A ransomware named Gusau file virus is another development of fraudsters. The principle of its functioning and the method of distribution is the same as in the case of the Madek ransomware, Gehad file virus, Herad file virus, and so on, the only difference is the .gusau extension applied to the files that are infected with it.
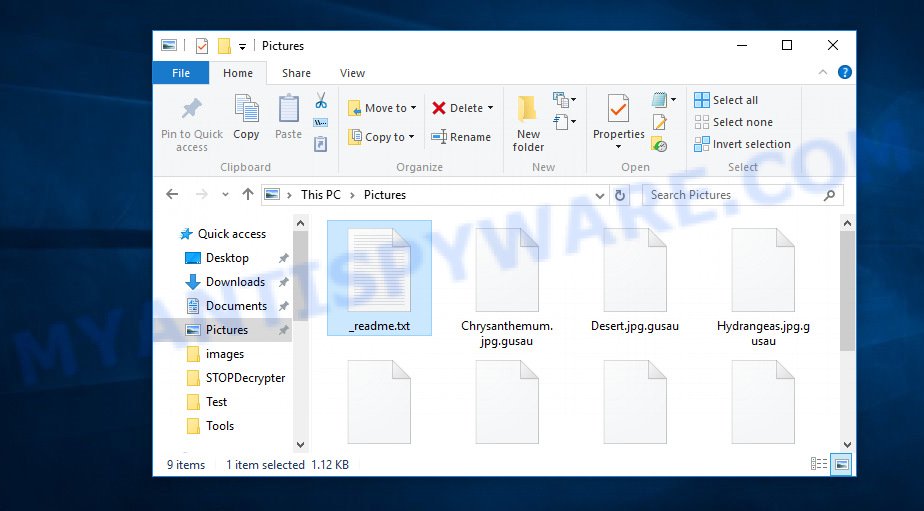
Files encrypted by .Gusau ransomware
Gusau ransomware was developed by fraudsters to lock various files on the user’s PC system, using a hybrid encryption mode, which makes it impossible for the user to independently decrypt the affected files that have received .gusau extension. It can encrypt almost all types of files, including common as:
.wpb, .pef, .kdb, .xpm, .das, .dazip, .wbc, .txt, .sid, .xlsb, .m4a, .cas, .mrwref, .wbk, .zi, .pptm, .dba, .vpp_pc, .gdb, .yml, .pem, .xmind, .ptx, .wmd, .z, .raf, .wsc, .hvpl, .xlsm, .sum, .ibank, .sr2, .wps, .wps, .kf, .bsa, .xar, .vdf, .mdf, .arch00, .wcf, .p7b, .map, .layout, .mp4, .t13, .vcf, .mlx, .wp4, .xmmap, .js, .sidd, .dwg, .x3f, .jpe, .ppt, .sav, .dxg, .xls, .png, .zif, .fsh, .w3x, .pdd, .avi, .qdf, .zip, .srw, .bc7, .mpqge, .bkp, .yal, .xx, .docx, .nrw, .pst, .zw, .wp, .litemod, .webdoc, .cr2, .xbplate, .rofl, .psd, .wav, .wpd, .wp7, .webp, .wpe, .x3d, .t12, .wgz, .hkdb, .bik, .hkx, .asset, .xdb, .dng, .wp5, .sis, .desc, .slm, .mddata, .menu, .xlsx, .iwd, .crw, .css, .xlsm, .wmv, .orf, .wsd, .syncdb, .bkf, .7z, .cer, .wdb, .xml, .ybk, .eps, .raw, .der, .d3dbsp, .x3f, .fos, .rar, .esm, .dbf, .r3d, .wpg, .1, .sie, .xbdoc, .xlsx, .x, .mov, .wb2, .xld, .csv, .py, .itl, .odc, .tax, .sidn, .xll, .wm, .wpl, .mef, .pptx, .blob, .db0, .xlgc, .mdbackup, .svg, .ff, .wma, .ntl, .bc6, .wbmp, .0, .apk, .flv, .dmp, .wmv, .vpk, .xy3, .re4, .rim, .jpg, .gho, .wbm, .ztmp, .wn, .itdb, .wsh, .doc, .forge, .wire, .rwl, .zabw, .y, .cfr, .hplg, .rb, .1st, .zip, .odm, .wp6, .icxs, .m3u, .cdr, .xyw, .crt, .rtf, .srf, .sql
Once on the PC, the Gusau virus completely locks up the documents, photos and music so that the victim can not open them. In this case, the only option to unlock the files is to pay a ransom to cyber criminals who are Gusau authors and offer a key to decrypt all affected files. The authors of crypto virus have done everything possible to be sure that the victim will immediately determine what exactly is affected with its crypto virus, as the locked photos, documents and music will have the .gusau extension. Also, cybercriminals leave a ransom message called ‘_readme.txt’ indicating the amount of money that victim need to pay to decrypt the files.
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-514KtsAKtH Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.
Threat Summary
| Name | Gusau |
| Type | Crypto virus, Ransomware, Filecoder, File locker, Crypto malware |
| Encrypted files extension | .gusau |
| Ransom note | _readme.txt |
| Contact | @datarestore (telegram), gorentos@bitmessage.ch |
| Ransom amount | $980 in Bitcoins |
| Detection Names | Win32:Malware-gen, A Variant Of Win32/Kryptik.GUSY, Trojan:Win32/Gedese.YA!MTB, Trojan.MalPack.GS |
| Symptoms | When you try to open your file, Windows notifies that you do not have permission to open this file. All of your documents, photos and music have a odd file extension appended to the filenames. Files called such as ‘_readme.txt’, ‘#_README_#’, ‘_DECRYPT_’ or ‘recover’ in each folder with at least one encrypted file. Ransom note in a pop-up window with cybercriminal’s ransom demand and instructions. |
| Distribution methods | Phishing emails that look like they come from a reliable source. Exploit kits (cybercriminals use crypto malware packaged in an ‘exploit kit’ that can find a vulnerability in PDF reader, Adobe Flash Player, Microsoft Windows OS, Browser). Social media, such as web-based instant messaging programs. Malicious web-pages. |
| Removal | To remove Gusau ransomware use the removal guide |
| Decryption | To decrypt Gusau ransomware use the steps |
We suggest you to remove Gusau ransomware virus as quickly as possible, until the presence of the ransomware has not led to even worse consequences. You need to follow the steps below that will help you to completely remove Gusau ransomware from your machine as well as recover encrypted personal files, using only few free tools.
Quick links
How to remove .Gusau file virus
The following instructions will allow you to remove Gusau ransomware virus and other malicious software. Before doing it, you need to know that starting to delete the ransomware, you may block the ability to decrypt documents, photos and music by paying creators of the ransomware virus requested ransom. Zemana Anti-malware, KVRT and Malwarebytes Anti-malware can detect different types of active ransomwares and easily delete it from your machine, but they can not recover encrypted files.
Remove Gusau ransomware virus with Zemana
Zemana Anti-Malware (ZAM) highly recommended, because it can find security threats such the Gusau crypto virus, other malware and trojans that most ‘classic’ antivirus applications fail to pick up on. Moreover, if you have any Gusau removal problems which cannot be fixed by this utility automatically, then Zemana AntiMalware provides 24X7 online assistance from the highly experienced support staff.
Download Zemana AntiMalware (ZAM) from the link below.
165054 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
After downloading is done, start it and follow the prompts. Once installed, the Zemana Free will try to update itself and when this process is done, press the “Scan” button . Zemana Anti Malware program will scan through the whole system for the Gusau crypto malware, other kinds of potential threats such as malware and trojans.

This procedure can take some time, so please be patient. During the scan Zemana will scan for threats present on your system. All detected threats will be marked. You can delete them all by simply click “Next” button.
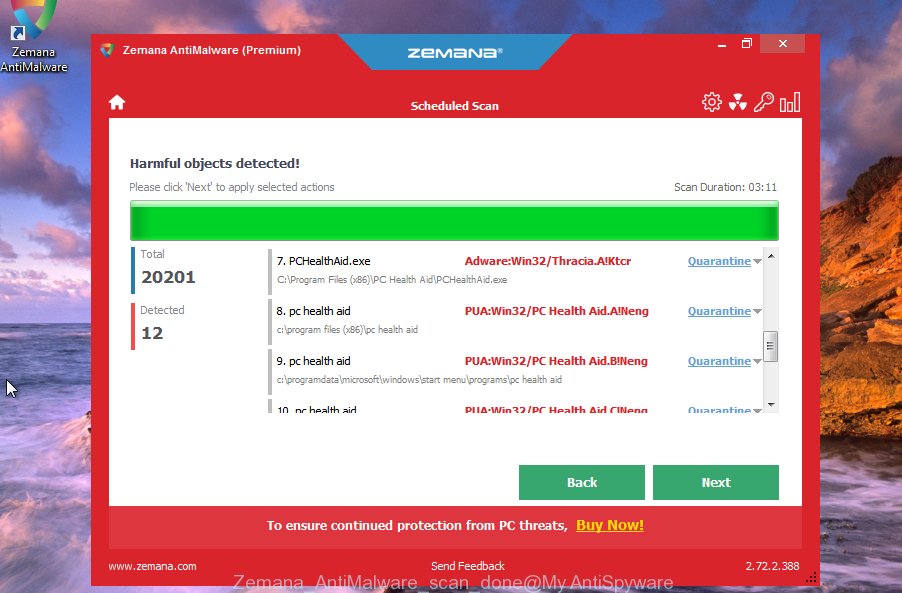
The Zemana will remove Gusau crypto virus related files, folders and registry keys and move items to the program’s quarantine.
How to remove Gusau with MalwareBytes Free
Get rid of Gusau crypto malware manually is difficult and often the crypto malware is not fully removed. Therefore, we suggest you to use the MalwareBytes Free which are fully clean your machine. Moreover, this free application will allow you to uninstall malware, PUPs, toolbars and adware software that your personal computer can be infected too.
Please go to the following link to download the latest version of MalwareBytes for MS Windows. Save it directly to your MS Windows Desktop.
327280 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
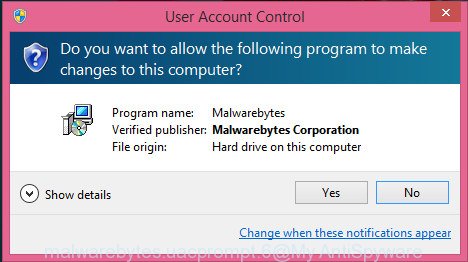
After the downloading process is complete, close all software and windows on your system. Double-click the setup file named mb3-setup. If the “User Account Control” dialog box pops up as displayed in the figure below, click the “Yes” button.
It will open the “Setup wizard” which will help you install MalwareBytes AntiMalware on your machine. Follow the prompts and don’t make any changes to default settings.
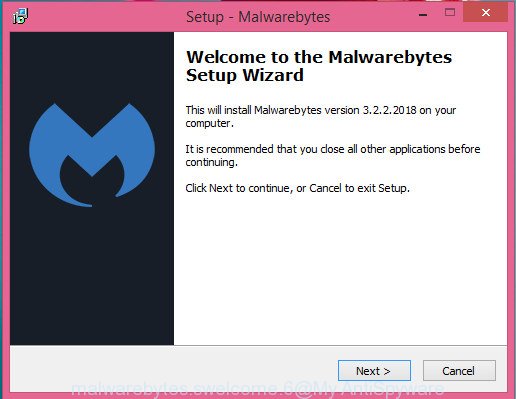
Once installation is finished successfully, click Finish button. MalwareBytes AntiMalware (MBAM) will automatically start and you can see its main screen as shown in the following example.
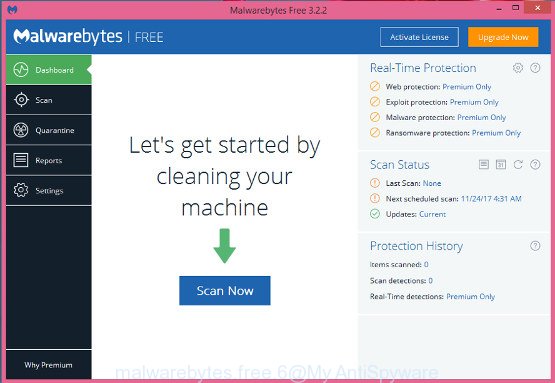
Now press the “Scan Now” button . MalwareBytes tool will begin scanning the whole machine to find out Gusau crypto malware related files, folders and registry keys. This task may take quite a while, so please be patient. While the MalwareBytes is scanning, you can see how many objects it has identified either as being malicious software.
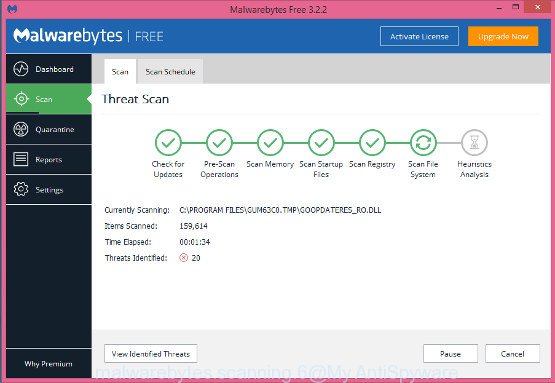
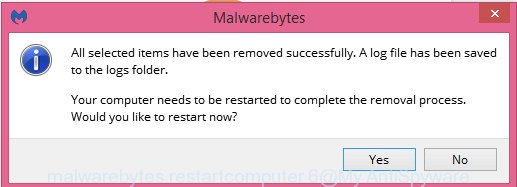
After finished, the results are displayed in the scan report. When you’re ready, click “Quarantine Selected” button. The MalwareBytes will remove Gusau ransomware virus, other kinds of potential threats such as malicious software and trojans and add threats to the Quarantine. After finished, you may be prompted to reboot the PC.
We suggest you look at the following video, which completely explains the process of using the MalwareBytes Anti Malware to remove adware, hijacker and other malicious software.
Remove Gusau ransomware from computer with KVRT
If MalwareBytes antimalware or Zemana anti-malware cannot uninstall this crypto virus, then we recommends to use the KVRT. KVRT is a free removal tool for crypto malwares, adware, potentially unwanted programs and toolbars.
Download Kaspersky virus removal tool (KVRT) on your Microsoft Windows Desktop from the link below.
129296 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
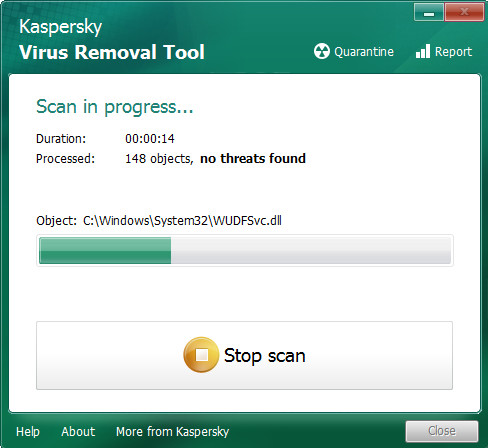
After the downloading process is done, double-click on the Kaspersky virus removal tool icon. Once initialization process is finished, you’ll see the Kaspersky virus removal tool screen as shown below.
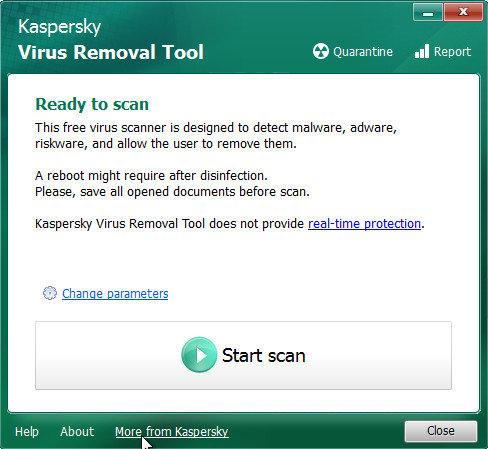
Click Change Parameters and set a check near all your drives. Click OK to close the Parameters window. Next click Start scan button to find Gusau crypto virus and other malware. This process can take quite a while, so please be patient.
As the scanning ends, KVRT will display a screen which contains a list of malware that has been detected as displayed on the screen below.
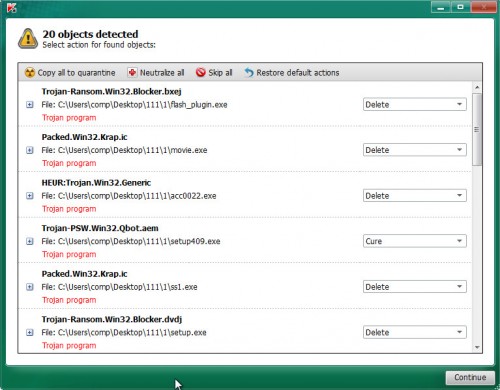
When you are ready, click on Continue to start a cleaning task.
How to decrypt .gusau files
As mentioned earlier, the ransom payment is the only way to decrypt .gusau files, unfortunately. After the user transfers the specified amount of money (usually $980 in Bitcoins) to the fraudsters, they provide a private key to decrypt the affected data.

Some users, wishing to unlock encrypted files, pay the ransom amount of money to cyber criminals. However, it is important to remember before performing this action that you are interacting with unscrupulous and dishonest people, and the probability that after transferring money they will not provide you with a special code key and Gusau decryption tool to decrypt .gusau files or increase the amount of ransom is high enough.
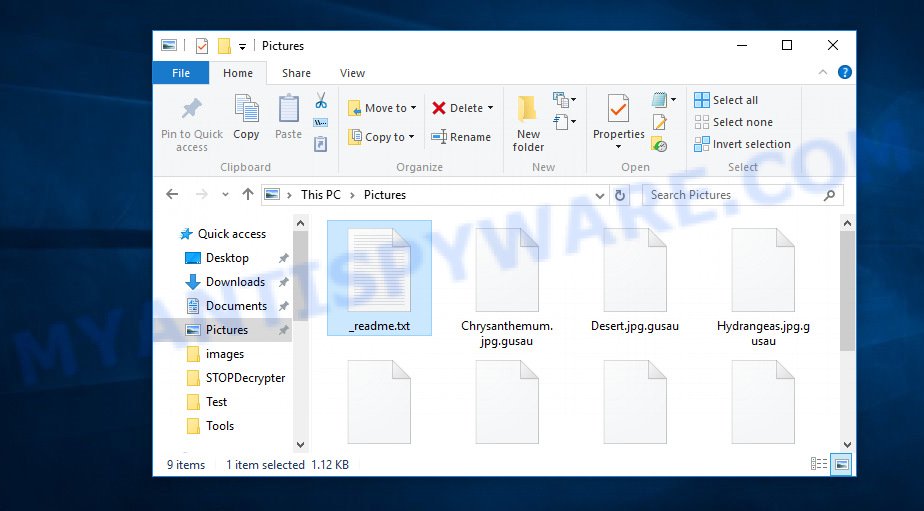
Files encrypted by .Gusau ransomware
However, it is not necessary to pay the authors of the Gusau ransomware virus a ransom, the best option in case of infection of this crypto virus is to archive the files that were locked by it, until the moment of obtaining the Gusau decryption tool. On this blog post below you will find effective steps on how to recover encrypted files for free.
Gusau decryption tool
With some variants of Gusau ransomware, it is possible to decrypt encrypted files using free tools listed below.
Michael Gillespie (@) released the Gusau decryption tool named STOPDecrypter. It can decrypt .Gusau files if they were encrypted by one of the known OFFLINE KEY’s retrieved by Michael Gillespie. Please check the twitter post for more info.
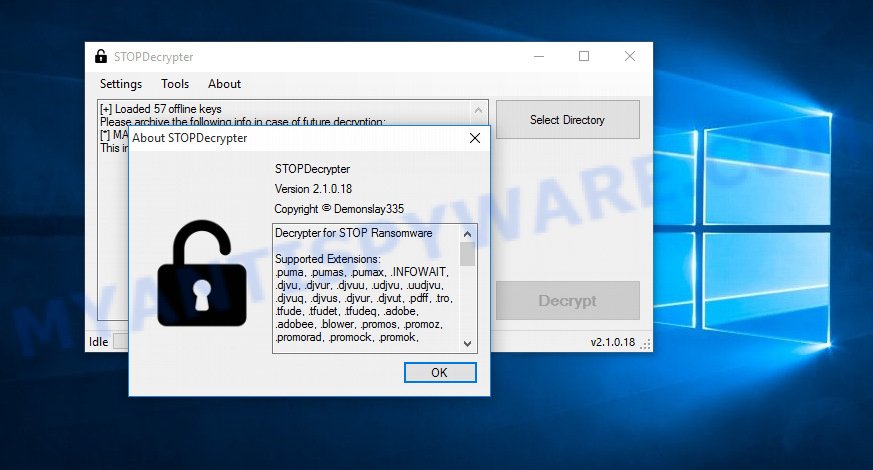
Gusau decryption tool
STOPDecrypter is a program that can be used for Gusau files decryption. One of the biggest advantages of using STOPDecrypter is that is free and easy to use. Also, it constantly keeps updating its ‘OFFLINE KEYs’ DB. Let’s see how to install STOPDecrypter and decrypt .Gusau files using this free tool.
- Installing the STOPDecrypter is simple. First you will need to download STOPDecrypter on your Windows Desktop from the following link.
download.bleepingcomputer.com/demonslay335/STOPDecrypter.zip - After the downloading process is done, close all applications and windows on your machine. Open a file location. Right-click on the icon that’s named STOPDecrypter.zip.
- Further, select ‘Extract all’ and follow the prompts.
- Once the extraction process is finished, run STOPDecrypter. Select Directory and press Decrypt button.
If STOPDecrypter does not help you to decrypt .Gusau files, in some cases, you have a chance to recover your files, which were encrypted by ransomware. This is possible due to the use of the tools named ShadowExplorer and PhotoRec. An example of recovering encrypted files is given here.




















MACs: FC:AA:14:3F:E6:BD
—————————————-
STOPDecrypter v2.1.0.18
OS Microsoft Windows NT 6.1.7601 Service Pack 1, .NET Framework Version 4.0.30319.42000
—————————————-
No key for ID: wkuAyVxM6n0NuHQPreJyNYqGxpOszX3lGQkvhn5E (.gusau )
Unidentified ID: wkuAyVxM6n0NuHQPreJyNYqGxpOszX3lGQkvhn5E (.gusau )
MACs: FC:AA:14:3F:E6:BD
Decrypted 0 files, skipped 21
If STOPDecrypter does not help you to decrypt .Gusau files, then try ShadowExplorer and PhotoRec. An example of recovering encrypted files is given below:
http://www.myantispyware.com/2019/07/19/madek-file-extension-ransomware-virus-restore-decrypt-madek-files/#restore
Sir This Software is not working on Gusau. so please update.. my all data is lost.
Read my previous comment.