Is the email a Scam?
As you may have noticed, I sent you an email from your email account is a sextortion SCAM. Sextortion is a type of scam where attackers send an email to the victim claiming that they have obtained sensitive information, such as intimate photos or videos, and threatening to release this information unless the victim pays a ransom. However, the attackers does not actually have access to the sensitive information, and the threat is empty. The goal of the attackers is to trick the victim into paying the ransom, often by instilling fear and panic in the victim.
It is important to never give in to sextortion demands, delete the fake email, and to seek help from law enforcement if you are a victim of this crime.
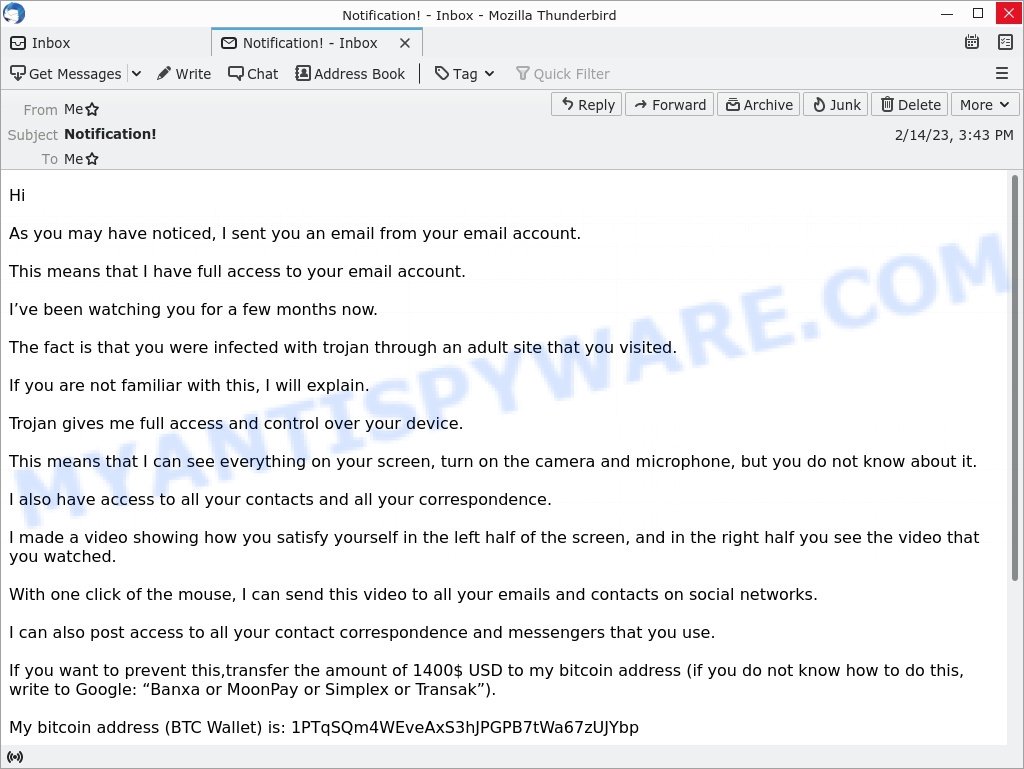
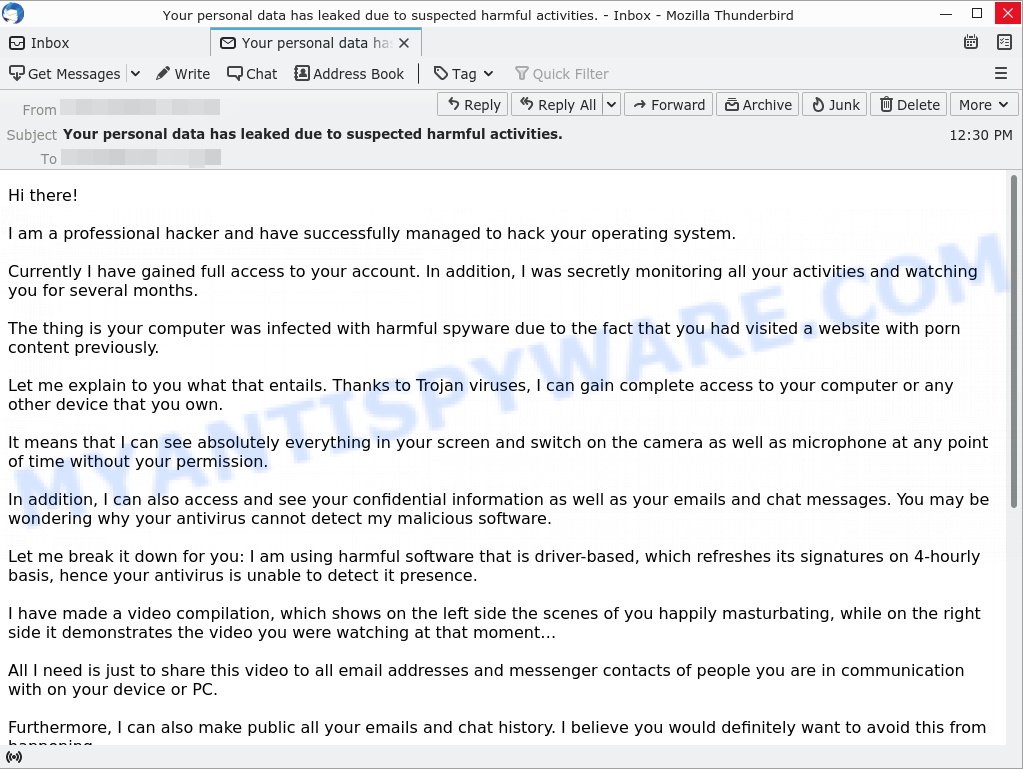
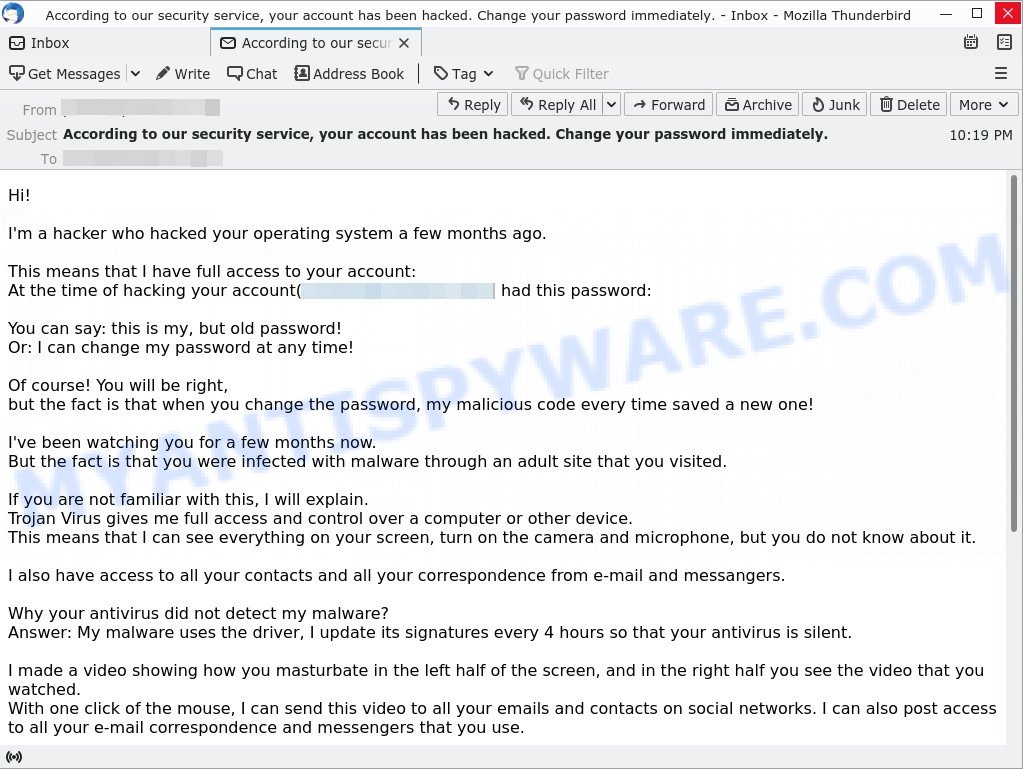
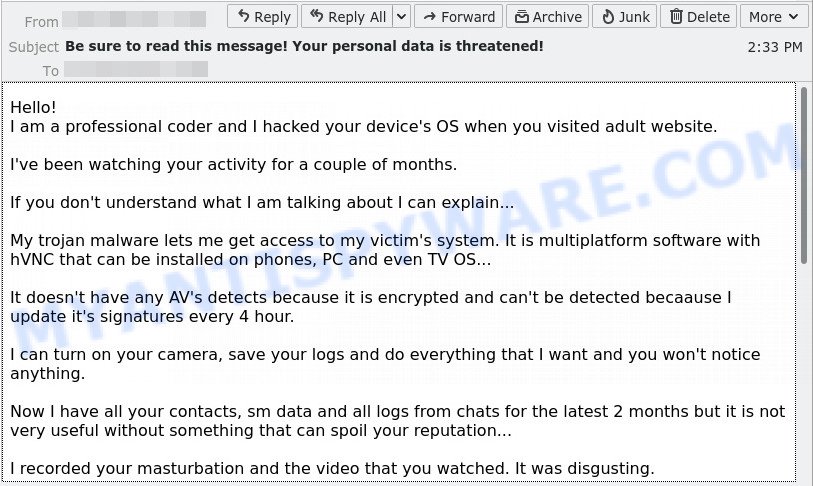
Here’s an example of the “I sent you an email from your account” Scam Email:
QUICK LINKS
- Is the email a Scam?
- I sent you an email from your account Scam Explained
- How the scam works
- Should you pay?
- What to do when you receive a sextortion email?
- Report a Scam
I sent you an email from your account Scam Explained
This email is a scam, and the threat of having access to your email and video recording of you is a lie. The email is designed to scare and extort money from the recipient.
One of the most obvious signs of this being a scam is the fact that the email begins with “Hi” and does not address the recipient by name. Additionally, the language used in the email is unprofessional and uses poor grammar.
The claim that the sender has been watching the recipient and has access to their email account and device is a lie. It is highly unlikely that someone would be able to gain full access to another person’s device without their knowledge or consent.
The email’s threat to release a video of the recipient to their contacts and social networks is also a lie. Even if the scammer did have a video, it is unlikely that they would be able to distribute it to the recipient’s entire contact list and social networks with just one click.
The request for payment via Bitcoin is another red flag. It is difficult to trace Bitcoin transactions, making it a preferred method for scammers.
In summary, if you receive an email like this, do not respond or send any money. Instead, mark the email as spam and delete it.
A typical “I sent you an email from your email account” scam email reads as follows:
Hi
As you may have noticed, I sent you an email from your email account.
This means that I have full access to your email account.
I’ve been watching you for a few months now.
The fact is that you were infected with trojan through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan gives me full access and control over your device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your contact correspondence and messengers that you use.
If you want to prevent this,transfer the amount of 1400$ USD to my bitcoin address (if you do not know how to do this, write to Google: “Banxa or MoonPay or Simplex or Transak”).
My bitcoin address (BTC Wallet) is: 1PTqSQm4WEveAxS3hJPGPB7tWa67zUJYbp
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regard
Many ask us questions like: “i received an email from my own email address demanding money”, “trojan virus email from own account”, “email from my own email address demanding bitcoin”, “email from me to me that i didn’t send”, “i got an email from my own email saying i was hacked”, “threatening email from my own email address”, “you have an outstanding payment blackmail email”, “sextortion email from my own account”. Here are some answers to the questions:
- If you received an email from your own email address demanding money or threatening to release sensitive information, it is most likely a scam. Do not send any money or respond to the email. You can mark the email as spam or report it to your email provider.
- If you received an email that claims your device is infected with a trojan virus, it is most likely a scam. Do not click on any links or download any attachments in the email. You can run a virus scan on your device to make sure it is not infected.
- If you received an email saying that you have an outstanding payment and demanding money, it is most likely a scam. Do not send any money or respond to the email. You can check your accounts to make sure there are no outstanding payments.
- If you received a threatening email from your own email address, it is most likely a scam. Do not respond to the email. You can mark the email as spam or report it to your email provider.
It is technically possible to receive an email that appears to come from your own email address, even if your account has not been hacked. This is known as “spoofing” and it involves the sender creating an email with a fake “From” address that appears to be from your email address.
However, it is important to note that this is a common tactic used by scammers and cybercriminals in phishing emails and other types of email-based attacks. So if you receive an email from your own email address that seems suspicious or demands money, it is likely a scam and should be treated with caution.
How the scam works
Sextortion scam emails work by using fear and emotional manipulation to trick victims into paying a ransom. Here is a general overview of how these scams operate:
- The attacker sends an email to a large number of people claiming to have gained access to their computer and sensitive information, such as personal photos or videos, through a virus or malware.
- The email threatens to release the false sensitive information to the victim’s contacts or on the internet if the ransom is not paid within a specified timeframe.
- The email demands payment in a cryptocurrency such as Bitcoin, which is difficult to trace and provides anonymity to the attacker.
- The email creates a sense of urgency and pressure by threatening to release the false information if the ransom is not paid quickly.
- If the victim pays the ransom, the attacker may demand more money or continue to extort the victim.
- If the victim does not pay the ransom, the attacker may still attempt to scam the victim by threatening to release the false information or by trying to extract more money through another scam.
It is important to note that these emails are scams and that the attacker does not actually have access to the sensitive information they claim to have. The ransom should not be paid, and victims should take steps to secure their online accounts and personal information. If you receive a sextortion email, it is best to delete it and report it to the relevant authorities.
Should you pay?
Don’t pay the ransom! Paying a ransom is not recommended for several reasons:
- It may encourage further scams: If the scammers see that you are willing to pay, they may continue to send similar emails or target other victims.
- It may result in financial losses: Paying a ransom will result in financial losses and put your personal and financial information at risk.
- It does not guarantee the scammers will stop: Even if you pay the ransom, there is no guarantee that the scammers will stop sending emails or will not release any fabricated sensitive information.
In summary, paying a ransom in response to a sextortion email, or any type of scam, is not recommended and may result in further harm to the victim. If you receive a sextortion email, it is best to seek help from law enforcement and take steps to secure your online accounts and personal information, instead of sending money to the attacker.
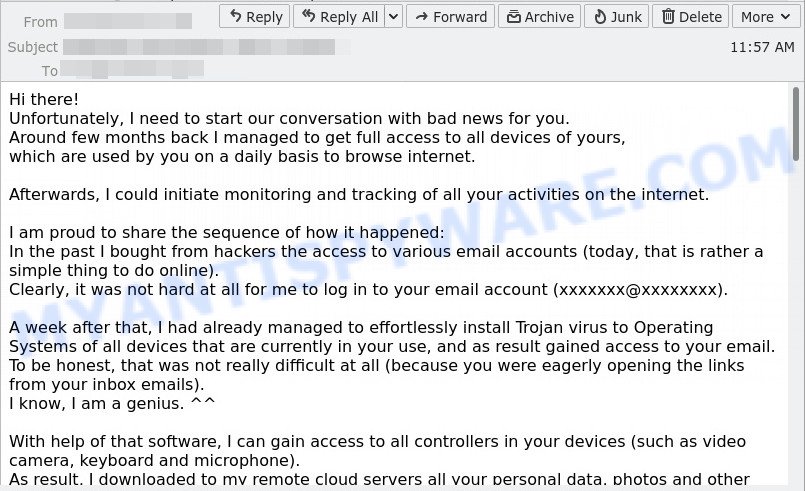
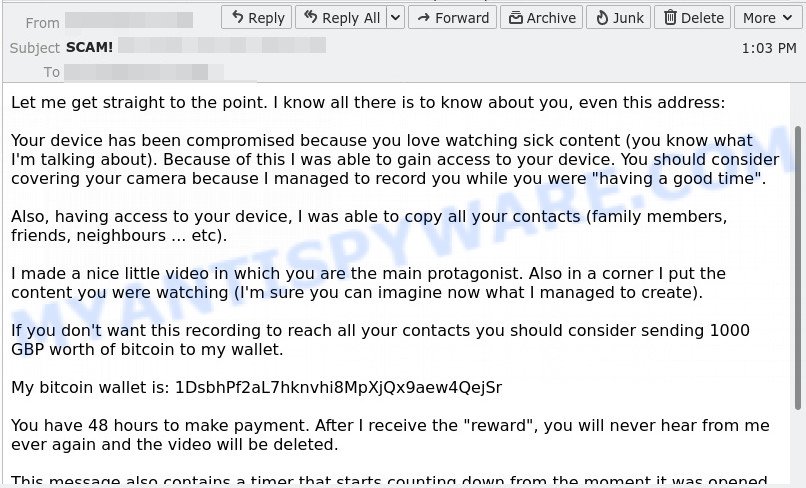
Examples of Sextortion Scams
I need to start our conversation with bad news for you, You have outstanding debt, Let me get straight to the point are other examples of Sextortion scam emails.
- I need to start our conversation with bad news for you Email Scam
- Let me get straight to the point Email Scam
- Your personal data has leaked due to suspected harmful activities. Email Scam
- I’m a hacker who hacked your operating system Email Scam
- I hacked your device EMAIL SCAM
What to do when you receive a sextortion email?
If you receive a sextortion email scam, it is important to take the following steps:
- Do not panic: While these emails are designed to instill fear and panic in the victim, it is important to stay calm and take a measured response to the situation. Remember that the email is fake, and that the attacker does not have access to the sensitive information they are threatening to release
- If the sextortion email scam contains a link, it is important to avoid clicking on it: Avoid clicking on links in sextortion emails as they may lead to malware or phishing sites that can compromise your computer or steal sensitive information.
- Do not respond to the email: Do not reply to the email, or send any money to the attacker.
- Report the scam: Report the scam to the FTC at https://www.ftc.gov/ and relevant authorities, such as your email provider or local law enforcement.
- Delete the email: Delete the email from your inbox and trash folder.
- Secure your accounts: Take steps to secure your online accounts and personal information, such as changing your passwords and enabling two-factor authentication.
- Stay informed: Stay informed about current scams and the tactics used by attackers, so that you can better recognize and avoid them in the future.
- If you suspect that your computer is infected with spyware or trojan, you accidentally clicked on a link in the scam email, or just want to scan your computer for malware, then use one of the best free malware removal tools.
Threat Summary
| Name | I sent you an email from your email account SCAM |
| Type | Phishing, Bitcoin Email Scam, Fraud, Scam |
| Email subject line | Notification! |
| Ransom amount | $950, $1400, $780 |
| Bitcoin Address | 1DEm6pe8iyjaY4WcJpg7TvFYRkJywrGTkz, 1PTqSQm4WEveAxS3hJPGPB7tWa67zUJYbp, 1F21U2R1LbxN6YvWqKnHuxLtVzHS1Mw92W, 1Q7VHR6XgCUFGTUDfVoaGTxLQUwR4xjHMv, 18vAy1BR5Ro5EZh8RCgL27pBSxJjWXK7u5, 19Q3HZtnznuB5cuWng8cacwqZV13gNpZaN, 1HPhZrmyevkNXKo1MYnZG1A65p2PtyEpqcw, 1NL9MTdnTxsVxEg9nHeY5oiw5U9Mxzsh8v, 12yCNJHAwda8Kgxv9DswpS9k16XnstSqcJ |
| Distribution method | spam email campaigns |
| Damage | significant financial loss, emotional distress, reputational damage, compromised personal information, stolen identity |
| Removal | If you gets an email like I sent you an email from your email account, our computer security experts recommend follow some easy steps above |
Report a Scam
If you have received the I sent you an email from your account Scam email or an email message that is similar but not the same as the example above, then post it as comment on this article. Please include the email address the email came from. This helps us to warn users about current scams, monitor trends and disrupt scams where possible.

















Hello!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $784 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 11wQFVQ65DdfzWXqup3JdY7prFazMbXjc
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
Hi
I received a similar e-mail with sligtly different wording, and without offering a password. The text is the following:
********************
Hello!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $795 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 142e8SgyTLnkvwkDkNNon9jMtKY4UDvQqr
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best wishes!
This account is hacked! Change your pswd immediately!
You probably do not know anything about me and you may be certainly wanting to know why you are getting this letter, right?
I am ahacker who crackedyour emailand devices and gadgetstwo months ago.
It will be a time wasting to attempt to get in touch with me or look for me, it is definitely impossible, considering that I forwarded you an email from YOUR account that I’ve hacked.
I have installed malware soft to the adult vids (porno) website and suppose that you have enjoyed this website to have fun (think you understand what I mean).
During you were watching these “great” vids, your internet browser began to act as a RDP (Remote Control) that have a keylogger which provided me the ability to access your screen and network camera.
Afterward, my softobtainedall information.
You have wrote passwords on the online resources you visited, I sniffed them.
Of course, you are able change them, or possibly already modified them.
But it really does not matter, my program updates it regularly.
What actually did I do?
I got a backup of every your system. Of each file and each contact.
I created a dual-screen record. The 1 part demonstrates the video you had been watching (you have got the perfect preferences, ahah…), the 2nd screen displays the tape from your own web camera.
What exactly should you do?
Well, in my opinion, 1000 USD is a good amount of money for our little riddle. You’ll do the deposit by bitcoins (if you do not understand this, try to find “how to purchase bitcoin” in Google).
My bitcoin wallet address:
1816WoXDtSmAM9a4e3HhebDXP7DLkuaYAd
(It is cAsE sensitive, so just copy and paste it).
Attention:
You have 48 hours to perform the payment. (I have an exclusive pixel in this e-mail, and at this point I know that you’ve read this email).
To tracethe reading of a letterand the actionsin it, I installeda Facebook pixel. Thanks to them. (Anything thatis usedfor the authorities can helpus.)
If I do not get bitcoins, I shall certainly transfer your recording to all your contacts, such as family members, colleagues, and so forth?
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you
see the video that you watched. With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $783 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1GoWy5yMzh3XXBiYxLU9tKCBMgibpznGio
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $744 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1GoWy5yMzh3XXBiYxLU9tKCBMgibpznGio
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
I received that message, but unfortunately, I clicked in one of the links! What should I do now??? My computer is new! It has only 2 months of use!!! :((((
I would recommend to scan your computer and find if there are any malware. Use Malwarebytes, or other malware removal tool – http://www.myantispyware.com/2018/04/23/best-free-malware-removal-tools/).
I received it too:
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $794 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1GdSHQ4aE7zUD8HDqVJDEwU9dxn3LfJLMK
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
I have received this dozens of times to an email account I check regularly, but don’t give out to people. I have been ignoring it for a long time, but sometimes I get two or 3 in one day. This message below is the second one today.
———————————————–
Your account was infected! Renew the pswd this time!
You might not heard about me and you obviously are certainly interested why you are reading this particular letter, right?
I am ahacker who crackedyour emailand systemtwo months ago.
Don’t make an attempt to get in touch with me or find me, it is impossible, because I forwarded you an email using YOUR account that I’ve hacked.
I’ve set up virus on the adult vids (porno) site and guess you watched this website to have a good time (think you understand what I mean).
Whilst you were keeping an eye on movies, your internet browser started out functioning like a RDP (Remote Control) that have a keylogger which provided me access to your desktop and web camera.
After that, my softgotall data.
You typed passwords on the web-sites you visited, I already caught all of them.
Without a doubt, you are able modify each of them, or possibly already modified them.
But it doesn’t matter, my malware renews information regularly.
What I have done?
I generated a reserve copy of your device. Of all the files and each contact.
I got a dual-screen movie. The first part demonstrates the film you had been observing (you have a very good taste, huh…), the 2nd part demonstrates the video from your own webcam.
What do you have to do?
Great, I think, 1000 USD is basically a realistic price for our little secret. You’ll make your deposit by bitcoins (in case you don’t understand this, search “how to buy bitcoin” in any search engine).
My bitcoin wallet address:
1B4cy9wtQmNBKKJA1QbYi1ttgiKQJWJY5m
(It is cAsE sensitive, so copy and paste it).
Important:
You will have only 48 hours to perform the payment. (I built in an unique pixel in this e-mail, and at this point I know that you have read this email).
To monitorthe reading of a messageand the activityinside it, I utilizea Facebook pixel. Thanks to them. (The stuff thatis appliedfor the authorities may helpus.)
In case I fail to get bitcoins, I shall undoubtedly send your videofile to each of your contacts, along with family members, co-workers, etc?
Received 3/14/2019. An email address was copied in subject line, not sure if it belongs to scammer or someone else:
Subject line: copy to
I’ve been observation you for a very long time.
The transaction is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.Trojan Virus gives me full access and control your devices.This means that I can see everything on your screen, turn on the camera and microphone, and you won’t even understand it. I can also see all your contacts and all your messages.
Why your antivirus did not detect malware? answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent. I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts. If you wish stop it, transfer the amount of $711 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”). My bitcoin address (BTC Wallet) is: 13FDEoFSZFYWmPd64aEB6pU1tJJCC7jb7N
After I get paid, I will delete the video and you will never hear me again. I give you 48 hours to pay. I have a notice reading this letter, And time starts to go. Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address. I never make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Subject: High level of danger. Your account was under attack. (Received 3/26/2019)
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $729 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 15pY2U8WBZBJRVxGhh8WRXsdkXQbMKD8k9
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
NOTICE – This email was sent from outside of the University – do NOT open any attachments or click on links if you are unsure of the sender’s identity.
one of my friends received it too…
this guy is generous, given 50 hours of time and amount is slightly less @ $762 hahaha
Hi!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $762 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1JBFFHR8tGiMgYLpnZCVG8n4cSpm591urc
After receiving the payment, I will delete the video and you will never hear me again.
I give you 50 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
I received this email. ON MY SCHOOL STUDENT EMAIL!
————————————————————————————————————————————————————————————–
Hello!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your device.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $742 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 14tfS3yWL2cABhXVJZ97XRhuDXC69aWH6Y
After receiving the payment, I will delete the video and you will never hear me again.
I give you 50 hours (more than 2 days) to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
I’ve received several of these emails. Some come as a jpg attachment, which is essentially the same email content:
Subject: I can destroy your life
Hello!
Look at the sender adress of this email ( From: ).
I sent this email from your account, I got full access to it and also your computer, even your webcam and microphone.
Few months ago you got automaticly infected with my malware, RAT ( Remote Administration Tool ), because your browser wasn’t patched to that time when visited some website where my iframe was placed wich redirected to my exploitpack (drive-by-exploit) in the background.
Since then I collected all your private stuff, I even made some videos from you over your webcam and I think we both know, that if everyone else would see all that, your life would be simply hell!
I got absolutly all your contacts, your account on social network and so on…
To publish all I got from you would take me 5 minutes!
You know exactly about the very bad stuff and everything else you got on your computer!!!
I give you the chance to stop me from doing this!
Send me exactly 900$ in bitcoin ( BTC ).
If you don’t know how and where to buy the bitcoins, Google “Where to buy bitcoins?”, it’s very simple task.
Your wallet can be created here: login.blockchain.com/en/#/signup/
My bitcoin adress is: 1Fjg3Q89MawTyfNcMbX6MUnfT923icRuMy
After that I will remove everything and we forget about everything – I promise!
I give you 3 days to get the bitcoins and pay me.
That all isn’t a joke, like I wrote above, look at the sender adress of this email, it is your email and I sent it from your email account, because I got access to everything from you!
———–
Here is another
Subject: Don’t miss the deal
Hello,
As you may have noticed, I sent this email from your email account (if you didn’t see, check the from Sender email ID.)
In other words, I have full access to your email account.
I infected you with a malware (RAT) / (Remote Administration Tool), a few months back when you visited an adult site, and since then, I have been observing your actions.
The malware gave me full access and control over your system, meaning, I can see everything on your screen, turn on your camera or microphone and you won’t even notice about it.
I have also access to all your contacts.
I made a video showing both you (through your webcam) and the video you were watching (on the screen) while statisfying yourself.
I can send this video to all your contacts (email, social network)!
You can prevent me from doing this.
To stop me, transfer exactly 900$ with the current (BTC) BITCOIN price, to my bitcoin address.
I think it’s a very good price compared to the damage, hell and suffering, it will bring into your life!
If you do not know how to get bitcoin, Google – “How to buy Bitcoin”.
Your wallet you can create here: login.blockchain.com/en/#/signup/ – to receive and send the bitcoin.
My bitcoin adress is: 17jHsGecV53ro2LGzo53s5trTH6Qf3gksS
After receiving the payment, I will delete the video, and we will forget everything!
I give you 8 days to get the bitcoins.
Since I already have access to your system, I know when you read this email.
Don’t share this email with anyone, this is our little secret!
Hey!
I know your pass is:
I infected you with my private malware, (RAT) / (Remote Administration Tool), a few months back when you visited some website where my iframe was placed and since then, I have been observing your actions.
The malware gave me full access and control over your system, meaning, I can see everything on your screen, turn on your camera or microphone and you won’t even notice about it.
I have also access to all your contacts, private pictures, videos, everything!
I MADE A VIDEO showing you (through your webcam) STATISFYING YOURSELF!
You got a very good taste! Hahaha…
I can send this video to all your contacts (email, social network) and publish all your private data everywhere!
Only you can prevent me from doing this!
To stop me, transfer exactly 1200$ with the current bitcoin (BTC) price to my bitcoin address.
I think it’s a very good price compared to the damage and hell it can bring into your life!
If you don’t know how to get bitcoin, Google – “How to buy Bitcoin”.
The wallet you can create here: login.blockchain.com/en/#/signup/
My bitcoin adress is: 1LZStbAiQYiBGUTEH8mbTYu8pbvmrDprZQ
After receiving the payment, I will delete the material I got from you, we will forget everything and you can continue living your life in peace like before!
I give you 3 days to get the bitcoins and pay!
Since I got access to your account, I know if this email already has been read!
To make sure you read this email, I sent it multiple times!
Don’t share this email with anyone, this should stay our little secret!
I received this email today. It is actually from an email I only had registered on PHPFreaks. This is most likely from their database hack they had.
Hello! xxxxx@xxxxx.xxx
As you may have noticed, I got your password: xxxxxxxxxx
This means that I have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $999 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1LtAM8MQZWmo63dmYYgzsFUhahXqXutqBf
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
P.S.
After you have transferred the money as I said, I need you to send the information below to my mailbox: cracker88772a@gmail.com.
E-mail account – xxxxx@xxxxx.xxx
Hardware Code – XXXXXXXXXXXXX
MAC Address of Gateway – xx:xx:xx:xx:xx:xx
I will verify your identity and uninstall the Trojans on your computer.
I will also patch your computer to ensure that you will not be infected with these malicious programs again in the future.
The last thing to say is that I also hacked your neighbor’s computer and got a lot of private data (about 30.5GB).
If you are interested in these, please let me know in the letter. I will send you some samples and tell you how to trade.
Remember, don’t ask me anything before you transfer money, I won’t bargain with anyone!!
Best wishes!
—#755805—
Fundamentally the same but different opening gambit…
From email address: Everlee
Hello!
I am a hacker who has access to your operating system.
I also have full access to your account.
I’ve been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.
If you want to prevent this,
transfer the amount of $500 to my bitcoin address (if you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 32UN6H1gSKMKeLn9RXUZUesc2DQsqzMEkJ
After receiving the payment, I will delete the video and you will never hear me again.
I give you 50 hours (more than 2 days) to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
I got one that is similar but again different.
Hello there!
Unfortunately, there are some bad news for you.
Around several months ago I have obtained access to your devices that you were using to browse internet.
Subsequently, I have proceeded with tracking down internet activities of yours.
Below, is the sequence of past events:
In the past, I have bought access from hackers to numerous email accounts (today, that is a very straightforward task that can be done online).
Clearly, I have effortlessly logged in to email account of yours (hunsarle@isu.edu).
A week after that, I have managed to install Trojan virus to Operating Systems of all your devices that are used for email access.
Actually, that was quite simple (because you were clicking the links in inbox emails).
All smart things are quite straightforward. -_-
The software of mine allows me to access to all controllers in your devices, such as video camera, microphone and keyboard.
I have managed to download all your personal data, as well as web browsing history and photos to my servers.
I can access all messengers of yours, as well as emails, social networks, contacts list and even chat history.
My virus unceasingly refreshes its signatures (since it is driver-based), and hereby stays invisible for your antivirus.
So, by now you should already understand the reason why I remained unnoticed until this very moment…
While collecting your information, I have found out that you are also a huge fan of websites for adults.
You truly enjoy checking out porn websites and watching dirty videos, while having a lot of kinky fun.
I have recorded several kinky scenes of yours and montaged some videos, where you reach orgasms while passionately masturbating.
If you still doubt my serious intentions, it only takes couple mouse clicks to share your videos with your friends, relatives and even colleagues.
It is also not a problem for me to allow those vids for access of public as well.
I truly believe, you would not want this to occur, understanding how special are the videos you love watching, (you are clearly aware of that) all that stuff can result in a real disaster for you.
Let’s resolve it like this:
All you need is $1450 USD transfer to my account (bitcoin equivalent based on exchange rate during your transfer), and after the transaction is successful, I will proceed to delete all that kinky stuff without delay.
Afterwards, we can pretend that we have never met before. In addition, I assure you that all the harmful software will be deleted from all your devices. Be sure, I keep my promises.
That is quite a fair deal with a low price, bearing in mind that I have spent a lot of effort to go through your profile and traffic for a long period.
If you are unaware how to buy and send bitcoins – it can be easily fixed by searching all related information online.
Below is bitcoin wallet of mine: 14UTJBbtUsKxPtkf8WvGwWBpB4D6MmGqAk
You are given not more than 48 hours after you have opened this email (2 days to be precise).
Below is the list of actions that you should not attempt doing:
> Do not attempt to reply my email (the email in your inbox was created by me together with return address).
> Do not attempt to call police or any other security services. Moreover, don’t even think to share this with friends of yours. Once I find that out (make no doubt about it, I can do that effortlessly, bearing in mind that I have full control over all your systems) – the video of yours will become available to public immediately.
> Do not attempt to search for me – there is completely no point in that. All cryptocurrency transactions remain anonymous at all times.
> Do not attempt reinstalling the OS on devices of yours or get rid of them. It is meaningless too, because all your videos are already available at remote servers.
Below is the list of things you don’t need to be concerned about:
> That I will not receive the money you transferred.
– Don’t you worry, I can still track it, after the transaction is successfully completed, because I still monitor all your activities (trojan virus of mine includes a remote-control option, just like TeamViewer).
> That I still will make your videos available to public after your money transfer is complete.
– Believe me, it is meaningless for me to keep on making your life complicated. If I indeed wanted to make it happen, it would happen long time ago!
Everything will be carried out based on fairness!
Before I forget…moving forward try not to get involved in this kind of situations anymore!
An advice from me – regularly change all the passwords to your accounts.
Hello there!
Unfortunately, there are some bad news for you.
Around several months ago I have obtained access to your devices that you were using to browse internet.
Subsequently, I have proceeded with tracking down internet activities of yours.
Below, is the sequence of past events:
In the past, I have bought access from hackers to numerous email accounts (today, that is a very straightforward task that can be done online).
Clearly, I have effortlessly logged in to email account of yours (jtcorre2@uc.cl).
A week after that, I have managed to install Trojan virus to Operating Systems of all your devices that are used for email access.
Actually, that was quite simple (because you were clicking the links in inbox emails).
All smart things are quite straightforward. (>_ Do not attempt to reply my email (the email in your inbox was created by me together with return address).
> Do not attempt to call police or any other security services. Moreover, don’t even think to share this with friends of yours. Once I find that out (make no doubt about it, I can do that effortlessly, bearing in mind that I have full control over all your systems) – the video of yours will become available to public immediately.
> Do not attempt to search for me – there is completely no point in that. All cryptocurrency transactions remain anonymous at all times.
> Do not attempt reinstalling the OS on devices of yours or get rid of them. It is meaningless too, because all your videos are already available at remote servers.
Below is the list of things you don’t need to be concerned about:
> That I will not receive the money you transferred.
– Don’t you worry, I can still track it, after the transaction is successfully completed, because I still monitor all your activities (trojan virus of mine includes a remote-control option, just like TeamViewer).
> That I still will make your videos available to public after your money transfer is complete.
– Believe me, it is meaningless for me to keep on making your life complicated. If I indeed wanted to make it happen, it would happen long time ago!
Everything will be carried out based on fairness!
Before I forget…moving forward try not to get involved in this kind of situations anymore!
An advice from me – regularly change all the passwords to your accounts.
BTrw