What is PLAY ransomware?
PLAY is a variant of ransomware which adds .PLAY extension to the encrypted file names. PLAY is a ransomware that infects Windows users, encrypts their files, deletes any shadow copies of these files, and demands a ransom for a decryption key. After encrypting the files, the ransomware then drops the ransomnote into a file (called “ReadMe.txt”), which requests that the victim contact the attacker via email to pay the ransom, in exchange for the decryption key.
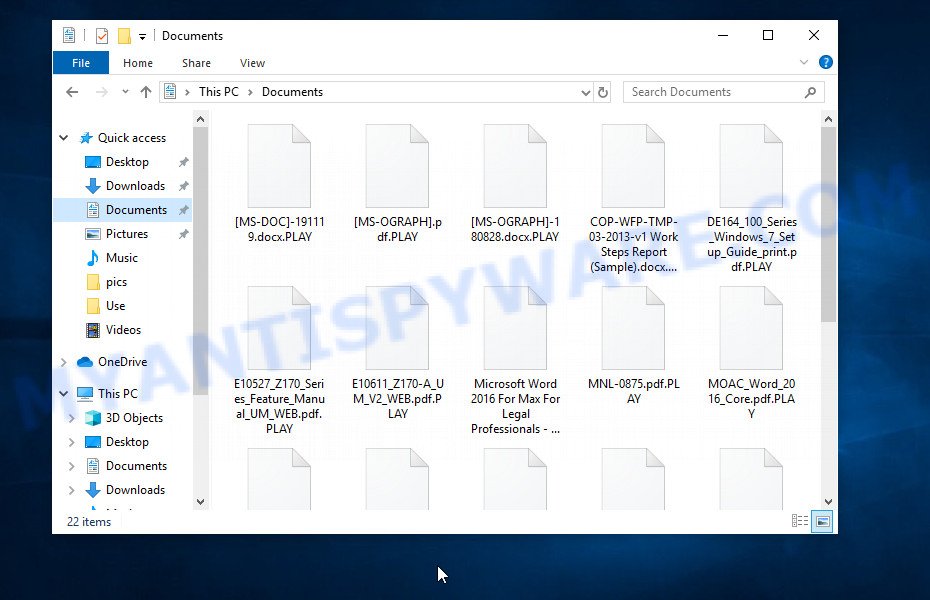
After encrypting the files, the ransomware appends the .PLAY extension to their filenames:
QUICK LINKS
PLAY ransomware in detail
PLAY ransomware is designed to encrypt files located on the victim’s computer, and then extort money to decrypt them. It sneaks into the system without any visible symptoms, which is why users notice that their computer is infected too late, when the files are already encrypted. Typically, ransomware like PLAY can infect a computer when a user runs and installs an infected program as well as cracked games, freeware, key generators, fake Windows/Chrome/Edge updates and other similar software.
Each file affected by ransomware is renamed so that the extension “.PLAY” is added to its old name on the right. This means the following, if the file was named “document.docx”, then after it is encrypted, it will be called “document.docx.PLAY”. Every file on the victim’s computer becomes the target of the PLAY virus. Whether the file is on an internal drive or network storage, it will be encrypted. Thus, the following types of files can be encrypted:
.re4, .xld, .rim, .ysp, .ff, .iwi, .mef, .js, .w3x, .wav, .py, .rwl, .flv, .wgz, .x3d, .sum, .odp, .xls, .bay, .xx, .wp7, .p12, .docx, .lvl, .xmmap, .xpm, .3dm, .ybk, .pst, .wpb, .hkdb, .nrw, .webp, .zip, .iwd, .wb2, .fos, .ibank, .menu, .t12, .bkp, .vtf, .wbz, .itl, .vpp_pc, .png, .snx, .sidd, .itm, .map, .gho, .wpa, .srf, .xmind, .upk, .1st, .x, .der, .3ds, .dxg, .wotreplay, .wpd, .mcmeta, .wp, .odc, .vdf, .wsh, .bc7, .raf, .rar, .wmo, .wot, .p7b, .sidn, .vcf, .slm, .yml, .qic, .pfx, .wp5, .mov, .mdbackup, .blob, .pdf, .raw, .csv, .cer, .dazip, .x3f, .txt, .mpqge, .r3d, .bsa, .xxx, .xyp, .arch00, .desc, .ntl, .pem, .odb, .cas, .wps, .wps, .bar, .itdb, .icxs, .asset, .sie, .xyw, .xbplate, .tor, .pdd, .y, .wm, .big, .0, .m3u, .xml, .doc, .arw, .crt, .wp6, .xlsx, .z3d, .zabw, .rgss3a, .hkx, .wdb, .xlk, .forge, .wpt, .jpg, .xlgc, .epk, .ods, .wpe, .odm, .webdoc, .bik, .xdb, .fpk, .mrwref, .p7c, .wbm, .xbdoc, .dmp, .kdc, .zdb, .ai, .wdp, .wire, .qdf, .wsc, .kf, .m2, .sql, .wma, .jpe, .apk, .litemod, .jpeg, .wn, .crw, .syncdb, .dba, .sav, .wma, .odt, .pkpass, .ptx, .xdl, .wri, .1, .psk, .xls, .ppt, .wbk, .avi, .db0, .wsd, .sr2, .wmv, .ltx, .xlsx, .d3dbsp, .orf, .pef, .m4a, .mdf, .z, .lbf, .fsh, .t13, .accdb
Encrypted files are locked, i.e. their contents cannot be accessed in any way. Renaming the files and changing their extension will not help unlock these files. In directories where there are encrypted files, the ransomware drops files called “ReadMe.txt”. These files contain a message from the ransomware authors. The content of all files with this name is the same and does not depend on which directory the file is in.
Typically, the message left by the attackers contains various information, such as the type of encryption, the amount of the ransom, the method of paying the ransom, and so on. But in this case, there is nothing of the kind, the message contains only the ransomware name (PLAY) and the attackers’ e-mail address. This address may change, depending on the variant of the ransomware.
Text presented in the ransom demand message (ReadMe.txt):
PLAY
boitelswaniruxl@gmx.com
We advise you not to pay the ransom, as paying the ransom supports attacks against victims in the future. In addition, most often the victims, even after paying the ransom, do not receive the tools to decrypt their files.
The only way to prevent further encryption is to remove the PLAY ransomware from your computer. But, it is important to emphasize that removing the virus does not restore already encrypted files. There are several alternative methods that can help restore files in some cases, but the easiest is to restore files from backups (of course, if there are any).
Therefore, we highly recommend that you back up important files and store them in multiple locations, both on connected storage devices and in cloud storage. This will ensure maximum data security.
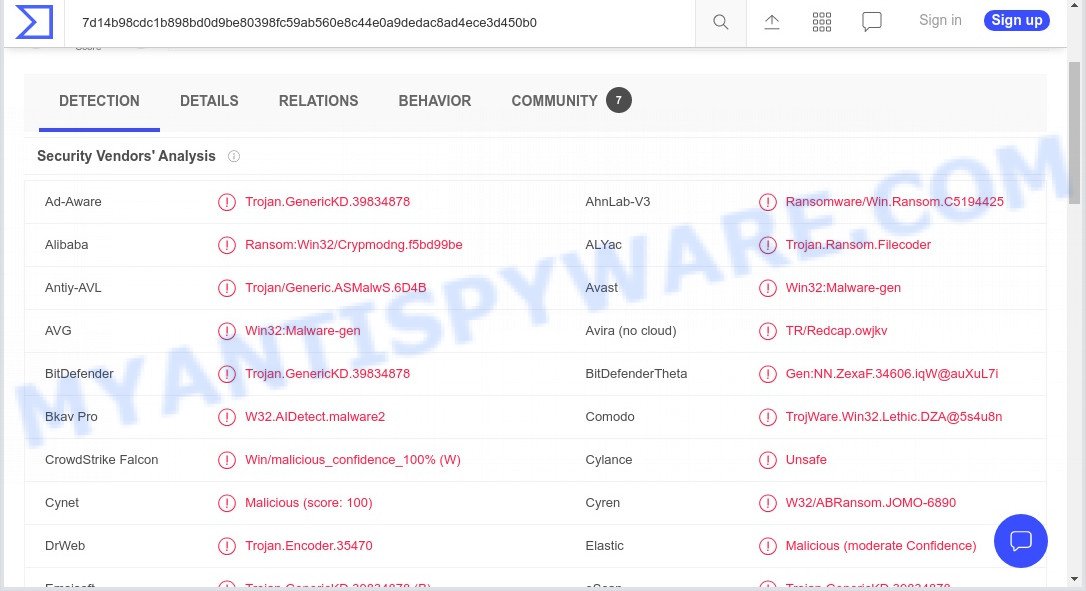
49 security vendors flagged the PLAY ransomware and warns users about running this program as it could harm the computers:
Threat Summary
| Name | PLAY ransomware |
| Type | Crypto malware, File locker, Ransomware, Crypto virus, Filecoder |
| Encrypted files extension | .PLAY |
| Ransom note | ReadMe.txt |
| CyberCriminals Contacts | boitelswaniruxl@gmx.com, teilightomemaucd@gmx.com |
| Detection | Ransom:Win32/Crypmodng.f5bd99be, TR/Redcap.owjkv, TrojWare.Win32.Lethic.DZA@5s4u8n, W32/ABRansom.JOMO-6890, W32/Filecoder.NHQDTEZ!tr.ransom, Ransomware/Win.Ransom.C5194425, Trojan.Encoder.35470, A Variant Of Win32/Filecoder.OLN, Ransom.FileCryptor, RDN/Ransom, Trojan.Crypmodng.by |
| Symptoms | Unable to open documents, photos and music. Your files now have a new extension. Files called such as ”, ‘#_README_#’, ‘_DECRYPT_’ or ‘recover’ in each folder with at least one encrypted file.. You have received instructions for paying the ransom. |
| Distribution ways | Unsolicited emails that are used to deliver malicious software. Drive-by downloads from a compromised web-site. Social media, such as web-based instant messaging applications. Remote desktop protocol (RDP) hacking. |
| Removal | PLAY removal guide |
| Recovery | Recovery Guide |
How to remove PLAY ransomware, Recover encrypted files
If your files were encrypted, then you first need to remove the PLAY ransomware, and then proceed with file recovery. Both the ransomware removal process and the file recovery process will take a long time, so don’t believe the magic instructions that say it can be done very quickly. We strongly recommend that even if for some reason one of the methods below does not suit you, try another and try them all. Perhaps one of them will help you. Feel free to ask questions in the comments below. And finally, before proceeding with the instructions, we advise you to carefully read it, and then print it or open it on a tablet or smartphone so that it is always at hand.
Remove PLAY ransomware virus
You first need to delete PLAY-related files and registry entries before proceeding with the recovery of encrypted files. This must be done since otherwise the ransomware may re-encrypt the restored files.
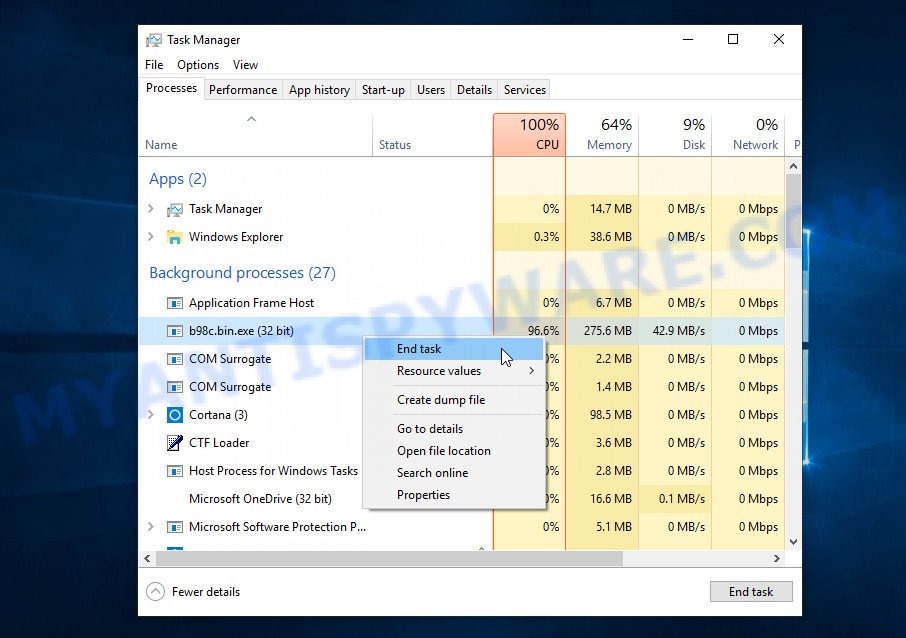
Kill malicious processes
Press CTRL, ALT, DEL keys together.
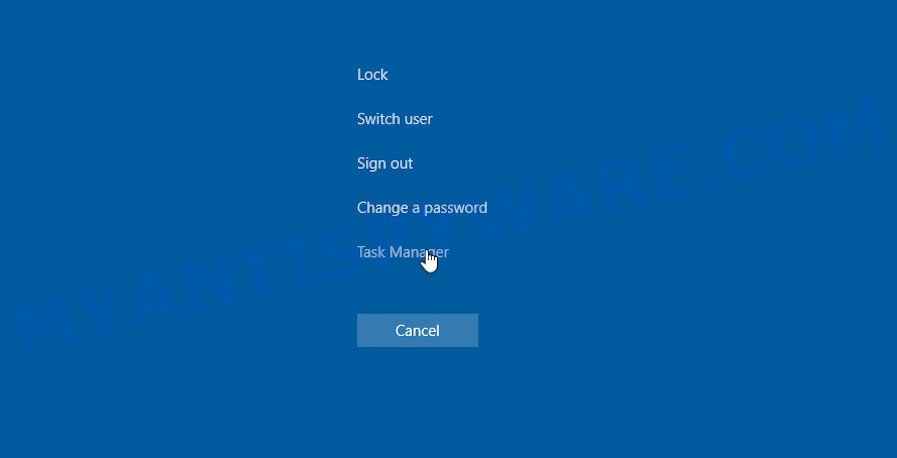
Click Task Manager. Select the “Processes” tab, look for something suspicious that is the PLAY ransomware then right-click it and select “End Task” or “End Process” option. If your Task Manager does not open or the Windows reports “Task manager has been disabled by your administrator”, then follow the guide: How to Fix Task manager has been disabled by your administrator.
Scan computer for malware
MalwareBytes is a malware removal tool that can be used to remove spyware, trojans, worms, adware, malware, ransomware and other security threats. This program is one of the most efficient anti-malware tools. It helps in ransomware removal and and defends all other types of malware. One of the biggest advantages of using MalwareBytes Anti Malware is that is easy to use and is free. Also, it constantly keeps updating its virus/malware signatures DB. Let’s see how to install and scan your computer with MalwareBytes in order to remove PLAY ransomware from the computer.
Installing the MalwareBytes is simple. First you’ll need to download it from the following link. Save it to your Desktop.
327714 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
When the download is complete, close all apps and windows on your device. Open a directory in which you saved it. Double-click on the icon that’s called MBSetup as displayed in the following example.
![]()
When the installation begins, you will see the Setup wizard which will help you setup Malwarebytes on your computer.
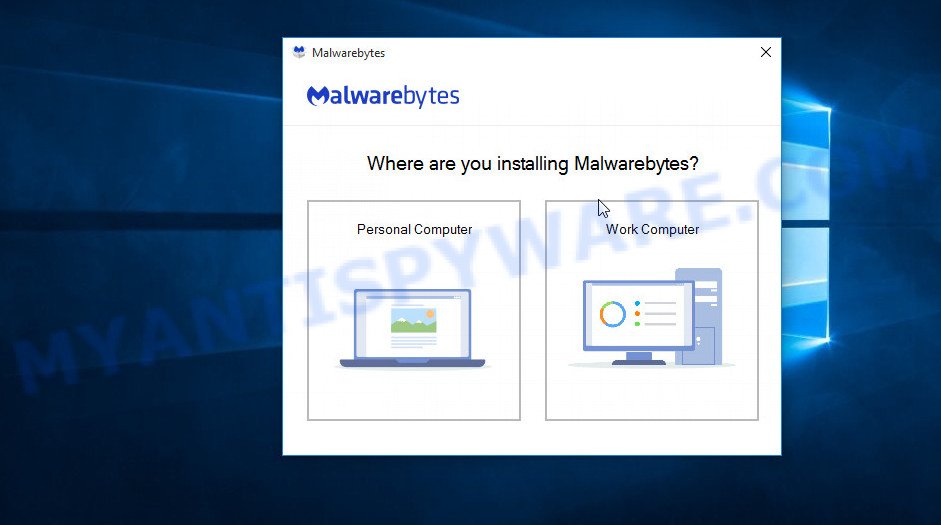
Once the installation is done, you will see window similar to the one below.
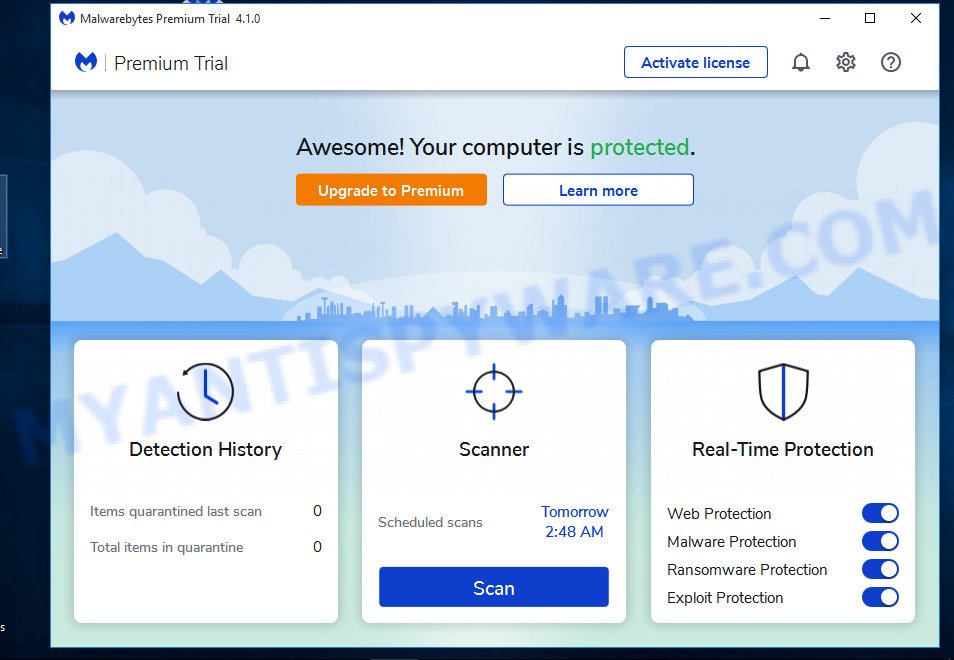
Now click the “Scan” button to scan your computer for the PLAY ransomware, spyware, worms, trojans and other malware. This process can take some time, so please be patient. When a threat is detected, the number of the security threats will change accordingly.
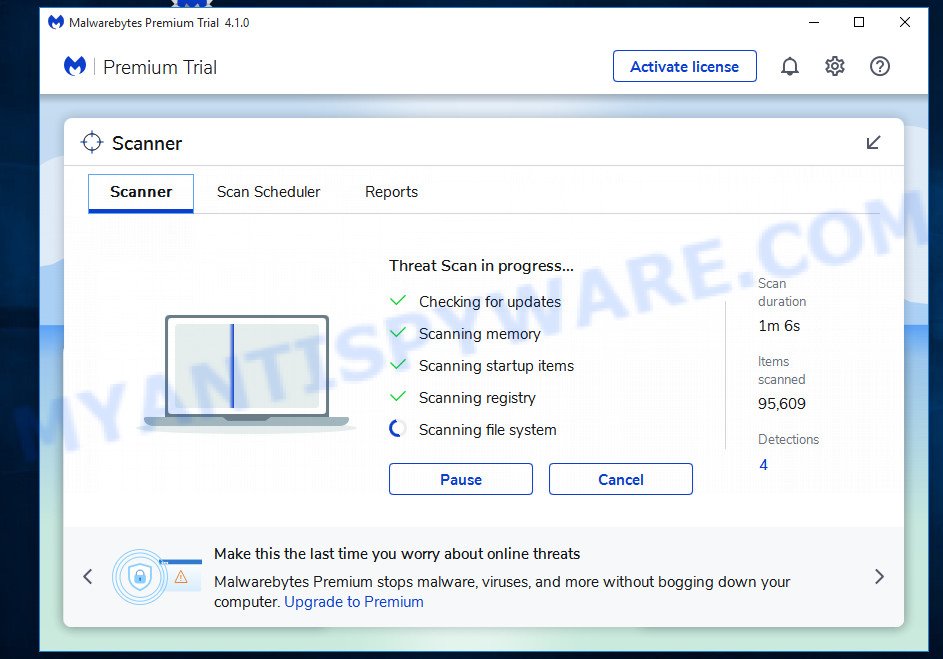
When the scan is done, MalwareBytes will show a list of malware found on the computer. Review the list and then click “Quarantine” button.
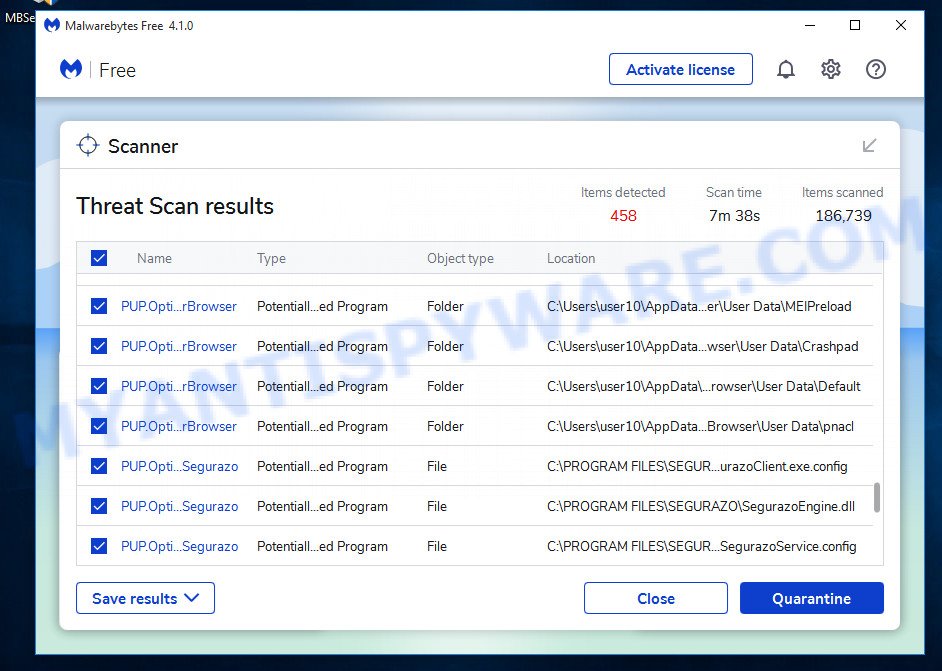
Malwarebytes will now move the selected threats to the program’s quarantine. Once disinfection is complete, you may be prompted to reboot your computer.
In order to be 100% sure that the computer no longer has the PLAY malware, we recommend using the Kaspersky virus removal tool (KVRT). This tool, as its name suggests, is created by the Kaspersky lab and uses the core of the Kaspersky Antivirus. Unlike the Kaspersky Antivirus, KVRT has a smaller size and, most importantly, it can work together with an already installed antivirus software. This utility has great capabilities and therefore we suggest using KVRT in the last turn to be sure that the PLAY ransomware virus has been removed.
Download KVRT on your personal computer from the following link.
129488 downloads
Author: Kaspersky® lab
Category: Security tools
Update: March 5, 2018
After downloading is finished, double-click on the KVRT icon. Once initialization procedure is complete, you’ll see the Kaspersky virus removal tool screen like below.
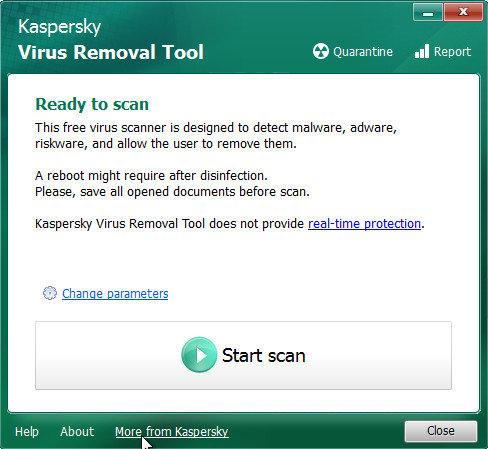
Click Change Parameters and set a check near all your drives. Press OK to close the Parameters window. Next click Start scan button to perform a system scan for the PLAY ransomware. A scan may take anywhere from 10 to 30 minutes, depending on the number of files on your PC and the speed of your PC. When a threat is found, the number of the security threats will change accordingly.
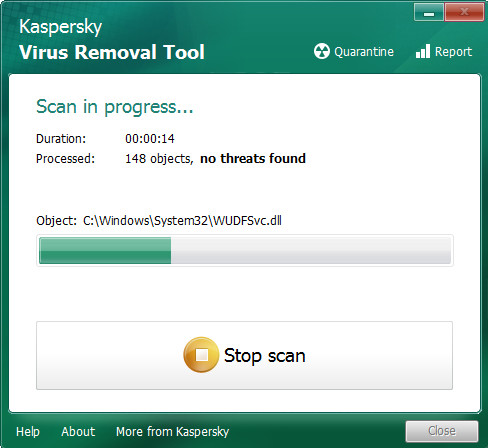
When Kaspersky virus removal tool is finished scanning your device, it will prepare a list of found threats similar to the one below.
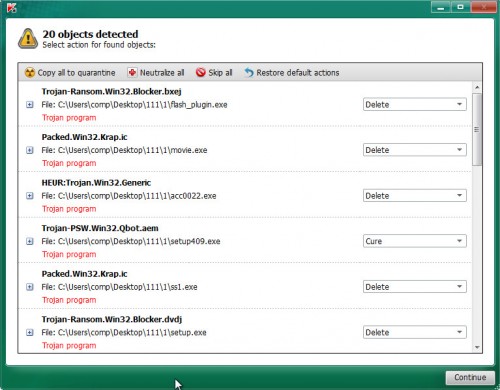
Once you have selected what you wish to delete from your computer press on Continue to begin a cleaning task.
Recover encrypted files
If your files are encrypted, then the only option to recover encrypted files is to use alternative methods. There are several alternative methods that may allow you to recover encrypted files. These methods do not use decryption, so there is no need for a key and a decryptor. Before you begin, you must be 100% sure that there are no active ransomware on your computer. So if you haven’t already scanned your computer for ransomware, do it now with free malware removal tools or go back to step 1 above.
Restore encrypted files using Shadow Explorer
Although Play ransomware tries to delete Shadow copies of files, it fails in some cases. Therefore, first of all, try to restore files from Shadow copies. A free tool named ShadowExplorer is a simple solution to use the ‘Previous Versions’ feature of MS Windows 11 (10, 8, 7 , Vista). You can recover your documents, photos, and music encrypted by PLAY ransomware from Shadow Copies for free.
Installing the ShadowExplorer is simple. First you will need to download ShadowExplorer on your system from the link below.
440038 downloads
Author: ShadowExplorer.com
Category: Security tools
Update: September 15, 2019
After the download is done, extract the saved file to a directory on your personal computer. This will create the necessary files as on the image below.
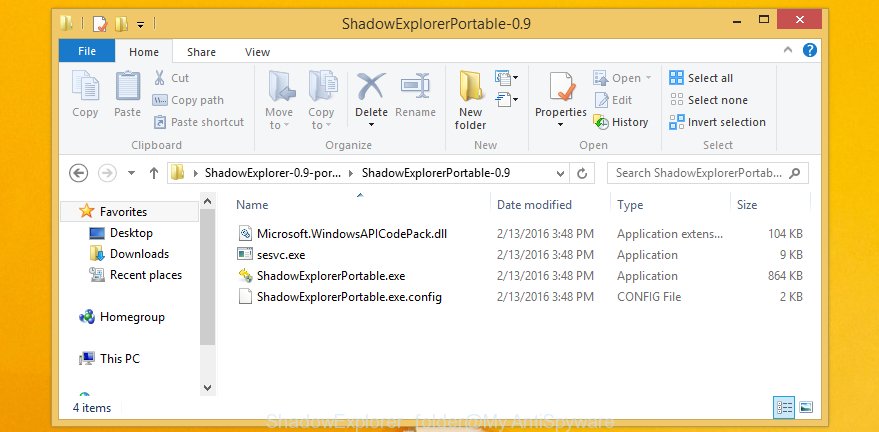
Run the ShadowExplorerPortable program. Now choose the date (2) that you want to restore from and the drive (1) you wish to recover files (folders) from such as the one below.
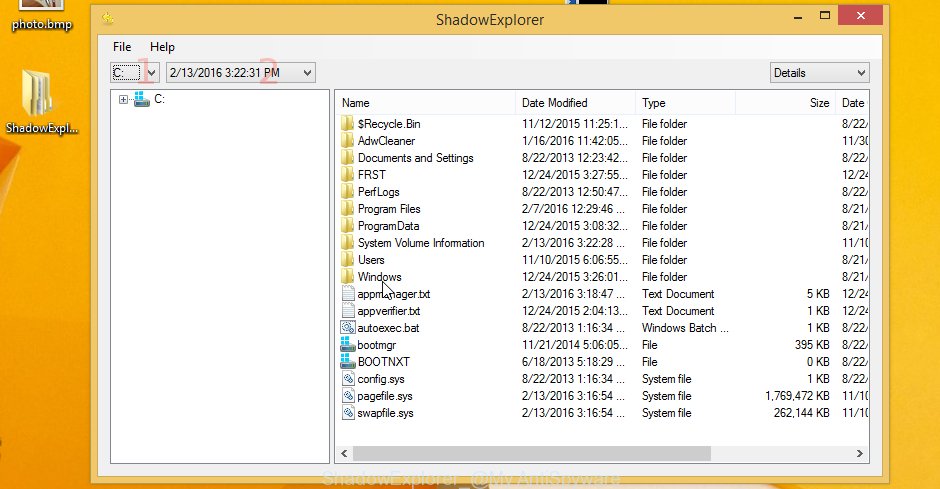
On right panel navigate to the file (folder) you want to recover. Right-click to the file or folder and click the Export button like below.

And finally, specify a directory (your Desktop) to save the shadow copy of encrypted file and click ‘OK’ button.
This video step-by-step guide will demonstrate How to recover encrypted files using Shadow Explorer.
Recover encrypted files with PhotoRec
There is another way to recover encrypted files. This method is based on the use of data recovery tools. We recommend using a tool called PhotoRec. It has all the necessary features and is completely free.
Download PhotoRec by clicking on the following link.
Once downloading is complete, open a directory in which you saved it. Right click to testdisk-7.0.win and select Extract all. Follow the prompts. Next please open the testdisk-7.0 folder as on the image below.

Double click on qphotorec_win to run PhotoRec for MS Windows. It will open a screen as displayed in the figure below.
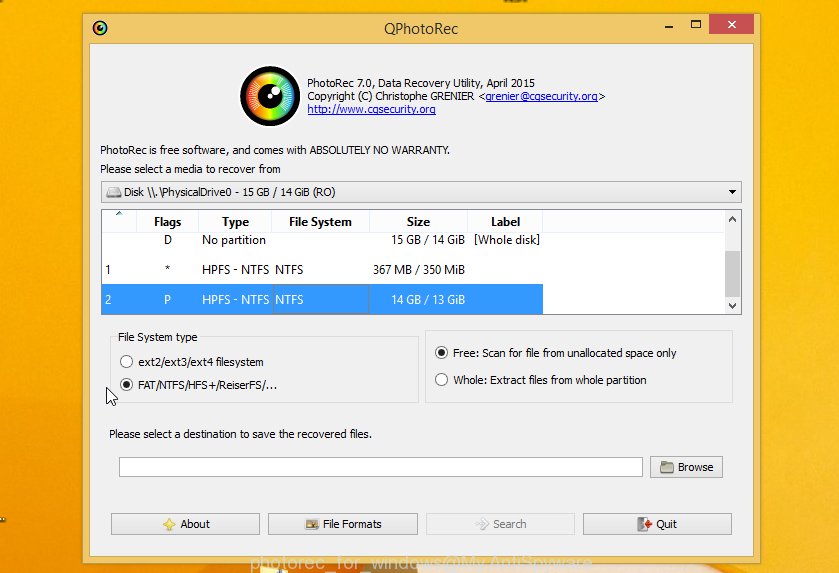
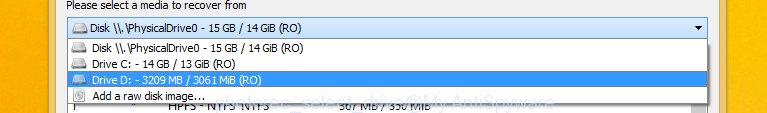
Select a drive to recover like below.
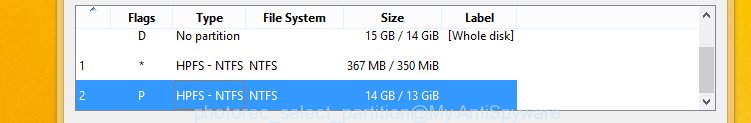
You will see a list of available partitions. Select a partition that holds encrypted files as shown below.
Press File Formats button and specify file types to recover. You can to enable or disable the restore of certain file types. When this is finished, press OK button.
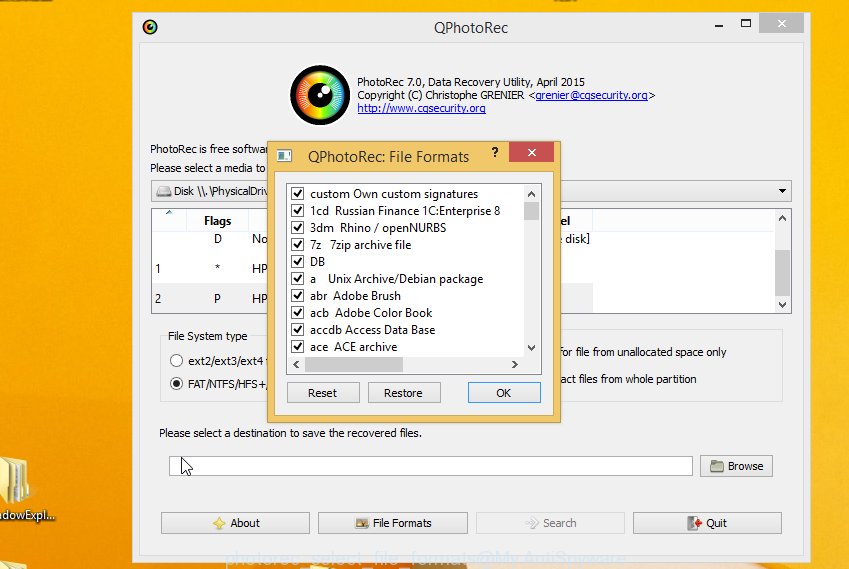
Next, press Browse button to choose where restored personal files should be written, then press Search. We strongly recommend that you use an external device to save the restored files!
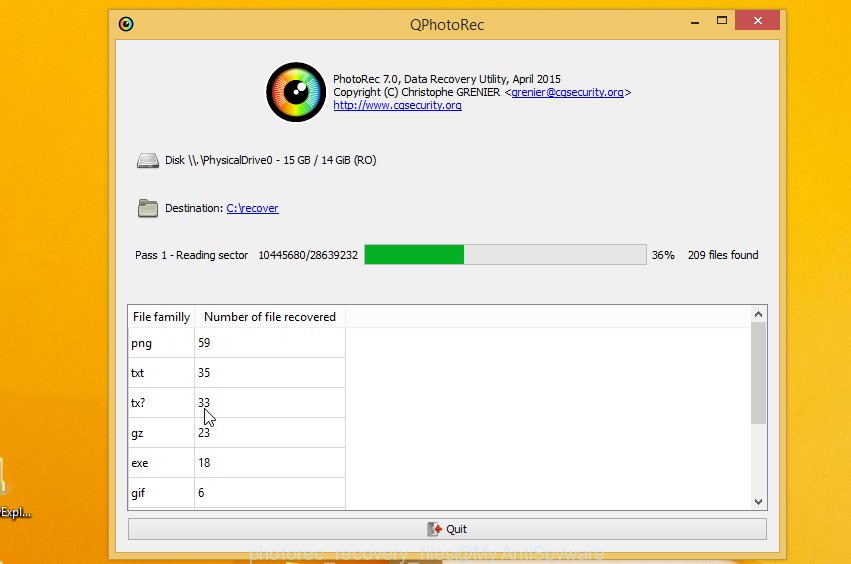
Count of recovered files is updated in real time. All restored personal files are written in a folder that you have chosen on the previous step. You can to access the files even if the restore process is not finished.
When the restore is finished, press on Quit button. Next, open the directory where restored documents, photos and music are stored. You will see a contents as displayed below.
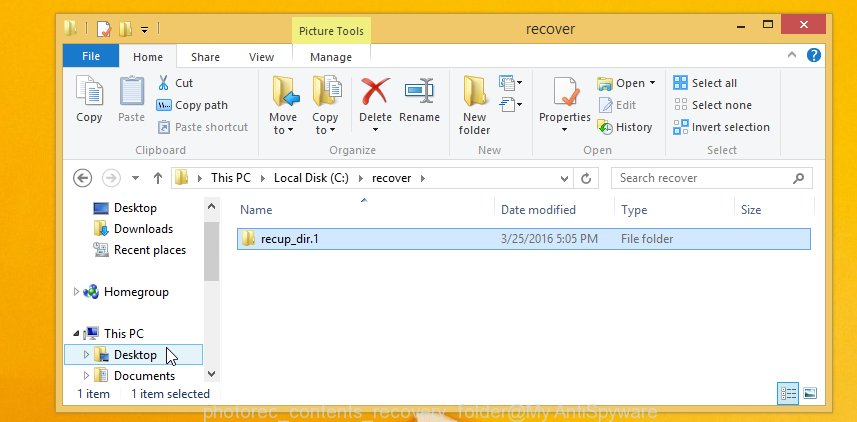
All recovered documents, photos and music are written in recup_dir.1, recup_dir.2 … sub-directories. If you are searching for a specific file, then you can to sort your recovered files by extension and/or date/time.
This video step-by-step guide will demonstrate How to recover encrypted files using PhotoRec.
Protect your PC from PLAY ransomware
Most antivirus programs already have ransomware protection built in. Therefore, if your computer does not have an antivirus program, be sure to install it. For additional protection, use HitmanPro.Alert. All in all, HitmanPro.Alert is a fantastic utility to protect your computer from any kind of ransomware. When ransomware is detected, HitmanPro.Alert automatically neutralizes malware and restores encrypted files. HitmanPro.Alert is compatible with all versions of MS Windows from Windows XP to Windows 11.
First, click the following link, then click the ‘Download’ button in order to download the latest version of HitmanPro.Alert.
After the downloading process is complete, open the file location. You will see an icon like below.

Double click the HitmanPro.Alert desktop icon. After the tool is started, you’ll be displayed a window where you can choose a level of protection, as displayed below.

Now click the Install button to activate the protection.
Finish words
This guide has been created to help all victims of the PLAY ransomware. We tried to answer the following questions: how to remove ransomware; how to recover encrypted files. We hope the information provided in this guide has helped you.
If you have questions, then write to us, leaving a comment below. If you need more help with PLAY related issues, go to here.



















