Probably you are one of those people, who are facing Webdigger.net and its unwanted changes to web browser settings, may think that there is something wrong with your personal computer. The constant homepage and search provider redirections may cause the difficulty of surfing the Internet. Your attempts to revert back your previous internet browser’s newtab, search provider by default and home page are usually in vain because restoring the Firefox, Internet Explorer, Edge and Google Chrome settings to default states becomes impossible unless you fully remove Webdigger.net browser hijacker infection from your personal computer.
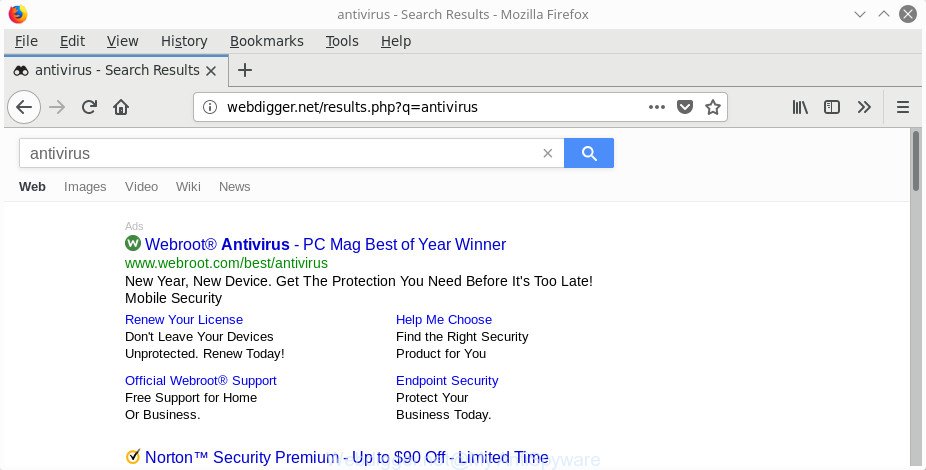
http://webdigger.net/results.php?q=
When the Webdigger.net browser hijacker infection is installed on a computer, it might:
- set Webdigger.net as default search engine, new tab page, and homepage;
- prevent users from replacing search provider or startpage address;
- redirect your queries to sponsored web-sites;
- provide altered search results;
- record your search queries;
- occasionally redirects to questionable websites;
- display unwanted advertisements;
- gather Web surfing habits and transfer it to third parties.
It’s likely that you might be worried with the hijacker responsible for Webdigger.net . You should not disregard this unwanted software. The hijacker might not only change your homepage or search provider, but reroute your internet browser to malicious web-sites. What is more, the browser hijacker infection can analyze your browsing, and gain access to your confidential info and, subsequently, can use it for marketing purposes. Thus, there are more than enough reasons to delete Webdigger.net from your internet browser.
A malicious software which can make changes to internet browsers settings on Webdigger.net usually affects only Google Chrome, FF, Edge and IE. However, possible situations, when any other browsers will be affected too. The Webdigger.net hijacker infection may change the Target property of web-browser’s shortcuts, so every time you launch the browser, instead of your home page, you will see a completely different web site.
In order to remove browser hijacker responsible for redirecting user searches to Webdigger.net from your PC system, clean the infected internet browsers and return the Firefox, Internet Explorer, Google Chrome and Microsoft Edge settings to its default state, please use the Webdigger.net removal guidance below.
How to remove Webdigger.net
There are a few ways that can be used to delete Webdigger.net. But, not all potentially unwanted programs such as this hijacker infection can be completely uninstalled using only manual ways. In most cases you’re not able to delete any browser hijacker infection using standard MS Windows options. In order to remove Webdigger.net you need complete a few manual steps and use reliable removal tools. Most security researchers states that Zemana, MalwareBytes Anti-Malware or Hitman Pro tools are a right choice. These free programs are able to scan for and remove Webdigger.net from your PC and restore your web browser settings to defaults.
To remove Webdigger.net, perform the following steps:
- How to manually remove Webdigger.net
- Use free malware removal tools to completely delete Webdigger.net redirect
- Use AdBlocker to stop Webdigger.net and stay safe online
- How did Webdigger.net hijacker get on your personal computer
- To sum up
How to manually remove Webdigger.net
Steps to remove Webdigger.net hijacker without any software are presented below. Be sure to carry out the step-by-step instructions completely to fully remove this intrusive Webdigger.net .
Remove Webdigger.net related software through the Control Panel of your computer
The process of hijacker infection removal is generally the same across all versions of Microsoft Windows OS from 10 to XP. To start with, it’s necessary to check the list of installed applications on your PC system and delete all unused, unknown and suspicious programs.
Press Windows button ![]() , then click Search
, then click Search ![]() . Type “Control panel”and press Enter. If you using Windows XP or Windows 7, then click “Start” and select “Control Panel”. It will display the Windows Control Panel like below.
. Type “Control panel”and press Enter. If you using Windows XP or Windows 7, then click “Start” and select “Control Panel”. It will display the Windows Control Panel like below.
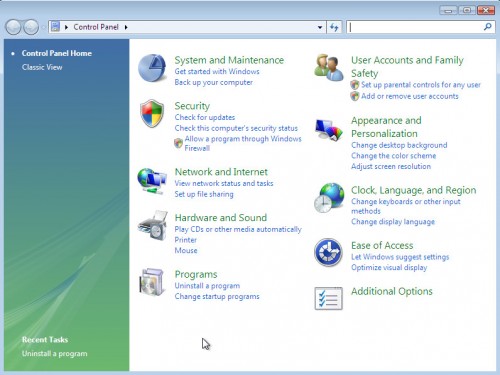
Further, click “Uninstall a program” ![]()
It will display a list of all applications installed on your personal computer. Scroll through the all list, and uninstall any questionable and unknown programs.
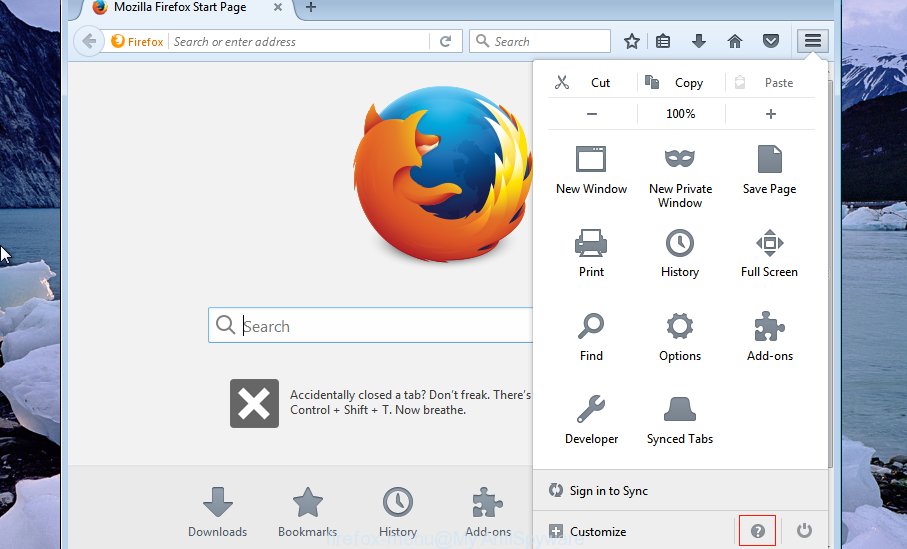
Remove Webdigger.net search from Firefox
If your Mozilla Firefox internet browser start page has modified to Webdigger.net without your permission or an unknown search provider displays results for your search, then it may be time to perform the internet browser reset.
Press the Menu button (looks like three horizontal lines), and press the blue Help icon located at the bottom of the drop down menu like below.
A small menu will appear, press the “Troubleshooting Information”. On this page, click “Refresh Firefox” button as displayed on the screen below.
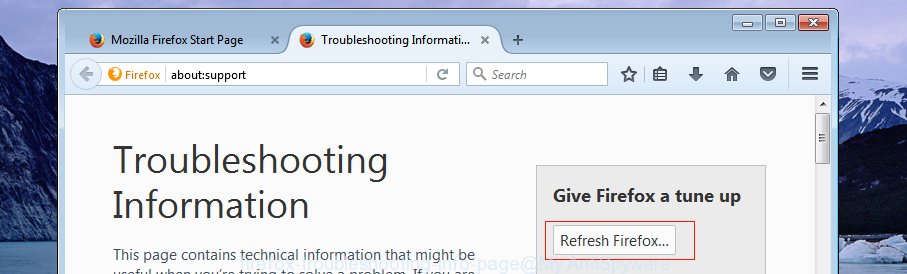
Follow the onscreen procedure to restore your Firefox web-browser settings to its original state.
Delete Webdigger.net from Google Chrome
Like other modern internet browsers, the Google Chrome has the ability to reset the settings to their default values and thereby recover the web-browser newtab, start page and default search engine that have been modified by the Webdigger.net browser hijacker.
Open the Google Chrome menu by clicking on the button in the form of three horizontal dotes (![]() ). It will show the drop-down menu. Choose More Tools, then click Extensions.
). It will show the drop-down menu. Choose More Tools, then click Extensions.
Carefully browse through the list of installed extensions. If the list has the plugin labeled with “Installed by enterprise policy” or “Installed by your administrator”, then complete the following guidance: Remove Chrome extensions installed by enterprise policy otherwise, just go to the step below.
Open the Google Chrome main menu again, press to “Settings” option.
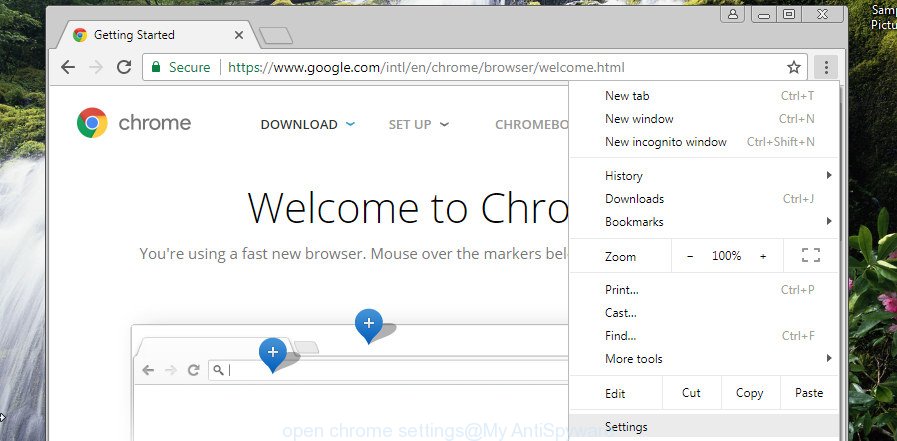
Scroll down to the bottom of the page and click on the “Advanced” link. Now scroll down until the Reset settings section is visible, as displayed on the image below and click the “Reset settings to their original defaults” button.
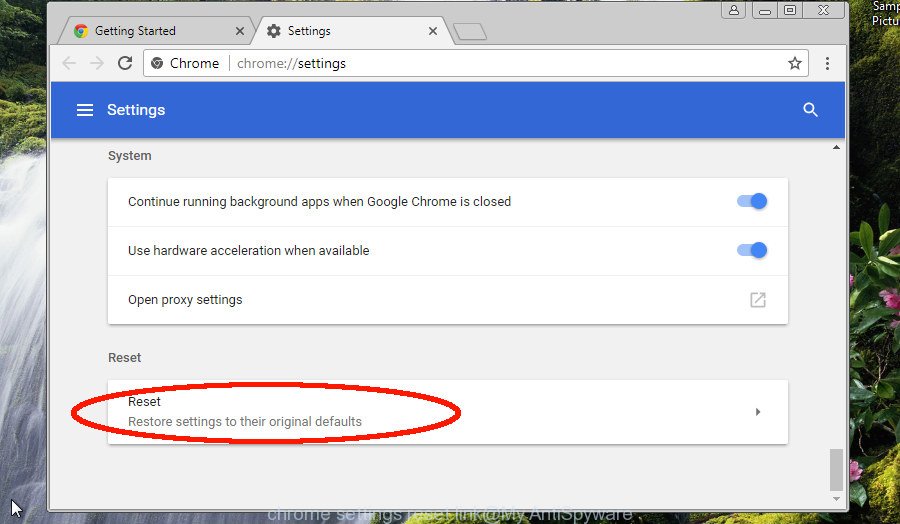
Confirm your action, press the “Reset” button.
Delete Webdigger.net redirect from Internet Explorer
By resetting IE browser you revert back your web-browser settings to its default state. This is good initial when troubleshooting problems that might have been caused by browser hijacker infection such as Webdigger.net.
First, open the Internet Explorer, press ![]() ) button. Next, click “Internet Options” as shown in the figure below.
) button. Next, click “Internet Options” as shown in the figure below.

In the “Internet Options” screen select the Advanced tab. Next, press Reset button. The Internet Explorer will open the Reset Internet Explorer settings dialog box. Select the “Delete personal settings” check box and click Reset button.

You will now need to restart your PC system for the changes to take effect. It will get rid of browser hijacker responsible for Webdigger.net , disable malicious and ad-supported browser’s extensions and restore the Microsoft Internet Explorer’s settings such as newtab, homepage and default search provider to default state.
Disinfect the browser’s shortcuts to delete Webdigger.net redirect
After the browser hijacker is started, it can also modify the internet browser’s shortcut files, adding an argument similar to “http://site.address” into the Target field. Due to this, every time you start the web browser, it will open an unwanted site.
Open the properties of the web-browser shortcut. Right click on the shortcut of infected internet browser and select the “Properties” option and it will show the properties of the shortcut. Next, choose the “Shortcut” tab and have a look at the Target field as displayed in the figure below.
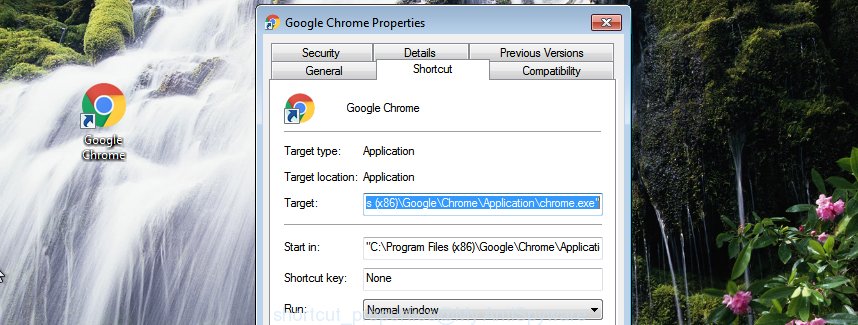
Normally, if the last word in the Target field is chrome.exe, iexplore.exe, firefox.exe. Be sure to pay attention to the extension, should be “exe”! All shortcut files which have been changed by browser hijacker infection that changes web-browser settings to replace your search provider, newtab page and home page with Webdigger.net page, usually point to .bat, .cmd or .url files instead of .exe like below
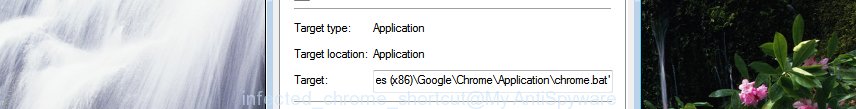
Another variant, an address has been added at the end of the line. In this case the Target field looks such as …Application\chrome.exe” http://site.address as displayed in the figure below.
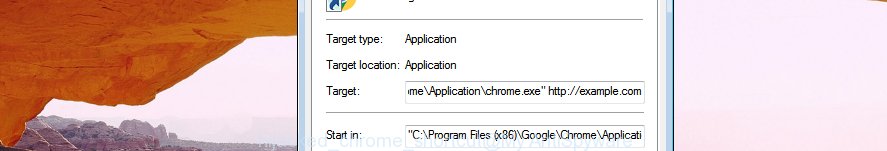
In order to fix the hijacked shortcut file, you need to insert right path to the Target field or remove an address (if it has been added at the end). You can use the following information to fix your shortcuts which have been modified by browser hijacker which cause a redirect to Webdigger.net web-site.
| Google Chrome | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe |
| C:\Program Files\Google\Chrome\Application\chrome.exe | |
| Mozilla Firefox | C:\Program Files\Mozilla Firefox\firefox.exe |
| IE | C:\Program Files (x86)\Internet Explorer\iexplore.exe |
| C:\Program Files\Internet Explorer\iexplore.exe | |
| Opera | C:\Program Files (x86)\Opera\launcher.exe |
| C:\Program Files\Opera\launcher.exe |
Once is finished, click OK to save changes. Repeat the step for all web browsers which are redirected to the Webdigger.net intrusive web-site.
Use free malware removal tools to completely delete Webdigger.net redirect
If you’re an unskilled computer user, then we recommend to run free removal utilities listed below to get rid of Webdigger.net redirect for good. The automatic solution is highly recommended. It has less steps and easier to implement than the manual solution. Moreover, it lower risk of system damage. So, the automatic Webdigger.net removal is a better option.
Run Zemana Free to get rid of Webdigger.net
Zemana is a tool that can remove ad-supported software, potentially unwanted software, hijackers and other malicious software from your PC easily and for free. Zemana Anti-Malware (ZAM) is compatible with most antivirus software. It works under Windows (10 – XP, 32 and 64 bit) and uses minimum of system resources.
Download Zemana Free on your MS Windows Desktop by clicking on the following link.
162847 downloads
Author: Zemana Ltd
Category: Security tools
Update: July 16, 2019
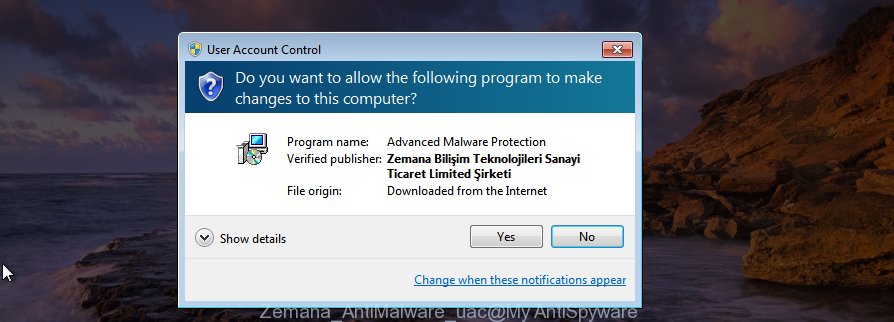
Once the downloading process is finished, close all applications and windows on your system. Double-click the install file called Zemana.AntiMalware.Setup. If the “User Account Control” prompt pops up as displayed in the following example, click the “Yes” button.
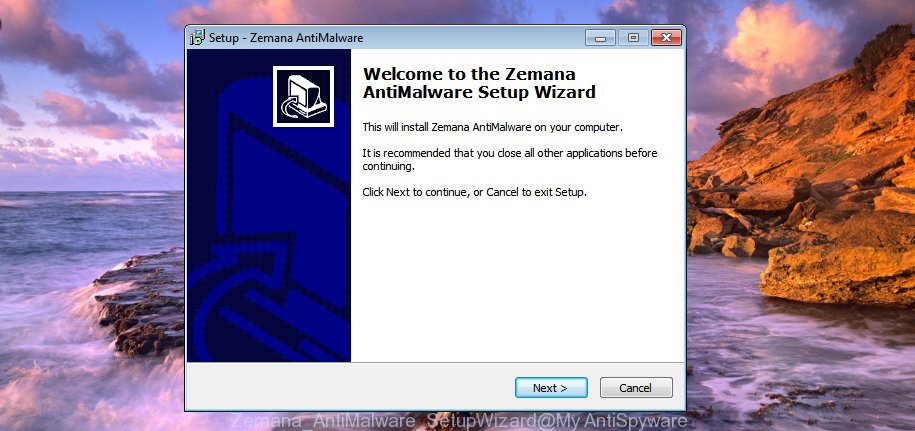
It will open the “Setup wizard” that will help you set up Zemana Anti-Malware on your system. Follow the prompts and do not make any changes to default settings.
Once installation is complete successfully, Zemana will automatically start and you can see its main screen as shown below.

Now press the “Scan” button to start checking your PC for the browser hijacker responsible for redirecting user searches to Webdigger.net. A system scan can take anywhere from 5 to 30 minutes, depending on your system. While the Zemana Anti Malware program is checking, you may see number of objects it has identified as threat.

When that process is finished, Zemana Free will show you the results. Once you’ve selected what you want to remove from your system click “Next” button. The Zemana Anti Malware (ZAM) will start to get rid of hijacker related to Webdigger.net . After disinfection is finished, you may be prompted to reboot the computer.
Scan your PC and delete Webdigger.net with HitmanPro
If Zemana AntiMalware (ZAM) cannot remove this browser hijacker, then we suggests to use the Hitman Pro. The HitmanPro is a free powerful, professional removal tool for malicious software, adware, potentially unwanted software, toolbars as well as browser hijacker which cause a redirect to Webdigger.net web-page. It completely deletes all traces and remnants of the infection.
HitmanPro can be downloaded from the following link. Save it directly to your MS Windows Desktop.
Download and run HitmanPro on your PC. Once started, press “Next” button to perform a system scan for the browser hijacker infection that modifies web browser settings to replace your new tab page, startpage and search provider with Webdigger.net webpage. This process can take some time, so please be patient. .
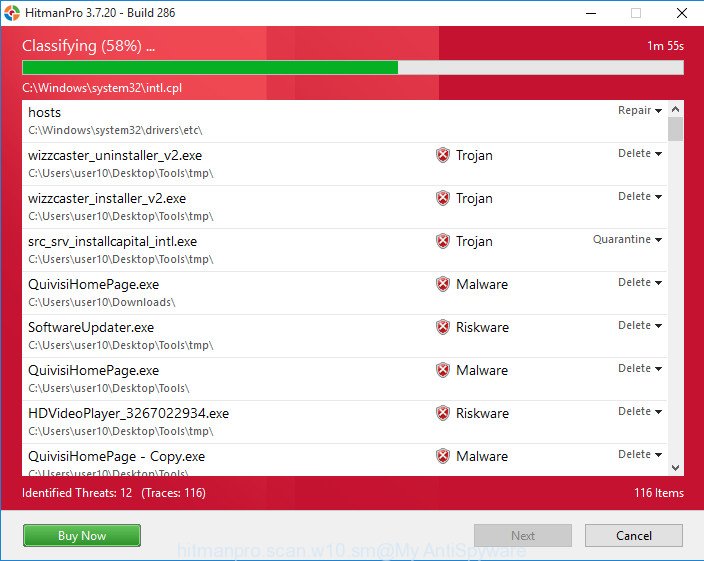
As the scanning ends, a list of all items found is created.
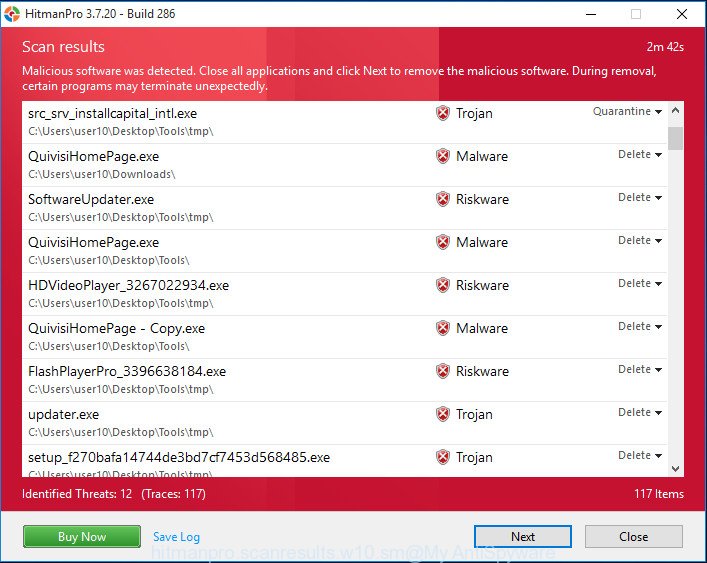
You may remove threats (move to Quarantine) by simply click Next button.
It will display a prompt, press the “Activate free license” button to start the free 30 days trial to delete all malicious software found.
Automatically delete Webdigger.net search with Malwarebytes
Manual Webdigger.net redirect removal requires some computer skills. Some files and registry entries that created by the hijacker infection can be not completely removed. We suggest that run the Malwarebytes Free that are completely clean your computer of browser hijacker. Moreover, the free program will allow you to remove malicious software, PUPs, adware and toolbars that your machine can be infected too.
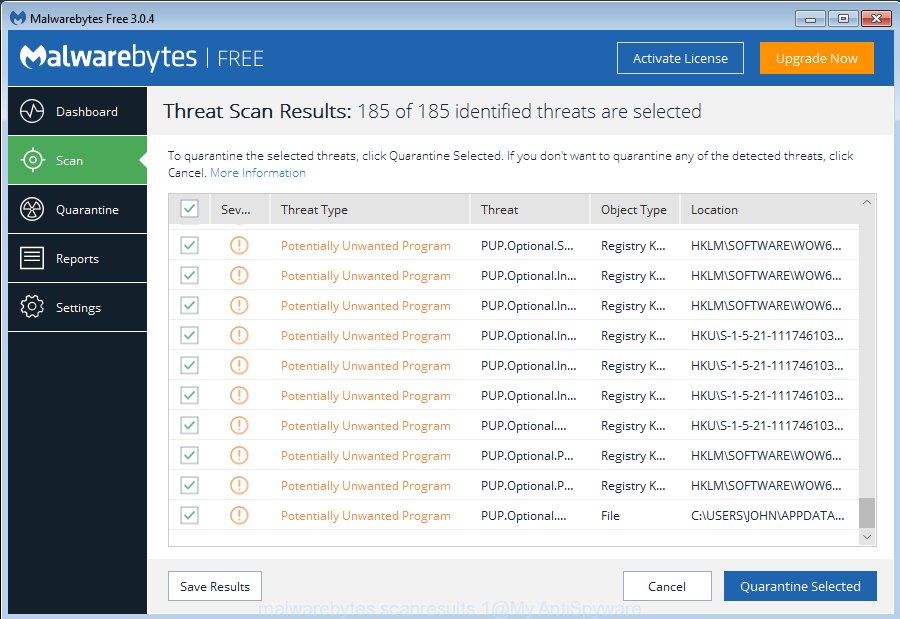
- Visit the following page to download MalwareBytes Free. Save it to your Desktop so that you can access the file easily.
Malwarebytes Anti-malware
324521 downloads
Author: Malwarebytes
Category: Security tools
Update: April 15, 2020
- When the download is complete, close all apps and windows on your computer. Open a file location. Double-click on the icon that’s named mb3-setup.
- Further, click Next button and follow the prompts.
- Once installation is complete, click the “Scan Now” button to perform a system scan with this utility for the browser hijacker related to Webdigger.net . This process may take quite a while, so please be patient. During the scan MalwareBytes Anti-Malware (MBAM) will search for threats exist on your PC system.
- As the scanning ends, the results are displayed in the scan report. In order to delete all items, simply click “Quarantine Selected”. After that process is finished, you can be prompted to restart your computer.
The following video offers a instructions on how to remove hijacker infections, adware and other malicious software with MalwareBytes.
Use AdBlocker to stop Webdigger.net and stay safe online
In order to increase your security and protect your system against new unwanted advertisements and malicious web sites, you need to run adblocker application that blocks an access to malicious advertisements and web sites. Moreover, the program can stop the display of intrusive advertising, which also leads to faster loading of pages and reduce the consumption of web traffic.
Visit the page linked below to download the latest version of AdGuard for Microsoft Windows. Save it on your Microsoft Windows desktop.
26351 downloads
Version: 6.4
Author: © Adguard
Category: Security tools
Update: November 15, 2018
After downloading it, start the downloaded file. You will see the “Setup Wizard” screen as displayed on the image below.
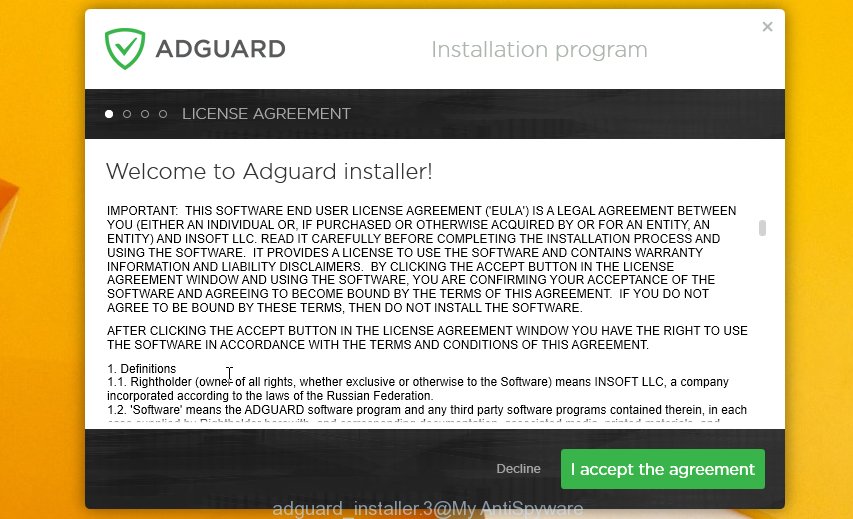
Follow the prompts. When the install is finished, you will see a window like below.

You can press “Skip” to close the installation program and use the default settings, or click “Get Started” button to see an quick tutorial which will help you get to know AdGuard better.
In most cases, the default settings are enough and you don’t need to change anything. Each time, when you start your system, AdGuard will start automatically and stop pop up ads, Webdigger.net redirect, as well as other malicious or misleading sites. For an overview of all the features of the application, or to change its settings you can simply double-click on the AdGuard icon, that may be found on your desktop.
How did Webdigger.net hijacker get on your personal computer
These days some free software authors bundle additional programs which could be potentially unwanted software like the Webdigger.net browser hijacker infection, with a view to making some money. These are not freeware as install an unwanted apps on to your Windows personal computer. So whenever you install a new free program that downloaded from the World Wide Web, be very careful during installation. Carefully read the EULA (a text with I ACCEPT/I DECLINE button), choose custom or manual setup option, uncheck all third-party software.
To sum up
Once you have finished the tutorial above, your computer should be free from browser hijacker infection responsible for modifying your internet browser settings to Webdigger.net and other malicious software. The Edge, IE, Google Chrome and FF will no longer open undesired Webdigger.net site on startup. Unfortunately, if the guidance does not help you, then you have caught a new browser hijacker infection, and then the best way – ask for help in our Spyware/Malware removal forum.




















