What is There is an overdue payment under your name EMAIL?
There is an overdue payment under your name. Please, settle your debts ASAP. is a ‘sextortion’ scam. Sextortion is a scam that targets victims via Email/SMS/text messages. This scam tries to guilt victims into paying off someone claiming to have secretly recorded video or compromising information. Scammers use a database of stolen email credentials to send out scam messages to millions of people around the World. The messages are sent to email addresses exposed in previous known data breaches in which the user email address and password has been compromised.
In some cases, sextortion scam emails may contain real passwords that the victim has used in the past (or even uses). Usually passwords are appended to these messages as proof, that is, if the password was actually used by the victim, then what is described in the email is true. Scammers get these real passwords by buying them on darknet.
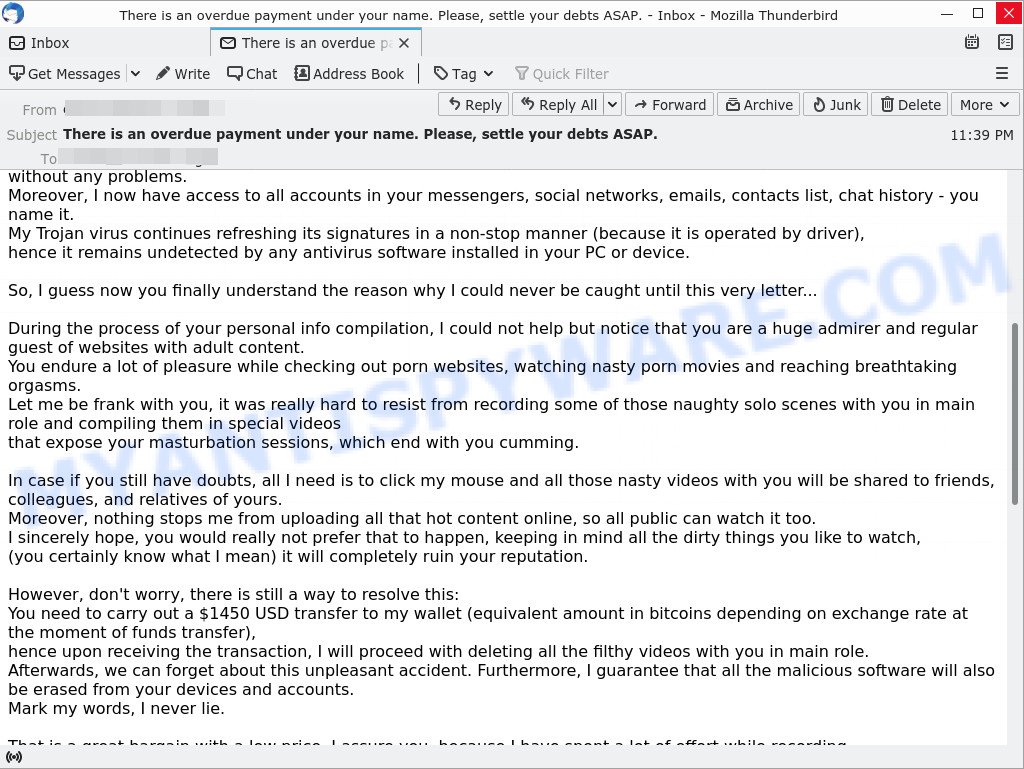
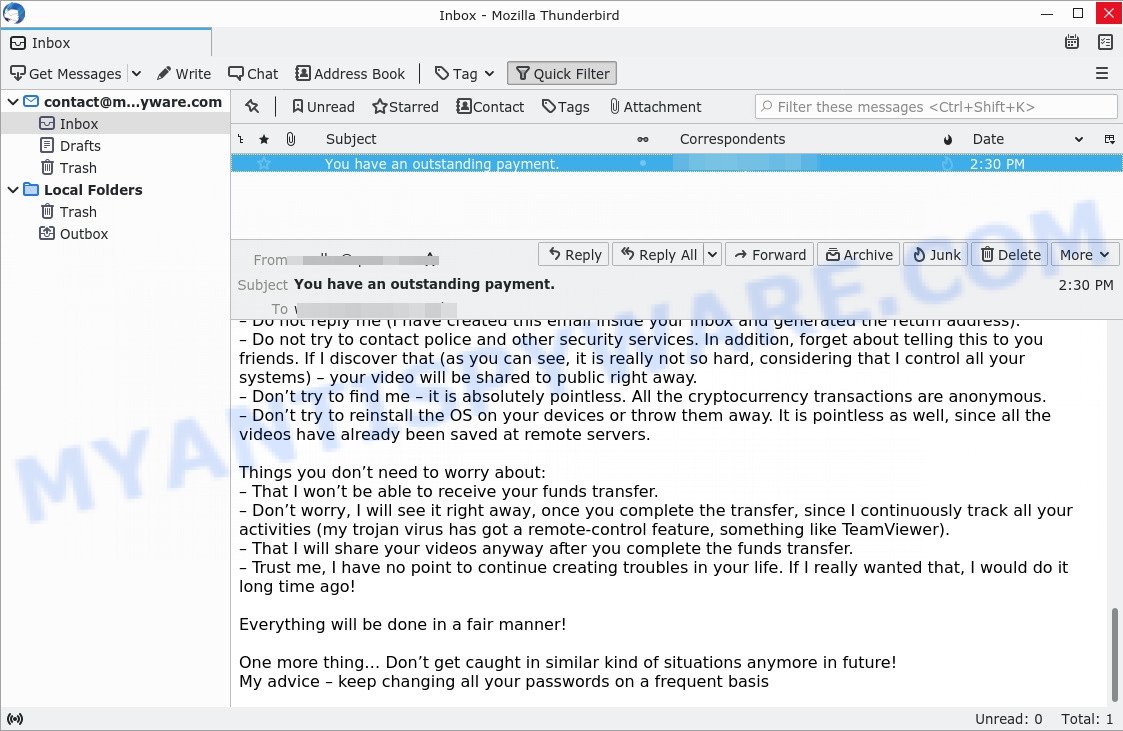
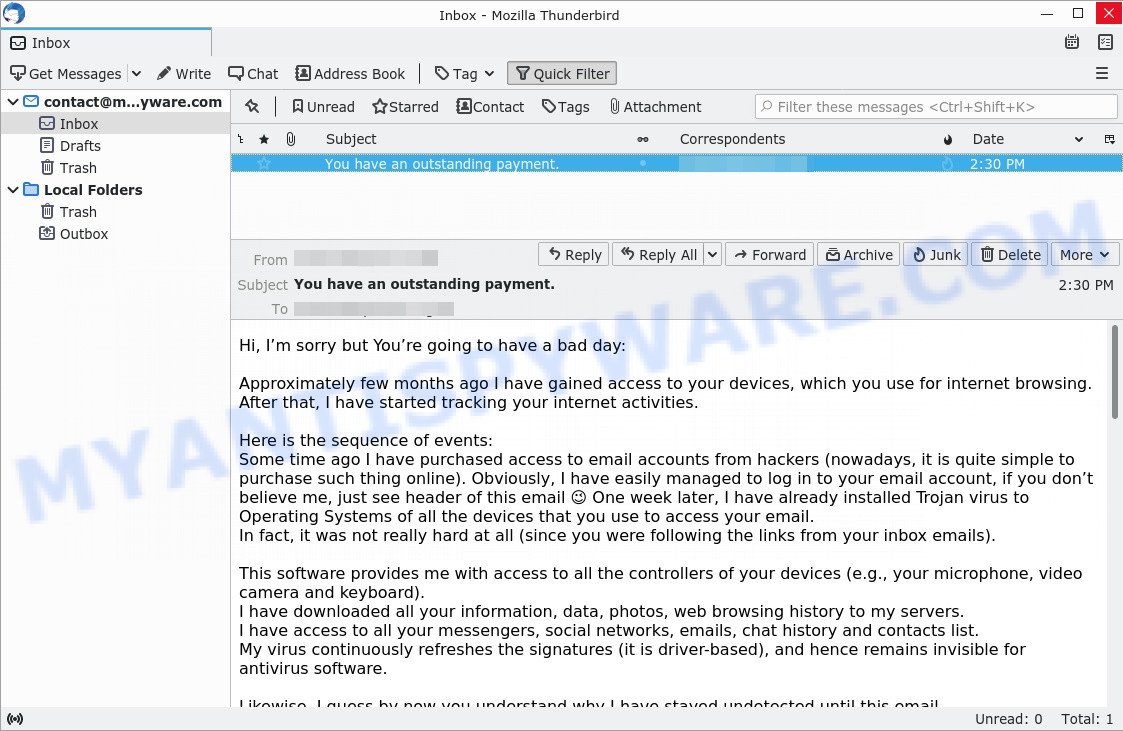
An example of the “There is an overdue payment under your name. Please, settle your debts ASAP.” EMAIL SCAM:
QUICK LINKS
- What is There is an overdue payment under your name EMAIL?
- Should you pay?
- What to do when you receive the email scam?
The scam in detail
The “There is an overdue payment under your name” scam is not the only one of its kind, there are many similar ones. They all have similar features: spelling and grammatical errors, statement that the victim’s computer and webcam were hacked, threats that the attackers recorded a compromising video, and a ransom demand.
Depending on the scam, victims are given 24 to 48 hours to pay a ransom in Bitcoin. The sextortion scams also contain claims that the victim’s contact information was stolen, allegedly the hacker copied the victim’s contact list and social media credentials. And finally, Sextortion scams contain threats, the victims must pay a ransom, or compromising materials will be sent to their contacts.
To summarize, the “There is an overdue payment under your name. Please, settle your debts ASAP.” message is just a sextortion scam. All claims and threats made in this email message are false. Therefore, recipients are not in danger, this email and similar emails can be safely ignored.
Should you pay?
The best advice is: Don’t pay the ransom! If you receive the sextortion email scam, just ignore the scammers’ empty threats. The best way to deal with the scam email is simply to move it to trash!
Threat Summary
| Name | There is an overdue payment under your name. Please, settle your debts ASAP. SCAM |
| Type | Sextortion, Phishing, Bitcoin Blackmail Scam |
| Ransom amount | $1450, $1250, $1550, $1590, $1190, $1290 (USD) |
| Bitcoin Address | 1ReCKyhNPdHkbNCjf3EyRgr6XZX78rURd, 1JSrCb8fwX15475Jztt3yA7JWHXzzxTX9h, 1LV8rSHsXYQ9JWUM4LRAGywH8RA6DXH6A7, 17YJKh4TNBDrgFKfbjbQHCGEmZH8uvFoVp, 1EKdS2BjXd8BzYtsu8U9nQmpcygCjGCjZx, 1Mjt2xobFExdZBGfjTVDcgzJWQxRxoHBdA |
| Distribution method | spam email campaigns |
| Removal | If you gets an email like There is an overdue payment under your name, our computer security experts recommend follow some easy steps below |
Examples of scam emails
There are many variants of the sextortion scam, scammers constantly change the text of emails so that spam filters do not work. In addition, in some cases, criminals can translate the text of sextortion messages into other languages, thus targeting a specific group of Internet users. I am sorry to inform you that your device was compromised, Unfortunately, there are some bad news for you, Have you recently noticed that I have e-mailed you from your account are other examples of sextortion scam emails.
- Bottom of the “Hi, I’m sorry but You’re going to have a bad day” scam email
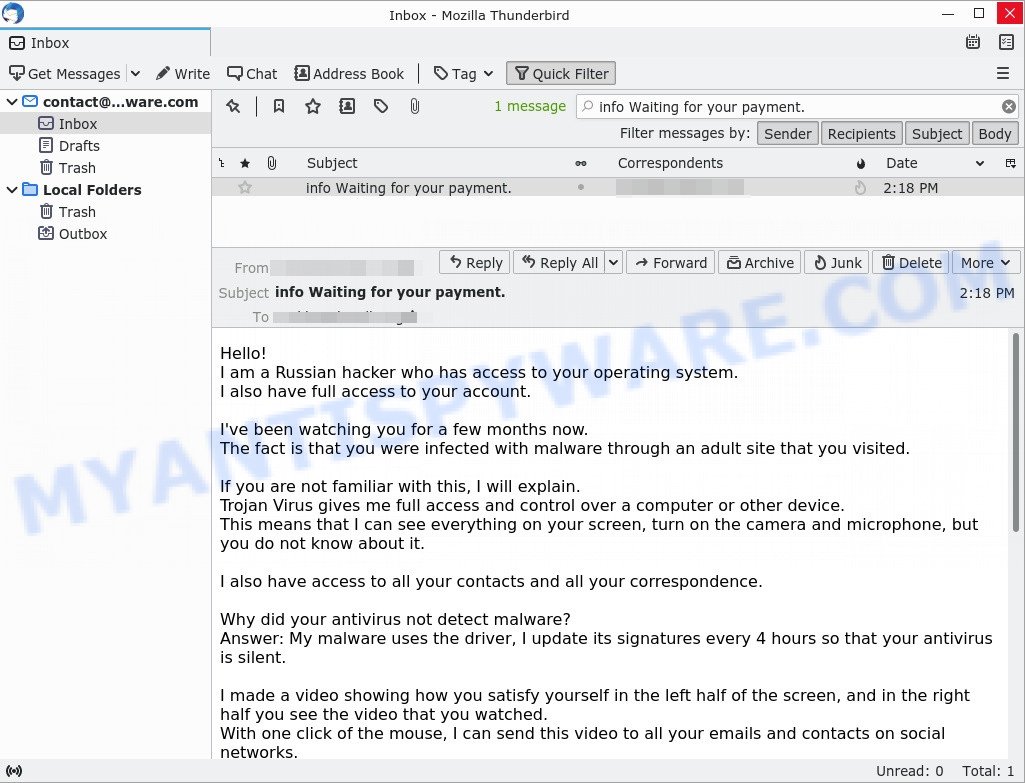
- “I am a Russian hacker who has access to your operating system” email message is a sextortion SCAM
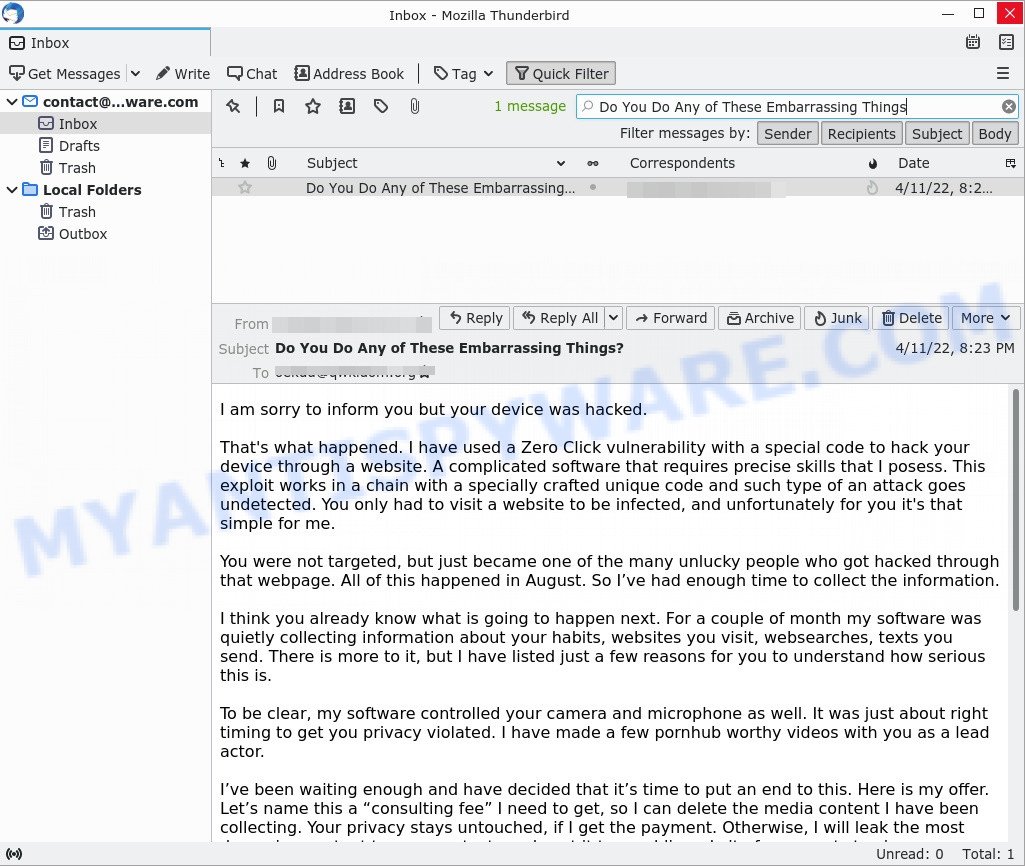
- “Do You Do Any of These Embarrassing Things” email message is a sextortion SCAM
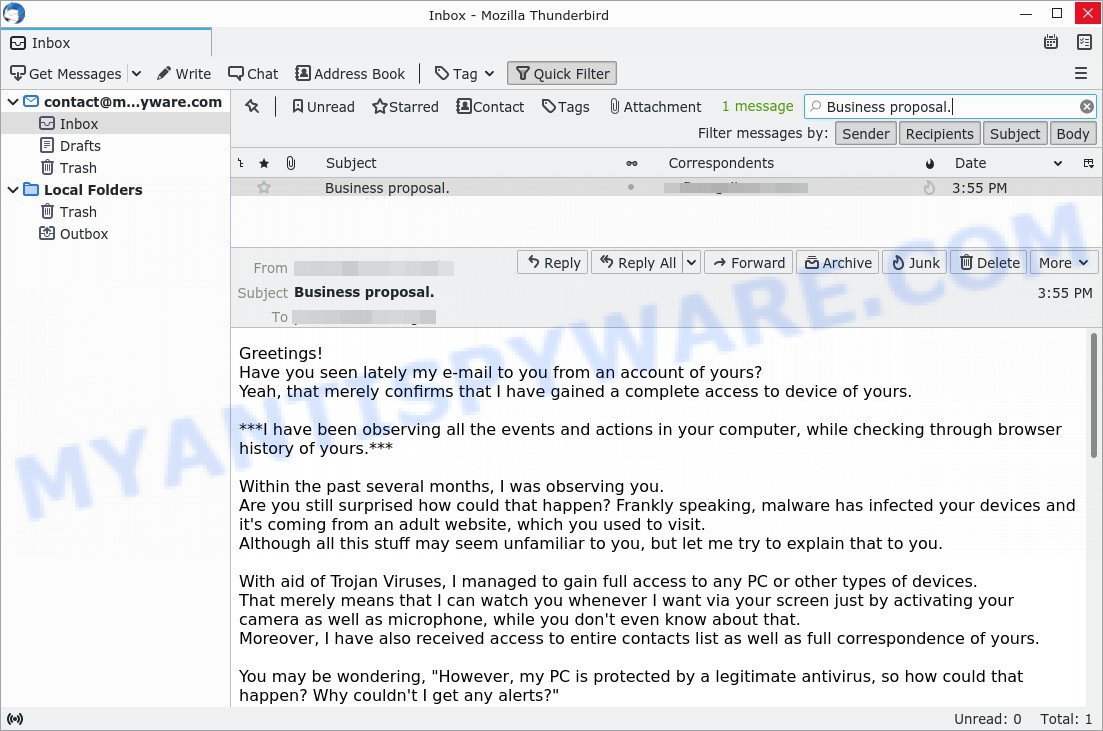
- The “Have you seen lately my e-mail to you from an account of yours” message is a sextortion SCAM
- The “Hi, I’m sorry but You’re going to have a bad day” email message is a new SCAM
Scam emails are used by cybercriminals to fraudulently ask for personal detail or money, distribute ransomware, trojans, worms and other malware. Some scams threaten its users using blackmail or any form of threatening message.
What to do when you receive the There is an overdue payment under your name SCAM
We advice to someone who gets this fraudulence message:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email spam to the FTC at https://www.ftc.gov/
- Mark the “the There is an overdue payment under your name” email as SPAM/JUNK and delete it
- Scan your computer for malware.
- Install an anti-phishing software.
How to scan your computer for malware
If you suspect that your computer is infected with malware, you accidentally clicked on a link in the scam email, or just want to scan your computer, then use one of the best free malware removal tools. MalwareBytes is an antivirus that can be used to perform a virus scan, detect and remove almost all the forms of malicious programs including ransomware, trojans, worms, adware, browser hijackers, potentially unwanted software and spyware. MalwareBytes has real-time protection that can defeat most malicious software and ransomware. Despite so many features, it does not reduce the performance of your computer. You can use MalwareBytes with any other antivirus without any conflicts.
First, please go to the link below, then click the ‘Download’ button in order to download the latest version of MalwareBytes.
327309 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
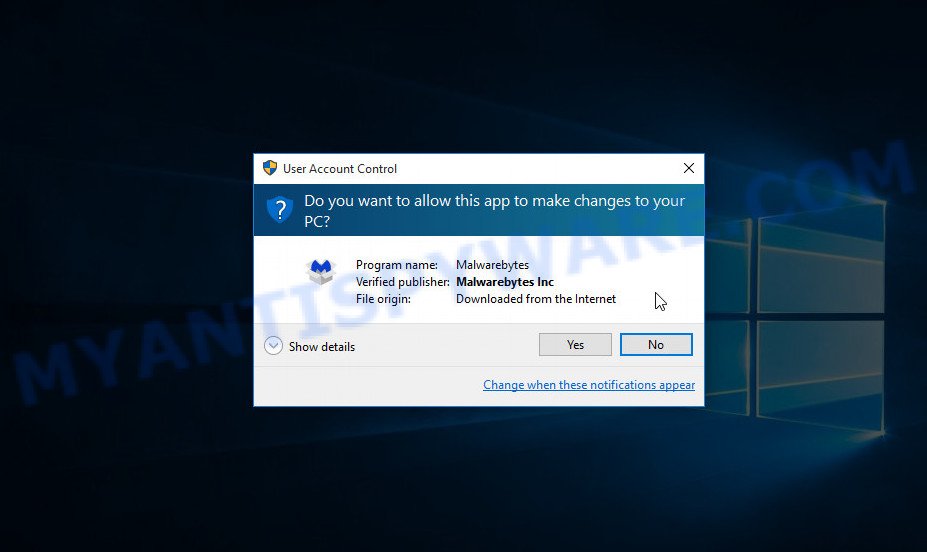
When the downloading process is done, close all windows on your computer. Further, launch the file named MBSetup. If the “User Account Control” dialog box pops up like below, click the “Yes” button.
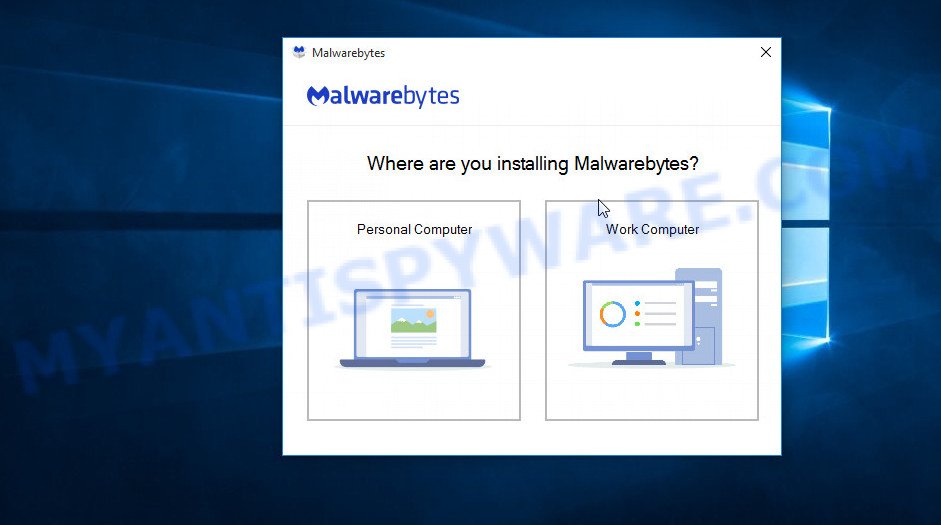
It will show the Setup wizard which will assist you install MalwareBytes on the computer. Follow the prompts and do not make any changes to default settings.
After the setup is complete successfully, press “Get Started” button. Then MalwareBytes AntiMalware will automatically run and you can see its main window such as the one below.
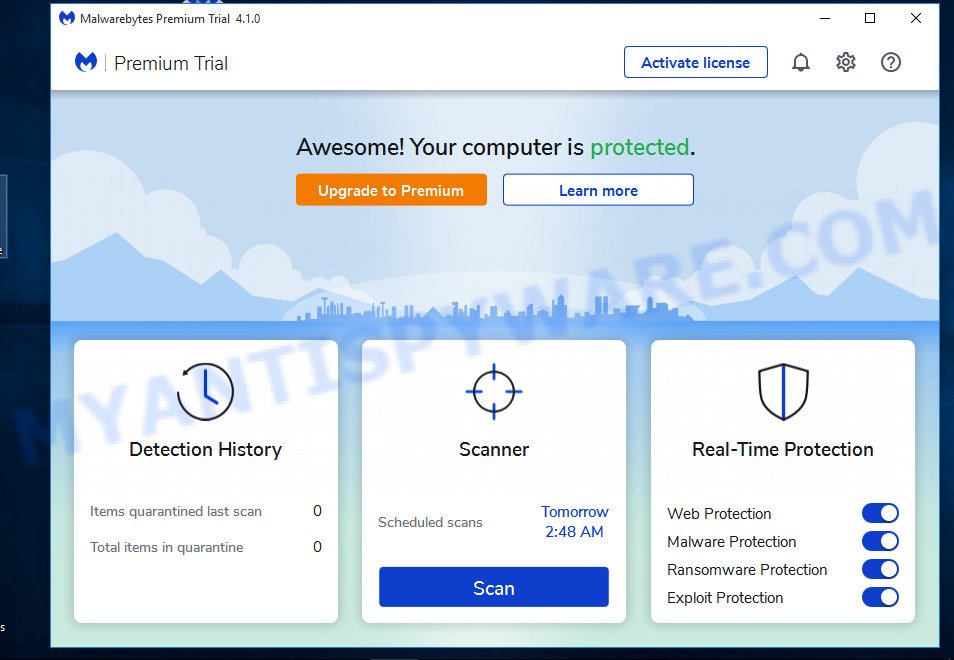
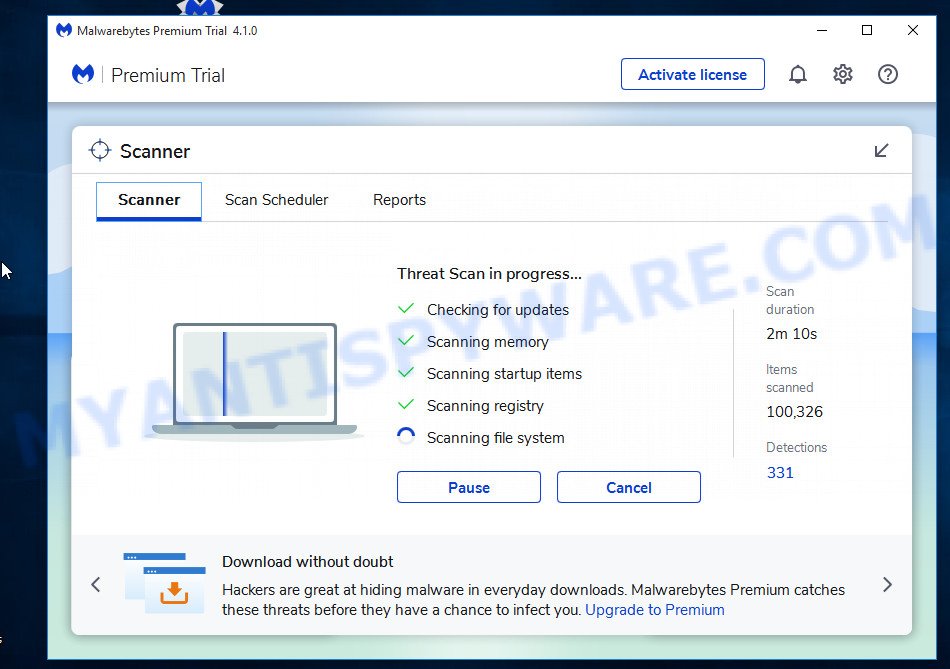
Next, click the “Scan” button for scanning your computer for malicious software and other security threats. A system scan can take anywhere from 5 to 30 minutes, depending on your computer. While MalwareBytes is scanning, you can see how many objects it has identified as threat.
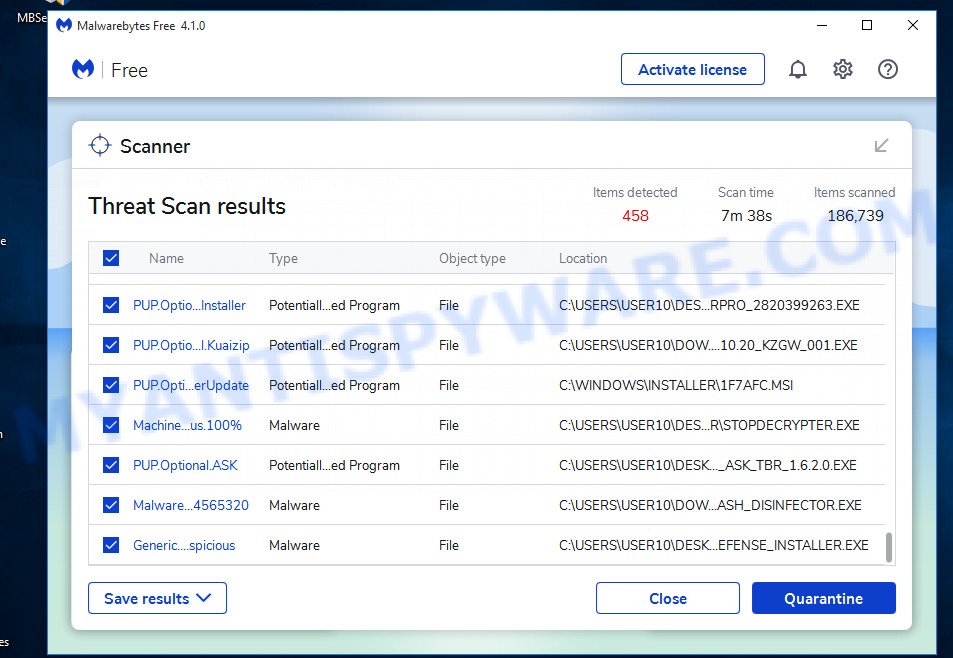
When the scanning is done, the results are displayed in the scan report. In order to remove all threats, simply press “Quarantine” button.
We suggest you look at the following video, which completely explains the process of using MalwareBytes to remove malicious software.
If you are having issues with malware removal, then check out Kaspersky virus removal tool. It can easily remove trojans, spyware, browser hijackers, adware, worms and ransomware with all their components such as files, folders and registry entries. Visit the page linked below to download the latest version of Kaspersky virus removal tool for Windows.
129309 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
How to protect yourself from phishing, malicious and misleading websites
If you want to protect yourself from phishing sites, install an ad blocking program like AdGuard. It can block malicious and misleading websites, stop unwanted ads and pop-ups while using Internet Explorer, Google Chrome, Firefox and Edge. So, if you like to surf the Internet and want to protect your computer from phishing scams, then AdGuard is your best choice.
Installing AdGuard is very easy. First you’ll need to download AdGuard by clicking on the link below.
26910 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as displayed below.
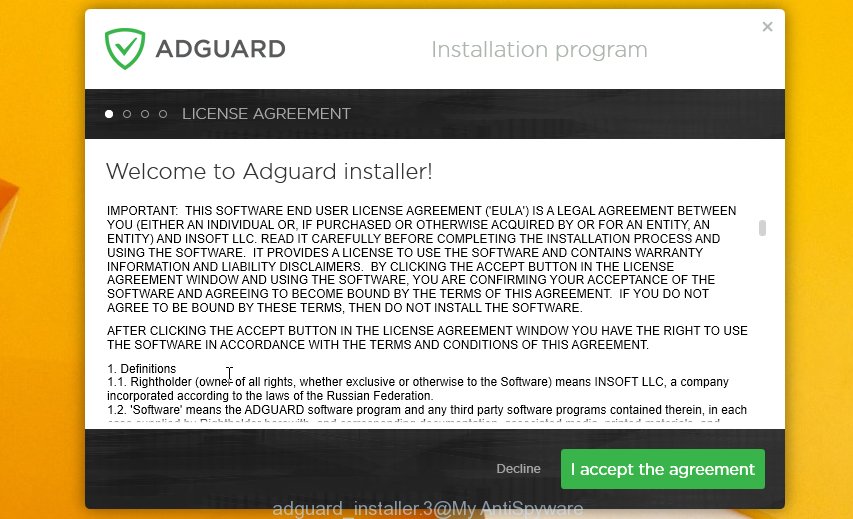
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guide as displayed on the screen below.

Click “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick guidance which will assist you get to know AdGuard better.
Each time, when you start your system, AdGuard will start automatically and stop unwanted advertisements, block phishing, as well as other harmful or misleading websites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
If you receive a scam email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. This helps us to warn users about current scams, monitor trends and disrupt scams where possible.




















Please, settle your debts ASAP
Hi!
Sadly, there are some bad news that you are about to hear.
About few months ago I have gained a full access to all devices used by you for internet browsing.
Shortly after, I started recording all internet activities done by you.
Below is the sequence of events of how that happened:
Earlier I purchased from hackers a unique access to diversified email accounts (at the moment, it is really easy to do using internet).
As you can see, I managed to log in to your email account without breaking a sweat: xxxxxxxxxxxx
Within one week afterwards, I installed a Trojan virus in your Operating Systems available on all devices that you utilize for logging in your email.
To be frank, it was somewhat a very easy task (since you were kind enough to open some of links provided in your inbox emails).
With help of that useful software, I am now able to gain access to all the controllers located in your devices (e.g., video camera, keyboard, microphone and others).
As result, managed to download all your photos, personal data, history of web browsing and other info to my servers without any problems.
Moreover, I now have access to all accounts in your messengers, social networks, emails, contacts list, chat history – you name it.
My Trojan virus continues refreshing its signatures in a non-stop manner (because it is operated by driver), hence it remains undetected by any antivirus software installed in your PC or device.
So, I guess now you finally understand the reason why I could never be caught until this very letter…
During the process of your personal info compilation, I could not help but notice that you are a huge admirer and regular guest of websites with adult content.
You endure a lot of pleasure while checking out porn websites, watching nasty porn movies and reaching breathtaking orgasms.
Let me be frank with you, it was really hard to resist from recording some of those naughty solo scenes with you in main role and compiling them in special videos that expose your masturbation sessions, which end with you cumming.
In case if you still have doubts, all I need is to click my mouse and all those nasty videos with you will be shared to friends, colleagues, and relatives of yours.
Moreover, nothing stops me from uploading all that hot content online, so all public can watch it too.
I sincerely hope, you would really not prefer that to happen, keeping in mind all the dirty things you like to watch, (you certainly know what I mean) it will completely ruin your reputation.
However, don’t worry, there is still a way to resolve this:
You need to carry out a $799 USD transfer to my wallet (equivalent amount in bitcoins depending on exchange rate at the moment of funds transfer), hence upon receiving the transaction, I will proceed with deleting all the filthy videos with you in main role.
Afterwards, we can forget about this unpleasant accident.
Furthermore, I guarantee that all the malicious software will also be erased from your devices and accounts. Mark my words, I never lie.
That is a great bargain with a low price, I assure you, because I have spent a lot of effort while recording and tracking down all your activities and dirty deeds during a long period of time.
In case if you have no idea how to buy and transfer bitcoins – feel free to check the related info on the internet.
Here is my bitcoin wallet for your reference: 1Gi5sqSA6NKfkaPdMu4szv1bzt3XxCyryU
Attention please! I can specified my Bitcoin wallet with spaces, please make sure that you key-in my bitcoin address without spaces to be sure that your coins successfully reach my wallet!
From now on, you have only 50 hours and countdown has started once you opened this very email (in other words, more than two days).
The following list contains things you should definitely abstain from doing or even attempting:
~>> Abstain from trying to reply this email (since the email is generated inside your inbox alongside with return address).
~>> Abstain from trying to call or report to police or any other security services.
In addition, it’s a bad idea if you want to share it with your friends, hoping they would help.
If I happen to find out (knowing my awesome skills, it can be done effortlessly, because I have all your devices and accounts under my control and unceasing observation) – kinky videos of yours will be share to public the same day.
~>> Abstain from trying to look for me – that would not lead anywhere either. Cryptocurrency transactions are absolutely anonymous and cannot be tracked.
~>> Abstain from reinstalling your OS on devices or throwing them away.
That would not solve the problem as well, since all your personal videos are already uploaded and stored at remote servers.
Things you may be confused about:
~>> That your funds transfer won’t be delivered to me.
Chill, I can track down any transactions right away, so upon funds transfer I will receive a notification as well, since I still control your devices (my trojan virus has ability of controlling all processes remotely, just like TeamViewer).
~>> That I am going to share your dirty videos after receiving money transfer from you.
Here you need to trust me, because there is absolutely no point to still bother you after receiving money.
Moreover, if I really wanted all those videos would be available to public long time ago!
I believe we can still handle this situation on fair terms!
Here is my last advice to you… in future you better ensure you stay away from this kind of situations!
My advice – don’t forget to regularly update your passwords to feel completely secure.