 SafePcAv is a rogue antispyware program that installed through the use of trojans that come from fake online antispyware scanners or misleading websites that ask users to install a fake codec or a flash update needed to watch a video online. Once the trojan is started, it will download and install SafePcAv onto your computer and register it in the Windows registry to run automatically when you logon into Windows.
SafePcAv is a rogue antispyware program that installed through the use of trojans that come from fake online antispyware scanners or misleading websites that ask users to install a fake codec or a flash update needed to watch a video online. Once the trojan is started, it will download and install SafePcAv onto your computer and register it in the Windows registry to run automatically when you logon into Windows.
When running, SafePcAv will run a fake system scan. It states that your computer is infected numerous infections and that you should purchase the program to remove them. Of course, this is nothing more but a scam, because SafePcAv identifies harmless files as dangerous infections. So, the scan results are fake and you may easily ignore all that the rogue shows you.
What is more, the same trojan that installs SafePcAv will also download and install two another trojans. First trojan is a FakeAlert trojan that once running will display a lot of nag screens and fake security notifications from Windows task bar. Second trojan is a TDSS trojan that may redirect search results in Google, Yahoo, MSN, block an access to security websites and much more. Last but not least, SafePcAv will also hijack Internet Explorer so that it will randomly show a warning page that stats that the website you are visiting is infected.
As you can see, SafePcAv is a scam. It designed with one purpose to scare you into purchasing so-called full version of the program! Use the removal guide below to remove SafePcAv and any associated malware from your computer for free.
More screen shoots of SafePcAv
Symptoms in a HijackThis Log
O4 – HKCU\..\Run: [
Spyware can do the following:
1. gather information about user habits of use of the Internet, what sites are visited most frequently (known as “tracking software”);
2. record keystrokes (keyloggers) and make a screenshots (screen scraper) and send collected data to the creator of the spyware;
3. remotely control user computer (remote control software) – backdoor, botnets, droneware;
4. download and run on user computer an additional malware;
5. analyze the state of security systems, scan an open ports, and look for vulnerabilities to crack passwords;
Use the following instructions to remove SafePcAv (Uninstall instructions)
Download TDSSKiller from here and unzip to your desktop.
Open TDSSKiller folder and double click the TDSSKiller icon. When the scan is finished, you will see window similar to the one below.
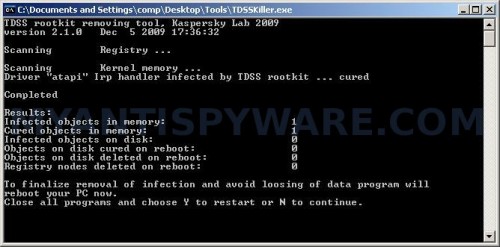
TDSS trojan remover
Close all programs and press Y key.
Download MalwareBytes Anti-malware (MBAM). Close all programs and Windows on your computer.
Double Click mbam-setup.exe to install the application. When the installation begins, keep following the prompts in order to continue with the installation process. Do not make any changes to default settings and when the program has finished installing, make sure a checkmark is placed next to Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware, then click Finish.
If an update is found, it will download and install the latest version.
Once the program has loaded you will see window similar to the one below.
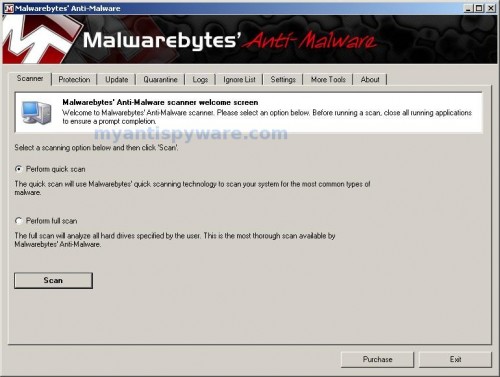
Malwarebytes Anti-Malware Window
Select Perform Quick Scan, then click Scan, it will start scanning your computer for SafePcAv infection. This procedure can take some time, so please be patient.
When the scan is complete, click OK, then Show Results to view the results. You will see a list of infected items similar as shown below. Note: list of infected items may be different than what is shown in the image below.
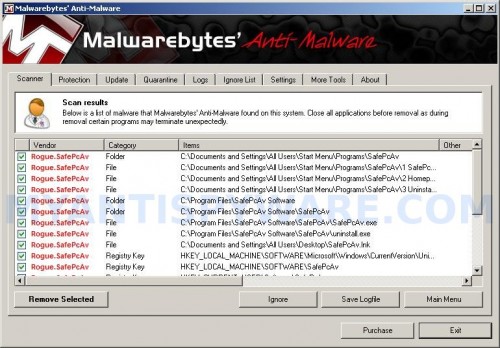
Malwarebytes Anti-malware, list of infected items
Make sure that everything is checked, and click Remove Selected for start SafePcAv removal process. When disinfection is completed, a log will open in Notepad and you may be prompted to Restart.
Note: if you need help with the instructions, then post your questions in our Spyware Removal forum.
SafePcAv creates the following files and folders
C:\Documents and Settings\All Users\Start Menu\Programs\SafePcAv
C:\Program Files\SafePcAv Software
C:\Program Files\SafePcAv Software\SafePcAv
C:\Program Files\SafePcAv Software\SafePcAv\SafePcAv.exe
C:\WINDOWS\system32\
Spyware can do the following:
1. gather information about user habits of use of the Internet, what sites are visited most frequently (known as “tracking software”);
2. record keystrokes (keyloggers) and make a screenshots (screen scraper) and send collected data to the creator of the spyware;
3. remotely control user computer (remote control software) – backdoor, botnets, droneware;
4. download and run on user computer an additional malware;
5. analyze the state of security systems, scan an open ports, and look for vulnerabilities to crack passwords;
C:\Documents and Settings\All Users\Start Menu\Programs\SafePcAv\1 SafePcAv.lnk
C:\Documents and Settings\All Users\Start Menu\Programs\SafePcAv\2 Homepage.lnk
C:\Documents and Settings\All Users\Start Menu\Programs\SafePcAv\3 Uninstall.lnk
C:\Program Files\SafePcAv Software\SafePcAv\uninstall.exe
C:\Documents and Settings\All Users\Desktop\SafePcAv.lnk
SafePcAv creates the following registry keys and values
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SafePcAv
HKEY_LOCAL_MACHINE\SOFTWARE\SafePcAv
HKEY_CURRENT_USER\Software\SafePcAv
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\
Spyware software are surreptitiously installed on user`s computer to collect information about computer’s configuration, user`s private information, user’s activity without his consent. Spyware may also change Windows settings, download and install other malicious programs without the user’s knowledge.
.exe














