Did you receive an e-mail that starts with something like “This account was recently infected!“? Since you are reading this blog post, then probably Yes. And here comes the main question: Is the email real? This email message is nothing more than an email scam. There are at least 3 different versions of this email floating around. They have “spam” style grammar, bad formatting, spelling errors, and slightly different text.
Myantispyware.com continue to receive reports of fraudulent emails. Recent version demands $1000 ransom payment. Here below is an example.
This account was recently infected! Renew your password right this moment! You might not know anything about me and you really are most probably wondering for what reason you are receiving this particular electronic message, proper? I'm hacker who cracked your email box and all devices several months ago. Never try out to contact me or alternatively try to find me, it is definitely impossible, since I sent you a letter using YOUR hacked account. I developed malware software to the * site and guess that you have enjoyed this website to enjoy it (you understand what I mean). When you were taking a look at movies, your internet browser started out operating like a RDP (Remote Control) having a keylogger that provided me permission to access your monitor and network camera. After that, my softwaregatheredall info. You have typed passcodes on the web-sites you visited, I caught them. Of course, you'll be able to change each of them, or already modified them. However it doesn't matter, my malware renews it every 5 minutes. What actually did I do? I got a reserve copy of every your system. Of each file and contacts. I created a dual-screen video recording. The 1st part demonstrates the video you had been watching (you've got an interesting taste, haha...), the 2nd screen displays the recording from your own camera. What must you do? So, in my view, 1000 USD will be a inexpensive price for this small secret. You'll make the deposit by bitcoins (if you do not recognize this, go searching “how to buy bitcoin” in Google). My bitcoin wallet address: 18LpnvnxavZrvbRyRvS6uEJGoY4C2SsK45 (It is cAsE sensitive, so copy and paste it). Warning: You have only 2 days to make the payment. (I put an unique pixel in this letter, and at this point I understand that you've read this email). To monitorthe reading of a messageand the actionswithin it, I usea Facebook pixel. Thanks to them. (Everything thatis usedfor the authorities can helpus.) In the event I do not get bitcoins, I shall certainly transfer your videofile to each of your contacts, such as relatives, co-workers, and many more?
Other variants of “This account was recently infected!” Email Scam
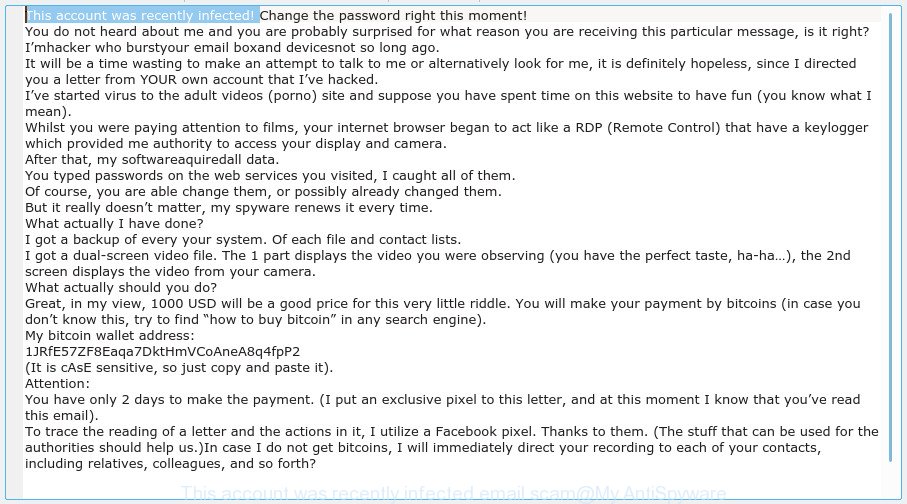
“This account was recently infected email scam” – variant 2
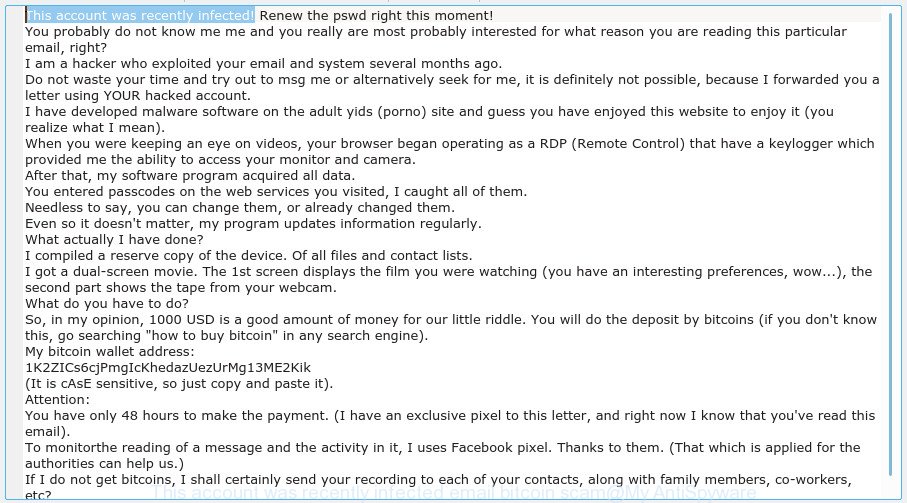
“This account was recently infected” email scam – variant 3
Should you pay the ransom?
The best advice is: Don’t pay the ransom! Scammers will try to rush you, pressure you to make a decision to pay him. We recommend you do not pay a ransom, because your payment will only increase attacks against you.
What to do when you receive “This account was recently infected” Email Scam
We advice to someone who gets this fraudulence message:
- Relax, do not panic.
- Do not respond to the email spam.
- If there’s a link in the scam email, do not click it, otherwise you could unwittingly install malware or ransomware on your computer.
- Report the email scam to the FBI.
- Scan your computer for malware.
- Install an anti-phishing software.
- If you receive an email that is similar but not the same as the example above, make sure you remove any personal info in this message, then post it as comment on this article. It will help our team monitor the latest scams.
How to scan your PC for malware
Malware removal tools differ from each other by many features like performance, scheduled scans, automatic updates, virus signature database, technical support, compatibility with other antivirus apps and so on. We recommend you run the following free software: Zemana, MalwareBytes Anti-Malware (MBAM) and Hitman Pro. Each of these programs has all of needed features, but most importantly, they can identify and remove malware from your personal computer.
We suggest using the Zemana Anti-Malware (ZAM). You can download and install Zemana Free to detect and remove malware from your computer. When installed and updated, this malicious software remover will automatically check and detect all security threats exist on your PC.
Zemana can be downloaded from the following link. Save it on your MS Windows desktop or in any other place.
162846 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
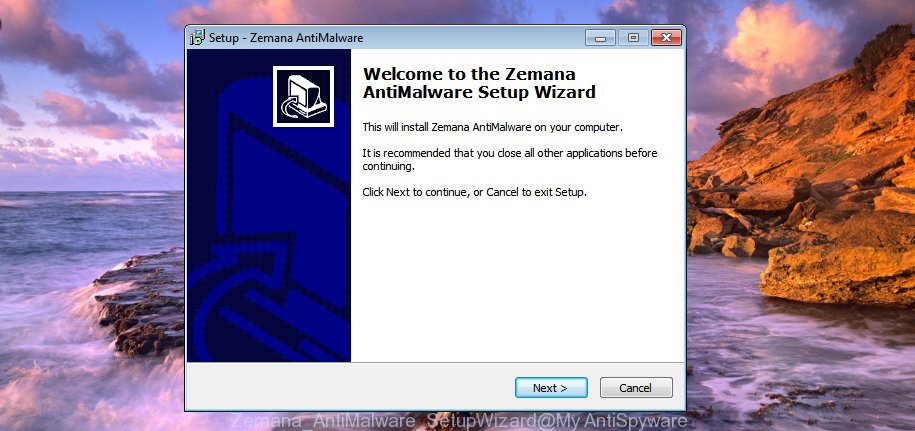
After the download is finished, close all apps and windows on your PC system. Open a directory in which you saved it. Double-click on the icon that’s called Zemana.AntiMalware.Setup as displayed in the figure below.
![]()
When the installation begins, you will see the “Setup wizard” that will help you install Zemana on your system.
Once install is complete, you will see window as displayed below.

Now press the “Scan” button to perform a system scan with this tool for malware and other security threats. This procedure may take some time, so please be patient. While the Zemana AntiMalware (ZAM) is scanning, you can see number of objects it has identified either as being malware.

After the system scan is complete, the results are displayed in the scan report. When you are ready, click “Next” button.
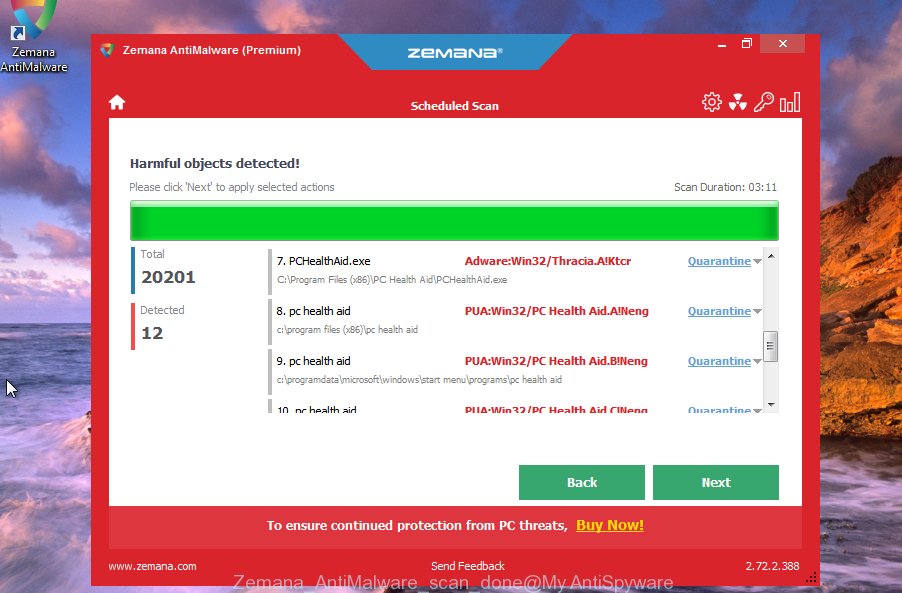
The Zemana Anti Malware will delete malware and add security threats to the Quarantine.
How to protect your computer from phishing web-sites
We recommend to install a program that can stop phishing, malicious, misleading and other unwanted web-sites. The ad-blocker utility such as AdGuard is a application which basically removes advertising from the Internet and stops access to phishing and malicious pages. Moreover, security experts says that using adblocker apps is necessary to stay safe when surfing the Web.
AdGuard can be downloaded from the following link. Save it on your Desktop.
26351 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, launch the downloaded file. You will see the “Setup Wizard” screen as on the image below.
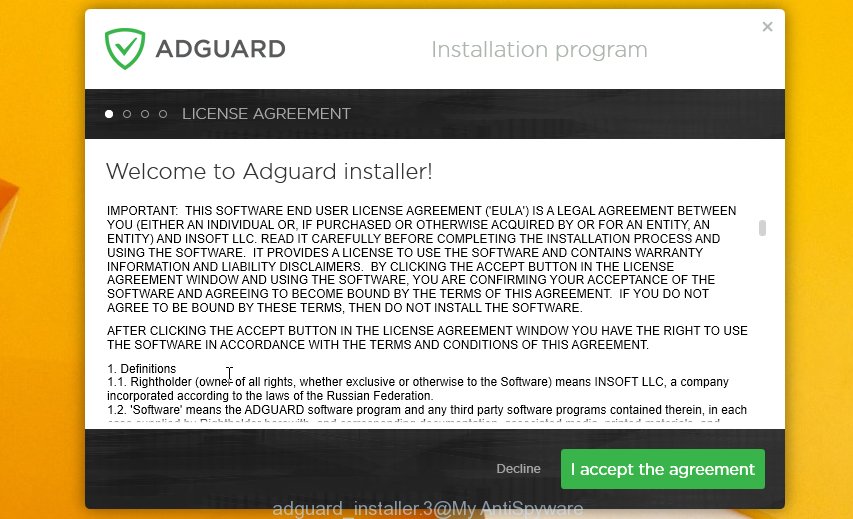
Follow the prompts. After the installation is done, you will see a window as shown in the figure below.

You can click “Skip” to close the installation application and use the default settings, or click “Get Started” button to see an quick tutorial that will assist you get to know AdGuard better.
In most cases, the default settings are enough and you don’t need to change anything. Each time, when you run your PC, AdGuard will run automatically and stop unwanted advertisements, block phishing, malicious or misleading pages. For an overview of all the features of the program, or to change its settings you can simply double-click on the AdGuard icon, that is located on your desktop.



















