What is Your computer was infected with my malware EMAIL?
Your computer was infected with my malware is a new ‘sextortion’ scam. Sextortion is a scam that targets victims via Email/SMS/text messages. This scam tries to guilt victims into paying off someone claiming to have secretly recorded video or compromising information. Scammers use a database of stolen email credentials to send out scam messages to millions of people around the World. The messages are sent to email addresses exposed in previous known data breaches in which the user email address and password has been compromised.
In some cases, sextortion scam messages may contain real passwords that the victim has used in the past (or even uses). Usually passwords are appended to these messages as proof, that is, if the password was actually used by the victim, then what is described in the email is true. Scammers get these real passwords by buying them on darknet.
Your computer was infected with my malware Email Message is a SCAM
QUICK LINKS
- What is Your computer was infected with my malware EMAIL?
- Should you pay?
- What to do when you receive the email scam?
The “Your computer was infected with my malware” scam is not the only one of its kind, there are many similar ones. All of them are similar in the following: spelling and grammatical errors, statements about the victim’s device being infected or hacked, use of a hijacked camera and microphone to record video that compromises the victim, a ransom demand.
Depending on the scam variant, victims are given 24 to 48 hours to pay a ransom in Bitcoin. The sextortion scams also contain claims that the victim’s contact information was stolen, allegedly the hacker copied the victim’s contact list and social media credentials. And finally, all variants of this scam contain threats, the victims must pay a ransom, otherwise compromising materials will be sent to their contacts.
To summarize, the “Your computer was infected with my malware” message is just a sextortion scam. All claims and threats made in this email message are false. Therefore, recipients are not in danger, this email and similar emails can be safely ignored.
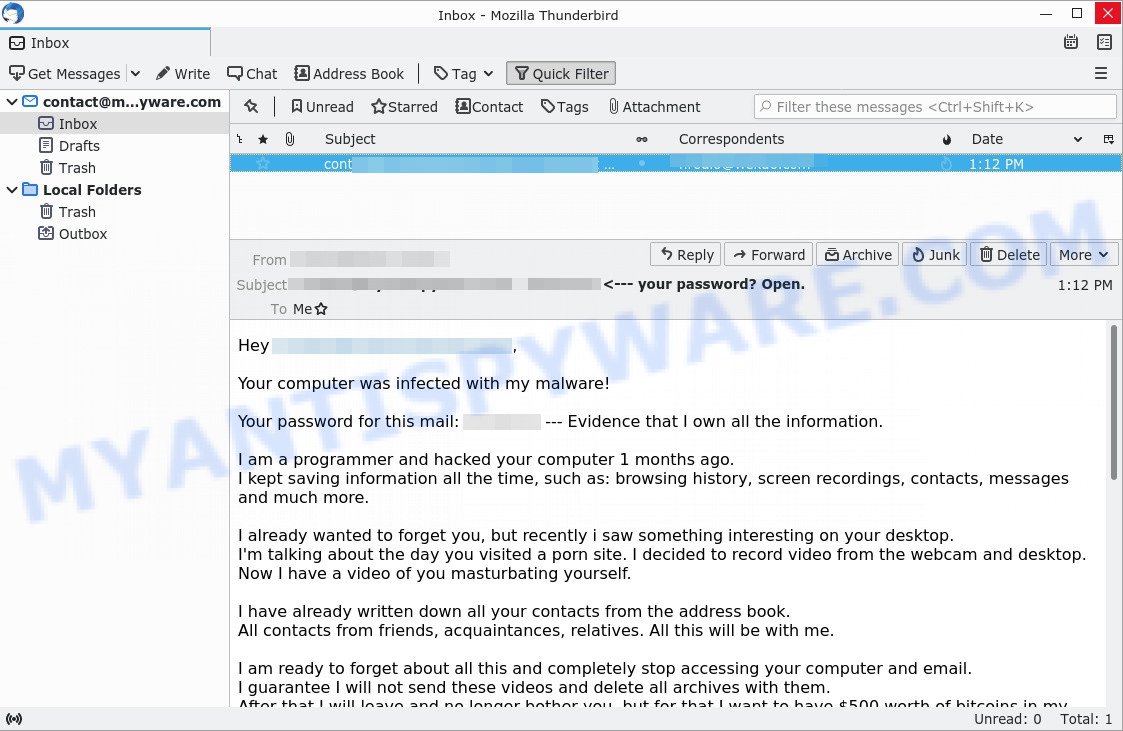
Text presented in the “Your computer was infected with my malware” message:
Hey xxxxxxxx
Your computer was infected with my malware!
Your password for this mail: xxxxxxxx — Evidence that I own all the information.
I am a programmer and hacked your computer 1 months ago.
I kept saving information all the time, such as: browsing history, screen recordings, contacts, messages and much more.I already wanted to forget you, but recently i saw something interesting on your desktop.
I’m talking about the day you visited a porn site. I decided to record video from the webcam and desktop. Now I have a video of you masturbating yourself.I have already written down all your contacts from the address book.
All contacts from friends, acquaintances, relatives. All this will be with me.I am ready to forget about all this and completely stop accessing your computer and email.
I guarantee I will not send these videos and delete all archives with them.
After that I will leave and no longer bother you, but for that I want to have $500 worth of bitcoins in my wallet. You have 48 hours after reading this email.
I still control your email and computer – and I know when you open them and read them.Don’t try to change your email password, everything is under control.
Do not try to contact me and answer this letter. I sent it to you from your email address.
Take a look at the sender, you will see that I have complete control over your email and your computer.Bitcoin wallet address:
bc1qu8zhx0xl58nmrqfqqgezf3e3e6vy6rc6w07nzs
If you do not know how to buy bitcoins, you can find information on how to buy bitcoins online. If you need help, you can read several articles about it.
hxxps://localbitcoins.com/guides/how-to-buy-bitcoins
hxxps://www.coinbase.com/buy-bitcoin?locale=en
hxxps://paxful.com/how-to-buy-bitcoinI look forward to your actions. If you don’t need this data online and with all your friends, send $500 to my wallet BTC. After that I will erase all data and disappear from your life.
Do not be offended by me. If you pay, nothing happens.
Should you pay?
The best advice is: Don’t pay the ransom! If you receive the sextortion email scam, just ignore the scammers’ empty threats. The best way to deal with the scam email is simply to move it to trash!
Threat Summary
| Name | Your computer was infected with my malware SCAM |
| Type | Sextortion, Phishing, Bitcoin Blackmail Scam |
| Email subject line | Login : password <--- your password? Open. |
| Ransom amount | $500 (USD) |
| Bitcoin Address | bc1qu8zhx0xl58nmrqfqqgezf3e3e6vy6rc6w07nzs |
| Distribution method | spam email campaigns |
| Removal | If you gets an email like Your computer was infected with my malware, our computer security experts recommend follow some easy steps below |
There are many variants of the sextortion scam, scammers constantly change the text of emails so that spam filters do not work. In addition, in some cases, criminals can translate the text of sextortion messages into other languages, thus targeting a specific group of Internet users. Unfortunately, there are some bad news for you, Have you recently noticed that I have e-mailed you from your account, I am sorry to inform you that your device was compromised are other examples of sextortion scam emails. Such emails are also often used to distribute ransomware, trojans, worms and other malware. Regardless of what is in the scam emails, scammers and the criminals behind them use these emails to generate profit by tricking the users, the recipients of these emails.
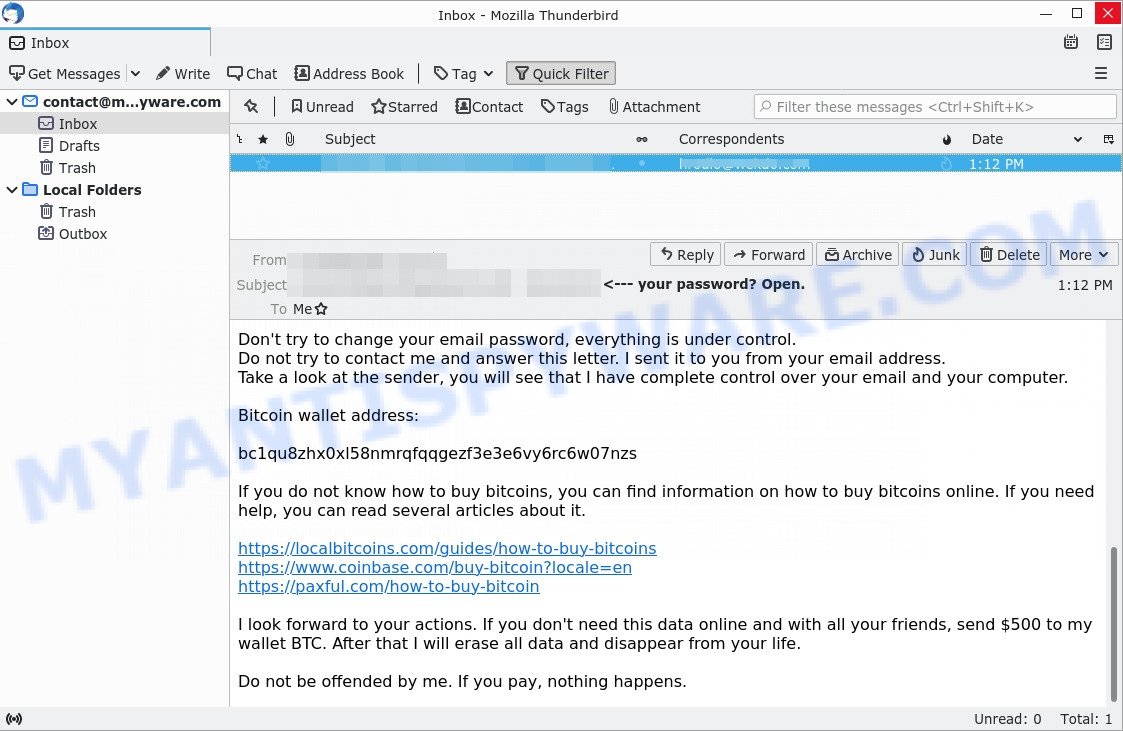
Bottom of the “Your computer was infected with my malware” scam
What to do when you receive the Your computer was infected with my malware SCAM
We advice to someone who gets this fraudulence message:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email spam to the FTC at https://www.ftc.gov/
- Mark the “the Your computer was infected with my malware” email as SPAM/JUNK and delete it
- Scan your computer for malware.
- Install an anti-phishing software.
How to scan your computer for malware
If you suspect that your computer is infected with spyware, you accidentally clicked on a link in the scam email, or just want to scan your computer for malware, then use one of the best free malware removal tools. One of these utilities is Zemana Anti Malware. It is a lightweight utility which designed to use alongside your antivirus software, detecting and removing malicious software, adware and PUPs that other security tools miss. Zemana Anti Malware is easy to use, fast, does not use many resources and have great detection and removal rates.
Please go to the following link to download the latest version of Zemana for Windows. Save it on your desktop.
165086 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
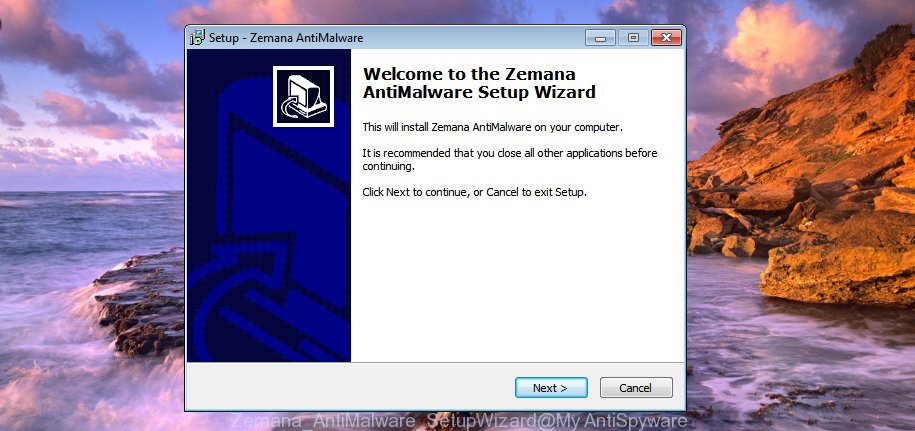
When downloading is complete, close all programs and windows on your PC. Double-click the set up file called Zemana.AntiMalware.Setup. If the “User Account Control” dialog box pops up as displayed in the following example, click the “Yes” button.
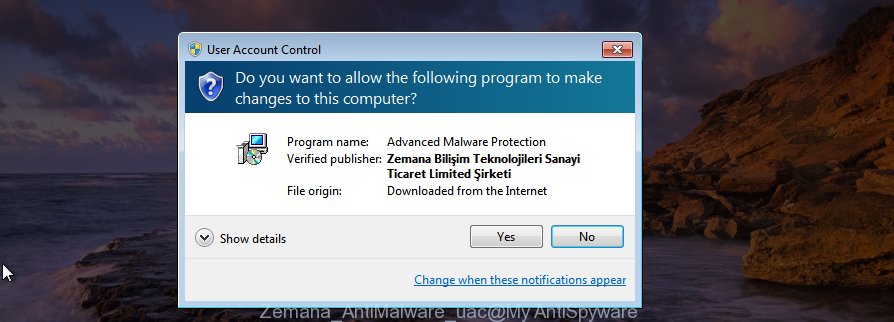
It will open the “Setup wizard” that will help you install Zemana on your PC. Follow the prompts and do not make any changes to default settings.
Once installation is complete successfully, Zemana Anti Malware will automatically start and you can see its main screen as shown on the image below.

Now click the “Scan” button to perform a system scan for malware. While Zemana is scanning the system, you can see how many objects it has identified either as being malware.

After Zemana completes the scan, It will display a screen which contains a list of malware that has been detected. Next, you need to click “Next” button. Zemana will start to remove malicious software. When finished, you may be prompted to restart the system.
If you are having issues with malware removal, then check out MalwareBytes. We recommend this free malware removal utility because it can easily delete trojans, spyware, browser hijackers, adware, potentially unwanted software and toolbars with all their components such as files, folders and registry entries. Visit the page linked below to download the latest version of MalwareBytes Anti-Malware for Windows.
327305 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
We suggest you look at the following video, which completely explains the process of using the MalwareBytes Anti Malware to remove malicious software.
How to protect yourself from phishing, malicious and misleading websites
If you want to protect yourself from phishing websites, then install an ad blocker program such as AdGuard. It can block malicious and misleading web sites, stop unwanted advertisements and popups when using Internet Explorer, Google Chrome, Firefox and Edge. So, if you like surf the Internet, and want to protect your computer from scam pages, then AdGuard is your best choice.
Installing the AdGuard is simple. First you’ll need to download AdGuard by clicking on the link below.
26910 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as displayed below.
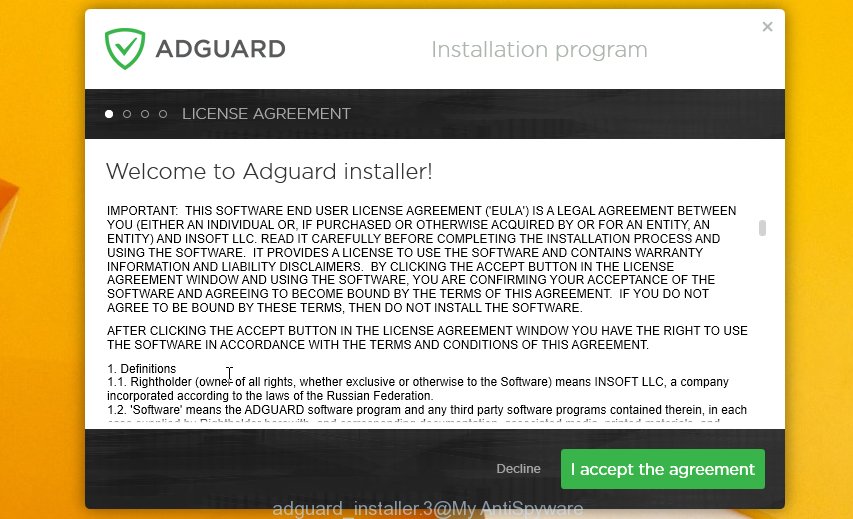
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guide as displayed on the screen below.

Click “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick guidance which will assist you get to know AdGuard better.
Each time, when you start your system, AdGuard will start automatically and stop unwanted advertisements, block phishing, as well as other harmful or misleading websites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. It will help our team monitor the latest scams.


















Hi, I have had a similar email, and the email password mentioned is fully correct, and is my actual password, although form the rest of the email I am sure that this is not true, like I am sure my webcam wasnt hacked, but how did they get my email? And how did it happen? Like how did they email me from my own id?? Like it shows you to you??
Yeah I got a similar email. How did they got my correct password?
it is likely that one of the services that you use or have used in the past has leaked personal data. I recommend that you change this password as soon as possible.
Your password for this mail: ifoycxvlpwrzdd
In my case, this is not my email password, but on Saturday the 22nd they changed the password of my Facebook account that is linked to my email account, I already recovered my Facebook account, but? All this seems suspicious to me, actually if I watch porn and if I masturbate, but will they have so much power to record me?
this email is a scam, ignore it. If you suspect that your computer is infected with a malware, scan it with Malwarebytes or Kaspersky.