What is Hello, I’m going to share important information with you EMAIL?
Hello, I’m going to share important information with you is a new ‘sextortion’ scam that spreads through spam email campaigns. Like most sextortion scams, it uses “social engineering techniques” to induce shame, panic or guilt. The scammers claim that they obtained material compromising victims’ reputations (as a result of a computer hack, email account hack, router hack, etc) and threaten to publish it if the ransom is not paid. All these claims are not based on anything, they are just deception. Therefore, you can safely ignore this email, just delete it or move it to spam.
The “Hello, I’m going to share important information with you.” message is a new SCAM
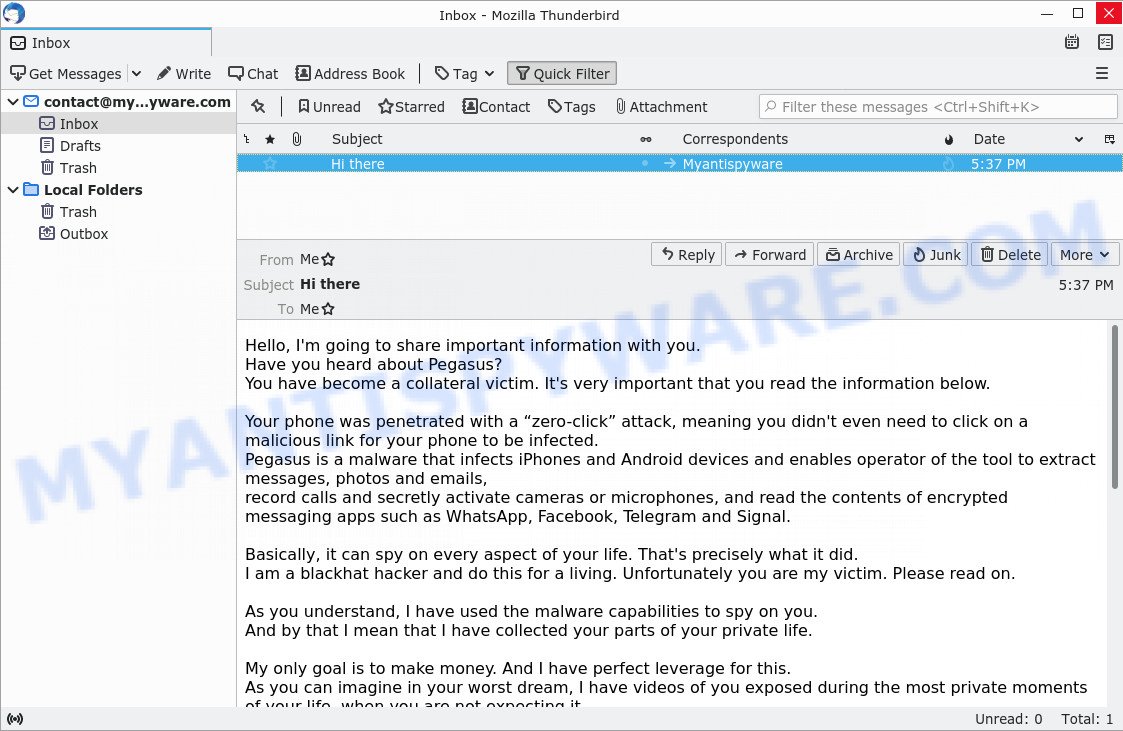
The “Hello, I’m going to share important information with you” email says that someone used a “zero-click” attack to infect the recipient’s device with Pegasus malware. The hacker claims to have recorded videos with parts of the victim’s private life, as this malware completely controls the infected phone, its camera and microphone. The attacker demands a ransom to delete the videos, if the victim does not pay the ransom, the hacker threatens to destroy the victim’s life, publish the videos to public websites and send the videos to contacts. Next, the scam email contains a bitcoin address to which the ransom should be transferred. This email is just a sextortion scam, all statements are fake. Just ignore this email, other similar emails and emails containing similar content.
Text presented in the “Hello, I’m going to share important information with you” message:
Hello, I’m going to share important information with you.
Have you heard about Pegasus?
You have become a collateral victim. It’s very important that you read the information below.Your phone was penetrated with a “zero-click” attack, meaning you didn’t even need to click on a malicious link for your phone to be infected.
Pegasus is a malware that infects iPhones and Android devices and enables operator of the tool to extract messages, photos and emails,
record calls and secretly activate cameras or microphones, and read the contents of encrypted messaging apps such as WhatsApp, Facebook, Telegram and Signal.Basically, it can spy on every aspect of your life. That’s precisely what it did.
I am a blackhat hacker and do this for a living. Unfortunately you are my victim. Please read on.As you understand, I have used the malware capabilities to spy on you.
And by that I mean that I have collected your parts of your private life.My only goal is to make money. And I have perfect leverage for this.
As you can imagine in your worst dream, I have videos of you exposed during the most private moments of your life, when you are not expecting it.I personally have no interest in them, but there are public websites, that have perverts loving that content.
As I said, I only do this to make money and not trying to destroy your life. But if necessary, I will publish the videos.
If this is not enough for you, I will make sure your contacts, friends and everybody you know see those videos as well.Here is the deal. I will delete the files after I receive 0.035 Bitcoin (about 1600 US Dollars).
You need to send that amount here 12mojuzVPeSh26qmA9GLJFADo4chgGbtj3I will also clear your device from malware, and you keep living your life.
Otherwise, shit will happen.The fee is non negotiable, to be transferred within 2 business days.
Obviously do not try to ask for any help from anybody unless you want your privacy to be violated.
I will monitor your every move until I get paid. If you keep your end of the agreement, you wont hear from me ever again.
Take care.
QUICK LINKS
- What is Hello, I’m going to share important information with you EMAIL?
- Should you pay?
- What to do when you receive the email scam?
What is Sextortion email scam
Sextortion is the practice of extorting money from victims by blackmailing them; threatening to reveal evidence of their sexual activity. It is an old scam scheme – which try to guilt people into paying off someone claiming to have secretly recorded video or compromising information. Scammers use a database of stolen email to send out scam emails to millions of people around the World. The messages are sent to email addresses exposed in previous known data breaches in which the user database (email address and/or password) was indexed online.
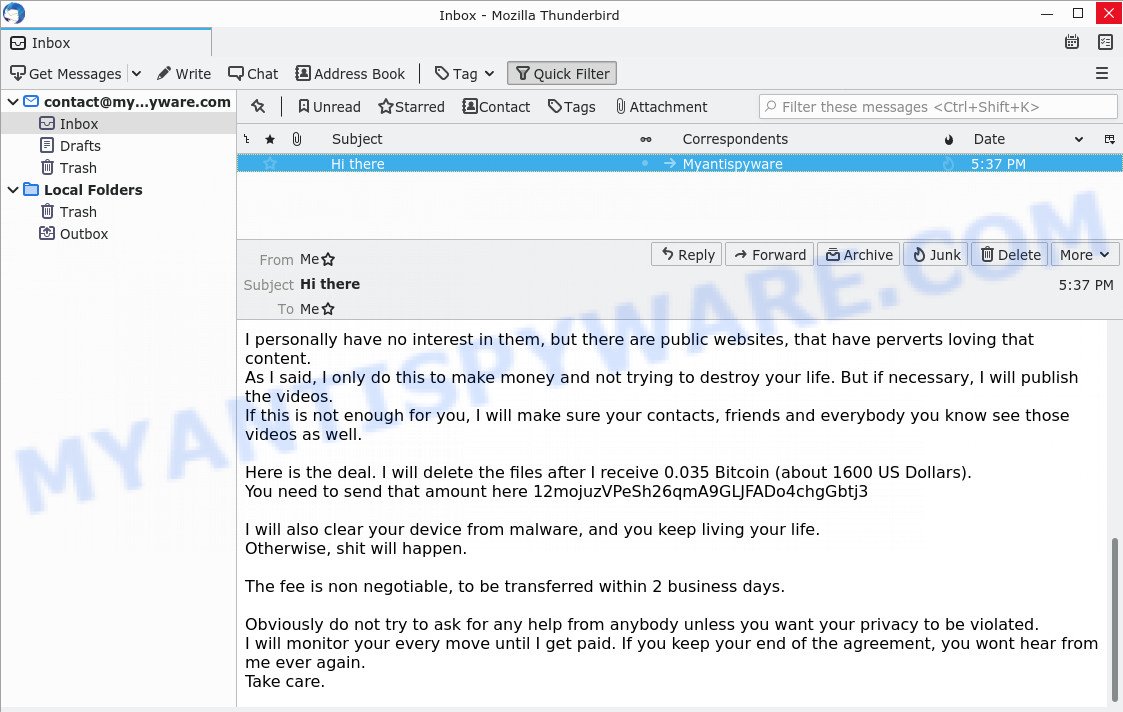
Bottom of the scam email
Should you pay?
The best advice is: Don’t pay the ransom! If you receive the sextortion email scam, just ignore the scammers’ empty threats. The best way to deal with the scam email is simply to move it to trash!
Threat Summary
| Name | Hello, I’m going to share important information with you SCAM |
| Type | Phishing, Bitcoin Email Scam, Fraud, Scam |
| Email subject line | Hi there |
| Ransom amount | 0.035 Bitcoin (about 1600 US Dollars) |
| Bitcoin Address | 12mojuzVPeSh26qmA9GLJFADo4chgGbtj3 |
| Distribution method | spam email campaigns |
| Removal | If you gets an email like Hello, I’m going to share important information with you, our computer security experts recommend follow some easy steps below |
I have to share bad news with you, I am sorry to inform you that your device was compromised and I know * is one of your password on day of hack. Lets get directly to the point. are other examples of Sextortion scam emails. Such emails are also often used to distribute ransomware, trojans, worms and other malware. Regardless of what is in the scam emails, scammers and the criminals behind them use these emails to generate profit by tricking the users, the recipients of these emails.
What to do when you receive the Hello, I’m going to share important information with you SCAM
We advice to someone who gets this fraudulence message:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email spam to the FTC at https://www.ftc.gov/
- Scan your computer for malware.
- Install an anti-phishing software.
How to scan your computer for malware
If you suspect that your computer is infected with Pegasus, you accidentally clicked on a link in the scam email, or just want to scan your computer for malware, then use one of the best free malware removal tools. One of these utilities is Zemana Anti Malware. It is a utility specially developed for malicious software removal. It can detect and remove spyware, adware, browser hijacker, PUPs, trojans, worms and other malicious software for free. Zemana is easy to use, fast, does not use many resources and have great detection and removal rates.
Please go to the following link to download the latest version of Zemana for Windows. Save it on your desktop.
165041 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
When downloading is complete, close all programs and windows on your PC. Double-click the set up file called Zemana.AntiMalware.Setup. If the “User Account Control” dialog box pops up as displayed in the following example, click the “Yes” button.
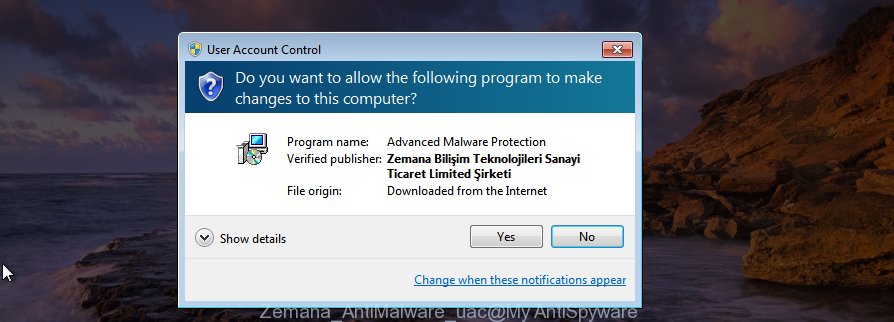
It will open the “Setup wizard” that will help you install Zemana on your PC. Follow the prompts and do not make any changes to default settings.
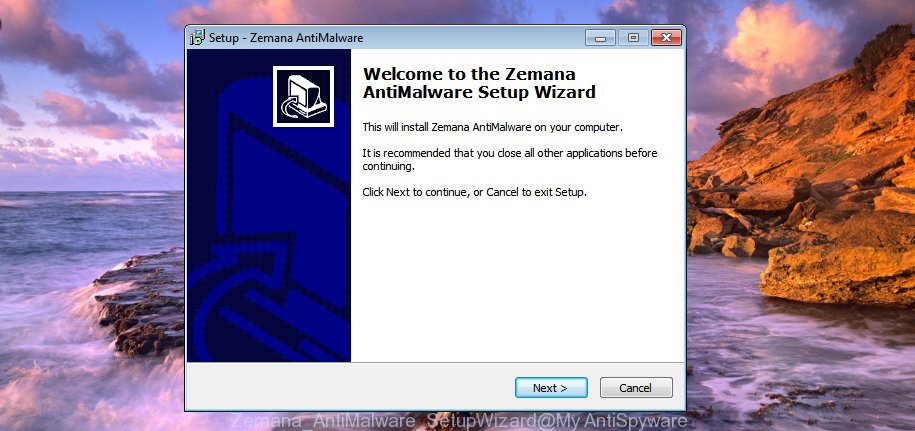
Once installation is complete successfully, Zemana Anti Malware will automatically start and you can see its main screen as shown on the image below.

Now click the “Scan” button to perform a system scan for malware. While Zemana is scanning the system, you can see how many objects it has identified either as being malware.

After Zemana completes the scan, It will display a screen which contains a list of malware that has been detected. Next, you need to click “Next” button. Zemana will start to remove malicious software. When finished, you may be prompted to restart the system.
If you are having issues with malware removal, then check out MalwareBytes. We recommend this free malware removal utility because it may easily delete trojans, spyware, browser hijackers, adware, potentially unwanted software and toolbars with all their components such as files, folders and registry entries. Visit the page linked below to download the latest version of MalwareBytes Anti-Malware for Windows.
327268 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
We suggest you look at the following video, which completely explains the process of using the MalwareBytes Anti Malware to remove malicious software.
How to protect yourself from phishing, malicious and misleading websites
If you want to protect yourself from phishing websites, then install an ad blocker program such as AdGuard. It can block malicious and misleading web sites, stop unwanted advertisements and popups when using the Internet Explorer, Google Chrome, Firefox and Edge. So, if you like surf the Internet, and want to protect your computer from malicious web pages, then the AdGuard is your best choice.
Installing the AdGuard is simple. First you’ll need to download AdGuard by clicking on the link below.
26901 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, double-click the downloaded file to start it. The “Setup Wizard” window will show up on the computer screen as displayed below.
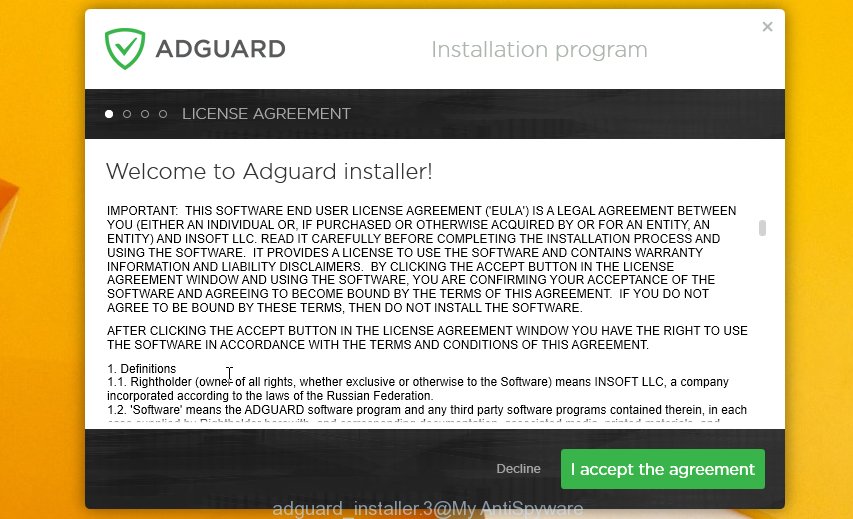
Follow the prompts. AdGuard will then be installed and an icon will be placed on your desktop. A window will show up asking you to confirm that you want to see a quick guide as displayed on the screen below.

Click “Skip” button to close the window and use the default settings, or press “Get Started” to see an quick guidance which will assist you get to know AdGuard better.
Each time, when you start your system, AdGuard will start automatically and stop unwanted advertisements, block phishing, as well as other harmful or misleading websites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, which can be found on your desktop.
Finish words
We hope that this article helped you understand what the “Hello, I’m going to share important information with you” SCAM is and not succumb to the threats of scammers. If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. It will help our team monitor the latest scams.




















Onmgggg i just got this from my office email nonetheless! Thanks for thebinfo phew