@datarestore is a telegram account that fraudsters use to communicate with victims of ransomware virus. What is this ransomware? It’s basically a malicious program that gets on your personal computer and runs. It locks up your documents, photos and music and changes their extensions to something like Gusau, Madek, Gehad and so on. Read below a brief summary of information related to this ransomware and how to restore or decrypt encrypted files for free.
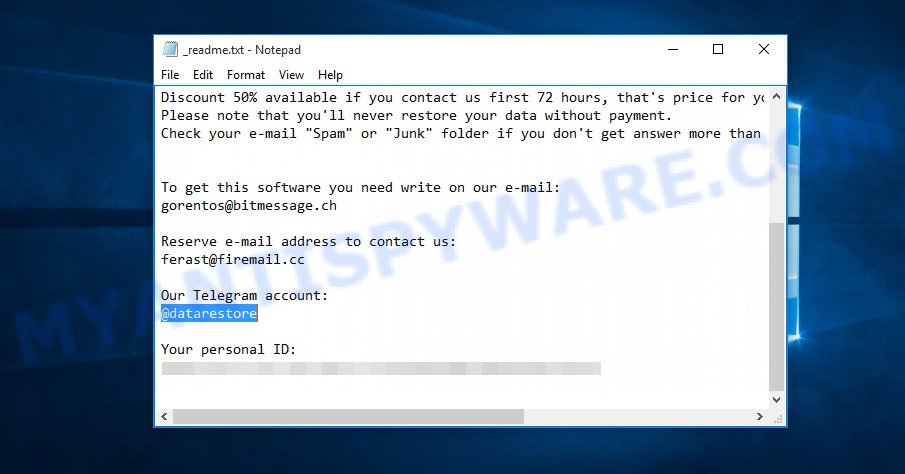
“@datarestore ransomware” – ransom note
The @datarestore ransomware limits you from opening your personal files. It forces you to pay the ransom through certain online payment methods in order to get your documents, photos and music back. It is able to encrypt almost all types of files, including common as:
.pptx, .mpqge, .xdb, .xlsm, .wmv, .crw, .ods, .bay, .gdb, .yal, .xbdoc, .mlx, .zi, .wp, .sidd, .itdb, .3fr, .wot, .m2, .kf, .wotreplay, .psk, .gho, .mdf, .ysp, .xar, .fpk, .wsh, .vpp_pc, .mef, .2bp, .litemod, .wire, .wpg, .wps, .epk, .wbz, .wmo, .dmp, .slm, .wpe, .png, .xlsx, .mov, .itm, .map, .hkx, .xx, .p12, .wma, .docm, .cfr, .doc, .sid, .nrw, .kdb, .srf, .js, .svg, .crt, .zif, .x3f, .pst, .wmd, .erf, .wpd, .re4, .pkpass, .vpk, .ncf, .x3d, .cdr, .wri, .dwg, .1, .cer, .xlsx, .syncdb, .hplg, .ptx, .p7b, .xpm, .wp6, .t12, .sav, .zip, .indd, wallet, .wpd, .x3f, .hvpl, .xlsm, .lbf, .raw, .der, .rtf, .zdb, .layout, .xlk, .xf, .rofl, .mcmeta, .mdbackup, .ppt, .xmmap, .tor, .odc, .xbplate, .wpa, .pef, .vfs0, .wp5, .wbm, .3dm, .jpe, .wgz, .pak, .bc6, .iwi, .csv, .wpt, .zw, .xyp, .upk, .dba, .raf, .mdb, .bik, .iwd, .das, .w3x, .wpb, .odp, .ltx, .zabw, .sidn, .dazip, .wma, .xlsb, .mrwref, .dng, .xwp, .ztmp, .pdd, .qdf, .rwl, .hkdb, .srw, .arw, .m3u, .psd, .eps, .xyw, .m4a, .rw2, .bar, .wsd, .zdc, .dbf, .z3d, .pptm, .avi, .webdoc, .jpeg, .bsa, .t13, .flv, .xxx, .cr2, .r3d, .wdb, .big, .xld, .xls, .vtf, .xy3, .jpg, .ai, .bkf, .wbd, .ff, .wbc, .xll, .xls, .esm, .cas, .wdp, .arch00, .pdf, .wbk, .fsh, .rar, .mp4, .yml, .kdc, .wcf, .wsc, .apk, .webp, .1st, .fos, .wn, .wmv, .0, .py, .sb, .ibank, .d3dbsp, .desc, .xlgc, .icxs, .orf, .rim, .dcr, .forge, .dxg, .bkp, .xdl, .tax, .pfx, .lvl, .wbmp, .sr2, .txt, .qic, .itl, .wpw, .wp7
The @datarestore ransomware virus encrypts users’ files using a complex encryption algorithm, overwrites most of the content of the original files with the encrypted data and adds a new extension to every encrypted file. The user who sees the files with a new extension understands that they are locked and will remain so until he pays the attackers the required amount of money for obtaining a special key that will decrypt the files. Usually, the creators of the @datarestore leave a ransom note called ‘_readme.txt’ to users who have infected their computer with this crypto malware, indicating the required amount of ransom.
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-g2wRDh3Pih Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: [email protected] Reserve e-mail address to contact us: [email protected] Our Telegram account: @datarestore Mark Data Restore Your personal ID:
Threat Summary
| Name | @datarestore ransomware |
| Type | Ransomware, Crypto virus, Crypto malware, Filecoder, File locker |
| Encrypted files extension | gusau, madek, gehad, .berosuce, .herad, .vusad, .budak, .godes, … |
| Ransom note | _readme.txt |
| Contact | @datarestore (telegram acc) |
| Ransom amount | $980 in Bitcoins |
| Symptoms | Unable to open files. Windows Explorer displays a blank icon for the file type. Files named like ‘_readme.txt’, or ‘_readme’ in each folder with at least one encrypted file. |
| Distribution methods | Malicious spam (also known as ‘malspam’). Drive-by downloading (when a user unknowingly visits an infected web page and then malware is installed without the user’s knowledge). Social media posts (they can be used to entice users to download malicious software with a built-in ransomware downloader or click a malicious link). Malvertising campaigns. |
| Removal | To remove @datarestore ransomware use the removal guide |
| Decryption | To decrypt @datarestore ransomware use the steps |
We recommend you to delete @datarestore virus as soon as possible, until the presence of the crypto virus has not led to even worse consequences. You need to follow the step-by-step guide below that will allow you to completely remove @datarestore ransomware from your computer as well as recover encrypted personal files, using only few free utilities.
Quick links
- How to remove @datarestore ransomware
- How to decrypt encrypted files
- @datarestore ransomware decryption tool
- How to protect your computer from @datarestore crypto virus?
How to remove @datarestore ransomware
The @datarestore ransomware virus can hide its components which are difficult for you to find out and uninstall completely. This may lead to the fact that after some time, the crypto virus again infect your computer and encrypt your files. Moreover, I want to note that it is not always safe to remove ransomware virus manually, if you don’t have much experience in setting up and configuring the Windows operating system. The best solution to scan for and remove @datarestore crypto malware is to use free malicious software removal applications that are listed below.
Remove @datarestore ransomware virus with Zemana AntiMalware (ZAM)
Zemana AntiMalware (ZAM) is a free malware removal tool. Currently, there are two versions of the program, one of them is free and second is paid (premium). The principle difference between the free and paid version of the utility is real-time protection module. If you just need to check your computer for malware and remove @datarestore ransomware and other security threats, then the free version will be enough for you.

- Zemana can be downloaded from the following link. Save it to your Desktop so that you can access the file easily.
Zemana AntiMalware
165741 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
- At the download page, click on the Download button. Your browser will open the “Save as” dialog box. Please save it onto your Windows desktop.
- When downloading is done, please close all apps and open windows on your PC. Next, start a file called Zemana.AntiMalware.Setup.
- This will run the “Setup wizard” of Zemana Anti Malware onto your PC system. Follow the prompts and don’t make any changes to default settings.
- When the Setup wizard has finished installing, the Zemana will run and open the main window.
- Further, press the “Scan” button to perform a system scan with this utility for the @datarestore crypto malware, other malicious software, worms and trojans. A scan may take anywhere from 10 to 30 minutes, depending on the number of files on your personal computer and the speed of your personal computer. While the utility is scanning, you can see how many objects and files has already scanned.
- After the scan get completed, Zemana Free will open a list of found items.
- Review the scan results and then click the “Next” button. The utility will uninstall @datarestore ransomware, other malware, worms and trojans and move items to the program’s quarantine. When finished, you may be prompted to restart the system.
- Close the Zemana and continue with the next step.
Remove @datarestore ransomware with MalwareBytes Free
Remove @datarestore crypto malware manually is difficult and often the ransomware is not fully removed. Therefore, we advise you to use the MalwareBytes AntiMalware (MBAM) which are completely clean your PC. Moreover, this free application will help you to uninstall malicious software, trojans, worms and spyware that your PC can be infected too.
Visit the following page to download MalwareBytes. Save it on your MS Windows desktop.
328051 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
After downloading is finished, close all windows on your PC system. Further, start the file named mb3-setup. If the “User Account Control” dialog box pops up as shown on the screen below, click the “Yes” button.
It will display the “Setup wizard” which will help you set up MalwareBytes Anti Malware (MBAM) on the system. Follow the prompts and do not make any changes to default settings.

Once setup is finished successfully, click Finish button. Then MalwareBytes AntiMalware will automatically start and you can see its main window as displayed on the screen below.
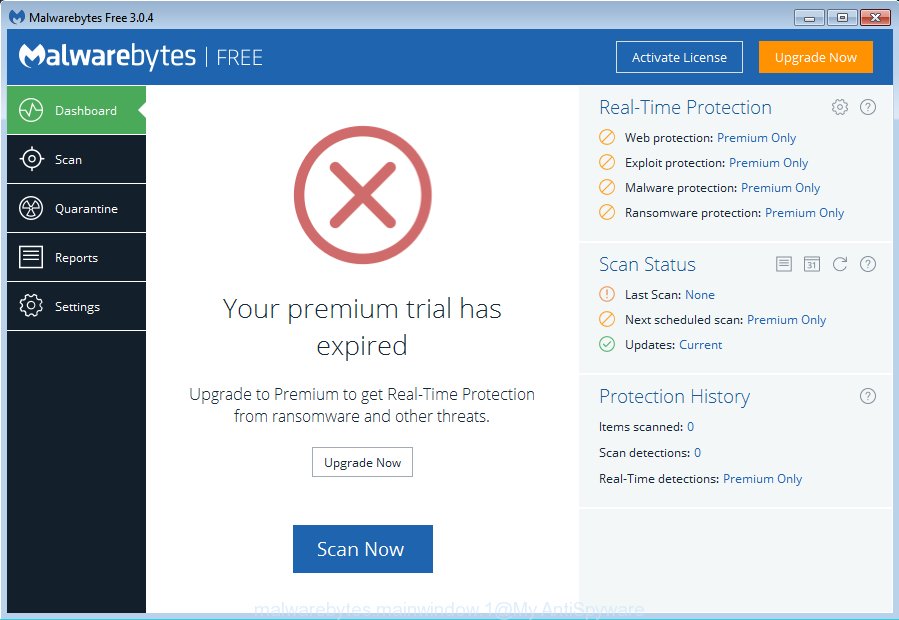
Next, click the “Scan Now” button to start checking your PC for the @datarestore ransomware virus related files, folders and registry keys. This procedure can take quite a while, so please be patient. While the MalwareBytes Free tool is scanning, you can see count of objects it has identified as being affected by malicious software.
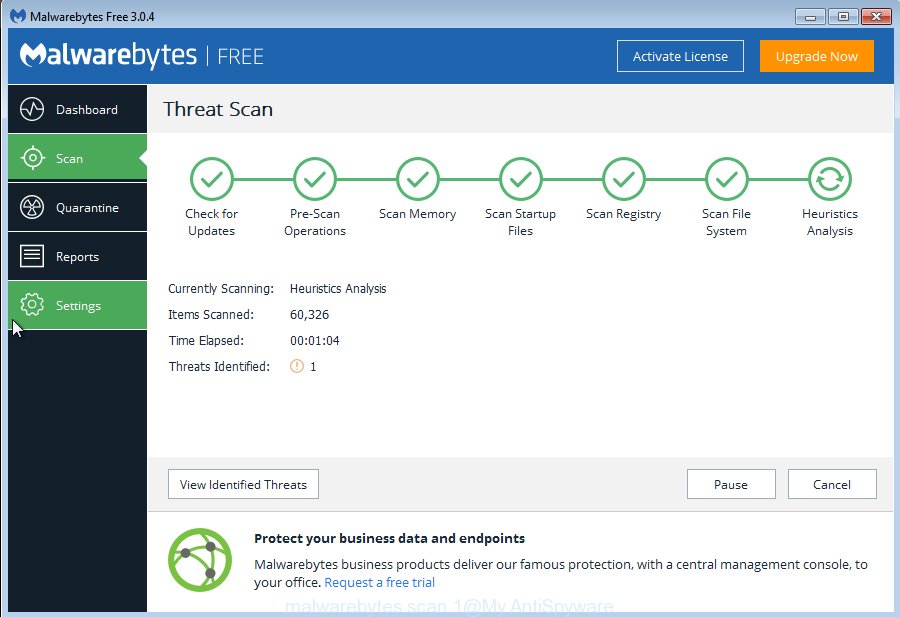
When finished, you will be displayed the list of all found threats on your computer. Review the scan results and then press “Quarantine Selected” button.
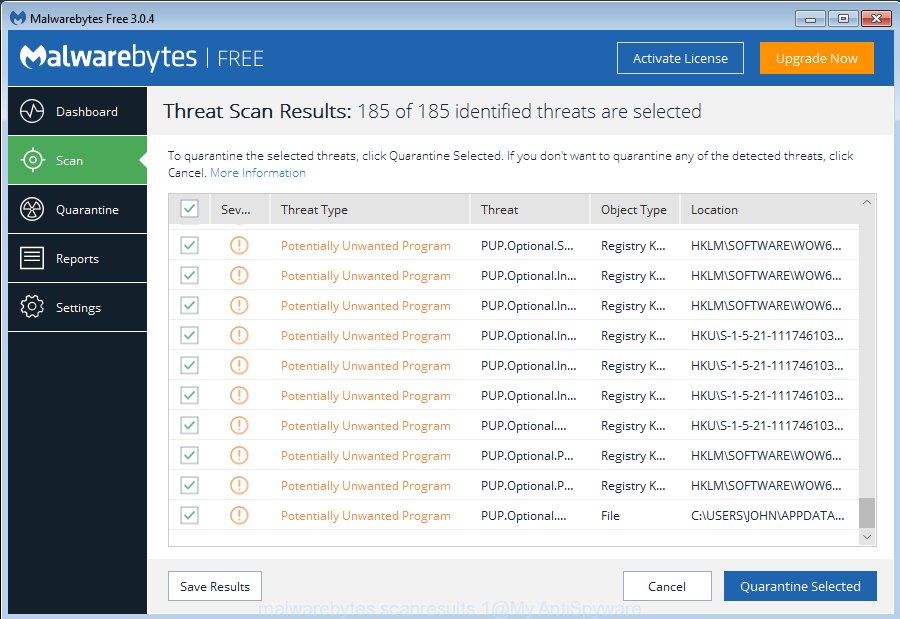
The MalwareBytes Anti-Malware (MBAM) will delete @datarestore crypto virus related files, folders and registry keys and add threats to the Quarantine. Once the clean up is finished, you may be prompted to restart your PC. We recommend you look at the following video, which completely explains the procedure of using the MalwareBytes to delete browser hijackers, adware software and other malware.
Run KVRT to delete @datarestore ransomware virus from the computer
KVRT is a free removal tool that can be downloaded and use to uninstall ransomware viruses, adware, malware, PUPs, toolbars and other threats from your PC system. You may run this utility to scan for threats even if you have an antivirus or any other security application.
Download Kaspersky virus removal tool (KVRT) by clicking on the link below.
129572 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
Once the downloading process is finished, double-click on the Kaspersky virus removal tool icon. Once initialization process is finished, you’ll see the KVRT screen such as the one below.
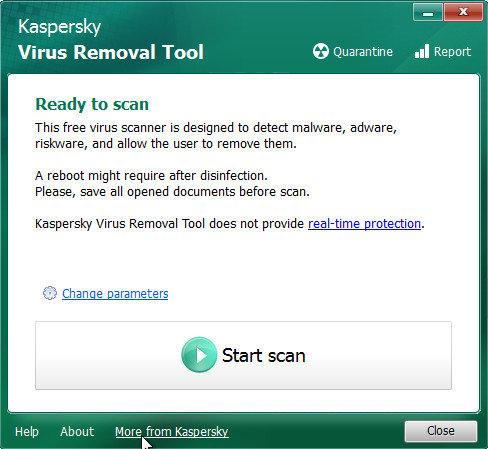
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next press Start scan button . KVRT tool will start scanning the whole PC system to find out @datarestore ransomware and other known infections. This process may take quite a while, so please be patient.
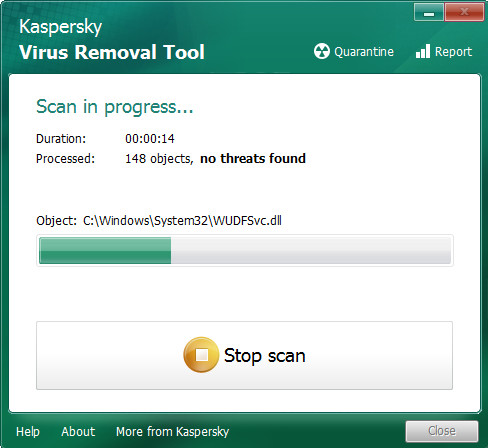
Once that process is done, a list of all threats detected is prepared as shown below.
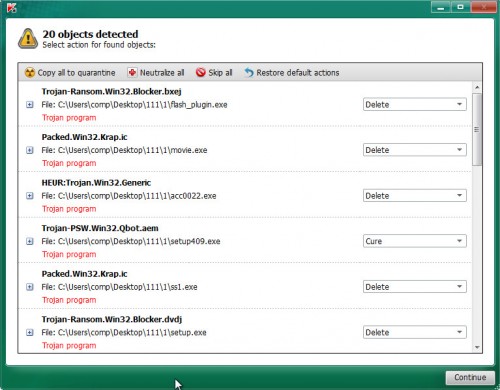
In order to remove all items, simply press on Continue to begin a cleaning procedure.
How to decrypt encrypted files
You can damage documents, photos and music encrypted with @datarestore ransomware virus, or make them useless forever if you try to find the special code key on your own, which is almost impossible in view of its cryptographic complexity. It is very important to know and understand the level of importance of constantly backing up important files to various media, such as an USB key, so that in case of damage to your system by malware you can always extract a copy of encrypted files.

However, it should be noted that the transferred amount of money to fraudsters is not yet a guarantee that the user will receive a code to unlock the affected documents, photos and music. Very often, after receiving the ransom payment, cyber criminals impose new requirements for the transfer of an even larger amount of money. It is impossible to predict unambiguously what will be the actions of cyber frauds who made the @datarestore crypto virus, but it is safe to say that these actions are immoral and illegal.
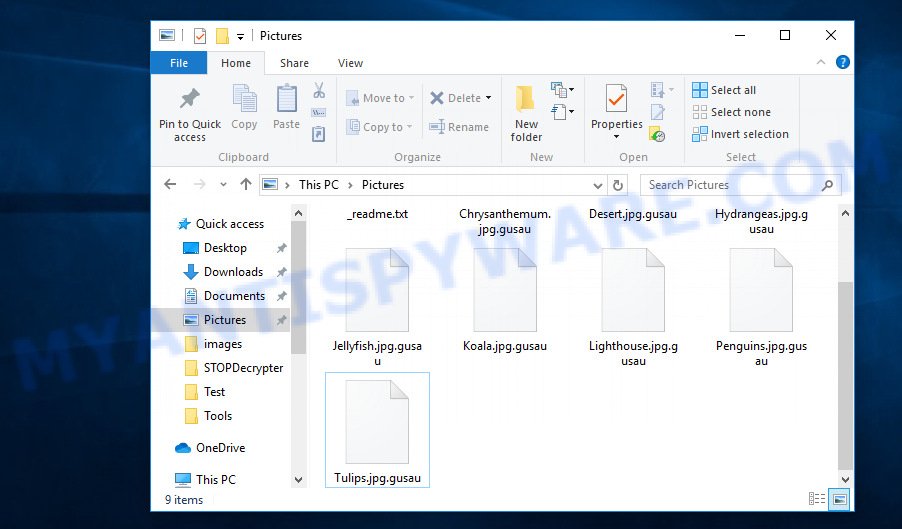
Files locked by @datarestore ransomware
@datarestore ransomware decryption tool
With some variants of @datarestore ransomware, it is possible to decrypt encrypted files using free tools listed below.
Michael Gillespie (@) released the @datarestore ransomware decryption tool named STOPDecrypter. It can decrypt locked files if they were encrypted by one of the known OFFLINE KEY’s retrieved by Michael Gillespie. Please check the twitter post for more info.
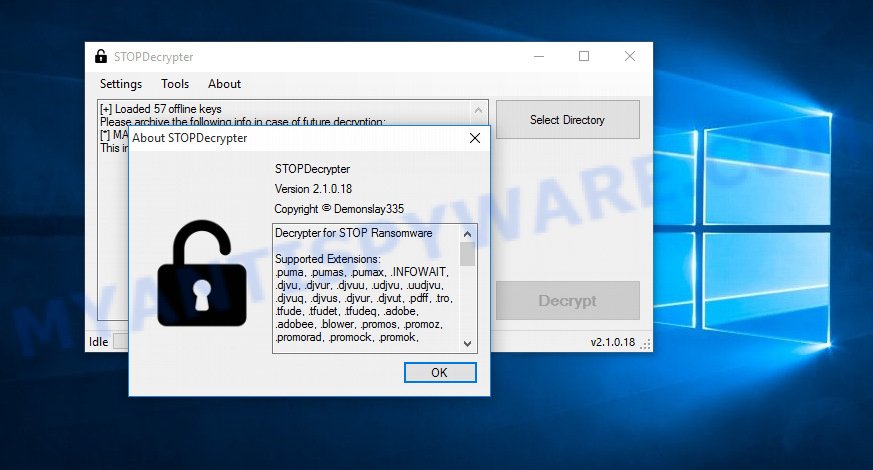
@datarestore ransomware decryption tool
STOPDecrypter is a program that can be used for @datarestore ransomware decryption. One of the biggest advantages of using STOPDecrypter is that is free and easy to use. Also, it constantly keeps updating its ‘OFFLINE KEYs’ DB. Let’s see how to install STOPDecrypter and decrypt encrypted files using this free tool.
- Installing the STOPDecrypter is simple. First you will need to download STOPDecrypter on your Windows Desktop from the following link.
download.bleepingcomputer.com/demonslay335/STOPDecrypter.zip - After the downloading process is done, close all applications and windows on your machine. Open a file location. Right-click on the icon that’s named STOPDecrypter.zip.
- Further, select ‘Extract all’ and follow the prompts.
- Once the extraction process is finished, run STOPDecrypter. Select Directory and press Decrypt button.
If STOPDecrypter does not help you to decrypt files, in some cases, you have a chance to recover your files, which were encrypted by ransomware. This is possible due to the use of the tools named ShadowExplorer and PhotoRec. An example of recovering encrypted files is given here.
How to protect your computer from @datarestore crypto virus?
Most antivirus programs already have built-in protection system against the ransomware virus. Therefore, if your PC does not have an antivirus program, make sure you install it. As an extra protection, use the HitmanPro.Alert.
Run HitmanPro.Alert to protect your PC from @datarestore ransomware virus
HitmanPro.Alert is a small security utility. It can check the system integrity and alerts you when critical system functions are affected by malware. HitmanPro.Alert can detect, remove, and reverse ransomware effects.
First, visit the following page, then press the ‘Download’ button in order to download the latest version of HitmanPro Alert.
When downloading is finished, open the file location. You will see an icon like below.

Double click the HitmanPro Alert desktop icon. After the utility is started, you’ll be shown a window where you can choose a level of protection, as displayed on the image below.

Now click the Install button to activate the protection.




















