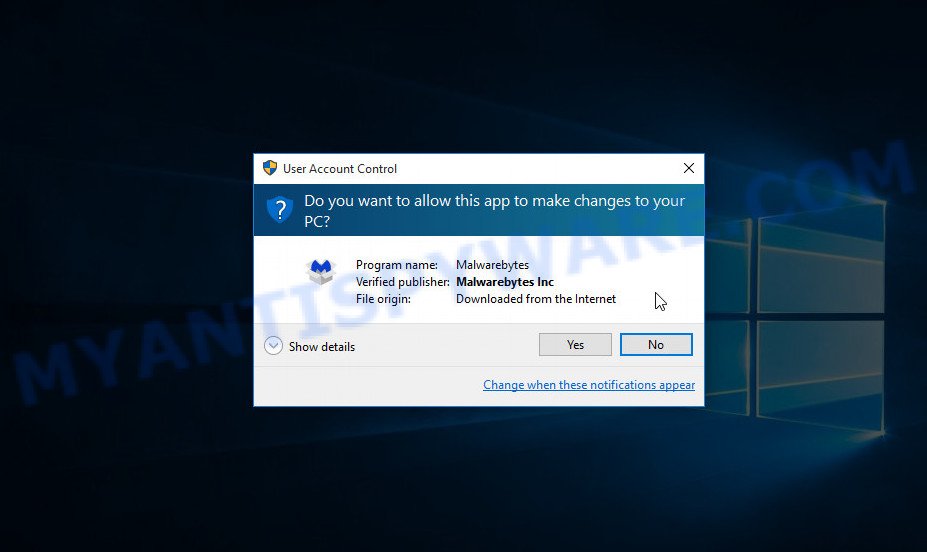
It will show the Setup wizard which will assist you install MalwareBytes on the computer. Follow the prompts and do not make any changes to default settings.
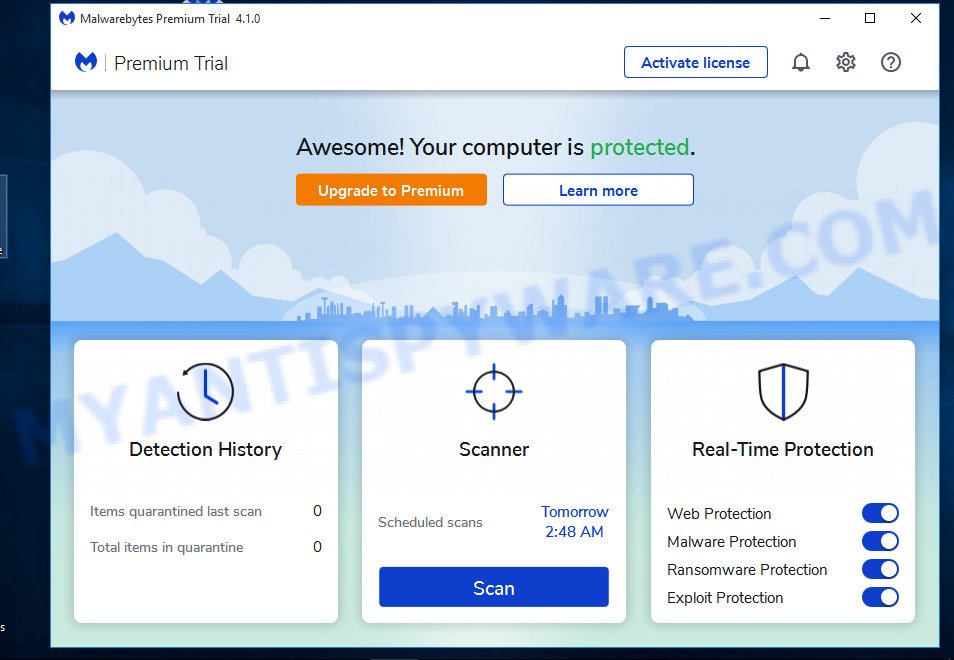
After the setup is complete successfully, press “Get Started” button. Then MalwareBytes AntiMalware will automatically run and you can see its main window such as the one below.
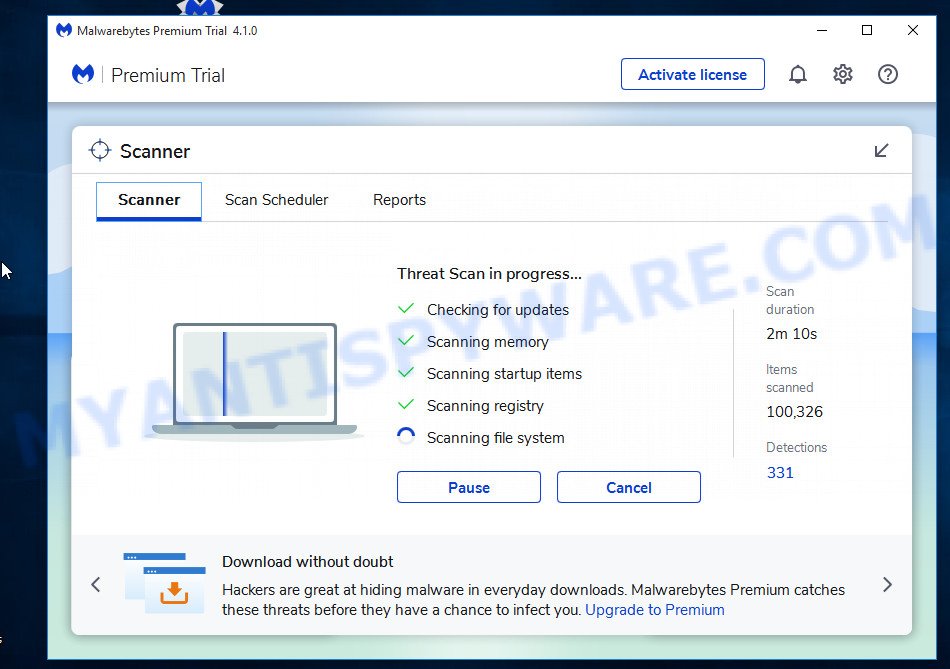
Next, click the “Scan” button for scanning your computer for malicious software and other security threats. A system scan can take anywhere from 5 to 30 minutes, depending on your computer. While MalwareBytes is scanning, you can see how many objects it has identified as threat.
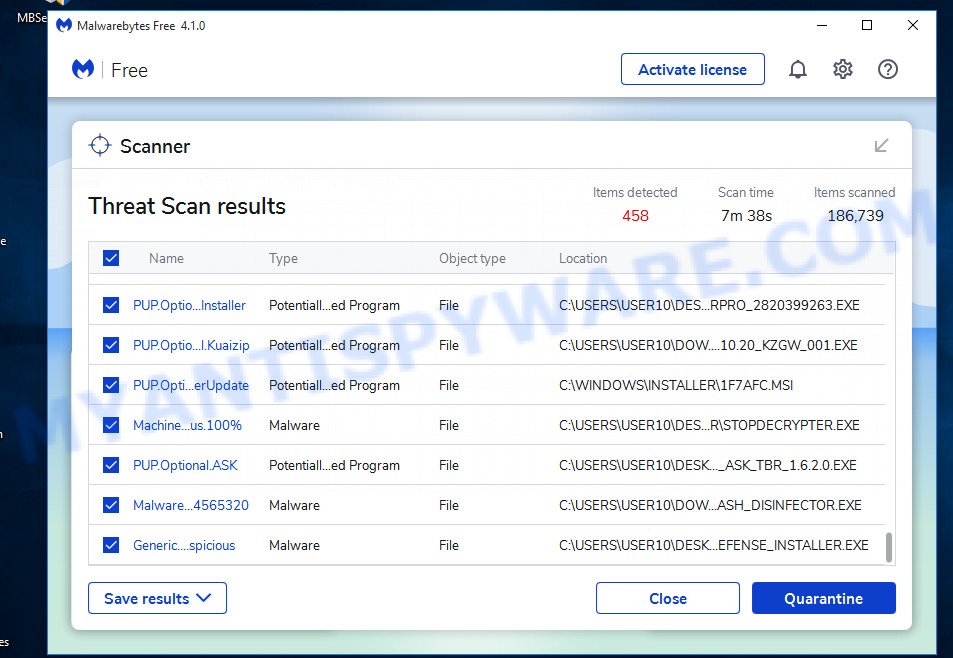
When the scanning is done, the results are displayed in the scan report. In order to remove all threats, simply press “Quarantine” button.
We suggest you look at the following video, which completely explains the process of using MalwareBytes to remove malicious software.
If you are having issues with malware removal, then check out Kaspersky virus removal tool. It can easily remove trojans, spyware, browser hijackers, adware, worms and ransomware with all their components such as files, folders and registry entries. Visit the page linked below to download the latest version of Kaspersky virus removal tool for Windows.
129296 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
How to protect yourself from phishing, malicious and misleading websites
If you want to protect yourself from phishing sites, install an ad blocking program like AdGuard. It can block malicious and misleading websites, stop unwanted ads and pop-ups while using Internet Explorer, Google Chrome, Firefox and Edge. So, if you like to surf the Internet and want to protect your computer from phishing scams, then AdGuard is your best choice.
Installing AdGuard is very easy. First you’ll need to download AdGuard by clicking on the link below.
26903 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as displayed below.
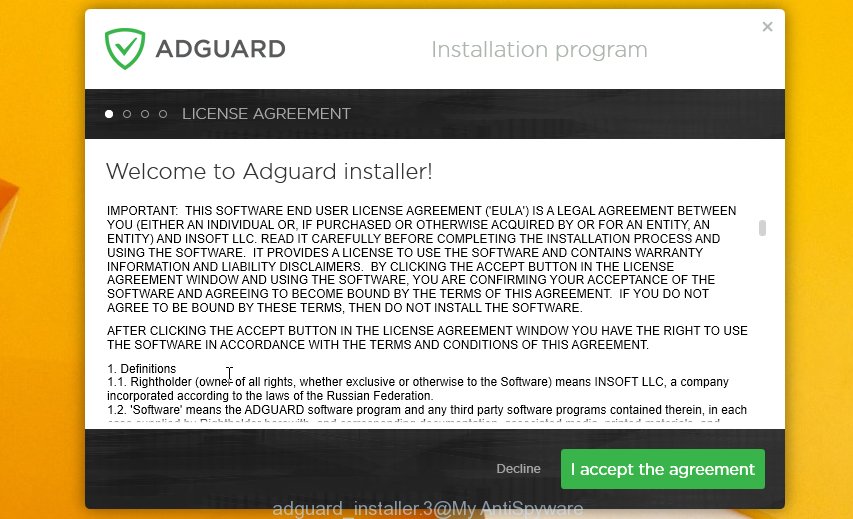
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guide as displayed on the screen below.

Click “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick guidance which will assist you get to know AdGuard better.
Each time, when you start your system, AdGuard will start automatically and stop unwanted advertisements, block phishing, as well as other harmful or misleading websites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
If you receive a scam email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. This helps us to warn users about current scams, monitor trends and disrupt scams where possible.