If you are reading this because you have received a email titled “Security Notice. Someone have access to you system.” and you are worried, you can stop worrying! This message is a new highly effective email scam. This email scam uses your email account name and old password to convince you that the hacker was able to hack your computer or other device, get full access to your email and use you webcam to record a video clip while you watch adult websites (porn). In order to keep this video from being sent to your contacts, the criminal demands a ransom payment in bitcoins.
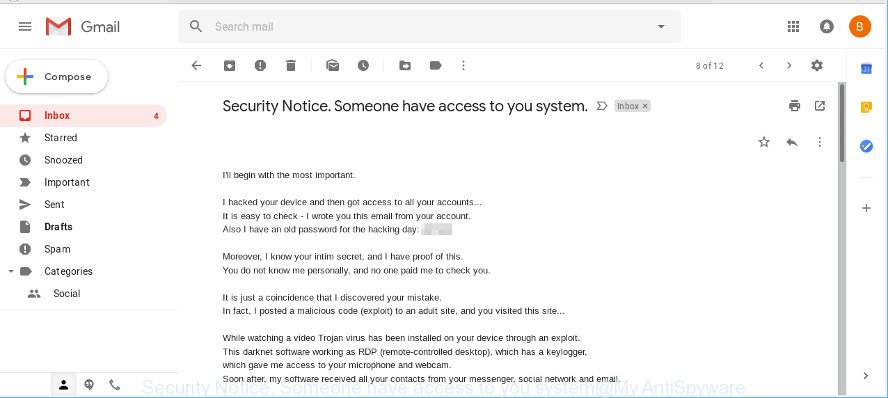
“Security Notice. Someone have access to you system.” Email Scam
Myantispyware.com continue to receive reports of fraudulent messages. There are variations in the wording of the email body, but all of these messages are basically the same. The scammers constantly switch up the body of scam emails in order to bypass spam filters.
Here below is an example. Recent version demands $700 ransom payment (Bitcoin Wallet Address is: 1FVuyuSN41aa3JN9sn8qkuD2PmaMEMHHnc).
Security Notice. Someone have access to you system. I'll begin with the most important. I hacked your device and then got access to all your accounts... Including ***. It is easy to check - I wrote you this email from your account. Also I have an old password for the hacking day: *** Moreover, I know your intim secret, and I have proof of this. You do not know me personally, and no one paid me to check you. It is just a coincidence that I discovered your mistake. In fact, I posted a malicious code (exploit) to an adult site, and you visited this site... While watching a video Trojan virus has been installed on your device through an exploit. This darknet software working as RDP (remote-controlled desktop), which has a keylogger, which gave me access to your microphone and webcam. Soon after, my software received all your contacts from your messenger, social network and email. At that moment I spent much more time than I should have. I studied your love life and created a good video series. The first part shows the video that you watched, and the second part shows the video clip taken from your webcam (you are doing inappropriate things). Honestly, I want to forget all the information about you and allow you to continue your daily life. And I will give you two suitable options. Both are easy to do. First option: you ignore this email. The second option: you pay me $700(USD). Let's look at 2 options in detail. The first option is to ignore this email. Let me tell you what happens if you choose this path. I will send your video to your contacts, including family members, colleagues, etc. This does not protect you from the humiliation that you and your family need to know when friends and family members know about your unpleasant details. The second option is to pay me. We will call this "privacy advice." Now let me tell you what happens if you choose this path. Your secret is your secret. I immediately destroy the video. You continue your life as if none of this has happened. Now you might think: "I'll call to police!" Undoubtedly, I have taken steps to ensure that this letter cannot be traced to me, and it will not remain aloof from the evidence of the destruction of your daily life. I don't want to steal all your savings. I just want to get compensation for my efforts that I put in to investigate you. Let us hope that you decide to create all this in full and pay me a fee for confidentiality. You make a Bitcoin payment (if you don't know how to do it, just enter "how to buy bitcoins" in Google search) Shipping amount: $700(USD). Getting Bitcoin Addresses: 1FVuyuSN41aa3JN9sn8qkuD2PmaMEMHHnc (This is sensitive, so copy and paste it carefully) Don't tell anyone what to use bitcoins for. The procedure for obtaining bitcoins can take several days, so do not wait. I have a spetial code in Trojan, and now I know that you have read this letter. You have 48 hours to pay. If I don't get BitCoins, I'll send your video to your contacts, including close relatives, co-workers, and so on. Start looking for the best excuse for friends and family before they all know. But if I get paid, I immediately delete the video. This is a one-time offer that is non-negotiable, so do not waste my and your time. Time is running out. Bye!
It’s important to understand that the email scam is social engineering tool. Scammers uses the database of emails and stolen passwords to increase trust and sent this email scam out to millions of people around the World in the hope of tricking a least a few people into sending the requested ransom. If the password emailed to you is one that you still use, then stop using it and change it right now!
What to do when you receive “Security Notice. Someone have access to you system.” email scam
Relax, Here are some easy steps which you need to follow after receiving these emails.
- Do not panic.
- We recommend you do not pay a ransom, because your payment will only increase attacks against you.
- Stop using the password that the scammer used in the email scam and change it. Make sure that you do not repeat passwords.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email scam to the FBI.
- Scan your computer for malware.
- Install an anti-phishing software.
- If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. It will help our team monitor the latest scams.
How to scan your computer for malware
There are not many good free malware removal tools with high detection ratio. The effectiveness of malware removal utilities depends on various factors, mostly on how often their virus/malware signatures DB are updated in order to effectively detect modern malicious software, ad-supported software, hijacker infections and other potentially unwanted apps. We recommend to run several applications, not just one. These applications that listed below will allow you remove all components of the ad supported software from your disk and Windows registry.
How to remove malware with Zemana Anti Malware (ZAM)
You can remove malware automatically with a help of Zemana Free. We advise this malware removal utility because it can easily detect and remove malware, browser hijackers, PUPs, adware with all their components such as folders, files and registry entries.
Visit the page linked below to download Zemana Anti-Malware. Save it on your Microsoft Windows desktop or in any other place.
165741 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
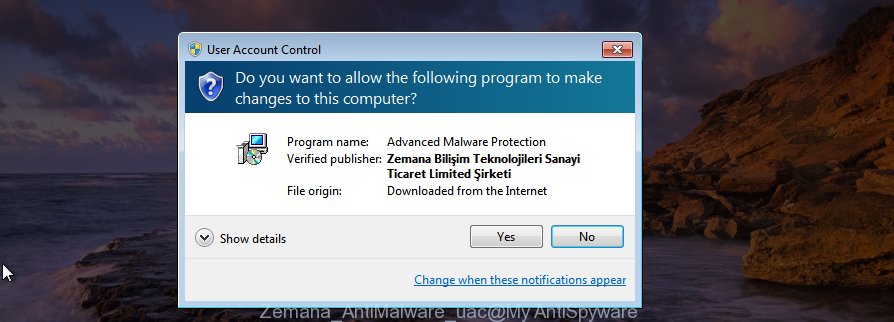
After the downloading process is finished, close all software and windows on your PC system. Double-click the install file called Zemana.AntiMalware.Setup. If the “User Account Control” prompt pops up as displayed in the following example, click the “Yes” button.
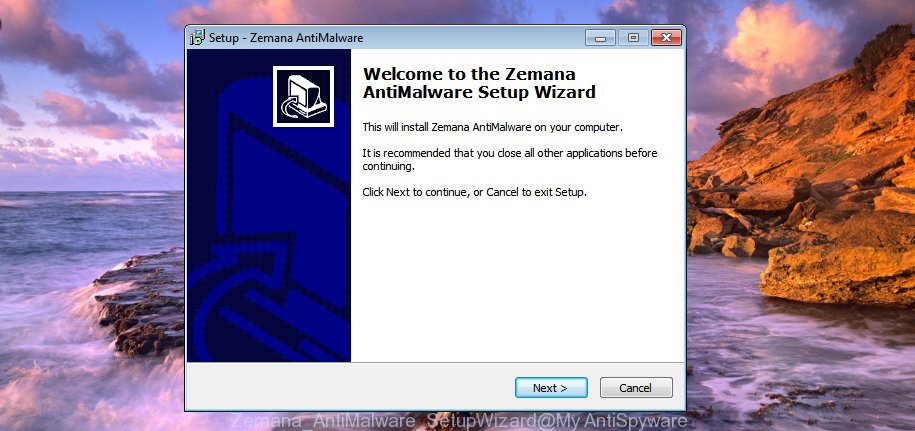
It will open the “Setup wizard” which will help you install Zemana Anti-Malware (ZAM) on your personal computer. Follow the prompts and do not make any changes to default settings.
Once installation is done successfully, Zemana Anti Malware (ZAM) will automatically start and you can see its main screen as shown below.

Now press the “Scan” button to perform a system scan for malware. A system scan can take anywhere from 5 to 30 minutes, depending on your PC system. While the Zemana Anti-Malware is scanning, you may see count of objects it has identified either as being malware.

Once Zemana has finished scanning, the results are displayed in the scan report. Review the scan results and then press “Next” button. The Zemana will delete malicious software and add threats to the Quarantine. After the process is finished, you may be prompted to reboot the system.
How to protect yourself from phishing web-sites
One of the worst things is the fact that you cannot stop all phishing web-sites using only built-in Windows capabilities. However, there is a program out that you can use to block phishing web-sites, malicious and misleading web-pages in any modern browsers including Google Chrome, Microsoft Internet Explorer, Mozilla Firefox and Microsoft Edge. It’s called Adguard and it works very well.
- Click the link below to download AdGuard. Save it to your Desktop.
Adguard download
27106 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
- After downloading it, start the downloaded file. You will see the “Setup Wizard” program window. Follow the prompts.
- After the install is finished, click “Skip” to close the setup program and use the default settings, or click “Get Started” to see an quick tutorial that will allow you get to know AdGuard better.
- In most cases, the default settings are enough and you don’t need to change anything. Each time, when you launch your computer, AdGuard will launch automatically and stop unwanted ads, block phishing web-sites, as well as other malicious or misleading pages. For an overview of all the features of the program, or to change its settings you can simply double-click on the icon called AdGuard, which can be found on your desktop.




















Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your acc: On moment of crack *** password: ***
You say: this is my, but old password!
Or: I will change my password at any time!
Of course! You will be right,
but the fact is that when you change the password, my malicious code every time saved a new one!
I’ve been watching you for a few months now.
But the fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence from e-mail and messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this, transfer the amount of $751 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1MrUDSrZiqD3ijxsBUPt2SukoFy534orP2
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Bye!
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your acc: On moment of crack [email protected] password: ***powerful****
You say: this is my, but old password!
Or: I will change my password at any time!
Of course! You will be right,
but the fact is that when you change the password, my malicious code every time saved a new one!
I’ve been watching you for a few months now.
But the fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence from e-mail and messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this, transfer the amount of $740 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1MrUDSrZiqD3ijxsBUPt2SukoFy534orP2
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Bye!
New bitcoin address (BTC Wallet) is: 15G9wyGRDssFXsfwEm1ihdJs2xabVPDu68
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account: At the time of hacking your account([email protected]) had this password: xxxxxxxxxxx
You can say: this is my, but old password!
Or: I can change my password at any time!
Of course! You will be right,
but the fact is that when you change the password, my malicious code every time saved a new one!
I’ve been watching you for a few months now.
But the fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence from e-mail and messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this, transfer the amount of $760 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 15G9wyGRDssFXsfwEm1ihdJs2xabVPDu68
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Bye!
Hello!
I have very bad news for you.
21/10/2018 – on this day I hacked your OS and got full access to your account **********@bigmir.net
So, you can change the password, yes… But my malware intercepts it every time.
How I made it:
In the software of the router, through which you went online, was a vulnerability.
I just hacked this router and placed my malicious code on it.
When you went online, my trojan was installed on the OS of your device.
After that, I made a full dump of your disk (I have all your address book, history of viewing sites, all files, phone numbers and addresses of all your contacts).
A month ago, I wanted to lock your device and ask for a not big amount of btc to unlock.
But I looked at the sites that you regularly visit, and I was shocked by what I saw!!!
I’m talk you about sites for adults.
I want to say – you are a BIG pervert. Your fantasy is shifted far away from the normal course!
And I got an idea….
I made a screenshot of the adult sites where you have fun (do you understand what it is about, huh?).
After that, I made a screenshot of your joys (using the camera of your device) and glued them together.
Turned out amazing! You are so spectacular!
I’m know that you would not like to show these screenshots to your friends, relatives or colleagues.
I think $706 is a very, very small amount for my silence.
Besides, I have been spying on you for so long, having spent a lot of time!
Pay ONLY in Bitcoins!
My BTC wallet: 1H1K8MfLEJgjCCfDEkTJmv9GJjD3XzEFGR
You do not know how to use bitcoins?
Enter a query in any search engine: “how to replenish btc wallet”.
It’s extremely easy
For this payment I give you two days (48 hours).
As soon as this letter is opened, the timer will work.
After payment, my virus and dirty screenshots with your enjoys will be self-destruct automatically.
If I do not receive from you the specified amount, then your device will be locked, and all your contacts will receive a screenshots with your “enjoys”.
I hope you understand your situation.
– Do not try to find and destroy my virus! (All your data, files and screenshots is already uploaded to a remote server)
– Do not try to contact me (this is not feasible, I sent you an email from your account)
– Various security services will not help you; formatting a disk or destroying a device will not help, since your data is already on a remote server.
P.S. You are not my single victim. so, I guarantee you that I will not disturb you again after payment!
This is the word of honor hacker
I also ask you to regularly update your antiviruses in the future. This way you will no longer fall into a similar situation.
Do not hold evil! I just do my job.
Have a nice day!
New bitcoin address (BTC Wallet): 1K7nnDHosR5czKZtuKT928YSxXXNSaDK6H
Hello!
I hacked your device, because I sent you this message from your account.
If you have already changed your password, my malware will be intercepts it every time.
You may not know me, and you are most likely wondering why you are receiving this email, right?
In fact, I posted a malicious program on adults (pornography) of some websites, and you know that you visited these websites to enjoy
(you know what I mean).
While you were watching video clips,
my trojan started working as a RDP (remote desktop) with a keylogger that gave me access to your screen as well as a webcam.
Immediately after this, my program gathered all your contacts from messenger, social networks, and also by e-mail.
What I’ve done?
I made a double screen video.
The first part shows the video you watched (you have good taste, yes … but strange for me and other normal people),
and the second part shows the recording of your webcam.
What should you do?
Well, I think $728 (USD dollars) is a fair price for our little secret.
You will make a bitcoin payment (if you don’t know, look for “how to buy bitcoins” on Google).
BTC Address: 1NcghPivgy9n5YkU4ferwBf9wmkNJHzUhm
(This is CASE sensitive, please copy and paste it)
Remarks:
You have 2 days (48 hours) to pay. (I have a special code, and at the moment I know that you have read this email).
If I don’t get bitcoins, I will send your video to all your contacts, including family members, colleagues, etc.
However, if I am paid, I will immediately destroy the video, and my trojan will be destruct someself.
If you want to get proof, answer “Yes!” and resend this letter to youself.
And I will definitely send your video to your any 16 contacts.
This is a non-negotiable offer, so please do not waste my personal and other people’s time by replying to this email.
Bye!
Hi, stranger!
I know the xxxxxx this is your password.
As you can see, I logged in with your account. And I wrote you this message from your account.
If you have already changed your password, my malware will be intercepts it every time.
You may not know me, and you are most likely wondering why you are receiving this email, right?
In fact, I posted a malicious program on adults (pornography) of some websites, and you know that you visited these websites to enjoy
(you know what I mean).
While you were watching video clips,
my trojan started working as a RDP (remote desktop) with a keylogger that gave me access to your screen as well as a webcam.
Immediately after this, my program gathered all your contacts from messenger, social networks, and also by e-mail.
What I’ve done?
I made a double screen video.
The first part shows the video you watched (you have good taste, yes … but strange for me and other normal people),
and the second part shows the recording of your webcam.
What should you do?
Well, I think $755 (USD dollars) is a fair price for our little secret.
You will make a bitcoin payment (if you don’t know, look for “how to buy bitcoins” on Google).
BTC Address: 1Q2yu5awJd1Z3UJVw2VckeGoLs6TfSHFQR
(This is CASE sensitive, please copy and paste it)
Remarks:
You have 2 days (48 hours) to pay. (I have a special code, and at the moment I know that you have read this email).
If I don’t get bitcoins, I will send your video to all your contacts, including family members, colleagues, etc.
However, if I am paid, I will immediately destroy the video, and my trojan will be destruct someself.
If you want to get proof, answer “Yes!” and resend this letter to youself.
And I will definitely send your video to your any 10 contacts.
This is a non-negotiable offer, so please do not waste my personal and other people’s time by replying to this email.
Bye!