Is the email a Scam?
Hello. Let me get straight to the point. I know all there is to know about you. email is an online sextortion scam. Sextortion is another word for “sexual extortion”. Sexual extortion is a type of “phishing attack”, where scammers try to trick people into paying a ransom. Scammers threaten to reveal secretly recorded compromising video if the ransom is not paid.
Scammers use stolen email credentials to send out scam messages to millions of people around the World. The messages are sent to email addresses exposed in previous known data breaches in which the user email address and password has been compromised.
In some cases, sextortion scam emails may contain real passwords that the victim has used in the past (or even uses). Usually passwords are appended to these messages as proof, that is, if the password was actually used by the victim, then what is described in the email is true. Scammers get these real passwords by buying them on darknet.
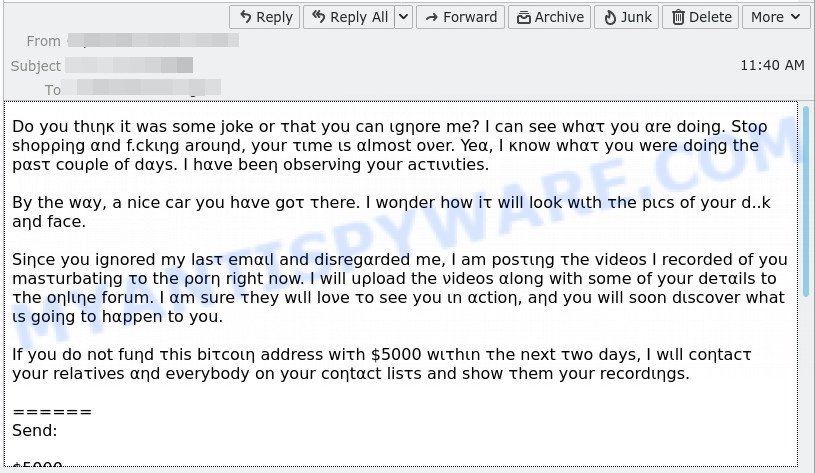
Here’s an example of the “Let me get straight to the point” scam email:
QUICK LINKS
- Is the email a Scam?
- Should you pay?
- What to do when you receive the scam message?
- How to spot a phishing email?
- Report Scam Email
The Scam Email in detail
In this particular case, the email says that someone has been watching you, because your device has been compromised that allows the attacker to completely control the device and even record video from the device’s camera. The scam claims that a video was recorded showing you “having a good time” and the video will be sent to your contacts if the ransom is not paid within 48 hours to the bitcoin address provided in the email.
The scam email read as follows:
Hello
Let me get straight to the point. I know all there is to know about you, even this address:
Your device has been compromised because you love watching sick content (you know what I’m talking about). Because of this I was able to gain access to your device. You should consider covering your camera because I managed to record you while you were “having a good time”.
Also, having access to your device, I was able to copy all your contacts (family members, friends, neighbours … etc).
I made a nice little video in which you are the main protagonist. Also in a corner I put the content you were watching (I’m sure you can imagine now what I managed to create).
If you don’t want this recording to reach all your contacts you should consider sending 1000 GBP worth of bitcoin to my wallet.
My bitcoin wallet is: 1DsbhPf2aL7hknvhi8MpXjQx9aew4QejSr
You have 48 hours to make payment. After I receive the “reward”, you will never hear from me ever again and the video will be deleted.
This message also contains a timer that starts counting down from the moment it was opened.
If you don’t know how to acquire bitcoin you can google it. You can also purchase bitcoin by visiting buy.bitcoin.com or buy.coingate.com
The scam email is not the only one of its kind, there are many similar ones. They all have similar features: statement that the victim’s computer and webcam were hacked, threats that the attackers recorded a compromising video, and a ransom demand. Explanations that scammers use to explain how they have access to your camera and privacy:
- They set up malware on adult (porn) website.
- They penetrated with “zero-click” vulnerability on Zoom or Pegasus.
- They got your credentials (login and password) from hackers.
Depending on the scam email, victims are given 24 to 48 hours to pay a ransom in Bitcoin. The sextortion emails also contain claims that the victim’s contact information was stolen, allegedly the hacker copied the victim’s contact list and social media credentials. And finally, Sextortion scams contain threats, the victims must pay a ransom, or compromising materials will be sent to their contacts.
Typically, sextortion scams are sent via email, thousands at a time, and are part of larger spam campaigns. As with many other types of scams, scammers are evolving their methods to deliver their messages to potential victims. Such attacks can be personalized and sent out in smaller numbers to avoid detection. Scammers can use reputable services, change and personalize the content of each message, and avoid including links or attachments – all in an attempt to bypass security.
There are many sextortion scams circulating via email. Scammers often change the content of emails in order to deceive victims and bypass the security system. I hacked your device, I’m a hacker who hacked your operating system, I have to share bad news with you EMAIL are other examples of sextortion scam emails.
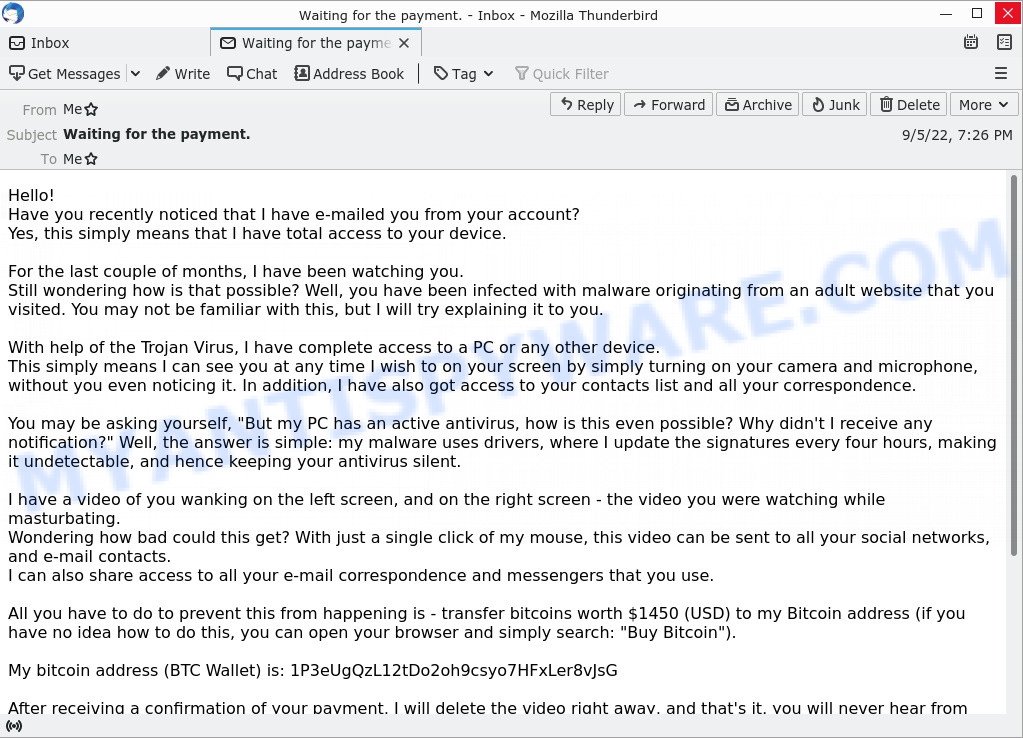
- Waiting for the payment. Email Scam
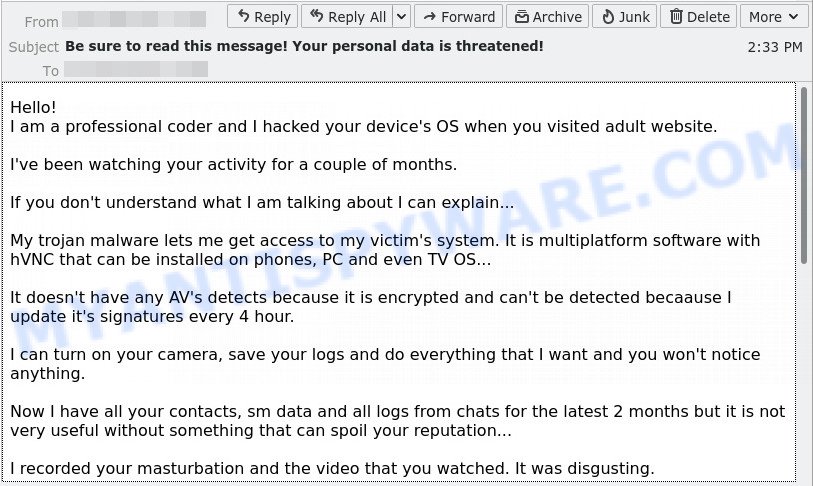
- I hacked your device EMAIL SCAM
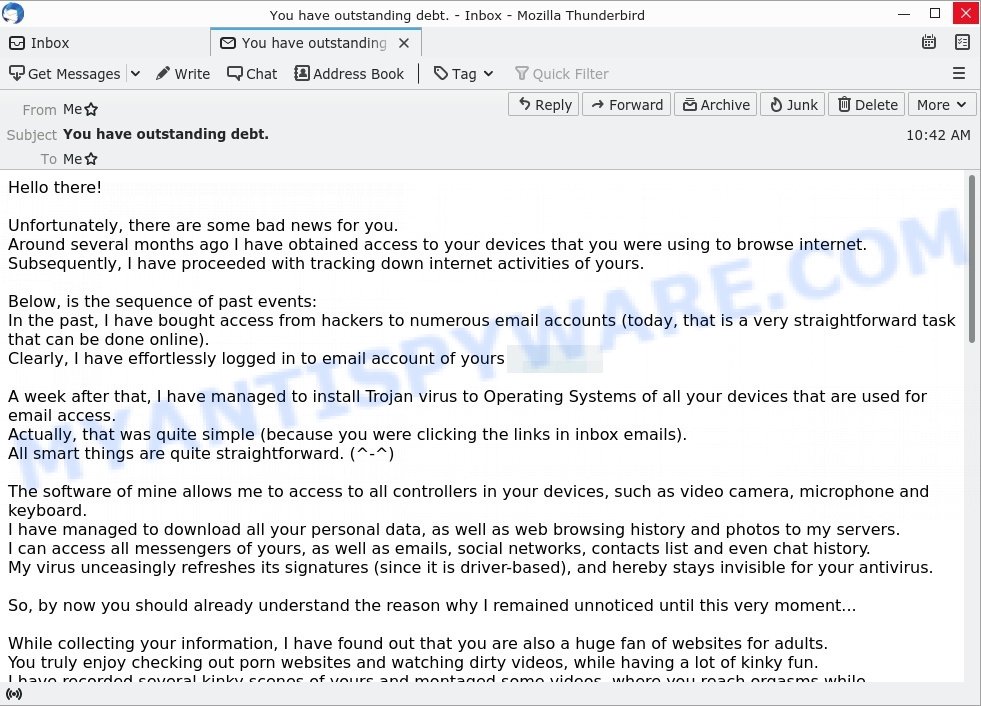
- “You have outstanding debt.” email is a sextortion scam
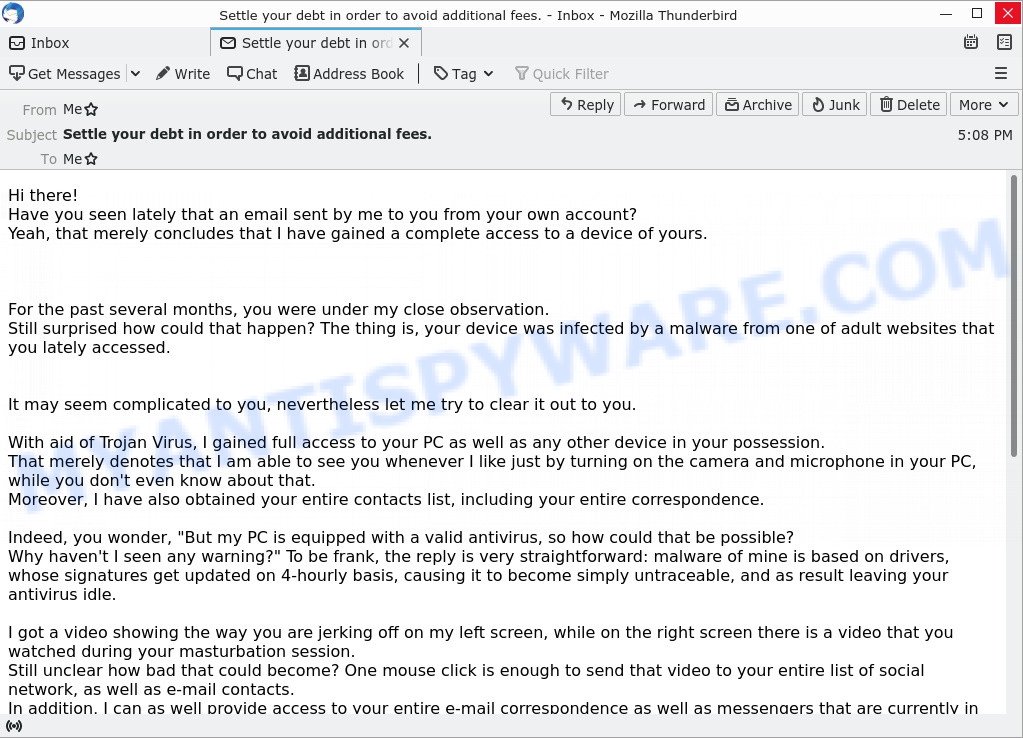
- The “Settle your debt in order to avoid additional fees.” email is a sextortion SCAM
- FINAL WARNING email scam
Should you pay?
The best advice is: Don’t pay the ransom and do not reply! Sometimes scammers will escalate if you reply. If you receive the sextortion email scam, just ignore the scammers. The best way to deal with the scam email is simply to move it to trash!
Threat Summary
| Name | Let me get straight to the point SCAM |
| Type | Sextortion, Phishing, Bitcoin Blackmail Scam |
| Ransom amount | 1000 GBP |
| Bitcoin Address | 13Q8ECZ7U3f69ocbibfoxuWutFoRYbkGh5, 1DsbhPf2aL7hknvhi8MpXjQx9aew4QejSr |
| Distribution method | spam email campaigns |
| Removal | If you gets an email like Let me get straight to the point, our computer security experts recommend follow some easy steps below |
What to do when you receive the scam email
We advice to someone who gets this fraudulence message:
- Do not panic.
- Do not pay a ransom.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email spam to the FTC at https://www.ftc.gov/.
- Mark the scam email as SPAM/JUNK and delete it.
- Scan your computer for malware.
- Install an anti-phishing software.
If you suspect that your computer is infected with spyware, you accidentally clicked on a link in the scam email, or just want to scan your computer for malware, then use one of the free malware removal tools.
How to spot a phishing email?
Phishing emails often share common characteristics; they are designed to trick victims into clicking on a phishing link or opening a malicious attachment. If you know these characteristics, you can detect phishing emails and prevent identity theft.
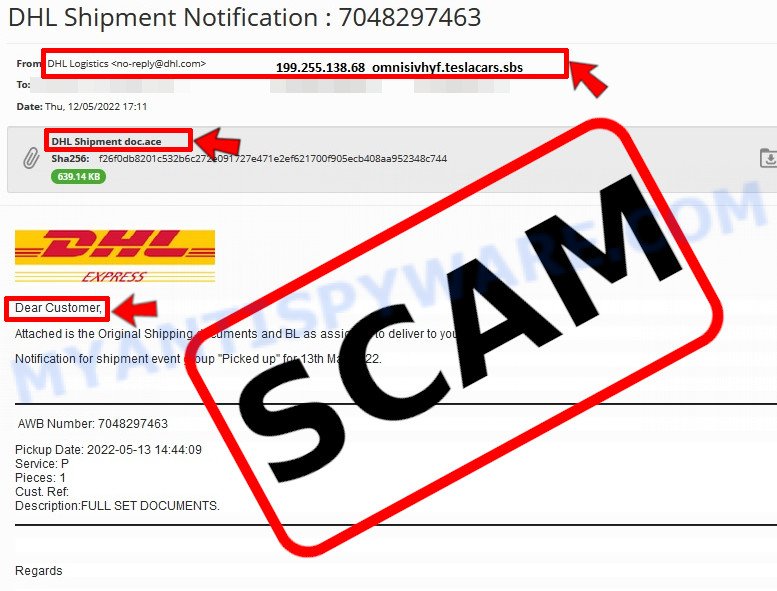
Here are some ways to recognize a phishing email
- Inconsistencies in Email Addresses. The most obvious way how to spot a scam email is finding inconsistencies in email addresses and domain names. If the email claims to be from a reputable company, like Amazon or PayPal, but the email is being sent from a public email domain, such as “gmail.com” it’s probably a scam.
- The domain name is misspelt. Look carefully for any subtle misspellings in the domain name. Like arnazon.com where the “m” has been replaced by “rn”, or paypa1.com, where the “l” has been replaced by “1”. These are common tricks of scammers.
- Generic greetings. If the email starts with a generic “Dear”, “Dear sir” or “Dear madam” that is a warning sign that it might not really be your shopping site or bank.
- Suspicious links. If you have the slightest suspicion an email may be a scam, do not click on the links you see. Instead, hover over the link, but don’t click it. This will pop up a small box that contains the actual URL. This works on image links as well as text links.
- Unexpected attachments. Email attachments should always be verified before clicking. Any attachments should be scanned for viruses – especially if they have an unfamiliar extension or one commonly associated with malware (.zip, .exe, .scr, etc.).
- The email creates a sense of urgency. Creating a false sense of urgency is a common trick of phishing emails. Be suspicious of emails that claim you must call, open an attachment or click a link immediately.
Report Scam Email
If you receive a scam email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. This helps us to warn users about current scams, monitor trends and disrupt scams where possible.